Introduction
Welcome to the world of torrenting, where you can freely download and share files with others across the globe. Torrents have revolutionized the way we access and distribute data, offering a vast array of content at our fingertips. However, when it comes to downloading torrents privately, there are several crucial factors to consider. This article will guide you through the steps to maintain your privacy and protect yourself while engaging in torrenting activities.
Sharing files through torrents involves a peer-to-peer (P2P) network, which means that your IP address can be easily tracked by others. This raises concerns about privacy and the potential risks associated with downloading copyrighted material. Additionally, internet service providers (ISPs) and government agencies often monitor torrent activity, which can lead to penalties or legal consequences.
To safeguard your privacy while torrenting, it is essential to take proactive measures. In this article, we will explore methods such as using a Virtual Private Network (VPN), proxy servers, and Seedbox to enhance anonymity and protect your identity. By following these steps, you can enjoy the benefits of torrenting while keeping your activities private and secure.
Before diving into the technical aspects, it is important to note that engaging in illegal activities, such as downloading copyrighted material without permission, is against the law. This article strictly focuses on maintaining privacy and protecting your personal information while participating in legal torrenting activities.
Now, let’s explore some key strategies and tools that will empower you to download torrents privately and securely. By implementing these measures, you can torrent with peace of mind, knowing that your online activities remain anonymous and your privacy is safeguarded.
Understanding Torrents and Privacy
Before we delve into the methods of downloading torrents privately, it is important to have a clear understanding of how torrents work and the potential privacy risks involved.
A torrent is a small file that contains metadata about the files and folders you want to download. Instead of relying on a single server for downloading, torrents use a decentralized approach where files are shared among multiple users, known as peers. When you initiate a torrent download, your computer connects to other peers in the network to download and upload pieces of the file simultaneously.
While this P2P system offers numerous advantages, including faster download speeds and increased availability of files, it also exposes your IP address to others in the network. Your IP address acts as a unique identifier and can be traced back to your device and location. This raises privacy concerns, as it allows anyone to monitor your online activities and potentially track the files you download.
Furthermore, torrenting often involves sharing copyrighted content like movies, TV shows, and music. This attracts the attention of copyright holders who may actively monitor torrent networks and initiate legal action against individuals involved in copyright infringement. ISPs also keep an eye on torrent activities and may throttle your internet speed or impose restrictions if they detect torrenting.
To protect your privacy while torrenting, it is crucial to employ techniques that make it difficult for others to track your online activities. This includes hiding your IP address, encrypting your connection, and ensuring that your downloads remain anonymous.
In the following sections, we will explore tools and strategies that will help you download torrents privately and securely. By implementing these measures, you can safeguard your privacy, avoid legal consequences, and maintain the freedom to enjoy torrenting.
Choosing the Right Torrent Client
When it comes to downloading torrents, selecting the right torrent client is crucial for both convenience and privacy. A torrent client is a software application that allows you to connect to the torrent network and download files.
There are several torrent clients available, each with its own set of features and capabilities. However, not all of them prioritize privacy and security. To ensure that your torrenting activities remain private, it is important to choose a torrent client that offers robust privacy features.
One popular option for privacy-conscious torrenters is qBittorrent. This open-source client offers a user-friendly interface and comprehensive privacy settings. It supports features like IP filtering, which allows you to block specific IP addresses or ranges of IPs from connecting to your client. This can help prevent malicious peers from monitoring your activities and potentially stealing your data.
Another privacy-focused torrent client is Deluge. Deluge is lightweight, easy to use, and offers advanced features to protect your privacy. It allows you to enable encryption for your connections, ensuring that your data remains encrypted and secure while downloading and uploading torrents.
If you prefer a client with a more minimalist design, Transmission might be the right choice for you. It is known for its lightweight performance and simplicity. Transmission also offers encryption options to enhance your privacy while torrenting.
Regardless of the torrent client you choose, it is important to regularly update it to stay protected against any potential security vulnerabilities. Keeping your client up-to-date ensures that you have access to the latest security patches and features.
Additionally, be cautious when downloading torrent clients from untrusted sources. Stick to reputable websites or official sources for downloading torrent clients to avoid any potential malware or compromised versions.
Remember, while your torrent client plays a role in maintaining privacy, it is just one piece of the puzzle. In the next sections, we will explore additional strategies, such as using Virtual Private Networks (VPNs) and proxy servers, to further enhance your privacy and security while torrenting.
Using a VPN for Torrenting
One of the most effective ways to download torrents privately and securely is by using a Virtual Private Network (VPN). A VPN creates a secure and encrypted connection between your device and the internet, ensuring that your online activities remain anonymous and protected.
When you connect to a VPN server, your internet traffic is routed through an encrypted tunnel. This means that your ISP and other prying eyes cannot see what you are doing online, including your torrenting activities. It also masks your IP address, replacing it with the IP address of the VPN server, making it difficult for others to trace your activities back to you.
When choosing a VPN for torrenting, there are several factors to consider. First and foremost, look for a VPN provider that has a strict no-logs policy. This means that the VPN provider does not keep any records of your online activities, ensuring that there is no identifiable information to be shared with third parties.
Speed and server coverage are also important considerations. Make sure that the VPN provider offers fast and reliable connections, as slow speeds can hinder your torrenting experience. Additionally, having a wide selection of servers in different locations can give you more options and better chances of finding peers for faster downloads.
It is crucial to choose a VPN provider that specifically allows torrenting on their network. Some VPNs restrict or prohibit P2P traffic on certain servers, so make sure to check the provider’s terms of service and acceptable use policy to ensure they are torrent-friendly.
Another essential feature to look for in a VPN is a kill switch. A kill switch is a security measure that automatically shuts down your internet connection if the VPN connection drops. This ensures that your real IP address is not exposed, even for a brief period, minimizing the risk of your torrenting activities being tracked by your ISP or other surveillance entities.
It is also worth considering the VPN’s jurisdiction and legal stance on privacy. Opt for a VPN provider based in a country with strong privacy laws and outside the jurisdiction of intelligence-sharing alliances. This adds an extra layer of protection against government surveillance.
Overall, using a VPN for torrenting is highly recommended to ensure your privacy and security. It encrypts your internet connection, hides your IP address, and protects your personal information from prying eyes. In the next section, we will discuss how to select the best VPN for torrenting.
Selecting the Best VPN for Torrenting
When it comes to selecting the best VPN for torrenting, there are several factors that you should consider to ensure optimal privacy, security, and performance. Here are some key aspects to keep in mind:
1. Logging Policy: Look for a VPN provider that has a strict no-logs policy. This means that they do not keep records of your online activities, ensuring that there is no information that can be linked back to you.
2. Security Measures: Ensure that the VPN offers robust security measures, such as strong encryption protocols (like OpenVPN), DNS leak protection, and a kill switch. These features will help safeguard your privacy and protect your data from any potential breaches.
3. Speed and Performance: Torrenting requires fast and stable internet connections. Choose a VPN provider that offers high-speed servers to ensure smooth and uninterrupted torrent downloads.
4. Server Network: A wide selection of servers in various locations allows for better connectivity and faster download speeds. Look for VPN providers with servers in countries where torrenting is legal and outside any surveillance alliances.
5. Torrent-Friendly Policy: Make sure that the VPN provider explicitly allows torrenting on their network and does not throttle or restrict P2P traffic. Some VPNs even offer dedicated servers optimized for torrenting activities.
6. User-Friendly Interface: A user-friendly VPN client makes the setup and configuration process easier, especially for less tech-savvy users. Look for VPN providers that offer intuitive and accessible applications across multiple devices.
7. Customer Support: Reliable and responsive customer support is essential in case you encounter any issues or need assistance with the VPN service.
8. Pricing and Plans: Consider the VPN provider’s pricing and subscription plans to ensure it fits within your budget. Look for providers that offer flexible payment options, including monthly, yearly, or longer-term plans.
9. Reputation and Reviews: Research the VPN provider’s reputation and read user reviews to gauge their reliability and performance. Look for feedback specifically related to torrenting to ensure that the VPN is suitable for your needs.
By carefully evaluating these factors, you can select the best VPN for torrenting that aligns with your privacy requirements and enhances your torrenting experience.
In the following sections, we will explore how to configure your VPN for torrenting and discuss additional strategies to enhance your privacy while engaging in torrent activities.
Configuring Your VPN for Torrenting
Once you have chosen a suitable VPN for torrenting, it is important to properly configure it to maximize your privacy and security. Here are some key steps to follow when setting up your VPN for torrenting:
1. Install and Update the VPN Client: Download and install the VPN client from the provider’s website. Make sure to regularly update the client to ensure you have the latest security patches and features.
2. Connect to a VPN Server: Open the VPN client and connect to a server of your choice. Select a server located in a country where torrenting is legal, and preferably outside the jurisdiction of surveillance alliances.
3. Enable Kill Switch: Most VPN clients have a kill switch feature that automatically disconnects your internet connection if the VPN connection drops. Enable this feature to ensure that your real IP address is not exposed, even momentarily.
4. Verify IP Address and DNS Leak Protection: Confirm that your VPN is working correctly by checking your IP address. Visit a website like whatismyip.com or ipleak.net to verify that your VPN’s IP address is displayed instead of your actual IP. Additionally, ensure that your VPN has DNS leak protection enabled to prevent DNS request leaks that could potentially reveal your real IP address.
5. Test Torrent Downloads: After configuring your VPN, test it by downloading a torrent file. Observe the download speed and make sure there are no IP leaks or interruptions in the connection. If you experience any issues, contact your VPN provider’s customer support for assistance.
6. Configure VPN on Your Torrent Client: Some torrent clients allow you to set up a VPN connection within the client itself. This ensures that your torrent traffic is always routed through the VPN. Check the settings of your torrent client and enable the VPN integration, if available.
7. Regularly Check for VPN Updates: Keep an eye out for any updates or patches released by your VPN provider. Updates often include important security fixes and performance enhancements, so it is essential to keep your VPN client up-to-date.
By following these steps and configuring your VPN properly, you can ensure that your torrenting activities remain private and secure. However, keep in mind that a VPN is just one layer of protection, and it is equally important to follow safe torrenting practices and avoid downloading copyrighted content without permission.
Next, we will explore additional measures you can take, such as using proxy servers and Seedbox, to enhance your anonymity when downloading torrents.
Using Proxy Servers for Added Anonymity
In addition to using a VPN, another method to enhance your anonymity while torrenting is to utilize proxy servers. A proxy server acts as an intermediary between your device and the internet, allowing you to access websites and download files while masking your IP address.
Proxy servers work by receiving requests from your device and forwarding them to the website or torrent tracker on your behalf. This means that your IP address is not directly exposed to the websites or peers you connect with, providing an extra layer of anonymity.
When it comes to torrenting, there are two main types of proxy servers you can use: HTTP proxies and SOCKS proxies.
1. HTTP Proxies: HTTP proxies are the most common type of proxies and are suitable for basic web browsing and torrenting. They only work with web traffic and do not provide encryption. However, they can still hide your IP address and provide some anonymity while downloading torrents.
2. SOCKS Proxies: SOCKS proxies are more versatile and can handle various types of traffic, including torrenting. They provide a higher level of anonymity and can be configured to work with specific applications, such as torrent clients. SOCKS proxies support both TCP and UDP connections and can offer better performance and security than HTTP proxies.
Using a proxy server for torrenting can be a viable option, especially if you are unable to use a VPN. However, it is important to note that proxy servers do not provide the same level of security and encryption as VPNs. They only hide your IP address and do not protect your data or encrypt your internet connection.
When selecting a proxy server for torrenting, consider the following factors:
1. Proxy Type: Choose between HTTP proxies and SOCKS proxies, depending on your specific needs and the level of anonymity you require.
2. Proxy Location: Select a proxy server located in a country where torrenting is legal and outside the jurisdiction of surveillance alliances.
3. Proxy Speed and Reliability: Look for proxy servers that offer fast and reliable connections to ensure smooth torrent downloads.
4. Proxy Compatibility: Ensure that the proxy server you choose is compatible with your torrent client and can be easily configured to work with it.
5. Proxy Security: While proxy servers do not provide encryption, some may offer additional security features like HTTPS encryption for added protection.
It is important to note that configuring a proxy server can be more complex than using a VPN. Incorrectly configuring a proxy server can lead to IP leaks or other security issues. Therefore, if you are not familiar with proxy server setup, it is recommended to seek guidance from reliable sources or consult with a knowledgeable individual.
Next, we will explore another option to further enhance your privacy while torrenting: utilizing Seedbox.
Utilizing Seedbox for Increased Privacy
For those seeking an additional level of privacy and convenience while torrenting, utilizing a Seedbox can be an excellent option. A Seedbox is a remote server hosted in a data center with a high-speed internet connection solely dedicated to torrenting activities.
When you use a Seedbox, you can upload and download torrents at incredibly fast speeds, thanks to the server’s high-bandwidth connection. This eliminates the need to rely on your personal internet connection, which can be slower and may expose your IP address to other peers in the torrenting network.
Using a Seedbox offers several benefits in terms of privacy and security:
1. Anonymity: When you download or upload torrents through a Seedbox, your actual IP address remains hidden from other peers. Instead, only the Seedbox’s IP address is visible to the torrenting network.
2. Encryption: Seedbox providers often offer the option to encrypt the connection between your device and the Seedbox. This ensures that your data remains secure and protected from potential eavesdropping or surveillance.
3. Sever Location: Choose a Seedbox provider that offers servers located in countries where torrenting is legal and outside the jurisdiction of intelligence-sharing alliances. This can help further protect your privacy and ensure compliance with applicable laws.
4. Remote Access: Seedboxes typically come with web-based interfaces that allow you to manage your torrents remotely. This means you can initiate or pause downloads, manage files, and even stream media directly from the Seedbox, all without exposing your own IP address.
5. Ratio Management: Seedboxes often come with built-in tools for managing your upload-to-download ratio. This helps you maintain a healthy share ratio on private torrenting trackers, increasing your overall standing and access to exclusive content.
6. Content Safety: By using a Seedbox, you can download torrents directly to the server and then transfer the files to your personal device via a secure connection. This ensures that potentially harmful files are isolated from your own system, protecting it from malware or viruses.
While Seedboxes offer many benefits, there are a few considerations to keep in mind:
1. Cost: Seedbox services often come with a monthly fee. Consider your budget and the value you place on increased privacy and convenience when deciding on a Seedbox service.
2. Technical Knowledge: Setting up and managing a Seedbox may require some technical know-how. However, many Seedbox providers offer user-friendly interfaces and support to assist users with the setup process.
Utilizing a Seedbox can significantly enhance your torrenting experience by providing increased privacy, speed, and convenience. By keeping your downloads on a remote server, you can torrent with peace of mind, knowing that your IP address and personal information are protected.
In the next section, we will discuss essential measures to ensure secure torrent downloads, regardless of the methods you choose to use.
Ensuring Secure Torrent Downloads
While downloading torrents, it is imperative to prioritize security and take necessary measures to protect yourself from potential risks. Here are some essential steps to ensure secure torrent downloads:
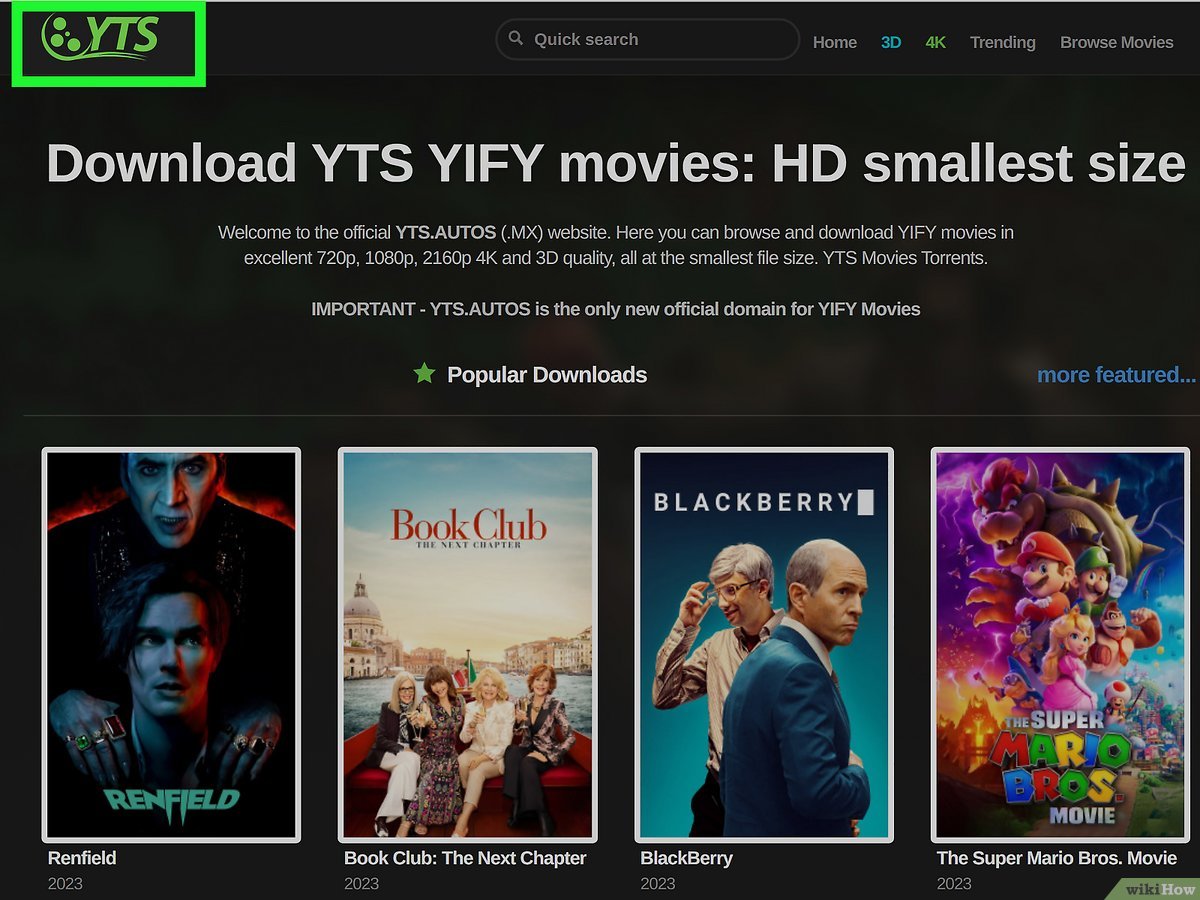
1. Verify the Source: Before downloading any torrent file, ensure that it comes from a trusted source. Look for torrents with a high number of seeds and positive user reviews, as this indicates reliability and decreases the likelihood of downloading malicious content.
2. Read Comments and Descriptions: Check the comments and descriptions associated with the torrent to gather more information about its quality and potential risks. Users often leave feedback about the file’s legitimacy or possible issues to be aware of.
3. Use Antivirus Software: Install reliable antivirus software on your device and keep it up to date. This will help identify and block any malware or viruses that may be present in downloaded files, providing an additional layer of protection for your system.
4. Enable Encryption: If your torrent client supports encryption, enable it to add an extra layer of security. Encryption helps prevent ISPs and other entities from monitoring or inspecting your torrenting activities.
5. Prioritize Legitimate Content: Only download and share legal content, such as open-source software, public domain books, or content with proper licensing. Engaging in illegal activities not only can have legal consequences but also increases the risk of downloading compromised or harmful files.
6. Avoid Suspicious Torrents: Exercise caution when downloading torrents that claim to offer new releases, premium software, or other copyrighted material for free. These torrents are often vehicles for malware or scams.
7. Regularly Update Your Software: Keep your operating system, torrent client, and any other software used for downloading torrents up to date. Updates often include security patches that address vulnerabilities and protect against potential threats.
8. Be Mindful of Personal Information: Never share personal information or login credentials through torrent clients or on torrent websites. Exercise caution and protect your identity and privacy both online and offline.
9. Seed Responsibly: Maintain a healthy sharing ratio by seeding the files you download. This helps promote a healthy torrenting community and ensures the availability of the content for other users.
10. Regularly Backup Your Data: Keep copies of your important files and data on external storage devices or cloud services. This way, even if any issues arise with your downloaded files, you can restore your data from backups.
By following these best practices, you can minimize security risks and enjoy a safer torrenting experience. Remember to always prioritize security and exercise caution when downloading and sharing files via torrents.
Next, we will conclude our discussion on downloading torrents privately and securely.
Conclusion
Torrenting can be an efficient and convenient way to access a wide range of files and content. However, it is important to prioritize privacy and security while engaging in torrent activities.
In this article, we explored various strategies and tools to download torrents privately and securely. We discussed the importance of understanding how torrents work and the privacy risks associated with torrenting. We also highlighted the significance of choosing the right torrent client, such as qBittorrent or Deluge, which offer comprehensive privacy settings and security features.
Using a reputable Virtual Private Network (VPN) emerged as a vital component of secure torrenting. VPNs encrypt your connection, hide your IP address, and protect your personal information from prying eyes. Selecting a VPN provider with a strict no-logs policy, fast speeds, and a wide server network is crucial to ensure optimal privacy and performance.
In addition to VPNs, we discussed the use of proxy servers for added anonymity. While not as secure as VPNs, proxy servers can help mask your IP address, making it harder for others to trace your activities. However, it is essential to choose reliable and reputable proxy servers and be aware of their limitations.
For those seeking increased privacy and convenience, utilizing a Seedbox can be an excellent option. Seedboxes provide a dedicated server with high-speed connections, ensuring fast and secure torrent downloads. It offers anonymity, encryption, and the ability to remotely manage your torrents.
Lastly, we emphasized the importance of ensuring secure torrent downloads. Verifying the source and quality of torrents, using antivirus software, enabling encryption, and avoiding suspicious content are crucial steps to protect yourself from malware and maintain a secure torrenting experience.
By implementing these strategies and utilizing the appropriate tools, you can enjoy the benefits of torrenting while minimizing the risks associated with privacy and security. Always remember to follow legal guidelines, respect copyrights, and act responsibly when downloading and sharing files via torrents.
Happy and safe torrenting!