The most secure email providers can give your digital correspondence the protection it deserves. These email sentinels offer email encryption, two-step verification, expiring emails, and the like. They employ strict protocols and policies to prevent unauthorized access to your emails. Let’s look at the most secure email providers and the features that make them stand out.


How Secure Are Email Providers?
Email may be the most ubiquitous form of communication on the modern planet. It’s how we communicate with colleagues at work and with friends and family who live far away. It’s also how we sign up for services and get notifications. Email is everywhere, and it’s clear that it’s our preferred communication method for many things. But email was never designed with privacy and security in mind, and this is a serious problem.
Emails transmitted through standard channels are stored as plain, unencrypted text in servers. Suppose that the email servers holding that data get hacked into by external parties. In that case, your personal correspondence and files could be exposed to the world. Emails are even more vulnerable during transit as anyone who eavesdrops on the network can see their contents.
There’s also a reason why email providers are happy to keep their services free. The likes of Google and Yahoo have been caught digging into their own user data in order to monetize it. Most of the data ends up in the hands of advertisers who use the data to create targeted ads.
Even governments are not exempted from dumpster-diving into their citizens’ emails. In fact, the US government has made headlines several times over for apparently forcing email providers to spy on millions of users.
Best Secure Email Providers in 2021


By now, you are probably eager to find a more secure alternative for your email provider. If you’ve just woken up to the reality of free providers, then congratulations. We’ve compiled a list of the most secure email providers. These providers have a well-established reputation in the tech security industry. They also have the features that qualify for a truly secure email service.
1. ProtonMail
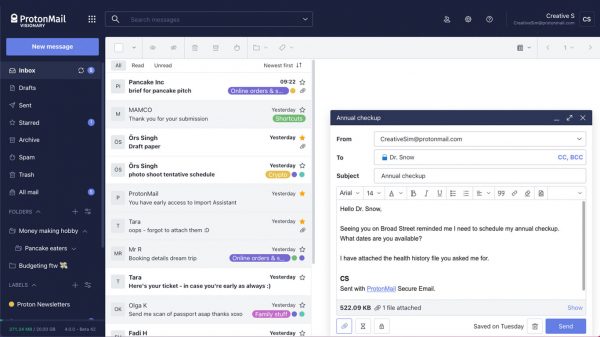
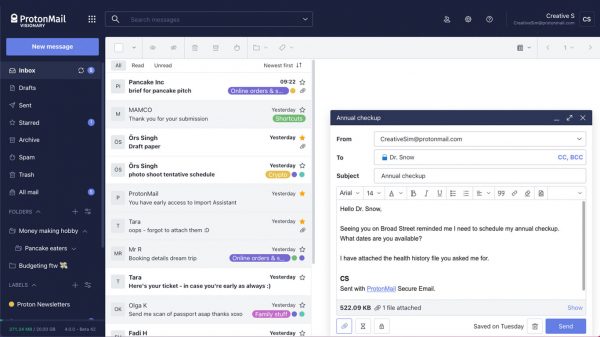
ProtonMail is a secure email provider featuring that offers users a zero-access guarantee. All messages stored in ProtonMail inboxes are protected by PGP encryption. This ensures that only the sender and the intended recipient are able to view the contents of the email. A team of former researchers created the software at CERN. This is the same team that created the popular VPN service, ProtonVPN.
One of the more interesting features of ProtonMail is self-destructing emails. This service feature allows you to set a timer for how long your emails will exist. When the countdown stops, the email will disappear from the recipient’s inbox. You can import contacts from Gmail or other email providers. The software will encrypt your contacts to prevent them from getting tampered with. It will also help your contacts stay safe from potential hackers.
ProtonMail is available in four pricing tiers: free, plus, professional, and visionary. The free tier will let you send encrypted emails. But it only comes with 500 GB of storage and a maximum of 150 emails per day. The premium tiers carry more storage, messages per day, and custom tiers. The most you can get in terms of storage space is approximately 20 GB. If you get any of the top two tiers, you get unlimited emails per day plus unlimited labels.
Visit ProtonMail Official Website
2. CounterMail
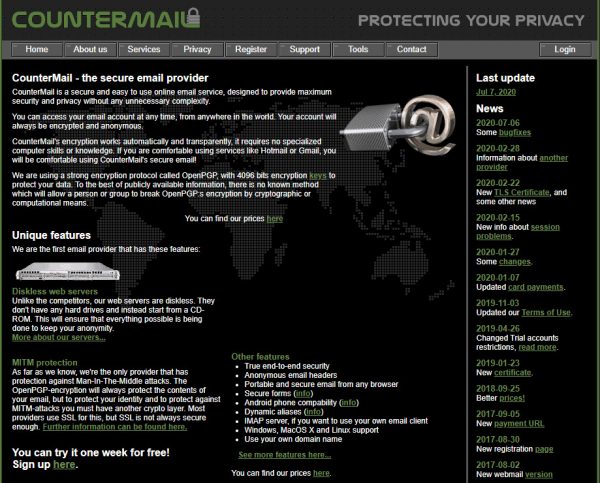
CounterMail is another great option for security-conscious users. The software features total end-to-end protection. This means that users themselves can generate their own keys or password to encrypt the files. Another great feature of CounterMail is that it secures the metadata on your email headers. As you may know, the headers of each email contain information such as transmission details and even your IP address. The software hides this information to ensure the network can trace it back to you. It also allows you to create aliases for your email account. In other words, you can create more than one email address that forwards to your inbox.
CounterMail encrypts emails using an OpenPGP encryption standard. This type of encryption protects not only email content but also user identity. It’s also the ideal encryption to fight against man-in-the-middle attacks (MTM). Additionally, OpenPGP allows for full key management of your contacts. However, the program doesn’t recommend doing this for your own keys. The service is also readily compatible with other email services that use PGP. The software also gives you the ability to use an IMAP server should you prefer to use your own email client.
CounterMail isn’t really a free service, but it does come with a one-week trial period. Your options for subscription vary according to duration and frequency of billing. They are available in increments of six months, twelve months, and two years. Each of these options gets you a minimum of 1000 MB of storage. You can even get additional storage for an extra fee. Even the payment process can be anonymous, as it accepts payment in Bitcoin format.
Visit CounterMail Official Website
3. Mailbox.org
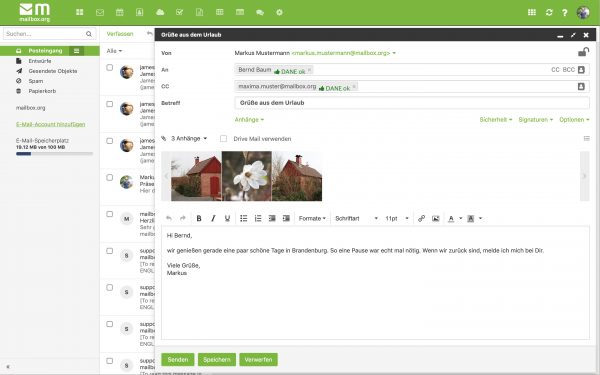
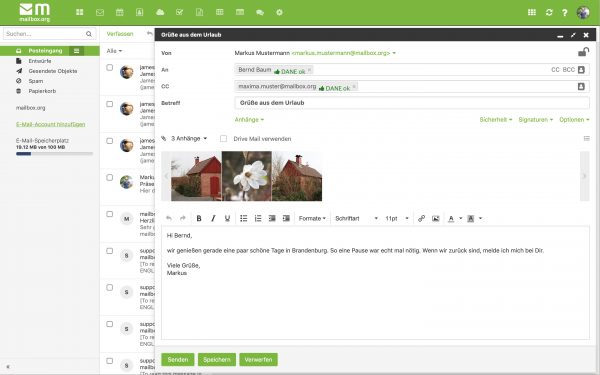
Mailbox.org is another secure email provider with a very affordable pricing plan. The software makes use of a wide selection of industry-approved encryption methods. Examples include SSL for mail transmission and PGP for email storage. It also uses a variety of security algorithms to prevent so-called “man-in-the-middle” attacks.
When it comes to protecting emails and data in storage, the software uses PGP encryption. This protocol is in charge of encrypting the messages that are already in your mailbox. If the system detects that the other user is not using a secure mailbox, it can inform the sender of the email and halt transmission of the email. Its PGP encryption also includes support for the web browser extension called Mailvelope, which encrypts emails separately. It also offers a dedicated Tor Exit Node with Hidden Onion Services to premium users. A tor exit node is basically a gateway that obscures information that can be traced back to you.
Mailbox.org also offers cloud storage and a video conferencing option for all plans. The service also comes with a free address book, to which you can import external contacts lists. You also get a calendar that you can use to schedule your deadlines and appointments.
Visit Mailbox.org Official Website
4. Hushmail
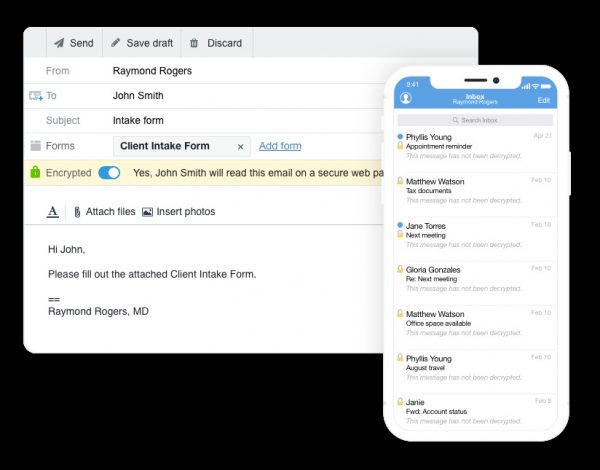
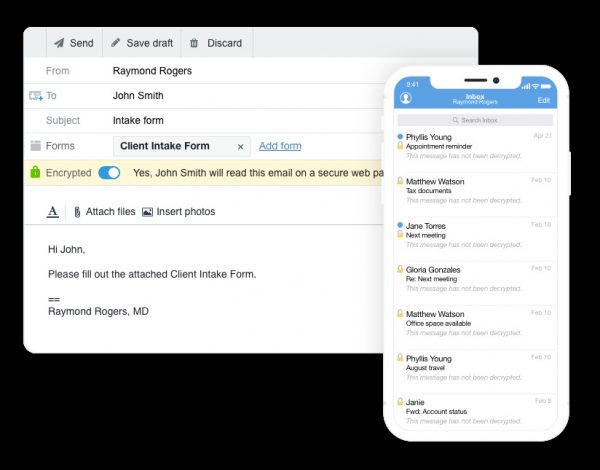
Hushmail is one of the oldest secure email providers available. Signing for Hushmail is completely anonymous. It won’t ask for any identifying information to protect you from the get-go. But on the security front, it makes use of a variety of encryption algorithms like OpenPGP and SSL. OpenPGP encrypts emails in storage, while SSL encrypts emails before transmission. Hushmail uses other security algorithms, including forwarding secrecy and HTTP Strict Transport Security to protect your emails.
As is the case with ProtonMail, you can send emails using Hushmail to non-Hushmail users. The software retains all of your email data on its servers since end-to-end encryption is not possible. The recipient only gets an encrypted link to access the file. The system will then ask the recipient a series of questions, and they must answer these questions correctly in order to decrypt the data. This makes up for the lack of encryption at the other end.
Two-factor authentication is an optional feature with Hushmail. This should allow users to receive a code via a secondary email account or authenticator software. Hushmail adds another security measure for your account through automated locks. Hushmail offers a variety of plans, personal and business that you can customize for specific security needs.
Visit Hushmail Official Website
5. Zoho Mail
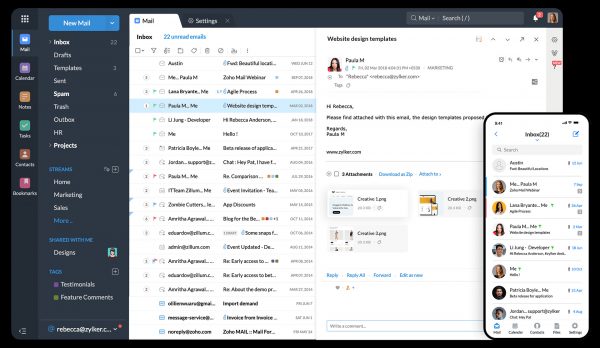
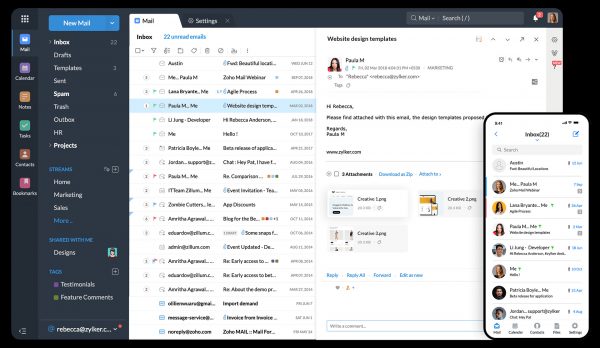
Zoho Mail is another secure email solution that alternates as a work management tool. The software encrypts all outgoing emails using TLs encryption. Meanwhile, it uses Advanced Encryption Standard (AES) to encrypt sensitive data at rest. When it comes to internal security, Zoho says that not even their staff can access your emails. In addition, they employ security protocols to protect the network from unauthorized access by hackers and cybercriminals. They use firewalls and segment network systems into separate networks.
If you sign up for Zoho Desk, Books, or Creator, you only have to sign in with a single username and password. They also offer multi-factor authentication, which adds another layer (or two) to the verification process. You actually have a lot of authentication methods to choose from. This feature will help protect your account in case someone gets hold of your password.
Zoho Mail also has a bunch of other tools related to workplace management. The key feature here would be Zoho Docs, which is the company’s version of Google Docs. With this, users can create different types of documents and collaborate with others in real time. The company also offers Clique, a team-based communication app. Just like with Microsoft Teams, users can discuss any topic, share ideas, and collaborate on content. You will also find other office management tools such as a calendar, notes, and task lists.
Visit ZohoMail Official Website
6. Posteo
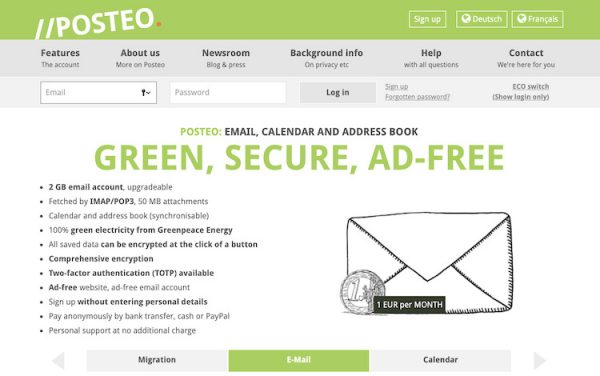
Posteo is a Germany-based, open-source, and secure email provider. Being based in Germany means it’s out of the scope of the Five Eyes. Unfortunately, it’s still part of the Fourteen Eyes, which is practically an expanded version of the Five Eyes. But in case Posteo runs into issues with the government, it will inform the users.
The service starts off with its anonymization of both the signup and payment processes. During the sign-up process, it will only ask for a username, a password, and a payment method. It will not ask for your personal information, such as your name, address, or backup email. The software also protects your payment details. It prevents anyone over the network from tracing your payment information back to you.
Posteo protects your emails in a lot of different ways. The software encrypts all outgoing emails with TLS encryption protocols with additional Perfect Forward Secrecy (PFS). This keeps the email protected from future exploits and security breaches. The software also strips all emails of local and public IP addresses to prevent third parties from tracking the email back to you. As for emails that you receive, you can set a password to serve as your private key.
Posteo also relies on strong AES encryption for all of its email servers to protect emails at rest. A variety of additional security protocols further protect access to the servers. It also offers support for two-factor authentication. This would require you to download an external authenticator app like Google Authenticator. However, Posteo recommends FreeOTP by Fedora since this authenticator is open-sourced. Other things you can do include importing your contacts list from another service or reading how-to guides from its comprehensive website.
7. PrivateMail
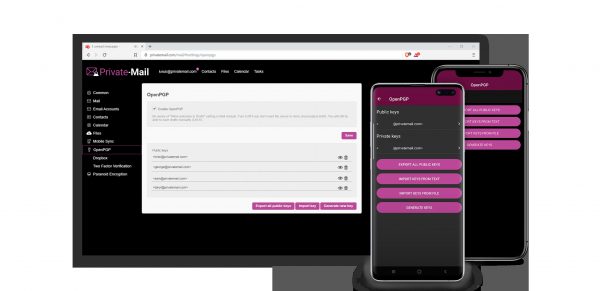
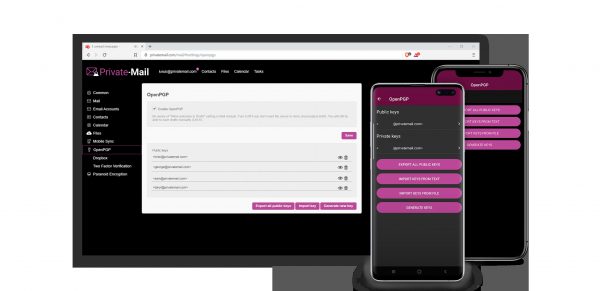
PrivateMail is another well-rounded option from the secure email providers list. The software is available in two tiers: Standard, Pro, and Business. These subscription options have the same security features, but they differ in terms of the number of aliases and cloud storage capacities. With aliases, you can pair them up with each of your domains, and all the emails end up in the same inbox. The least you can get is five aliases for the standard account, and the most are 20 aliases for the Standard account.
PrivateMail does not automatically encrypt your emails from end-to-end. Email encryption in this case would require you to enable the OpenPGP function manually. OpenPGP option manually. After that, you would have to share a password with everyone you’re going to exchange emails with. Furthermore, the receiver will also need to set up their own password and share it with you. If you feel that OpenPGP is not enough, we also recommend getting a reliable VPN to back it up. Check out this guide on how to set up a VPN for your device.
Despite the rather complicated encryption process, the software does have some redeeming qualities. It uses AES encryption on all of the files that you store on the cloud. The software stores all decryption keys for encrypted emails locally on your device. That means not even PrivateMail staff will have access to your email data.
Visit PrivateMail Official Website
8. Mailfence
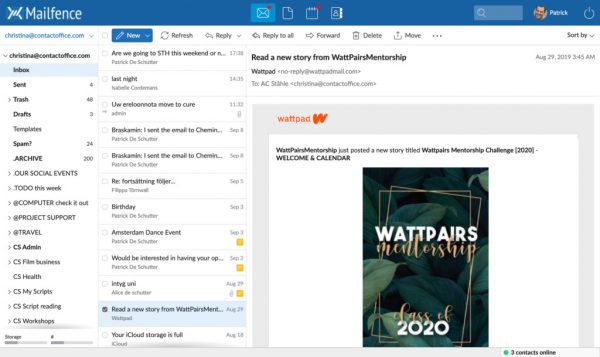
Mailfence is another fully-featured and secure email provider. Since the provider is based in Belgium, it’s not part of the Five Eyes surveillance movement, though it’s still part of the Fourteen Eyes. In other words, the government can still interfere and acquire user data when needed. On the positive side, Belgium is not subjected to gag orders. This means that Mailfence can publish a transparency report informing users about a data retention request.
Mailfence implements a simple, one-click process for encrypting outgoing emails using OpenPGP. You can send emails to fellow Mailfence users using TLS encryption, and these will remain stored within Mailfence servers. You can also send emails to non-members unencrypted or encrypted. If you want them encrypted, you would have to sign them off with a digital PGP key. Besides OpenPGP, the software also supports a variety of alternative protocols.
Mailfence also strips all public and private IP addresses from your emails prior to transmission. This helps to ensure that no one watching the network can identify you. Other features of Mailfence include syncing for contacts and emails. Practically, you can easily import your contacts from another source such as Gmail or Yahoo. It also automatically syncs your emails across all connected accounts. Users can also set up a virtual drive where they can upload important files. Users can set up passwords for each folder in the virtual drive. This digital drive feature is also applicable on Android and IOS versions of the software.
Visit Mailfence Official Website
How Does a Secure Email Provider Work?


Email security hinges on a single aspect—encryption. In simple terms, encryption converts data into an unreadable format to protect it. Encryption is usually done before the email is sent for transmission. Once the email reaches its destination, it is decrypted with a security key that only the recipient would know. The implication is that only the sender and intended recipient will not be able to view the email data.
How Do They Encrypt Emails?
There are different methods for encrypting emails. But for most secure email providers, their options are limited to either PGP or S/MIME. These methods are similar in that they both use public-key cryptography. With S/MIME, a digital certificate is issued to you by a certification authority (CA). The certificate comes along with any email that you send to prove your identity as the sender. It also serves as proof that the email has not been tampered with. At the opposite end, any person who wants to send you an email can get their own certificate to sign off on messages. When you receive the email, a certificate attached will prove the identity of the sender.
In other cases, email providers use PGP instead of S/MIME. PGP programs prove the sender’s identity using digital signatures. But unlike the S/MIMe, these do not need to be signed off by a certificate authority (CA). The first thing that a PGP system does is generate a specific session key to your email. A session key is a long code that is used to encrypt and data the contents of the message. The session key is encrypted further using a sender’s public key. A public key is a unique code that is used to identify you, and it is accessible to anyone who wants to send you a message.
Features to Look For in a Secure Email Provider


Most email providers claim to be safe and secure. But in reality, they fail to provide the features that make for a secure email service. Sometimes, these claims can do more harm than good, as people are lulled into a false sense of security. Since you are here, you are probably aware of the risks and are looking for an alternative. But in your search, make sure to look for the following safety features to ensure that you get your money’s worth.
End-to-End Encryption


This is the basic requirement for any email provider to call themselves “secure.” Without it, there is a chance that third parties will be able to intercept your email while it’s en route to your recipient. If an email service is end-to-end encrypted, it would be nearly impossible for people looking over the network to decipher the email’s contents. Not even the email provider will be able to read your message.
The PGP standard is one of the most effective and commonly used methods for this type of encryption. While other secure email providers present with secure email transfers that are not end-to-end encrypted, it remains preferable over regular encryption protocols.
Multi-Factor Authentication
Multi-factor authentication is a method of verification that goes much further than the simple passcode and username. This method adds a second or third layer of security to your account in case someone else gets a hold of your password. There are a variety of authentication methods that can be useful for two-factor authentication.
Some examples include touch-based authentication or fingerprinting, a push-based notification, QR-code-based authentication, and time-bound one-time-passwords (OTP). The most common 2FA method is OTP, which sends a one-time passcode to other devices that you have. For simpler transactions such as emails. two-factor authentication or 2FA usually suffices. This adds a second layer of protection to your basic password and username.
Message Expiration


Select secure email providers, a special feature that makes emails destruct after a set period. This feature essentially turns your emails into a self-destructing entity that will disappear at a pre-appointed time. This feature usually comes with a timer, which lets you set the week, day, or hour for the countdown. Once the countdown stops, the message will simply disappear from the recipient’s inbox.
This feature is very useful for passing on top-secret messages or highly confidential files.
Secured Metadata Headers
Each email has two components of the data-the body and the header. The header has an underlying set of information called metadata. The metadata includes details about content type, recipient, date of delivery, and more. If you use a standard email, this metadata remains visible even as the message is encrypted. But if you use a secure email service, the metadata will be blurred out.
Server Location


Not all countries look at data privacy the same way. Countries such as the US, UK, Canada, New Zealand, and Australia are part of an intelligence alliance called the Five Eyes. The Five Eyes gather surveillance information and share them with each other. These countries have also created policies to support surveillance activities.
The best example would be data retention policies, which give intelligence agencies the authority to instruct email providers to retain user data for a specified period. For example, in the US, email providers can be instructed by the government to retain data for up to 180 days.
Final Thoughts on the Best Secure Email Providers in 2021


Most free email providers in the market promise safety and security. But in reality, these services only use the bare minimum-security protocols. These protocols will not ensure the safety of your emails while on transit and at rest. In many cases, it is the email providers themselves who exploit their free platforms. This comes with highly ethical complications, especially as these are considered a major breach of data privacy laws. But not to worry, since there are already a lot of more secure options available.
Of course, you must be willing to pay for the security features, and in reality, they are not all that expensive. Overall, investing in a reliable and secure email provider is the best way to protect the integrity and safety of your emails.
Looking for more alternatives? Another great option for securing your digital correspondence would be to use disposable email services.