Introduction
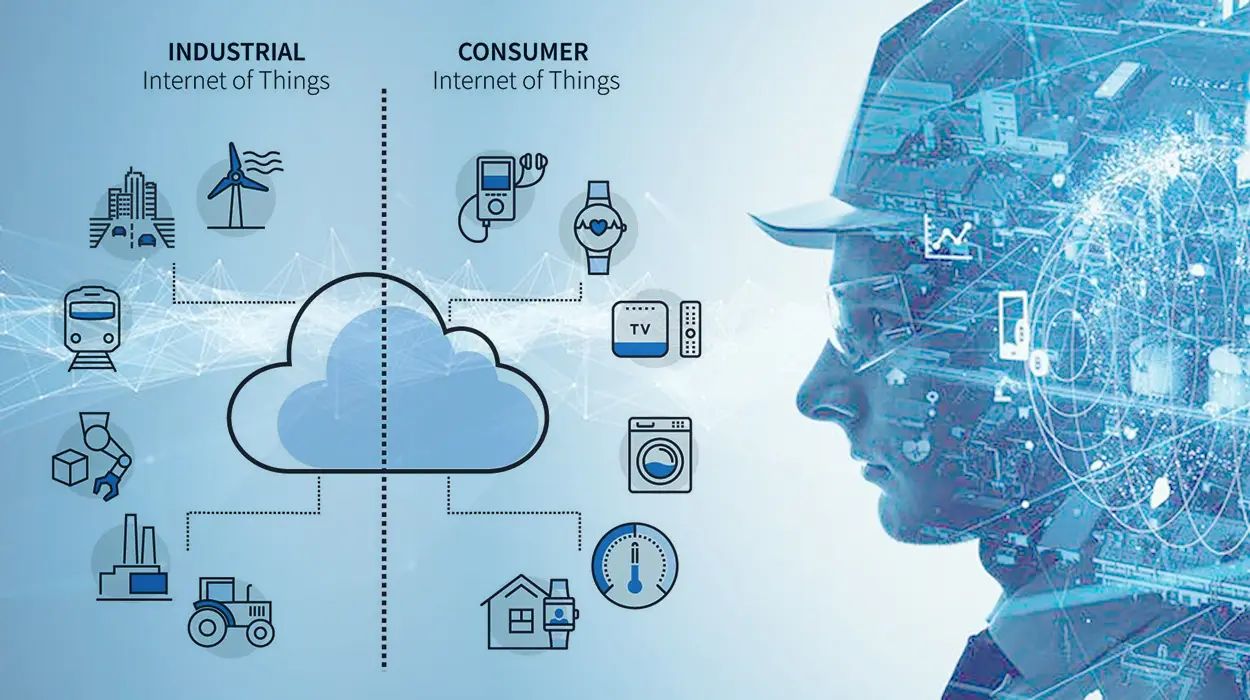
The Internet of Things (IoT) has revolutionized the way we live and interact with technology. It refers to the network of physical objects, such as appliances, vehicles, and wearable devices, that are embedded with sensors, software, and connectivity, allowing them to collect and exchange data. While IoT devices offer numerous benefits, such as increased convenience and efficiency, their widespread adoption has raised significant concerns.
In this article, we will explore two major concerns regarding IoT devices – data security and privacy. The rapid proliferation of connected devices has led to an exponential increase in data being generated and exchanged. This massive amount of data creates vulnerabilities that can be exploited by malicious actors. Additionally, the interconnected nature of IoT devices amplifies the risks associated with data breaches, as a single compromised device can potentially compromise an entire network.
Data Security:
One of the primary concerns regarding IoT devices is data security. These devices operate by constantly collecting and transmitting data, making them attractive targets for cybercriminals. The data collected by IoT devices can include personal information, sensitive financial data, and even physical location data. Without robust security measures in place, this data can be intercepted, stolen, or manipulated, leading to serious consequences such as identity theft, financial loss, or even physical harm.
Privacy Concerns:
In addition to data security, privacy is a major concern associated with IoT devices. IoT devices are designed to constantly monitor and track user behavior in order to provide personalized experiences and automate certain tasks. However, this poses significant privacy risks, as users may be unaware of the extent to which their personal information is being collected and shared. Furthermore, data collected by one IoT device can potentially be combined with data from other devices to create detailed profiles of individuals, raising questions about consent, ownership, and control over personal data.
The potential consequences of inadequate data security and privacy measures in IoT devices are far-reaching. From personal privacy infringements to compromise of sensitive corporate information, the risks are significant. In order to address these concerns, it is crucial for device manufacturers, developers, and policymakers to prioritize the implementation of robust security protocols, data encryption, and user consent mechanisms.
In the following sections, we will delve deeper into the specific concerns and challenges posed by IoT devices, including the lack of standards and interoperability, vulnerability to cyberattacks, limited lifespan and compatibility issues, lack of user awareness and understanding, as well as the ethical and legal implications surrounding IoT.
Data Security
Data security is a critical concern when it comes to IoT devices. As these devices constantly collect and transmit data, they become targets for cybercriminals seeking to exploit vulnerabilities and gain unauthorized access to sensitive information. The sheer volume of data generated by IoT devices, coupled with the interconnectivity among different devices, amplifies the risks associated with data breaches.
One of the primary challenges regarding data security in IoT devices is the lack of standardized protocols and security measures. With a wide array of IoT devices on the market, each having its own unique characteristics and operating systems, it becomes difficult to implement uniform security practices across all devices. This results in inconsistencies in security measures and leaves many devices vulnerable to attacks.
Another challenge is the issue of data encryption. Many IoT devices transmit data over wireless networks, making it susceptible to interception by hackers. Without adequate encryption measures, sensitive information can be easily accessed, putting user privacy at risk. Additionally, the storage and processing capabilities of IoT devices are often limited, which means that implementing robust encryption algorithms can be challenging.
The complex nature of IoT ecosystems also introduces potential vulnerabilities. As different devices communicate with each other, a security breach in one device can have a ripple effect across the entire network. For example, a compromised smart home security camera could provide hackers with access to other connected devices, such as door locks or thermostats, putting the entire household at risk.
Furthermore, IoT devices often have a long lifespan, which means that security updates and patches may not be regularly released by manufacturers. This leaves devices running outdated software, making them more susceptible to new and evolving cyber threats. In some cases, users may not even be made aware of security vulnerabilities in their devices until it is too late.
To mitigate these concerns, it is essential for manufacturers to prioritize incorporating robust security features into IoT devices from the design phase. Implementing strong authentication mechanisms, encryption protocols, and regular firmware updates can significantly enhance the security posture of these devices. Additionally, educating users about the importance of regularly updating their devices and practicing good cybersecurity hygiene can help prevent exploitation.
Overall, data security in IoT devices is a multifaceted challenge that requires a comprehensive approach. By addressing issues such as standardized protocols, data encryption, device interconnectivity, regular updates, and user education, we can strive towards ensuring the privacy and security of IoT devices and the data they collect.
Privacy Concerns
Privacy is a significant concern when it comes to IoT devices. These devices are designed to collect vast amounts of data about users’ behaviors, habits, and preferences in order to deliver personalized experiences and automate tasks. However, this constant monitoring raises questions about the extent to which personal information is collected, shared, and used without the explicit consent or knowledge of the users.
One of the main issues surrounding privacy in IoT devices is the lack of transparency regarding data collection and usage. Many users are unaware of the types of data collected by their IoT devices, how it is being shared with third parties, and for what purposes it is being used. This lack of transparency can erode trust and create concerns about potential misuse of personal information.
Furthermore, the combination of data from multiple IoT devices can paint a comprehensive picture of individuals’ lives. For example, by aggregating data from smart speakers, fitness trackers, and home security systems, a detailed profile can be created, including information about people’s daily routines, personal preferences, and even health conditions. This raises concerns about the potential for unauthorized access, exploitation, or abuse of such detailed personal profiles.
IoT devices also introduce challenges in terms of consent and control over personal data. Given the continuous nature of data collection, users may not explicitly provide consent for every piece of information collected. Additionally, it may be difficult for users to control and manage their data across multiple devices, especially when data is stored in the cloud or shared with third-party service providers.
The sharing of data with third-party service providers is another aspect that can compromise privacy. IoT devices often rely on cloud-based services to store and process data, which means that sensitive information is transmitted and stored outside of users’ control. This raises concerns about data security and the potential for unauthorized access or data breaches by third parties.
Addressing privacy concerns in IoT devices requires a multi-faceted approach. Device manufacturers should prioritize incorporating privacy-by-design principles into the development process. This includes implementing privacy settings and controls, providing clear and concise privacy policies, and allowing users to easily access and manage their data.
Additionally, industry-wide standards and regulations can play a crucial role in safeguarding privacy in IoT devices. Governments and regulatory bodies can establish guidelines for data collection, usage, and storage, as well as enforce stringent security measures to protect user privacy. Implementing mechanisms for user consent, anonymization of data, and data minimization can also help address privacy concerns.
Ultimately, balancing the benefits of IoT devices with the privacy rights of individuals is of utmost importance. By adopting privacy-centric practices, promoting transparency, and empowering users to have control over their personal data, we can ensure that IoT devices respect and protect user privacy.
Lack of Standards and Interoperability
A key challenge in the realm of IoT devices is the lack of standardized protocols and interoperability. With a wide variety of devices from different manufacturers operating on different platforms and utilizing different communication protocols, achieving seamless integration and communication between devices can be a complex task.
The absence of a universal set of standards and protocols poses several issues. Firstly, it hinders the ability of different IoT devices to communicate with each other effectively. For example, a smart home security system may not be compatible with a smart thermostat from a different brand, limiting the potential for interoperability and automation within the home ecosystem.
This lack of interoperability also restricts the potential for IoT devices to work together to provide more comprehensive solutions. For instance, a healthcare monitoring device may not be able to seamlessly integrate with a hospital’s electronic health record system, limiting the exchange of vital patient information and hindering the delivery of efficient and coordinated care.
Furthermore, the absence of uniform standards can lead to fragmentation within the IoT market. Different manufacturers develop their own proprietary platforms, resulting in a multitude of incompatible ecosystems. This fragmentation not only creates confusion for consumers but also stifles innovation, as developers are required to invest significant resources in adapting their solutions to multiple platforms.
The lack of standards and interoperability in IoT devices also raises concerns about security and privacy. In the absence of standardized security protocols, vulnerabilities specific to individual platforms or devices may go unnoticed or unaddressed, leaving them open to potential attacks. Additionally, the inability to securely exchange data between devices due to a lack of interoperability can hinder the implementation of robust data protection measures.
To address these challenges, industry players, standards organizations, and regulatory bodies must come together to establish and promote universal interoperability standards for IoT devices. These standards should encompass communication protocols, security measures, and data exchange formats, enabling seamless integration and communication between devices from different manufacturers.
Standardizing protocols and interoperability will not only enhance the user experience but also foster innovation and market growth. Developers would be able to focus on creating value-added services and applications instead of spending resources on adapting their solutions to multiple platforms and ecosystems.
Furthermore, standards and certification programs can provide a framework for ensuring security and privacy in IoT devices. By adhering to standardized practices and protocols, manufacturers can build more secure and resilient devices that protect user data and privacy.
In summary, the lack of standards and interoperability in IoT devices poses significant challenges in terms of device connectivity, integration, and security. Establishing universal standards and protocols will not only enable seamless communication between devices but also enhance security, foster innovation, and promote market growth in the IoT industry.
Vulnerability to Cyberattacks
One of the most pressing concerns associated with IoT devices is their vulnerability to cyberattacks. These devices are often connected to the internet and collect vast amounts of data, making them attractive targets for hackers seeking to exploit security weaknesses. The interconnected nature of IoT devices further amplifies the risks and potential impact of cyberattacks.
One major vulnerability is the lack of built-in security features in many IoT devices. Manufacturers often prioritize functionality and time-to-market over security, resulting in devices with weak or non-existent security measures. For example, default passwords are often used, which are easily guessable or even publicly known, leaving devices susceptible to unauthorized access.
The large-scale deployment of IoT devices also creates a wider attack surface for cybercriminals. With numerous devices interconnected in a network, a single compromised device can act as a stepping stone to gain access to other devices or even the entire network. This can lead to devastating consequences, such as unauthorized access to sensitive data, disruption of critical systems, or the launching of further attacks.
Additionally, IoT devices often lack timely security updates and patches. With long lifecycles and a multitude of different devices on the market, manufacturers may not prioritize or provide regular security updates for their devices. This leaves devices running outdated software, making them more vulnerable to new and emerging cyber threats.
Another vulnerability lies in the communication channels used by IoT devices. Many devices transmit data over wireless protocols, such as Wi-Fi or Bluetooth, which can be intercepted by hackers. Without proper encryption and secure communication protocols, the data exchanged between devices can be compromised, leading to potential privacy breaches or manipulation of data.
Moreover, the use of third-party services and cloud platforms introduces additional attack vectors. IoT devices often rely on external services for data storage and processing, and these services may have their own vulnerabilities. A breach in these services can result in unauthorized access to the data collected by IoT devices, exposing users to privacy risks and potential misuse of their personal information.
To address the vulnerability of IoT devices to cyberattacks, manufacturers need to prioritize security as a fundamental aspect of device design and development. This includes implementing robust authentication mechanisms, encryption protocols, and secure communication channels. Regular security updates and patches should also be provided to protect devices from emerging threats.
Furthermore, collaboration among manufacturers, security researchers, and regulatory bodies is essential in identifying and addressing vulnerabilities in IoT devices. Creating industry-wide security standards and guidelines can help ensure that devices meet a minimum level of security requirements and undergo regular security assessments.
Lastly, user education and awareness play a crucial role in mitigating cyber risks associated with IoT devices. Users should be educated on best practices for securing their devices, such as changing default passwords, keeping devices up to date, and being cautious about granting permissions and sharing personal information.
By addressing the vulnerabilities present in IoT devices, we can enhance the security and resilience of these devices and protect users from the potentially devastating consequences of cyberattacks.
Limited Lifespan and Compatibility Issues
The limited lifespan and compatibility issues of IoT devices present significant challenges in terms of sustainability and efficient use of resources. IoT devices, like any other technology, have a finite lifespan, often determined by factors such as technological advancements, changing consumer demands, and the availability of software updates and support.
One issue associated with the limited lifespan of IoT devices is the potential for premature obsolescence. As technology evolves at a rapid pace, newer and more advanced devices enter the market, rendering older devices outdated and incompatible with emerging standards and protocols. This can lead to a significant waste of resources, as consumers are forced to replace their devices frequently to keep up with the latest technology.
Compatibility issues further compound the problem of limited lifespan. With a lack of standardized protocols and communication frameworks, older devices may not be compatible with newer devices or platforms. This can hinder the seamless integration and interoperability between devices, limiting the potential for automation and creating fragmented IoT ecosystems.
Additionally, limited software support and updates contribute to the short lifespan of IoT devices. As manufacturers focus on developing new products and optimizing resources, older devices may no longer receive regular software updates or security patches. This leaves devices running outdated and potentially vulnerable software, making them more susceptible to cyberattacks and compromising user privacy.
The limited lifespan and compatibility issues of IoT devices raise concerns about the overall sustainability and environmental impact. The constant disposal and replacement of devices contribute to electronic waste, which poses challenges in terms of proper disposal and recycling. Moreover, the production and disposal of IoT devices require significant amounts of energy and resources, contributing to carbon emissions and environmental degradation.
To address these challenges, manufacturers need to prioritize the development of IoT devices with longer lifespans and upgradeable software. Designing devices with modular components and software architecture that allows for updates and upgrades can extend the lifespan of devices and reduce the need for frequent replacements.
Standardization efforts also play a crucial role in addressing compatibility issues. By establishing universal protocols and communication frameworks, manufacturers can ensure that devices from different generations and manufacturers can seamlessly communicate and interact with each other. This promotes interoperability, extends the usefulness of older devices and reduces electronic waste.
Furthermore, consumers need to be informed and educated about the lifespan and compatibility issues of IoT devices. Understanding the implications of purchasing devices with limited support and compatibility can help consumers make more informed decisions, considering factors such as long-term value, upgradeability, and environmental impact.
Legislation and regulatory measures can also promote sustainability in the IoT industry. Initiatives such as extended producer responsibility (EPR) can incentivize manufacturers to design devices with longer lifespans, provide software updates and support, and ensure proper disposal and recycling of electronic waste.
By addressing the limited lifespan and compatibility issues in IoT devices, we can promote sustainability, reduce electronic waste, and maximize the value and longevity of these devices. Collaboration among manufacturers, policymakers, and consumers is crucial in driving the necessary changes to create a more sustainable IoT ecosystem.
Lack of User Awareness and Understanding
A significant concern in the realm of IoT devices is the lack of user awareness and understanding regarding these technologies. Many individuals may own and use IoT devices without fully comprehending their capabilities, potential risks, and proper usage. This lack of awareness can lead to potential issues related to privacy, security, and optimal device utilization.
One aspect of concern is users’ limited knowledge about the data that IoT devices collect and how that data is used. Users often do not have a clear understanding of the types of information being collected, the purposes for which it is being used, and the potential implications for their privacy. The lack of transparency from manufacturers and service providers further exacerbates this issue, as users may not have access to clear and concise information about data collection and usage practices.
Another area where user awareness is lacking is cybersecurity. IoT devices, like any connected devices, are susceptible to cyberattacks and unauthorized access. However, users may not prioritize or fully understand the importance of implementing security measures such as strong passwords, regular software updates, and encryption protocols. This can leave their devices and personal information vulnerable to exploitation by malicious actors.
Additionally, users may not be aware of the potential risks associated with using default settings or granting excessive permissions to IoT devices. Certain devices may come with default settings that prioritize ease of use over security, leaving users unaware of the need to change these settings to mitigate risks. Furthermore, users may unknowingly grant extensive permissions to IoT devices, such as access to their location or personal files, without fully understanding the implications and control they have over their own data.
Furthermore, users often lack knowledge about the possibilities and benefits of optimizing their IoT devices for their specific needs. Many IoT devices offer extensive customization and automation options, but users may not fully explore or utilize these features. This can result in underutilization of the devices’ capabilities, limiting the potential efficiency and convenience that IoT technologies can offer.
To address the lack of user awareness and understanding, educational initiatives are crucial. Manufacturers should prioritize providing clear and accessible user manuals and documentation that explain the functionalities, data collection practices, and security measures of their devices. User interfaces should be designed with simplicity and clarity in mind, ensuring that users can easily understand and control their devices’ settings and permissions.
Furthermore, governments and organizations should invest in public awareness campaigns to educate users about the importance of privacy and security when using IoT devices. These campaigns can emphasize the risks associated with default settings, the need for regular software updates, and the significance of creating strong passwords and implementing encryption measures.
User education should also cover topics such as data ownership, data sharing practices, and the importance of reading privacy policies. By understanding their rights and responsibilities, users can make informed choices and take necessary precautions to protect their privacy and security.
In summary, enhancing user awareness and understanding is vital to foster responsible and secure use of IoT devices. Through educational initiatives, clear documentation, simplified user interfaces, and public awareness campaigns, we can empower users to make informed decisions and utilize IoT technologies optimally while protecting their privacy and security.
Ethical and Legal Implications
The rise of IoT devices has brought about numerous ethical and legal implications that need to be carefully considered. As these devices become more integrated into our daily lives, issues surrounding privacy, data ownership, consent, and accountability have come to the forefront.
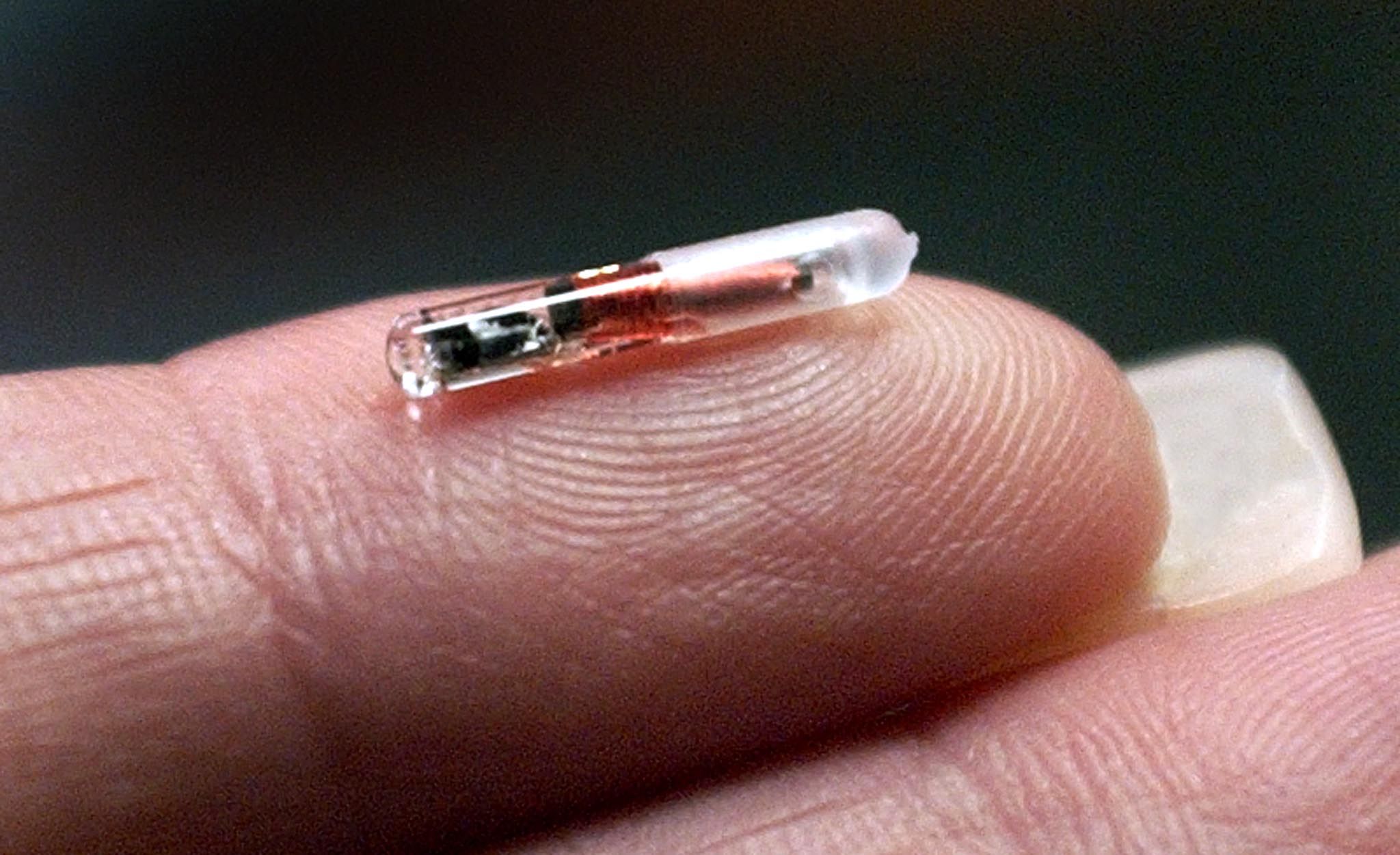
One significant ethical concern is the potential for intrusion into individuals’ privacy. IoT devices collect and transmit vast amounts of personal data, ranging from location information to health and behavioral data. The unauthorized or unethical use of this data can lead to privacy infringements and potential discrimination.
Another ethical consideration is the issue of consent. Users may not fully understand the extent to which their personal information is being collected, shared, and used by IoT devices. Clear and informed consent processes are crucial to ensuring that users are fully aware of what data is being collected and how it will be utilized.
Data ownership is another complex issue in the realm of IoT devices. With the constant collection and transmission of data, questions arise as to who owns and has control over this information. Users should have the right to determine how their data is used, shared, and retained, and manufacturers and service providers should be transparent about the ownership and usage rights of collected data.
Accountability is a key aspect of the ethical implications surrounding IoT devices. In the event of a data breach or misuse of personal information, determining who is responsible and accountable can be challenging. Clear legal frameworks and regulations are necessary to establish liability and accountability for any unethical or illegal activities involving IoT devices.
Legal considerations also come into play when it comes to issues such as data protection, consumer rights, and product liability. Regulations must protect the rights of individuals to control their personal data, ensure that manufacturers adhere to privacy and security standards, and establish mechanisms for compensation and redress in the event of harm or misuse of IoT devices.
Furthermore, ethical considerations extend to the impact IoT devices may have on society as a whole. Issues related to job displacement due to automation, inequality in access to IoT technologies, and the environmental impact of electronic waste are all ethical concerns that need to be addressed.
To address these ethical and legal implications, a multi-faceted approach is required. Governments and regulatory bodies should establish clear and robust legal frameworks that protect user privacy, establish data ownership rights, and define liability and accountability for unethical or illegal activities. Industry collaboration is essential to developing best practices and ethical guidelines for data collection, usage, and retention.
Education and awareness initiatives are crucial to ensuring that individuals understand their rights and responsibilities when using IoT devices. Consumers should be empowered to make informed decisions, understand the potential risks and implications of using IoT devices, and protect their privacy and security interests.
In summary, the ethical and legal implications of IoT devices are complex and multifaceted. By addressing privacy concerns, ensuring clear consent processes, establishing ownership rights over data, and implementing robust legal frameworks, we can foster the responsible and ethical use of IoT technologies while protecting individual rights and societal values.
Conclusion
The proliferation of IoT devices has undoubtedly brought about numerous benefits and advancements in technology. However, it is crucial to address the significant concerns that arise alongside their widespread adoption. The issues related to data security, privacy, lack of standards and interoperability, vulnerability to cyberattacks, limited lifespan and compatibility, lack of user awareness, and ethical and legal implications must be carefully considered and mitigated.
Data security and privacy are paramount concerns when it comes to IoT devices. Robust security measures, encryption protocols, and transparent data collection and usage practices are essential to protect user information and mitigate the risk of data breaches.
The lack of standards and interoperability poses challenges in terms of device connectivity, integration, and security. Establishing universal protocols and standardized frameworks will enhance device compatibility, promote interoperability, and foster innovation in the IoT industry.
The vulnerability of IoT devices to cyberattacks necessitates stronger security measures, regular updates, and patches. Manufacturers should prioritize security in device design and user awareness campaigns to ensure that adequate protection is in place.
Addressing the limited lifespan and compatibility issues of IoT devices requires longer device lifecycles, upgradeable software, and industry-wide collaboration to reduce electronic waste and promote sustainable practices.
Moreover, user awareness and understanding should be prioritized through education and clear documentation to empower individuals to make informed decisions, protect their privacy, and maximize the potential of their IoT devices.
Lastly, ethical and legal implications surrounding IoT devices need to be carefully considered, including issues related to privacy, consent, data ownership, accountability, and the impact on society. By establishing legal frameworks, ethical guidelines, and educating users about their rights and responsibilities, we can ensure the responsible and ethical use of IoT technologies.
In conclusion, as we continue to embrace the benefits of IoT devices, it is crucial to address the concerns that arise alongside their adoption. By addressing data security, privacy, interoperability, vulnerability, lifespan, user awareness, and ethical and legal implications, we can create a more secure, sustainable, and ethical IoT ecosystem that respects individuals’ rights and safeguards their privacy and security.