Introduction
Welcome to the digital age, where downloading software, files, and media has become an essential part of our everyday lives. However, with the convenience of downloads comes the risk of encountering harmful files that can compromise the security of your devices. It is crucial to know how to distinguish between safe and potentially dangerous downloads to protect your personal information and ensure the smooth operation of your devices.
So, what exactly is a safe download? A safe download can be defined as a file or program that is free from malware, viruses, and other malicious elements that may harm your computer or device. It is a download that can be trusted to perform its intended function without compromising your data or system integrity.
When it comes to determining the safety of a download, it is essential to look out for certain signs and take specific precautions. In this article, we will explore some common signs of a safe download, methods to verify the source, and steps to identify suspicious downloads. By following these guidelines, you can minimize the risk of downloading harmful files and ensure the security of your devices.
So, whether you are downloading software for work, movies for entertainment, or any other files from the internet, read on to learn how you can differentiate between safe downloads and potential threats.
What is a Safe Download?
A safe download refers to a file or program that is free from malicious elements and poses no threat to the security and functionality of your computer or device. It is crucial to understand what characteristics make a download safe, as this knowledge can help you make informed decisions when downloading files from the internet.
Here are some key attributes that define a safe download:
- Authenticity: A safe download should come from a reputable and trusted source. It is essential to download files from official websites, trusted software platforms, or reputable app stores. By doing so, you reduce the risk of downloading files that have been tampered with or contain malware.
- Integrity: A safe download should maintain its integrity throughout the downloading and installation process. Unaltered files that have not been modified or corrupted during transmission will provide a safer experience. Verifying the integrity of a file can be done through checksum values or digital signatures provided by the source.
- Security Certificates: Websites and platforms that offer safe downloads often have valid security certificates. This indicates that the website has been verified and encrypted to protect your data during the download process. Look for the padlock symbol or “https” in the website URL to ensure a secure connection.
- Scan Results: Before downloading a file, it is a good practice to scan it with up-to-date antivirus software. A safe download should pass the antivirus scan without any detections of malware, viruses, or other malicious code.
- Frequent Updates: Safe downloads, especially software applications, regularly receive updates from their developers. These updates often include bug fixes and security patches to address vulnerabilities. Ensuring that you download the latest version of a file reduces the risk of potential security breaches or compatibility issues.
By understanding these characteristics, you can evaluate the safety of a download before proceeding with the installation. Remember, the responsibility lies with the user to be vigilant and cautious when downloading files from the internet. Taking the necessary steps to verify the authenticity and integrity of a download can go a long way in maintaining the security of your devices.
Common Signs of a Safe Download
When downloading files from the internet, it is crucial to be able to identify common signs that indicate a safe download. By recognizing these signs, you can make informed decisions and protect yourself from potentially harmful downloads. Here are some key indicators that a download is safe:
- Source Credibility: A reputable and trustworthy source is an important factor to consider. Downloads from well-known software developers, official websites, or legitimate app stores are generally safer than downloads from unknown sources or suspicious websites.
- Positive User Feedback: Checking user reviews and ratings can provide valuable insights into the safety and reliability of a download. If a download has a high number of positive reviews and ratings, it is more likely to be safe and well-regarded by the user community.
- Regular Updates: Safe downloads are often regularly updated by developers to fix bugs, address security vulnerabilities, and enhance performance. Keep an eye out for download versions that are actively maintained and regularly updated, as this signifies ongoing efforts to ensure the safety and functionality of the download.
- Official Digital Signatures: Some downloads, especially software applications, may provide digital signatures from their developers. These signatures verify the authenticity and integrity of the file, providing assurance that the download has not been tampered with or modified by unauthorized parties.
- Secure Connection: Look for a secure connection when downloading files, especially if you are providing personal information or payment details. URLs starting with “https” and a padlock symbol indicate that your connection is encrypted and secure, reducing the risk of unauthorized access to your data.
- Trusted Antivirus Software: Using reputable antivirus software can help identify and prevent the download of malicious files. Regularly update your antivirus software and perform scans on downloaded files to ensure their safety.
- Verified Publishers: Check if the download comes from a verified publisher. Many software applications display the publisher’s name during the installation process. Verifying the publisher’s authenticity can provide additional assurance of a safe download.
Keep in mind that these signs should not be considered individually, but rather collectively. It is important to assess the download’s credibility based on multiple factors and indicators. By being vigilant and observant of these common signs, you can significantly reduce the risk of downloading harmful files and enjoy a safer digital experience.
Verifying the Source
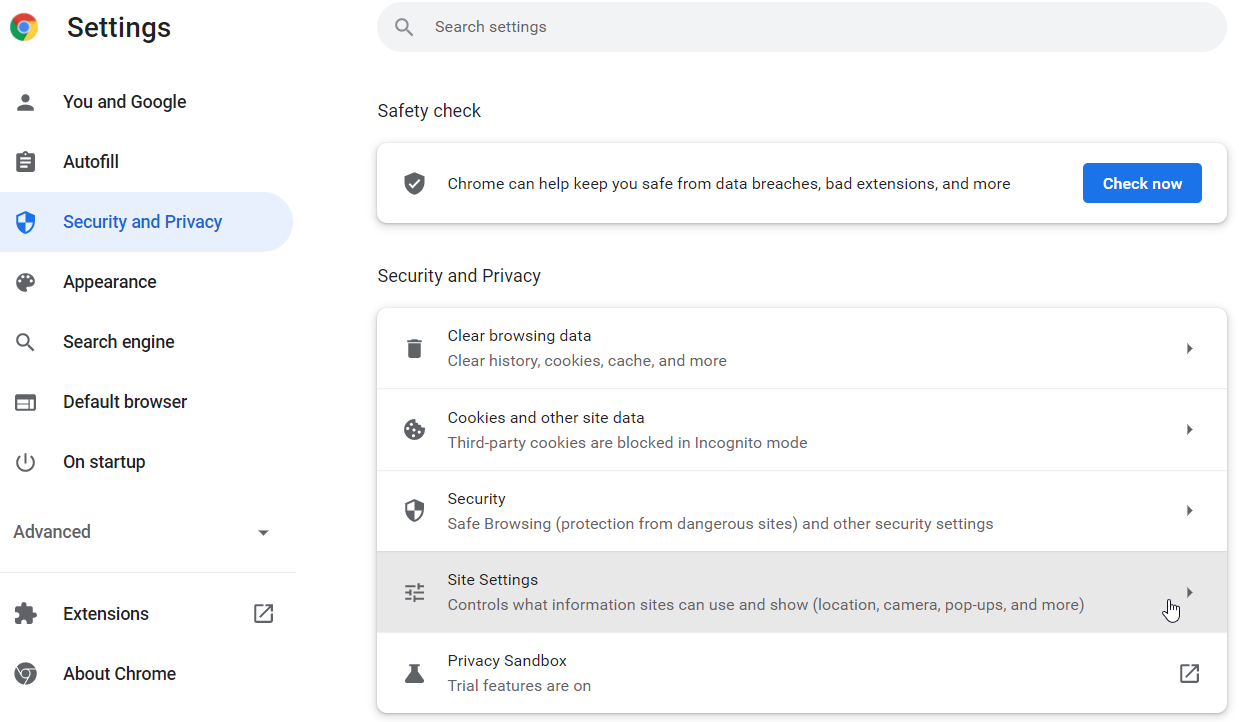
One of the most crucial steps in ensuring a safe download is to verify the source of the file or program. By confirming the authenticity and reliability of the source, you can significantly reduce the risk of downloading harmful files. Here are some methods to help you verify the source:
- Official Websites: When downloading software or files, it is recommended to obtain them from official websites. These websites are designed and managed by the developers themselves and provide a secure and trustworthy source for their products. Look for the official website of the software or file you want to download and ensure that the URL is legitimate and matches the developer’s official domain.
- Secure Platforms: Utilize trusted software platforms and app stores. Platforms such as Microsoft Store, Apple App Store, Google Play Store, and reputable third-party platforms like Softonic and CNET often verify the integrity of the downloads they offer. These platforms also provide user reviews, ratings, and additional information about the downloads, making it easier to gauge their safety.
- Developer Credentials: Check the credentials and reputation of the software developer. Research the company or individual behind the software or file and verify their track record. Established and reputable developers are more likely to offer safe and reliable downloads.
- Secure Download Links: Be cautious of download links from untrusted sources, such as forums, social media platforms, or unknown websites. These links may lead to potentially harmful downloads or malicious sites. Stick to official sources or trusted platforms to minimize the risk.
- Malicious Domain Checks: Before downloading a file, check the domain of the website to ensure it is not registered as a malicious domain. Various online tools and security services can help identify if a domain has a history of distributing malicious content. Avoid downloading files from websites associated with suspicious or malicious activities.
- Multi-Factor Verification: Some software and websites offer multi-factor verification, such as Two-Factor Authentication (2FA) or email verification. These additional security measures add another layer of trust and confidence in the source. Look for platforms that implement such verification processes for enhanced security.
Verifying the source is crucial to ensure the trustworthiness and reliability of the download. By being diligent and cautious when choosing where to download from, you can minimize the risks associated with untrusted sources and protect your computer or device from potential harm.
Checking User Reviews and Ratings
One effective way to assess the safety and reliability of a download is by checking user reviews and ratings. User feedback provides valuable insights into the experiences of others who have already downloaded and used the file or program. Here are some key points to consider when evaluating user reviews and ratings:
- Quantity and Quality: Look for downloads that have a significant number of reviews and ratings. This indicates a larger pool of users who have tried the download and can provide a more accurate representation of its safety and performance. Additionally, pay attention to the quality of the reviews – look for detailed and informative feedback rather than generic or vague statements.
- Recent Feedback: Prioritize recent feedback over older reviews. Software and file versions can change over time, and developers may release updates that address security concerns or improve functionality. Recent reviews give you a better idea of the current state of the download and its safety.
- Variety of Opinions: Consider both positive and negative reviews to gain a balanced perspective. Remember that not all negative reviews indicate a security issue; sometimes, users may have different preferences or encountered compatibility problems. Look for patterns or common concerns raised in the reviews to identify any potential red flags.
- Response from Developers: Check if the developers actively engage with user feedback and address concerns. Developers who promptly respond to user reviews, address issues, and provide updates demonstrate a commitment to their product’s safety and reliability.
- Reputation of Reviewing Platform: Be mindful of the credibility and reputation of the reviewing platform. Consider using trusted sources like official app stores or established software review websites that employ moderation and verification measures to ensure the authenticity of user reviews.
- Comparing Multiple Sources: Don’t rely solely on one source of user reviews and ratings. Explore multiple platforms and websites to gather a wider range of opinions. By comparing feedback from different sources, you can form a more comprehensive understanding of the download’s safety.
While user reviews and ratings provide valuable insights, it is important to use them as one factor among others when assessing the safety of a download. Remember to consider other aspects such as the source credibility, official digital signatures, and security checks to make an informed decision.
Using Antivirus Software
One of the most effective ways to protect your computer or device from malicious downloads is by using reliable antivirus software. Antivirus software is designed to detect, prevent, and remove malware, viruses, and other security threats. Here’s how you can leverage antivirus software to enhance your download safety:
- Install Trusted Antivirus Software: Choose a reputable antivirus software and install it on your computer or device. Look for well-known brands with a proven track record of effectively combating malware and providing regular updates.
- Keep the Software Up-to-Date: Regularly update your antivirus software to ensure it has the latest virus definitions and security patches. New threats emerge constantly, and keeping your software up-to-date is essential for effective protection.
- Perform Scans on Downloaded Files: Use the scanning feature of your antivirus software to scan downloaded files before opening or executing them. This will help identify any potential threats and prevent you from inadvertently downloading harmful files.
- Real-Time Protection: Enable real-time scanning and protection features offered by your antivirus software. This will automatically scan files as you download or access them, providing an additional layer of security against potential threats.
- Customize Scan Settings: Familiarize yourself with the scan settings of your antivirus software. Customize the scan options according to your needs, such as scanning specific folders or file types, enabling heuristic scanning for detecting unknown threats, or scheduling regular scans.
- Quarantine and Removal: If your antivirus software detects a malicious file during a scan, follow the recommended actions to quarantine or remove the file. Quarantining isolates the threat, preventing it from causing further harm, while removal permanently eliminates the threat from your system.
- Trustworthy Download Sources: While antivirus software provides a crucial layer of protection, it is still important to download files from reputable sources. Antivirus software can detect known threats, but it is best to minimize the risk by obtaining files from trusted websites or platforms.
- Enable Firewall Protection: Ensure that your computer’s built-in firewall is enabled or consider using a separate firewall software. The firewall acts as a barrier between your device and the internet, blocking unauthorized access and potentially malicious downloads.
Remember, antivirus software is a valuable tool for protecting your computer or device, but it should not be your sole line of defense. It is crucial to exercise caution when downloading files and follow other safety measures, such as verifying the source and checking user reviews, to ensure the overall safety of your downloads.
How to Identify Suspicious Downloads
Identifying suspicious downloads is an essential skill in ensuring your online safety. By being able to recognize warning signs of potentially harmful files, you can protect your devices and personal information from security threats. Here are some tips to help you identify suspicious downloads:
- Unusual File Names: Be cautious of files with strange or nonsensical names, as they may indicate attempts to deceive or obfuscate the true nature of the file. Avoid downloading files with names that include random numbers, symbols, or misspellings.
- Pop-up Ads and Redirects: Beware of download links that appear as pop-up ads or redirect you to unfamiliar websites. These ads and redirects often lead to potentially harmful downloads or phishing attempts. Stick to trusted sources and avoid clicking on suspicious ads or links.
- Unsolicited Emails: Exercise caution when downloading files attached to unsolicited emails. Malicious actors often use email attachments to distribute malware. Avoid opening email attachments from unknown senders or unexpected sources, especially if the content seems irrelevant or suspicious.
- Too Good to Be True: Be wary of downloads that promise extraordinary features, freebies, or exclusive content. If an offer seems too good to be true, it is likely a ploy to entice users into downloading malicious files. Use your discretion and research the download and its source before proceeding.
- No User Reviews or Ratings: Downloads that do not have any user reviews or ratings can be an indicator of an untested or newly released file. Exercise caution when downloading such files and consider researching the source or waiting for reviews to surface before proceeding.
- Warnings from Antivirus Software: Pay attention to warnings or alerts from your antivirus software. If your antivirus detects a potential threat or flags a download as suspicious, it is best to follow its recommendations and avoid downloading or executing the file.
- Unauthorized Permissions: When downloading mobile apps, review the permissions requested by the app. If the requested permissions seem excessive or unnecessary for the app’s functionality, it may be a sign of a potentially malicious download. Be mindful of granting access to sensitive information or device features.
- Multiple File Extensions: Exercise caution when encountering files with multiple file extensions, such as “file.exe.docx” or “file.jpg.exe”. These files may be disguised as harmless documents but actually contain executable files that can install malware on your device.
Remember, the key is to be vigilant and skeptical when downloading files. Trust your instincts and rely on multiple indicators to determine if a download is suspicious. When in doubt, it is better to err on the side of caution and refrain from downloading the file until you can verify its safety.
Signs of Malware or Viruses
Malware and viruses pose significant threats to the security and functionality of your devices. Being able to identify the signs of malware or viruses can help you take immediate action and prevent further damage. Here are some common signs that indicate the presence of malware or viruses:
- Slow Performance: If your computer or device suddenly becomes sluggish, takes longer to start up, or experiences frequent crashes, it could be a sign of malware or a virus. Malicious software can consume system resources, resulting in decreased performance.
- Unusual Behavior: Pay attention to any abnormal behavior exhibited by your computer or device. This can include unexpected error messages, programs opening or closing by themselves, or changes to system settings that you did not initiate.
- Increased Network Activity: Malware or viruses often communicate with remote servers or perform unauthorized activities in the background. Monitor your network activity and look for unusually high data usage or network traffic, especially when your computer is idle.
- Modified or Deleted Files: If files and folders on your computer or device have been modified, encrypted, or deleted without your knowledge or permission, it may indicate the presence of malware. Ransomware, for example, encrypts your files and demands a ransom for their release.
- Unexpected Pop-ups: Persistent and intrusive pop-up ads, especially those that cannot be easily closed, may be a sign of adware or potentially harmful software. Avoid clicking on these pop-ups and consider running a scan with your antivirus software.
- Disabled Antivirus Software: If your antivirus software or security features have been deactivated or you receive notifications that your protection is turned off, it could indicate malware tampering with your security settings. Immediately re-enable your antivirus software and run a full system scan.
- Unusual Network Connections: Monitor your network connections and look for unusual or unauthorized connections. Malware can establish connections to remote servers or other infected devices, allowing attackers to gain control or steal your personal information.
- Unexplained High CPU Usage: If you notice your computer’s CPU usage constantly at a high level, even when you are not running demanding tasks, it could be a sign of malware. Malicious programs can use your CPU resources to perform malicious activities without your knowledge.
If you observe any of these signs or suspect that your computer or device is infected with malware or a virus, it is important to take immediate action. Run a full system scan with your antivirus software, update your security software, and consider seeking assistance from a professional if necessary. Prevention is key, so regularly update your software, maintain strong security practices, and exercise caution when downloading files or clicking on links to minimize the risk of malware or virus infections.
Avoiding Phishing Attempts
Phishing is a common method used by cybercriminals to deceive and trick individuals into revealing sensitive information, such as passwords, credit card details, or personal data. Recognizing and avoiding phishing attempts is essential to protect yourself from identity theft and financial fraud. Here are some important steps to avoid falling victim to phishing:
- Verify the Sender: Be cautious when receiving emails, messages, or calls from unknown senders. Verify the identity of the sender before opening any attachments, clicking on links, or providing any personal information. Beware of emails that claim to be from reputable organizations but have suspicious or unfamiliar email addresses.
- Double-Check URLs: Before clicking on any links, hover your cursor over them to reveal the actual URL. Be suspicious of URLs that are misspelled, slightly altered, or have a different domain from the legitimate website. Avoid clicking on links in emails or messages that seem urgent or create a sense of panic.
- Keep Software Up-to-Date: Regularly update your operating system, web browsers, and security software to ensure you have the latest protection against phishing attempts. These updates often include security patches that address vulnerabilities that could be exploited by phishers.
- Be Wary of Urgent Requests: Phishing emails and messages often create a sense of urgency or fear to prompt immediate action. Be skeptical of requests for urgent personal information, immediate account verification, or threats to disable or close your accounts. Legitimate organizations typically do not request sensitive information via email or phone.
- Use Two-Factor Authentication (2FA): Enable 2FA whenever possible, especially for online accounts that contain sensitive information. This adds an extra layer of security by requiring a verification code or confirmation in addition to your password. Even if a phisher obtains your password, they won’t be able to access your account without the secondary authentication.
- Employ Antiphishing Tools: Use browser plugins or security software that can detect and block known phishing websites. These tools can provide an extra layer of protection by identifying and warning you about potentially harmful websites.
- Be Cautious on Public Wi-Fi Networks: Avoid accessing sensitive or personal accounts when connected to public Wi-Fi networks. These networks are often unsecured, making it easier for attackers to intercept your data. If you must access sensitive information, consider using a virtual private network (VPN) for an added layer of encryption and security.
- Stay Informed: Keep yourself updated about current phishing techniques and scams. Stay informed by following reputable sources and educate yourself on the latest phishing trends. By staying informed, you can spot and avoid new phishing attempts.
Remember that phishers are constantly evolving their tactics, so it is important to remain vigilant and skeptical when dealing with emails, messages, or calls requesting personal information. When in doubt, always err on the side of caution and verify the authenticity of the request before taking any action.
Importance of Updating Software
Keeping your software up-to-date is a crucial aspect of maintaining the security and functionality of your computer or device. Regular software updates provide important benefits that help protect you against security vulnerabilities, enhance performance, and ensure compatibility with newer technologies. Here are some key reasons why updating software is essential:
- Security Patches: Software updates often include security patches that address known vulnerabilities. Hackers and cybercriminals are constantly finding new ways to exploit weaknesses in software, and updates help close those security gaps. Failure to update your software leaves you more vulnerable to malware, viruses, and other security threats.
- Bug Fixes: Updates also include bug fixes that address software glitches, crashes, and stability issues. By regularly updating your software, you can ensure a smoother and more reliable user experience, minimizing the risk of data loss or system malfunctions.
- Compatibility: As technology evolves, software updates are necessary to ensure compatibility with newer hardware, operating systems, or third-party applications. Outdated software may become incompatible with new technologies, leading to performance issues or limited functionality.
- Improved Features: Software updates often introduce new features, functionality enhancements, and performance optimizations. By updating, you can take advantage of these improvements, which can offer a more efficient and enjoyable user experience.
- Protection Against Exploits: Cybercriminals frequently target outdated software and exploit known vulnerabilities to gain unauthorized access to your devices or personal information. Regularly updating your software helps protect against these exploits, reducing the risk of data breaches and identity theft.
- Vendor Support: Software vendors typically offer support and assistance for the latest versions of their software. If you encounter any issues or require assistance, having updated software makes it easier to receive help from the vendor, including access to troubleshooting guides, user forums, or customer service.
- Regulatory Compliance: In some industries, it may be mandatory to keep software up-to-date to comply with regulatory standards and requirements. Failure to update software in such cases can result in legal and financial consequences.
It is crucial to make updating software a regular practice. Enable automatic updates whenever possible or periodically check for updates manually. Ensure that your operating system, antivirus software, web browsers, and other applications are all kept up-to-date to maintain a secure and optimized computing environment.
Conclusion
Ensuring the safety of our downloads is a critical aspect of using technology in today’s digital landscape. By understanding what constitutes a safe download and being able to identify potential risks, we can protect ourselves from malware, viruses, and other security threats.
In this article, we explored the characteristics of a safe download, such as authenticity, integrity, and security certificates. We discussed the importance of verifying the source, checking user reviews and ratings, and utilizing antivirus software for enhanced protection. We also covered how to identify suspicious downloads and avoid falling victim to phishing attempts.
It is essential to keep our software up-to-date to benefit from the latest security patches, bug fixes, and compatibility improvements. By regularly updating our software, we fortify our defenses against cyber attacks and enjoy optimal performance.
Remember, the responsibility lies with us as users to remain vigilant and cautious when downloading files. We should always verify the source, check for signs of malware or viruses, and exercise caution when sharing personal information online. By adopting these practices and staying informed about emerging threats, we can significantly reduce the risks associated with downloading files from the internet.
Let’s make safe downloads a priority, protecting our devices, data, and online identities. By doing so, we can navigate the digital world with confidence and peace of mind.