Introduction
The Internet of Things (IoT) has revolutionized the way we live, enabling everyday objects to connect and interact with each other. From smart homes to wearable devices, IoT has made our lives easier and more efficient. However, with the increasing number of IoT devices being integrated into our lives, security concerns have become a major issue.
Securing IoT devices is crucial to protect our personal information, prevent unauthorized access, and ensure the privacy and integrity of our data. As IoT devices are connected to the internet, they are vulnerable to cyber attacks and security breaches. Therefore, it is essential to understand the common security risks associated with IoT devices and take the necessary steps to make them secure.
This article will guide you through the importance of securing IoT devices and provide practical tips on how to enhance their security. By following these steps, you can significantly reduce the risk of your IoT devices being compromised and protect your digital presence.
Understanding IoT Devices
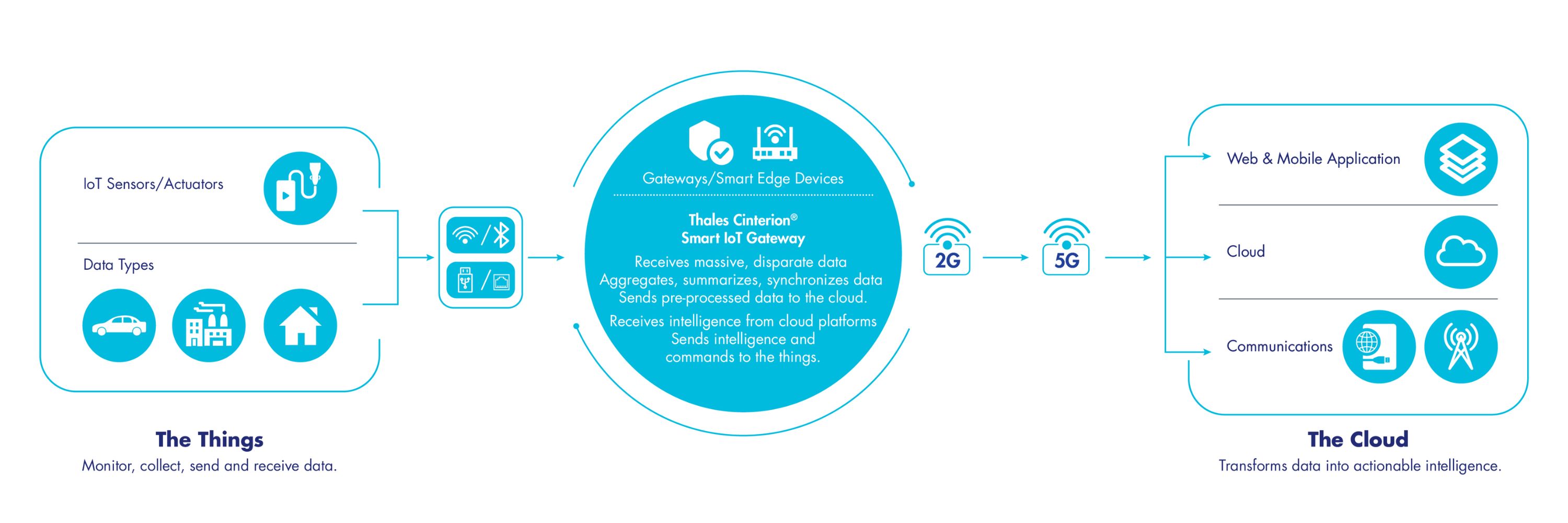
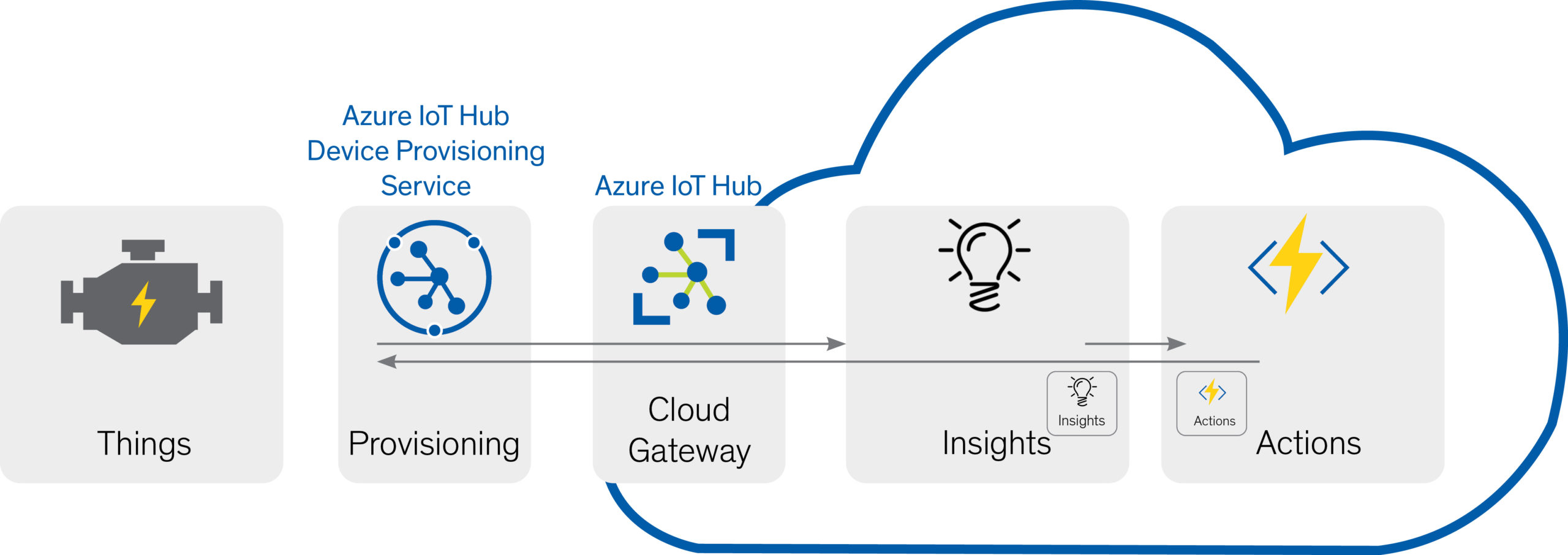
Before diving into the security measures for IoT devices, it’s important to have a basic understanding of what they are and how they function. IoT devices are physical objects embedded with sensors, software, and network connectivity that enable them to collect and exchange data.
These devices come in various forms, including smart thermostats, home security systems, fitness trackers, and even industrial machinery. They are designed to provide convenience, automation, and improved efficiency in various aspects of our lives.
One of the key features of IoT devices is their ability to connect to the internet, allowing users to control and monitor them remotely. This connectivity enables the devices to gather real-time data and communicate with other devices within the IoT network.
However, the inherent connectivity of IoT devices also poses security risks. They become potential entry points for hackers to gain unauthorized access to sensitive data or control the devices themselves. This is why implementing robust security measures is crucial to protect the privacy and integrity of the data transmitted and stored by these devices.
Furthermore, it’s important to note that IoT devices typically have limited computational power and memory, making them more susceptible to security vulnerabilities. These vulnerabilities can be exploited by hackers to launch attacks such as malware infections, data breaches, or even taking control of the devices.
Understanding the vulnerabilities and limitations of IoT devices is a crucial first step in ensuring their security. By being aware of these risks, you can implement effective security measures and safeguard your IoT devices from potential threats.
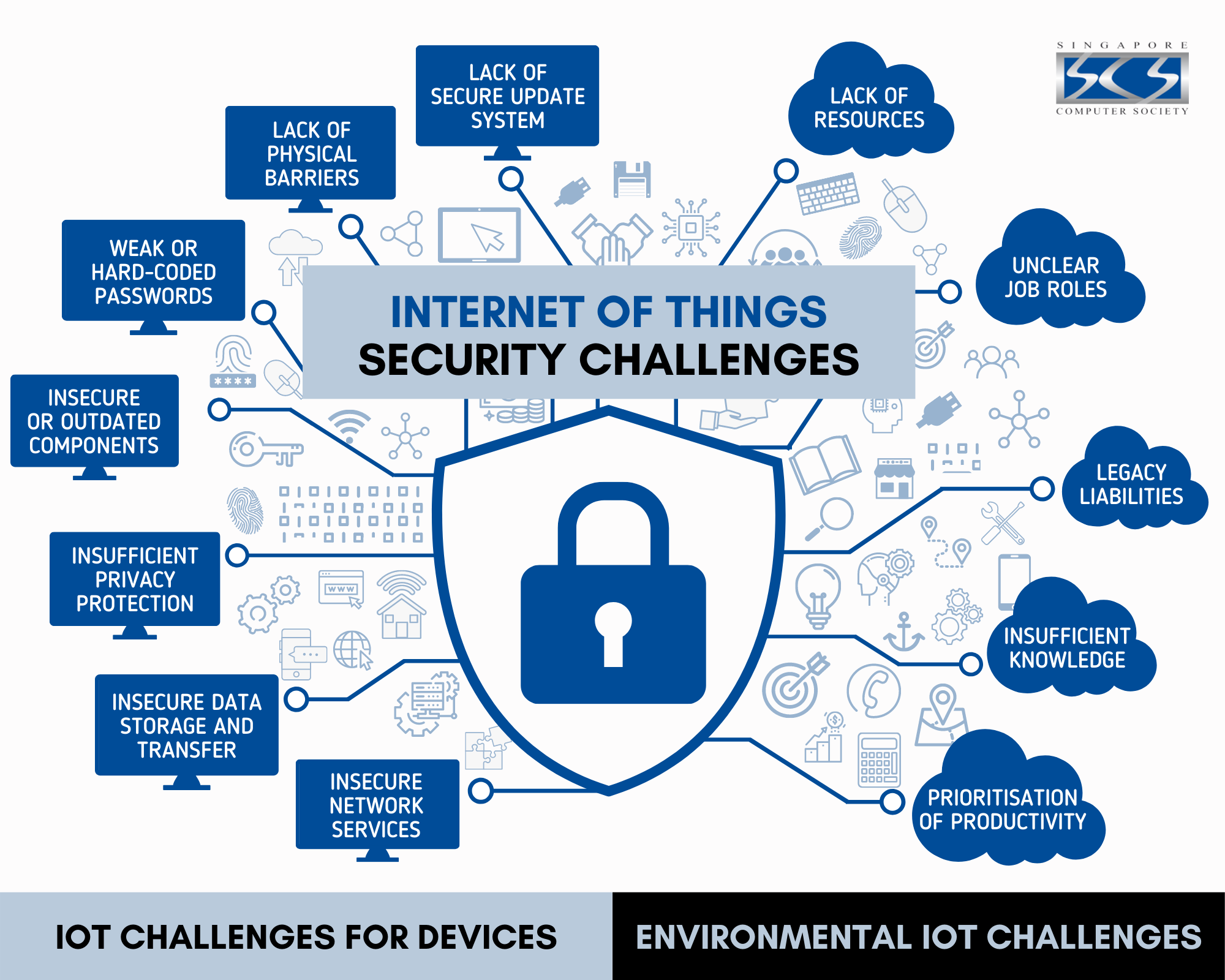
Common Security Risks with IoT Devices
While IoT devices offer numerous benefits, they also come with inherent security risks that need to be addressed. Understanding these common security risks is essential to implement proper security measures and protect your IoT devices.
1. Weak Authentication and Password Protection: Many IoT devices come with default passwords that are easily guessable or widely known. If users fail to change these default credentials, it can leave the devices vulnerable to unauthorized access.
2. Lack of Regular Firmware Updates: Manufacturers often release firmware updates to address security vulnerabilities and improve device performance. Failure to regularly update the firmware can leave devices exposed to known security flaws.
3. Inadequate Data Encryption: Insecure data transmission can expose sensitive information to interception or tampering. Without encryption, hackers can easily access and manipulate the data being transmitted by the IoT devices.
4. Lack of Secure Network Configuration: IoT devices may connect to a home or office network, and if the network is not adequately secured, it can provide an entry point for hackers to gain access to all connected devices.
5. Insufficient Device Authentication: Without proper device authentication protocols, malicious actors can impersonate authorized devices and gain unauthorized control over the network and connected devices.
6. Sensor and Data Privacy Concerns: IoT devices often collect personal and sensitive data. If the devices are not designed with built-in privacy controls, this data can be at risk of being exposed or misused.
7. Physical Security Risks: Physical access to IoT devices can be a potential threat. If devices are not adequately protected, they can be physically tampered with or stolen, compromising their security and integrity.
By being aware of these security risks, you can take proactive steps to mitigate them and ensure the safety and security of your IoT devices and the data they handle.
Steps to Make IoT Devices Secure
Securing IoT devices is critical to protect your personal information, maintain privacy, and prevent unauthorized access. Here are some important steps you can take to enhance the security of your IoT devices:
- Keep IoT Devices Updated with Latest Firmware: Regularly check for firmware updates provided by the device manufacturer. These updates often address security vulnerabilities and can help improve the overall performance and security of the device.
- Change Default Passwords and Usernames: Immediately change default passwords and usernames provided by the manufacturer. Choose strong, unique passwords that are not easily guessable and consider using a password manager to securely store your credentials.
- Implement Strong Network Security Measures: Secure your home or office network by using a strong password for the Wi-Fi router, enabling network encryption (WPA2 or higher), and disabling remote management access.
- Use Encryption for Data Transmission: Ensure that data transmitted between your IoT devices and the cloud or other devices is encrypted. Look for devices and platforms that support secure protocols such as SSL/TLS for data encryption.
- Disable Unnecessary Features and Services: Review the settings of your IoT devices and disable any unnecessary features or services that are not being used. This reduces the attack surface and minimizes potential vulnerabilities.
- Regularly Monitor and Audit IoT Devices: Keep a close eye on your devices for any suspicious activities or unauthorized access. Regularly review device logs and enable notifications for any security-related events to stay informed.
- Keep Physical Security in Mind: Place IoT devices in secure locations and restrict physical access to them. If possible, consider using physical locks or enclosures to protect your devices from tampering or theft.
By following these steps, you can significantly improve the security of your IoT devices and reduce the risk of potential security breaches. It’s important to remember that securing IoT devices is an ongoing process, and staying vigilant and proactive is key to safeguarding your devices and data.
Keep IoT Devices Updated with Latest Firmware
Regularly updating the firmware of your IoT devices is a fundamental step in ensuring their security. Firmware updates are released by manufacturers to address security vulnerabilities, improve device performance, and introduce new features.
Outdated firmware can leave your IoT devices susceptible to known security flaws that hackers can exploit. By keeping your devices up to date, you can protect them from potential attacks and ensure that they are operating at their optimal level.
To check for firmware updates, visit the manufacturer’s website or check the device’s settings menu, where you may find an option to automatically check for updates. Some devices may also have a notification system to alert you when updates are available.
When updating firmware, make sure to follow these best practices:
- Backup your device: Before applying any firmware updates, create a backup of your device’s settings and configurations. This will allow you to restore your device in case anything goes wrong during the update process.
- Follow manufacturer’s instructions: Read the instructions provided by the manufacturer for updating the firmware. These instructions may include specific steps or precautions that need to be followed to ensure a smooth and successful update.
- Verify the authenticity of the update: Only download firmware updates from official sources. Avoid downloading updates from third-party websites or suspicious links, as they may contain malware or unauthorized modifications.
- Keep an eye on release notes: Read the release notes accompanying the firmware update. These notes may provide important information about bug fixes, security enhancements, or any known issues that you should be aware of.
- Test the updated device: After applying the firmware update, test the device to ensure that it is functioning properly. Check all the features and functionalities to verify that the update has not caused any adverse effects on the device’s performance.
By making a habit of regularly updating your IoT devices with the latest firmware, you can protect your devices from potential security vulnerabilities and ensure that they continue to operate securely and efficiently.
Change Default Passwords and Usernames
One of the most crucial steps in securing your IoT devices is changing the default passwords and usernames that are often provided by manufacturers. Default credentials are widely known and can easily be exploited by hackers to gain unauthorized access to your devices.
Changing the default passwords and usernames adds an additional layer of security and makes it harder for attackers to gain control over your IoT devices. Here are some important considerations when setting up new passwords and usernames:
- Create strong and unique passwords: Use a combination of uppercase and lowercase letters, numbers, and special characters to create a password that is hard to guess. Steer clear of using easily guessable information such as your name, birthdate, or common words.
- Use a password manager: To manage and generate secure passwords, consider using a password manager tool. This tool stores your passwords in an encrypted vault, making it easy for you to access them securely across your devices.
- Enable two-factor authentication (2FA): Whenever possible, enable two-factor authentication for your IoT devices. This adds an extra layer of security by requiring a second form of verification, such as a code sent to your phone, in addition to your password.
- Change usernames as well: In addition to changing passwords, it’s also advisable to change default usernames. Attackers often know the default usernames associated with specific devices and can use them to attempt unauthorized access.
- Use different credentials for each device: Avoid using the same set of credentials for multiple IoT devices. If one device is compromised, using unique credentials will prevent the attacker from gaining access to other devices on your network.
- Regularly update passwords: Set a reminder to change your passwords periodically. This will further enhance your device’s security and reduce the likelihood of unauthorized access. Aim to update your passwords at least once every three to six months.
By changing default passwords and usernames with strong, unique alternatives and employing additional security measures like two-factor authentication, you significantly reduce the risk of unauthorized access to your IoT devices. Taking these simple yet crucial steps contributes to a more robust security posture for your IoT ecosystem.
Implement Strong Network Security Measures
Securing your home or office network is essential to protect your IoT devices from unauthorized access and ensure their overall security. Implementing strong network security measures helps create a barrier between your devices and potential threats. Here are some key steps to enhance network security:
- Change default router credentials: Just like IoT devices, routers often come with default usernames and passwords. It is crucial to change these credentials to unique and strong alternatives to prevent unauthorized access to your network.
- Enable network encryption: Use Wi-Fi Protected Access 2 (WPA2) or higher encryption standards to secure your network. Encryption scrambles the data transmitted between devices, making it extremely difficult for hackers to intercept or understand the information.
- Create a guest network: Set up a separate guest network for visitors or devices that you do not fully trust. This way, you can keep your main network isolated and minimize the risk of unauthorized access to sensitive resources.
- Disable remote management: Disable any remote management features provided by your router. This prevents unauthorized individuals from accessing and controlling your router settings from outside your network.
- Segment your network: Segmenting your network involves creating separate subnetworks for different types of devices, such as IoT devices, computers, and smartphones. This adds an extra layer of protection by limiting the ability of a compromised device to affect other devices on the network.
- Regularly update router firmware: Keep your router’s firmware up to date by promptly installing any available updates. Router firmware updates often contain security patches and enhancements that protect against known vulnerabilities.
- Use a strong Wi-Fi password: Create a strong, unique password for your Wi-Fi network. Avoid using common or easily guessable passwords, and consider using a combination of letters, numbers, and special characters.
- Monitor connected devices: Regularly review the list of devices connected to your network. This helps you identify any unauthorized devices that may have gained access and take appropriate actions.
By implementing strong network security measures, you create a more secure environment for your IoT devices. These measures act as a barrier against potential threats and ensure that your devices and data are protected from unauthorized access.
Use Encryption for Data Transmission
When it comes to securing IoT devices, one critical aspect is ensuring the encryption of data during transmission. Encryption adds a layer of protection by converting the data into an unreadable format, making it difficult for unauthorized individuals to intercept or manipulate the information.
Here are some important considerations for implementing encryption for data transmission:
- Choose devices and platforms with built-in encryption: When purchasing IoT devices, look for devices and platforms that support secure encryption protocols such as SSL/TLS (Secure Sockets Layer/Transport Layer Security). This ensures that data transmitted between the device and other systems is encrypted and protected.
- Enable encryption settings: Review the settings of your IoT devices and ensure that encryption is enabled for data transmission. Enable any available encryption options provided by the device or platform to strengthen the security of your device’s communication.
- Secure your network with encryption: Implement network encryption protocols, such as WPA2 or WPA3, to encrypt the data transmitted over your Wi-Fi network. This prevents unauthorized individuals from intercepting sensitive data as it travels between your IoT devices and the network.
- Use secure communication protocols: Avoid using insecure communication protocols, such as HTTP, for transmitting data between devices. Instead, opt for more secure protocols like HTTPS (HTTP Secure) that provide an added layer of encryption and ensure the integrity of the transmitted data.
- Ensure end-to-end encryption: If your IoT devices communicate with other devices or cloud platforms, ensure that end-to-end encryption is implemented. This means that data is encrypted from the device itself, throughout its transmission, and until it reaches its final destination.
- Regularly update encryption protocols: Keep the encryption protocols and certificates used by your devices up to date. Regularly check for updates and patches provided by the device manufacturer to ensure the highest level of encryption security.
By leveraging encryption for data transmission, you create a secure and private channel for the communication between your IoT devices and the external systems they interact with. This ensures that your data remains confidential and protected from unauthorized access or tampering.
Disable Unnecessary Features and Services
One effective way to enhance the security of your IoT devices is to disable any unnecessary features and services. By doing so, you reduce the potential attack surface and minimize the risk of exploitation by hackers. Here are some important steps to follow:
- Review device settings: Take the time to thoroughly review the settings of your IoT devices. Understand the functionality and features they offer, and determine which ones are necessary for your specific needs.
- Disable default services: Many IoT devices come with default services enabled, some of which may not be necessary for your use case. Disable any default services that you do not need to reduce the potential attack vectors.
- Disable unused communication ports: Some IoT devices may have multiple communication ports, such as USB ports or Ethernet ports. If you are not using these ports, disable them to minimize the risk of unauthorized access or potential exploitation.
- Disable remote access: Evaluate whether you truly need remote access to your IoT devices. If remote access is not essential, it is advisable to disable it. Remote access can provide an entry point for hackers if not properly secured.
- Turn off unnecessary features: Some IoT devices come with additional features that may not be crucial for their primary function. Evaluate these features and disable any that you do not use or need.
- Regularly update device firmware: Firmware updates often offer new settings and options. Regularly check for firmware updates and install them to ensure that you have the most up-to-date features and security enhancements.
- Consider privacy implications: Some features and services may collect personal or sensitive data. Evaluate the privacy implications of these features and disable or limit data collection if necessary.
By disabling unnecessary features and services, you reduce the potential attack surface for hackers, making it more difficult for them to exploit vulnerabilities. This simple step can go a long way in improving the overall security posture of your IoT devices.
Regularly Monitor and Audit IoT Devices
Regular monitoring and auditing of your IoT devices are crucial to maintaining their security and detecting any potential vulnerabilities or suspicious activities. By actively monitoring your devices, you can identify and address security concerns before they escalate. Here are some important steps to follow:
- Monitor device logs: Check the logs of your IoT devices regularly. Monitor for any unusual or suspicious activities, such as multiple failed login attempts or unauthorized access attempts.
- Enable device notifications: Configure your devices to send you notifications in case of any security-related events. This allows you to stay informed and take immediate action in response to potential threats.
- Set up intrusion detection systems (IDS): Implement an IDS to actively monitor network traffic and detect any unauthorized or suspicious activities. An IDS can alert you in real-time to potential threats or security breaches.
- Perform periodic vulnerability scans: Conduct regular vulnerability scans of your IoT devices to identify any potential weaknesses or vulnerabilities. This helps in proactively addressing security issues before they are exploited.
- Keep track of device inventories: Maintain an accurate record of all your IoT devices, including their proper names, locations, and associated credentials. This allows you to quickly identify any discrepancies or unauthorized additions to your device network.
- Stay updated on security threats: Stay informed about the latest security threats and vulnerabilities related to your specific IoT devices. Subscribe to security bulletins or follow security blogs to stay up to date with the evolving security landscape.
- Perform regular security audits: Conduct periodic security audits of your IoT ecosystem. This involves reviewing the security measures in place, checking for compliance with security standards, and identifying areas that require improvement.
By regularly monitoring and auditing your IoT devices, you can ensure that any potential security concerns are identified and addressed promptly. This proactive approach helps to maintain the security and integrity of your IoT infrastructure and protect against potential threats.
Keep Physical Security in Mind
While securing IoT devices often focuses on digital measures, it’s important not to overlook the physical security aspects. Ensuring the physical protection of your IoT devices is vital to prevent unauthorized access, tampering, or theft. Here are some key considerations to keep in mind:
- Select secure device placement: Place your IoT devices in secure locations, away from prying eyes and potential physical tampering. Choose areas that can be monitored and limit access to authorized individuals only.
- Secure device connections: If your IoT devices have physical connections, such as Ethernet cables or power cords, ensure that they are properly secured and not easily accessible or detachable.
- Use physical locks or enclosures: Consider using physical locks or enclosures to protect your IoT devices. Locking them down adds an extra layer of security, preventing physical tampering or theft.
- Keep devices out of reach: Place IoT devices in locations that are not easily accessible, especially in public or high-traffic areas. This reduces the risk of devices being tampered with or stolen.
- Secure the premises: Implement security measures such as surveillance cameras, alarm systems, and access control mechanisms to protect the premises where your IoT devices are located.
- Dispose of devices securely: When disposing of IoT devices, ensure that any stored data is wiped clean and the devices are properly disposed of, following manufacturer or local guidelines.
- Educate users: Educate users, including family members or employees, about the importance of physical security for IoT devices. Encourage them to report any suspicious activities or individuals in the vicinity of the devices.
By keeping physical security in mind, you can significantly reduce the risk of unauthorized access or physical tampering with your IoT devices. This complements the digital security measures and ensures a holistic approach to safeguarding your IoT infrastructure.
Conclusion
Securing IoT devices is of paramount importance in today’s interconnected world. The risks associated with these devices can pose significant threats to our privacy, data integrity, and overall digital security. By following the steps outlined in this article, you can significantly enhance the security of your IoT devices and minimize the risk of potential security breaches.
Keeping IoT devices updated with the latest firmware ensures that known security vulnerabilities are patched, and devices operate at optimal security levels. Changing default passwords and usernames adds a strong layer of protection against unauthorized access. Implementing robust network security measures, such as encryption and disabling unnecessary features and services, strengthens your overall defense against cyber attacks.
Regularly monitoring and auditing your IoT devices helps in detecting and addressing potential vulnerabilities or suspicious activities before they cause harm. Additionally, considering physical security measures like secure device placement, locks, and enclosures ensures protection against physical tampering and theft.
In conclusion, securing IoT devices requires a multi-layered approach. It involves a combination of digital and physical security measures, ongoing monitoring, and user awareness. By incorporating these practices into your IoT device management, you can enjoy the benefits of these connected devices while maintaining a secure and protected digital environment.