Introduction
The Internet of Things (IoT) has revolutionized the way we live, work, and interact with technology. It refers to the vast network of interconnected devices that are capable of sharing data and communicating with each other over the internet. From smart home devices like thermostats and doorbell cameras to wearable fitness trackers and industrial sensors, IoT devices have permeated every aspect of our lives.
As the popularity of IoT devices continues to grow, so do the risks associated with their use. These devices, while convenient and innovative, bring about significant security vulnerabilities that can potentially compromise our personal and business security. Understanding these risks is crucial in order to proactively address and mitigate them.
This article will delve into the major risks of using IoT devices, including security vulnerabilities, data privacy concerns, lack of standardization and regulation, as well as the potential for botnet and Distributed Denial of Service (DDoS) attacks. We will also explore the impact of these risks on both personal and business security and discuss strategies to secure IoT devices effectively.
By gaining a comprehensive understanding of these risks, we can make informed decisions when it comes to using IoT devices and take steps to protect ourselves and our sensitive data from potential threats.
What is the Internet of Things (IoT)?
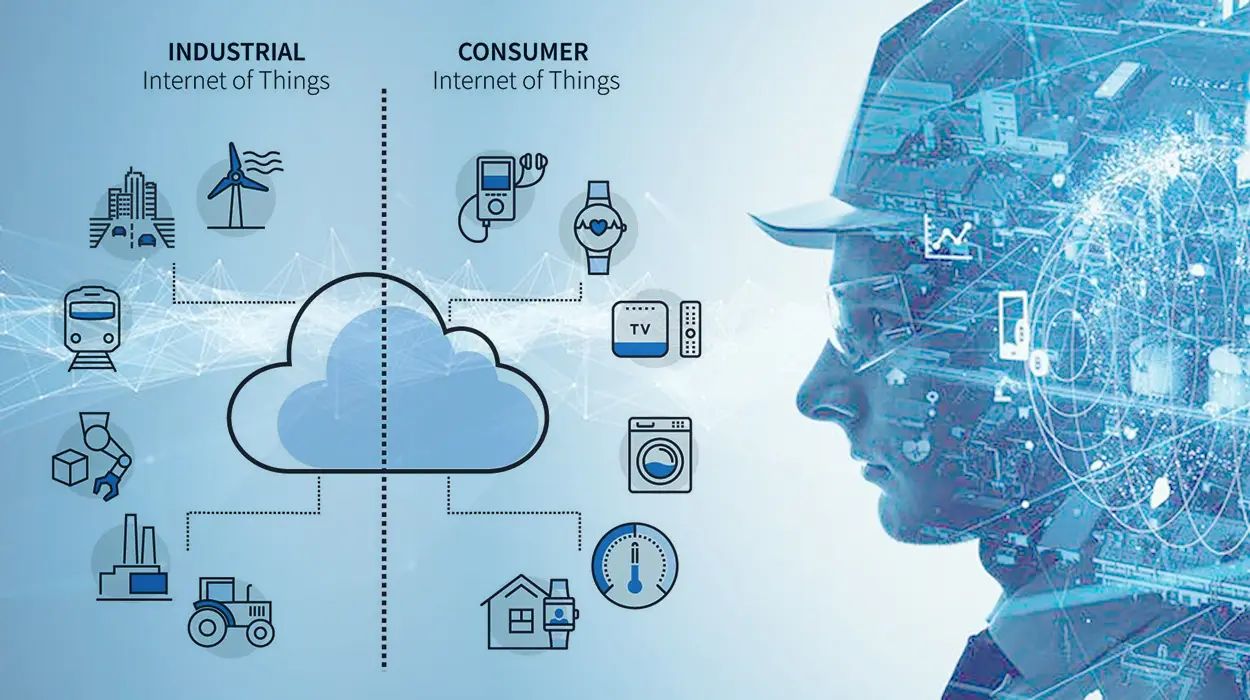
The Internet of Things (IoT) refers to the interconnected network of physical objects or devices that are embedded with sensors, software, and other technologies, enabling them to collect and exchange data over the internet. These devices can range from everyday objects such as smartphones, watches, and home appliances to more complex systems used in industries like healthcare, transportation, and manufacturing.
The key concept behind IoT is the ability of these devices to communicate with each other and with users, creating a seamless and efficient ecosystem. By gathering and analyzing data, IoT devices can provide valuable insights, automate processes, and optimize various aspects of our lives. Whether it’s controlling the temperature in your home remotely, monitoring your heart rate during exercise, or tracking inventory in a warehouse, IoT devices have the potential to revolutionize the way we live and work.
The primary components of an IoT system include:
- Sensors and Actuators: These are the physical components that collect data from the environment or perform actions based on received instructions. Sensors can detect changes in temperature, light, pressure, or other variables, while actuators can perform actions like opening or closing doors, turning on lights, or adjusting settings.
- Connectivity: IoT devices rely on various communication technologies to connect with each other and with other systems. This can include Wi-Fi, Bluetooth, cellular networks, or even satellite connections.
- Data Processing: The collected data is transmitted to cloud-based servers or local systems, where it is processed and analyzed to derive meaningful insights and trigger appropriate actions.
- User Interface: IoT devices often have interfaces that allow users to interact with them, either directly through a control panel or remotely via smartphones, tablets, or web applications.
The potential applications of IoT are vast and continue to expand. From smart homes and cities to healthcare monitoring, industrial automation, and environmental conservation, IoT has the power to transform industries and improve our quality of life. However, with this increased connectivity and data exchange comes significant security and privacy challenges, which need to be addressed to ensure a safe and secure IoT ecosystem.
The Growing Popularity of IoT Devices
Over the past decade, there has been an exponential growth in the popularity and adoption of Internet of Things (IoT) devices. This can be attributed to several factors, including advancements in technology, increased connectivity, and the demand for automation and convenience in our daily lives.
One of the primary drivers behind the surge in IoT devices is the rapid advancement of wireless communication technologies. The widespread availability and affordability of high-speed internet and the proliferation of smartphones have created a fertile ground for IoT to flourish. With wireless connectivity becoming more accessible, it has paved the way for the seamless integration and control of IoT devices in homes, offices, and industries.
The rise of smart homes has played a significant role in the increasing popularity of IoT devices. Homeowners now have the ability to control their lights, thermostats, security cameras, and even appliances through voice commands or mobile apps. This level of convenience and automation has not only improved the quality of life but has also contributed to energy savings and increased home security.
Moreover, IoT devices have found their way into various industries, revolutionizing processes and operations. The healthcare sector, for example, has embraced IoT devices to remotely monitor patients’ health conditions, improving patient care and reducing hospital readmissions. Industrial IoT applications have enabled predictive maintenance, optimizing the performance and uptime of machinery and equipment, ultimately reducing downtime and costs.
Another contributing factor to the growing popularity of IoT devices is the increasing consumer demand for connected and intelligent products. From wearable fitness trackers that monitor our health to voice-activated personal assistants that can answer questions and control other smart devices, consumers are embracing the convenience and interconnectedness that IoT devices provide. Additionally, the rapid growth of e-commerce has made it easier than ever to purchase and install IoT devices, further fueling their popularity.
The COVID-19 pandemic has further accelerated the adoption of IoT devices. With the need for remote work and social distancing measures, individuals and businesses have turned to IoT solutions for virtual collaboration, remote monitoring, and contactless operations. From video conferencing tools to smart temperature sensors in public spaces, IoT devices have played a crucial role in mitigating the impact of the pandemic.
As the number of IoT devices continues to grow, it is important to acknowledge and address the security and privacy risks associated with their use. The next sections will explore these risks and provide insights into securing IoT devices to ensure a safe and protected digital environment.
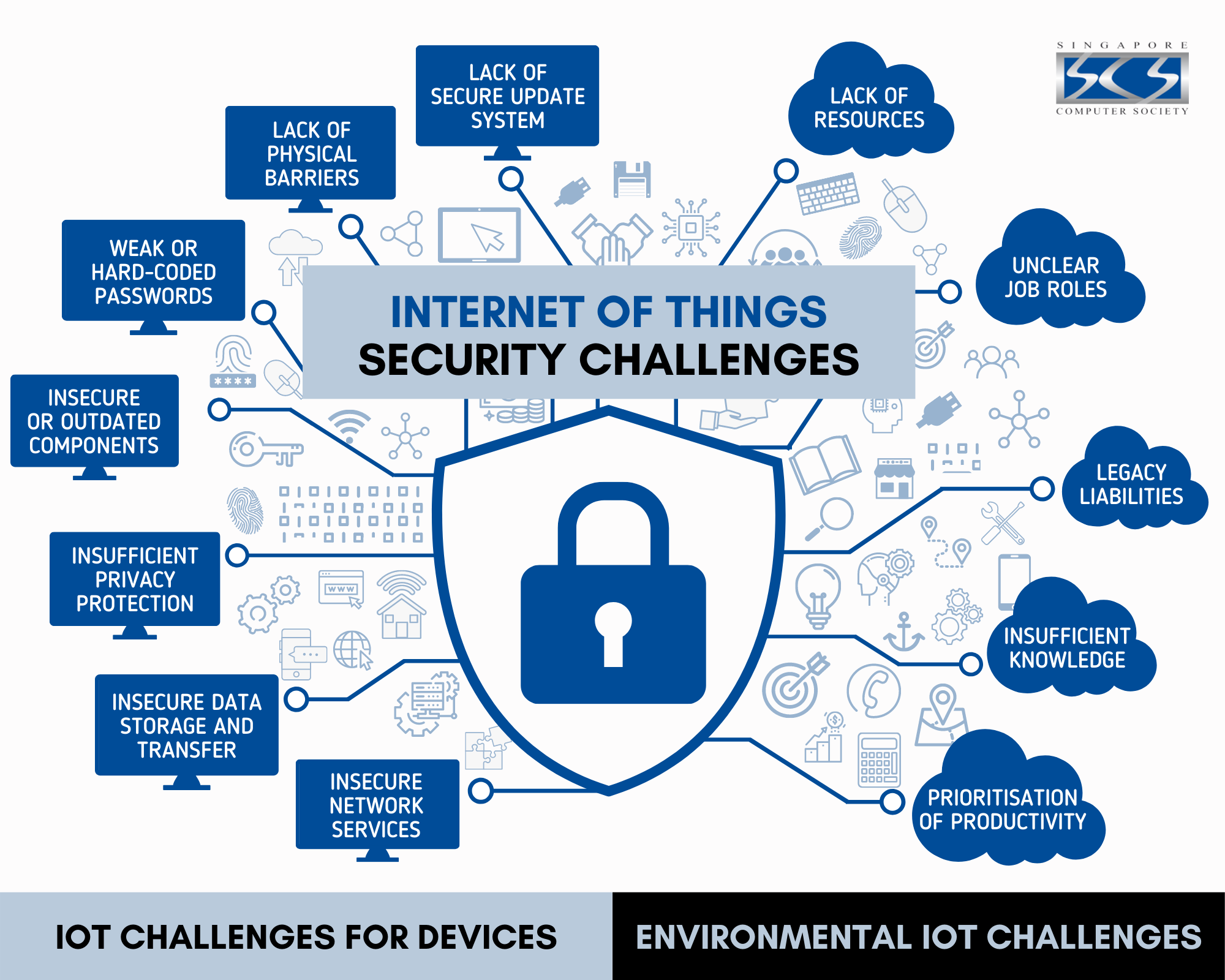
Security Risks and Vulnerabilities of IoT Devices
While the Internet of Things (IoT) has brought about numerous benefits, it has also introduced significant security risks and vulnerabilities. The interconnected nature of IoT devices and the vast amount of sensitive data they collect and transmit make them attractive targets for cybercriminals. Understanding these risks is crucial in order to protect our personal and business security.
One of the primary security risks of IoT devices is weak or default passwords. Many IoT devices come with default usernames and passwords that users often neglect to change. Attackers can exploit this by gaining unauthorized access to the devices and controlling them remotely. This could lead to privacy breaches, manipulation of device settings, or even turning the devices into botnets for launching large-scale attacks.
Another vulnerability lies in the lack of firmware updates and security patches. IoT devices often have complex software systems that require regular updates to fix security issues and vulnerabilities. However, manufacturers may not provide timely updates, or users may neglect to install them. This leaves the devices exposed to known vulnerabilities that can be exploited by attackers.
Additionally, IoT devices typically have limited computational power and memory, which can make implementing strong security measures challenging. Many devices prioritize functionality and ease of use over robust security. This can result in inadequate encryption protocols, weak authentication mechanisms, and other vulnerabilities that can be exploited by hackers.
The sheer number of IoT devices and the diversity of manufacturers also contribute to security risks. With numerous vendors producing IoT devices, ensuring consistent security practices and standards can be difficult. Some manufacturers may not prioritize security in their product development lifecycle, leading to inherent vulnerabilities in the devices.
Furthermore, the scale and complexity of IoT systems can introduce challenges in monitoring and securing the entire network. Each connected device represents a potential entry point for attackers. If one device is compromised, it can be used as a stepping stone to gain access to other devices or the broader network, posing significant risks to data confidentiality and integrity.
IoT devices’ reliance on communication protocols can be exploited by attackers as well. Man-in-the-middle attacks, where an attacker intercepts and alters data exchanged between devices, can compromise the security and privacy of user information. Additionally, IoT devices that transmit data over unsecured networks or without proper encryption mechanisms are susceptible to eavesdropping and data interception.
These security risks and vulnerabilities call for robust security measures and proactive management of IoT devices. The following sections will delve into strategies to secure IoT devices and mitigate these risks to safeguard our personal and business security.
Data Privacy Concerns
As Internet of Things (IoT) devices continue to proliferate in our homes, workplaces, and public spaces, data privacy has become a major concern. IoT devices collect vast amounts of data about our behaviors, preferences, and even our physical surroundings. This data often includes personal and sensitive information, making it imperative to address the privacy risks associated with IoT device usage.
One of the primary data privacy concerns is the potential for unauthorized data collection and sharing. IoT devices constantly gather data from their surroundings, which can include personal identifiers, location data, and even audio or video recordings. There is a fear that this data could be used by companies or malicious actors for surveillance, targeted advertising, or other invasive purposes without the user’s consent.
Additionally, the sheer volume and variety of data collected by IoT devices pose challenges in terms of storage and processing. It raises concerns about where the data is stored, who has access to it, and how long it is retained. Inadequate data storage and management practices can increase the risk of data breaches and unauthorized access.
The sharing of data between IoT devices and third-party applications or platforms also raises privacy concerns. IoT devices often rely on cloud services or mobile apps to function effectively. However, when data is transmitted or shared with these external entities, there is a risk that the data could be used, sold, or mishandled without the user’s knowledge or consent.
Furthermore, IoT devices that communicate with each other and form interconnected networks raise the possibility of data leakage. The data exchanged between devices can be intercepted or accessed by unauthorized parties if adequate security measures, such as encryption, are not in place.
An additional concern is the potential for identity theft or impersonation through IoT devices. If attackers gain access to IoT devices or the data they collect, they may be able to manipulate or exploit the data to perform identity theft or fraud.
To address these data privacy concerns, it is crucial for both manufacturers and users to take proactive measures. Manufacturers should prioritize privacy by design, implementing robust data protection measures, including data encryption, secure storage, and granular user consent mechanisms. Furthermore, manufacturers should be transparent about the types of data collected, how it is used, and with whom it is shared.
Users also have a responsibility to protect their privacy when using IoT devices. This includes carefully reviewing privacy settings, reading and understanding privacy policies, and regularly updating passwords and device firmware.
Government and regulatory bodies play a vital role in addressing data privacy concerns related to IoT devices. Establishing clear privacy regulations and standards can help protect users’ data and provide guidelines for manufacturers to follow. It is essential for organizations to prioritize user privacy and ensure that the use of IoT devices aligns with applicable privacy laws and regulations.
By addressing data privacy concerns and implementing strong privacy protections, we can enjoy the benefits of IoT devices while maintaining control over our personal information and ensuring our privacy rights are respected.
Lack of Standardization and Regulation
One of the significant challenges in the realm of Internet of Things (IoT) is the lack of standardization and regulation. The rapid growth of IoT devices and the diverse range of manufacturers have resulted in a fragmented ecosystem with varying degrees of security, compatibility, and interoperability.
Without standardized protocols and frameworks, IoT devices often struggle to communicate and work seamlessly with each other. This lack of interoperability hinders the potential for IoT to truly deliver its promised benefits. Users may find themselves locked into a specific ecosystem, limiting their choices and the ability to integrate devices from different manufacturers. This not only creates inconvenience but also poses security risks, as incompatible devices may introduce vulnerabilities when forced to work together.
Moreover, the absence of consistent security standards for IoT devices leaves users vulnerable to potential threats. With no universal guidelines to follow, manufacturers may prioritize functionality and cost over security measures, putting users’ data and privacy at risk. This lack of standardized security practices can also hinder effective management and monitoring of IoT devices, making it challenging for users to identify and address security concerns.
Furthermore, the rapid pace of technological advancements means that regulatory bodies struggle to keep up with the evolving IoT landscape. Existing regulations may be outdated or not specifically tailored to address the unique security and privacy challenges posed by IoT devices. This regulatory gap leads to uncertainty and a lack of enforceable standards that can help ensure the safe and ethical use of IoT technology.
However, the need for standardization and regulation is increasingly recognized by industry stakeholders and policymakers. Efforts are being made to establish frameworks and guidelines to address the challenges posed by IoT. Organizations and consortia are working towards developing interoperability standards and protocols to improve device compatibility and security.
Regulatory bodies are also taking steps to address the gaps in IoT regulations. Privacy laws, such as the General Data Protection Regulation (GDPR) in the European Union, focus on protecting individuals’ data privacy and provide guidelines on data collection, storage, and consent. Additionally, regulatory bodies are exploring the potential for industry-specific regulations and frameworks to address the unique challenges posed by IoT devices in sectors such as healthcare, transportation, and smart cities.
Standardization and regulation are essential to create a secure and trustworthy IoT ecosystem. They provide guidelines for manufacturers to develop secure and interoperable devices, and they empower users with the knowledge and confidence to make informed decisions about IoT technology.
Going forward, it is crucial for industry stakeholders, regulatory bodies, and policymakers to collaborate and drive the development and implementation of standardized security measures and regulations. This will create a more reliable and secure IoT environment, ensuring that IoT devices can be safely integrated into our daily lives and businesses without compromising on privacy and security.
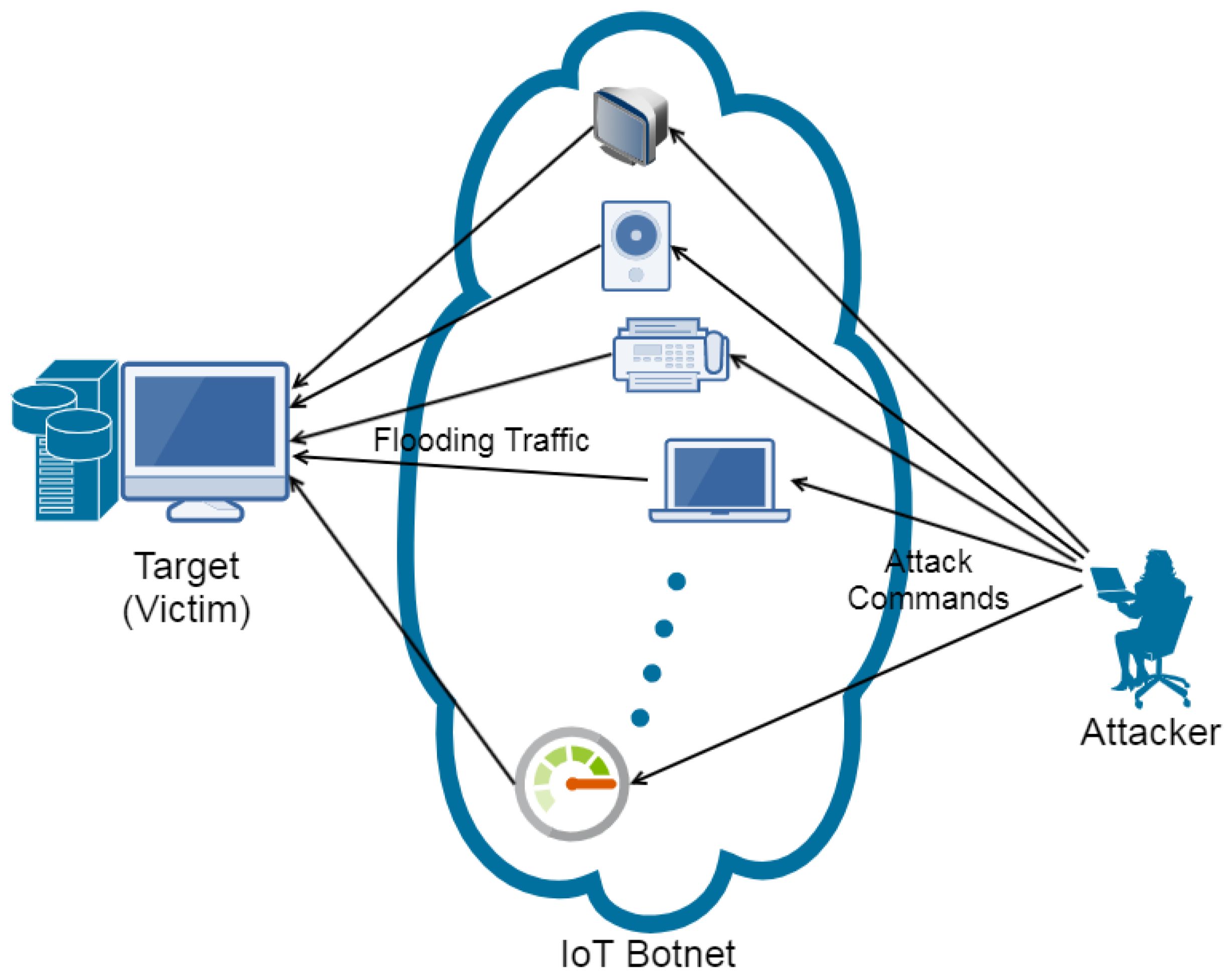
Botnet Attacks and DDoS Attacks
Botnet attacks and Distributed Denial of Service (DDoS) attacks pose significant threats to the security and stability of Internet of Things (IoT) devices and networks. These attacks leverage the interconnected nature of IoT devices to launch large-scale attacks that can disrupt services, compromise data, and cause financial losses.
A botnet is a network of compromised devices that are under the control of a malicious actor. These devices, often IoT devices, are infected with malware that allows the attacker to remotely control them without the owners’ knowledge. The attacker can then use the botnet to carry out various malicious activities, including launching DDoS attacks.
In a DDoS attack, the attacker overwhelms a target system or network by flooding it with an enormous volume of traffic from multiple sources. IoT devices, such as cameras, routers, and smart home devices, are often targeted due to their large numbers and limited security measures. The attacker exploits vulnerabilities in these devices to compromise them and turn them into unwitting participants in the attack.
By coordinating the compromised devices within the botnet, the attacker can direct a massive amount of traffic towards the target, effectively rendering it unavailable to legitimate users. This can have severe consequences for businesses that rely on their online presence, such as e-commerce websites or online service providers.
Botnet and DDoS attacks not only disrupt services but also have a broader impact on the internet infrastructure. They can saturate network bandwidth, degrade performance, and impact the availability of critical services. Furthermore, the collateral damage caused by these attacks can extend beyond the targeted organization to affect other innocent parties sharing the same network or infrastructure.
The widespread use of IoT devices with weak security measures and default passwords makes them an attractive target for attackers looking to build and control botnets. In many cases, users fail to change the default credentials, making it easier for attackers to take control of these devices. Additionally, the lack of firmware updates and patch management for IoT devices leaves them vulnerable to being exploited and used in botnet and DDoS attacks.
Efforts have been made to mitigate the risks associated with botnet and DDoS attacks on IoT devices. Manufacturers are increasingly focusing on improving device security by implementing stronger authentication mechanisms, regular firmware updates, and monitoring for suspicious activity. Users should also take proactive steps, such as changing default credentials, keeping devices updated, and employing network security measures like firewalls and intrusion detection systems.
Furthermore, network and internet service providers play a crucial role in detecting and mitigating botnet and DDoS attacks. They can implement traffic monitoring and filtering solutions to detect abnormal traffic patterns and block suspicious requests. Collaboration between industry stakeholders, governments, and law enforcement agencies is crucial to combat these attacks effectively and hold perpetrators accountable.
Protecting IoT devices from being compromised and used in botnet and DDoS attacks is vital for maintaining a secure and resilient IoT ecosystem. By implementing robust security measures, raising awareness among users, and promoting collaboration across the industry, we can reduce the risks associated with these attacks and ensure the integrity and availability of IoT services.
Impact on Personal and Business Security
The proliferation of Internet of Things (IoT) devices has significant implications for both personal and business security. While these devices offer convenience and enhance our daily lives, they also introduce new vulnerabilities and potential risks that can compromise the security of individuals and organizations.
On a personal level, the security of IoT devices directly affects the privacy and safety of individuals and their homes. IoT devices, such as smart locks, security cameras, and voice assistants, are often interconnected, creating an ecosystem that can be exploited by attackers. Breaches in these devices can lead to unauthorized access to personal information, surveillance, and even physical harm. For example, compromised home security systems can provide valuable insight to potential burglars, posing a direct threat to personal safety.
Personal data collected by IoT devices can also be used for targeted attacks and identity theft. Attackers may exploit vulnerabilities in IoT devices to gain access to sensitive information or manipulate device settings. Furthermore, unauthorized data collection and sharing by manufacturers or third-party applications can result in privacy violations and the potential for data misuse or abuse.
From a business perspective, the security of IoT devices is crucial for maintaining the integrity and confidentiality of sensitive corporate data. Many organizations rely on IoT devices for various purposes, such as monitoring environmental conditions, controlling production processes, or managing inventory. A breach or compromise in these devices can not only disrupt operations but also lead to significant financial losses and reputational damage.
IoT devices used in industrial settings, such as manufacturing plants or critical infrastructure, present unique security challenges. A successful attack on IoT devices controlling critical systems can have severe consequences, including physical damage, operational disruptions, and potential risks to public safety.
Moreover, IoT devices can serve as entry points for cyber attackers to gain unauthorized access to corporate networks. Once inside the network, attackers can move laterally, compromising other systems and stealing sensitive data. This highlights the importance of securing IoT devices as part of a comprehensive cybersecurity strategy.
For both personal and business security, the impact of compromised IoT devices extends beyond the immediate consequences. The loss of trust and confidence in IoT technology can hinder the further adoption and realization of its full potential. Users may become hesitant to embrace the benefits of IoT devices, fearing the potential risks and vulnerabilities associated with them.
To mitigate the impact on personal and business security, it is imperative for users and organizations to take proactive measures. This includes ensuring that IoT devices are purchased from reputable manufacturers, implementing strong security measures such as unique and strong passwords, regularly updating firmware and software, and segmenting IoT devices from critical networks. Additionally, education and awareness about the potential risks, privacy concerns, and best security practices surrounding IoT devices are crucial for users to make informed decisions and take appropriate actions.
Industry collaboration, research, and regulatory initiatives play a vital role in addressing the evolving security challenges posed by the IoT landscape. By aligning efforts, establishing standards, and driving innovation in IoT security, we can enhance the personal and business security of IoT devices and foster a secure and trustworthy IoT ecosystem.
Securing IoT Devices
Securing Internet of Things (IoT) devices is essential to protect against the growing security risks and vulnerabilities they pose. With the increased connectivity and data exchange, it is crucial for users and manufacturers to implement robust security measures throughout the lifecycle of IoT devices.
One of the first steps in securing IoT devices is to ensure strong authentication and access controls. Default usernames and passwords should be changed to unique and strong credentials. Two-factor authentication (2FA) should be enabled whenever possible to add an extra layer of security. Additionally, manufacturers should implement secure firmware and software update mechanisms to address vulnerabilities as they are discovered.
Data encryption is another critical aspect of securing IoT devices. All sensitive data should be encrypted both at rest and in transit to protect against unauthorized access and interception. Encryption protocols should be implemented following industry best practices, and strong encryption algorithms should be used to ensure data confidentiality.
Network segmentation is a technique that helps isolate IoT devices from critical systems and networks. By separating IoT devices into their own network segment, the impact of a compromised device can be limited. Access controls and traffic monitoring can be implemented to prevent unauthorized access to critical systems through IoT devices.
Regular monitoring and analysis of IoT devices’ activity and network traffic can help detect and respond to security incidents promptly. Intrusion detection and prevention systems (IDPS) can detect suspicious behavior and alert users or security teams. Additionally, logging and auditing can provide valuable forensic information in the event of a security breach or incident.
Implementing stringent physical security measures is also important for protecting IoT devices. Devices should be physically secured to prevent unauthorized access or tampering. Physical safeguards can include secure mounting, tamper-evident seals, and controlled access to device locations.
Adherence to security best practices and standards is crucial for both manufacturers and users. Manufacturers should prioritize security in the design and development of IoT devices, implementing secure coding practices and adhering to recognized security standards. Users, on the other hand, should stay informed about the latest security threats and vulnerabilities, regularly update device firmware, and follow recommended security guidelines provided by manufacturers.
Collaboration and information sharing among stakeholders are key to staying ahead of evolving security threats in the IoT ecosystem. Manufacturers, industry consortia, researchers, and government bodies should work together to establish security guidelines, share threat intelligence, and proactively address emerging vulnerabilities.
Lastly, user education and awareness are fundamental in securing IoT devices. Users should be educated on the potential risks and security best practices related to their devices. This includes understanding how to recognize phishing attempts, regularly reviewing and adjusting privacy settings, and being cautious about granting permissions and sharing sensitive information.
Securing IoT devices requires a multi-layered approach that encompasses technical, physical, and procedural security measures. By implementing these measures and fostering collaboration among stakeholders, we can create a more secure and resilient IoT ecosystem.
Conclusion
The Internet of Things (IoT) has transformed the way we interact with technology, offering convenience and enhancing our daily lives. However, with this increased connectivity and reliance on IoT devices comes significant security risks and vulnerabilities.
In this article, we have explored the major risks associated with IoT devices, including security vulnerabilities, data privacy concerns, the lack of standardization and regulation, and the potential for botnet and Distributed Denial of Service (DDoS) attacks. We have discussed the impact of these risks on both personal and business security and provided insights into securing IoT devices effectively.
To mitigate the risks, securing IoT devices should be a collective effort. Manufacturers should prioritize security by design, implementing robust authentication mechanisms, encryption protocols, and secure firmware updates. They should also prioritize privacy, being transparent about data collection and usage, and providing users with granular control over their personal information.
Users play a crucial role in securing IoT devices by changing default credentials, applying regular firmware updates, and implementing network security measures. Education and awareness are also important for users to recognize potential risks and make informed decisions about their IoT devices.
Moreover, standardization and regulation are vital to ensure the security and interoperability of IoT devices. Collaborative efforts between industry stakeholders, regulatory bodies, and policymakers can establish consistent security practices, privacy regulations, and industry standards.
Addressing the security challenges of IoT devices requires constant vigilance, innovation, and collaboration. By implementing robust security measures, raising awareness, and promoting collaboration, we can create a more secure and resilient IoT ecosystem that safeguards personal and business security.
As IoT technology continues to advance, it is essential to prioritize security and privacy without compromising on innovation and convenience. With a proactive approach and a shared commitment to security, we can confidently embrace the benefits of IoT devices, knowing that our personal and business security is protected in the interconnected world of the Internet of Things.