Introduction
With the rapid expansion of the Internet of Things (IoT), more and more devices are becoming interconnected, forming a complex network that has the potential to revolutionize various industries. From smart homes to industrial automation, IoT devices are changing how we live and work. However, this increased connectivity also brings about new challenges, particularly when it comes to the security of these devices.
IoT devices, which include smart thermostats, connected cameras, wearable fitness trackers, and even household appliances, pose a greater risk than other computing devices on a network. The unique characteristics of IoT devices make them vulnerable to cyberattacks, raising concerns about privacy, data breaches, and potential disruptions to critical infrastructure.
In this article, we will delve into the reasons why IoT devices are more prone to security risks compared to traditional computing devices on a network. Understanding these risks is crucial for users, developers, and organizations to take proactive measures and implement effective security strategies to protect their IoT devices and networks.
Definition of IoT Devices
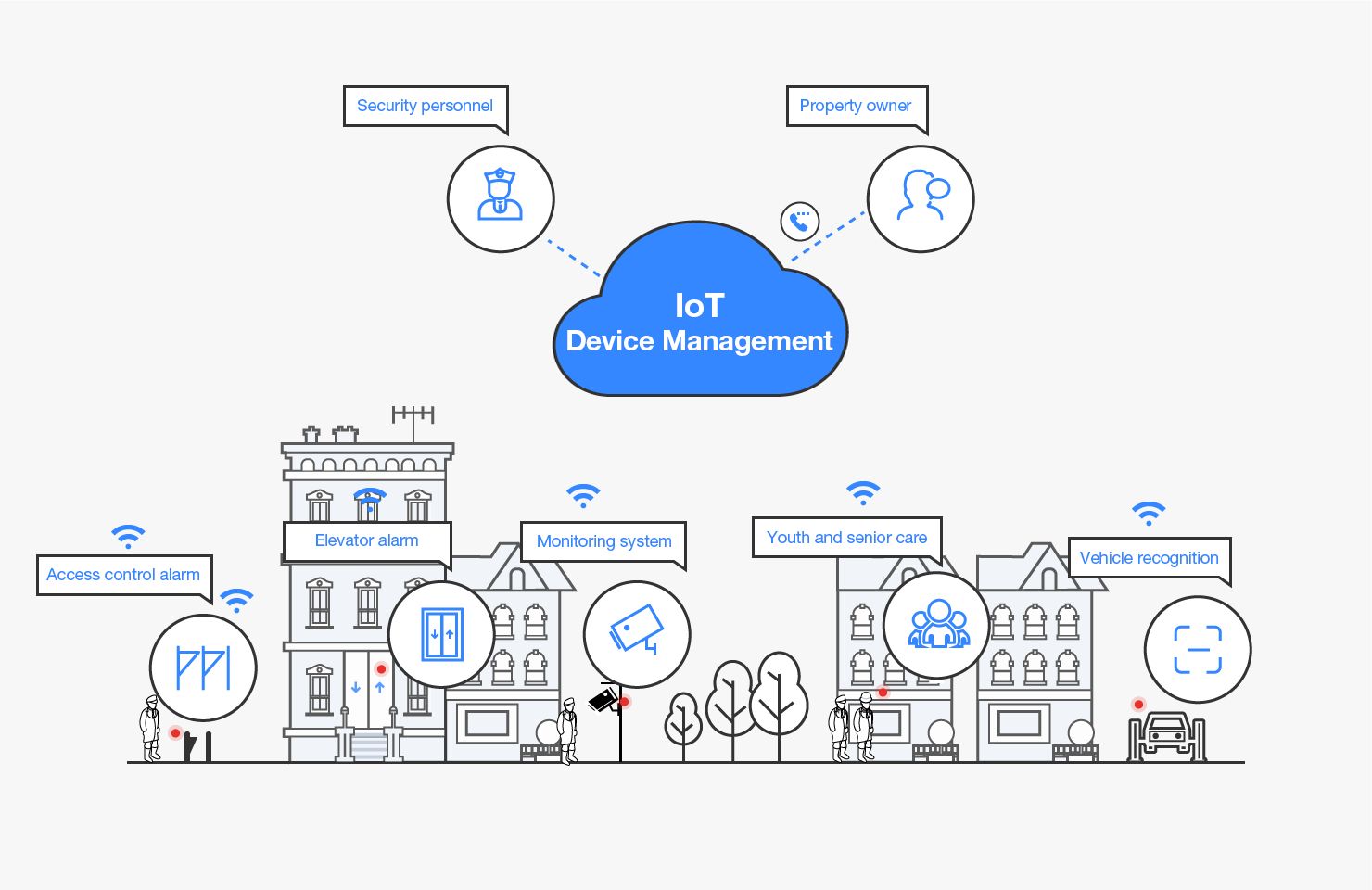
The Internet of Things (IoT) refers to the network of physical objects or “things” embedded with sensors, software, and connectivity, enabling them to collect and exchange data. These “things” can range from everyday household items like light bulbs and refrigerators to complex industrial machinery and infrastructure.
IoT devices are designed to facilitate communication and interaction between the physical world and the digital world. They connect to the internet and other devices, allowing users to control and monitor them remotely. These devices often have built-in sensors that gather data, which can be analyzed to provide valuable insights or trigger specific actions.
Common examples of IoT devices include wearable fitness trackers, smart thermostats, surveillance cameras, smart home assistants like Amazon Echo or Google Home, and even smart cars. These devices are typically equipped with wireless communication capabilities, such as Wi-Fi, Bluetooth, or cellular connectivity, enabling them to connect to a network and transmit data.
IoT devices play a significant role in creating smart homes, cities, and industries. They offer numerous benefits, such as improved efficiency, convenience, and enhanced quality of life. However, with the growing number of interconnected devices, the security risks associated with IoT have also increased.
It is important to note that IoT devices can vary in terms of their capabilities and complexity. Some devices have limited computing power and memory, while others are more sophisticated and capable of running complex applications. Despite these differences, all IoT devices share a common thread of being susceptible to security vulnerabilities.
Overview of IoT Devices on a Network
When IoT devices are connected to a network, they become part of a larger ecosystem that can include other devices, servers, and cloud infrastructure. This networked environment allows IoT devices to communicate and share data, enabling them to function as intended. However, this interconnectedness also presents various security challenges.
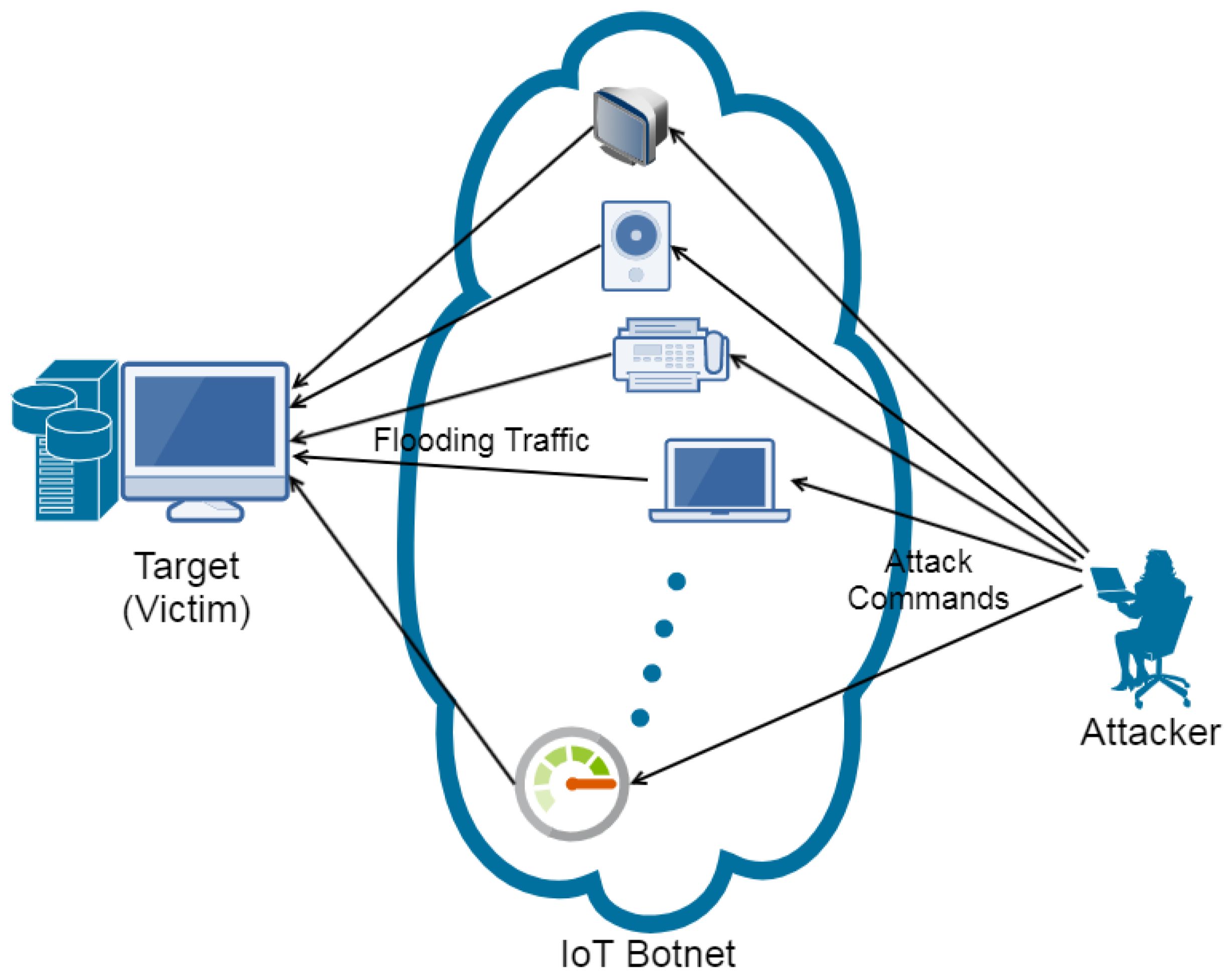
Firstly, the sheer number of IoT devices connected to a network can increase the attack surface. Each device becomes a potential entry point for cybercriminals to exploit. With more devices interconnected, there are more opportunities for hackers to gain unauthorized access, manipulate data, or launch attacks on the network.
Furthermore, many IoT devices lack robust security measures. Unlike traditional computers or smartphones, IoT devices are often designed with a focus on functionality and cost-efficiency, rather than robust security features. As a result, they may not have built-in encryption, secure authentication mechanisms, or secure update mechanisms, making them vulnerable to various attack vectors.
Additionally, IoT devices typically have limited processing power and memory. This constraint makes it challenging to implement advanced security measures or run security software on the devices themselves. As a result, IoT devices may rely heavily on external systems or cloud services for certain security operations, which introduces potential vulnerabilities and dependencies.
Another concern is the prevalence of default credentials and common vulnerabilities in IoT devices. Many manufacturers use default usernames and passwords that are easily discoverable or found within publicly available documentation. As a result, adversaries can exploit these default credentials to gain unauthorized access. Additionally, IoT devices often have software vulnerabilities or weak security configurations that can be exploited by attackers.
Furthermore, there is a lack of standardization and regulation in the IoT industry. This can lead to inconsistencies in security practices across different devices and manufacturers. While some companies prioritize security and follow best practices, others may prioritize speed to market or cost reduction, resulting in devices with inadequate security measures.
Lastly, the use of third-party applications and untrusted sources poses additional risks. Many IoT devices allow users to install apps or connect to third-party services to enhance functionality or interoperability. However, these third-party apps may not undergo thorough security testing, making them potential entry points for cyberattacks.
Overall, the interconnected nature of IoT devices on a network, combined with their limited security measures and potential vulnerabilities, creates a challenging landscape for securing IoT ecosystems.
Increased Attack Surface
One of the key reasons why IoT devices pose a greater risk than other computing devices on a network is their expanded attack surface. With the proliferation of IoT devices, the number of potential entry points for cyberattacks significantly increases.
Unlike traditional computers or smartphones that are typically used by individuals, IoT devices can be found in various settings, including homes, offices, hospitals, and industrial facilities. Each device, regardless of its size or functionality, has the potential to connect to the internet and communicate with other devices within the network.
As the number of connected devices grows, so does the attack surface. Hackers can exploit vulnerabilities in any connected device to gain unauthorized access to the network. This means that even a seemingly insignificant IoT device can serve as a doorway for cybercriminals to infiltrate the entire system.
Moreover, the interconnectedness between different types of IoT devices can further exacerbate the attack surface. For instance, a compromised smart thermostat in a home network could be used as a launching pad to target other connected devices, such as cameras or smart locks. This interconnectedness increases the complexity and difficulty of securing the network as a whole.
Additionally, IoT devices often have different communication protocols and operating systems, which can introduce additional vulnerabilities. For example, some devices may use Wi-Fi for connectivity, while others rely on Bluetooth or Zigbee. Each protocol has its own unique security considerations, and any weaknesses or vulnerabilities within these protocols can be exploited by attackers.
Furthermore, the variety of IoT device manufacturers and models also contributes to the expanded attack surface. With so many different devices in the market, each with its own specific security implementation, it becomes challenging to maintain a consistent level of security across all devices. Manufacturers may have varying levels of expertise and investment in security measures, resulting in inconsistencies in the security posture of different devices.
Overall, the increased attack surface presented by the sheer number and diversity of IoT devices connected to a network poses a significant challenge for security professionals. Protecting against potential vulnerabilities and securing the entire IoT ecosystem requires a comprehensive approach that addresses the unique characteristics and risks associated with these devices.
Lack of Security Measures
An inherent problem with many IoT devices is the lack of robust security measures, making them more susceptible to attacks compared to other computing devices on a network.
One reason for this is that IoT devices are often designed with a primary focus on functionality and cost-efficiency, rather than built-in security features. Manufacturers prioritize providing users with convenient and connected experiences, often overlooking the potential security risks associated with these devices.
As a result, many IoT devices lack fundamental security components such as encryption, secure authentication mechanisms, or secure update mechanisms. Without proper encryption, the data transmitted between IoT devices and the network can be intercepted and accessed by unauthorized parties. Without secure authentication mechanisms, attackers can bypass user authentication processes and gain unauthorized access to the device or the network.
Furthermore, IoT devices typically have limited processing power and memory. This constraint makes it challenging to implement advanced security measures or run security software on the devices themselves. The limited resources available for security-related tasks can lead to vulnerabilities and weaknesses that can be exploited by malicious actors.
In addition to the lack of built-in security measures, many IoT devices come with default credentials that are commonly known or easily discoverable. Manufacturers often use generic usernames and passwords for simplicity, which makes it easier for hackers to gain unauthorized access to the device or the network. This problem is further compounded by users who fail to change the default credentials, leaving their devices susceptible to attacks.
Furthermore, there is a lack of standardization and regulation in the IoT industry when it comes to security practices. This leads to inconsistencies in security measures across different devices and manufacturers. Some companies prioritize security and follow best practices, while others may prioritize cost reduction or speed to market, resulting in devices with inadequate security measures.
Addressing the lack of security measures in IoT devices requires a multi-faceted approach. Manufacturers need to prioritize security during the design and development phase, ensuring that devices have built-in security features, robust authentication mechanisms, and secure communication protocols. Users also play a crucial role in actively changing default credentials, keeping devices updated with the latest security patches, and practicing good security hygiene.
Overall, the lack of significant security measures in IoT devices leaves them vulnerable to attacks and makes them a prime target for cybercriminals.
Limited Processing Power and Memory
One of the inherent limitations of IoT devices that contributes to their increased security risks is their limited processing power and memory. Unlike traditional computing devices, such as computers or smartphones, IoT devices are often resource-constrained due to their small size, low power requirements, and cost considerations.
Due to these limitations, IoT devices may not have the capacity to implement robust security measures or run security software efficiently. The limited processing power and memory make it challenging to perform complex security operations, such as encryption, decryption, or running resource-intensive security algorithms.
This limitation can lead to vulnerabilities and weaknesses that can be exploited by hackers. For example, without sufficient processing power, IoT devices may not have the capability to perform encryption and decryption operations at the necessary speed, making the transmission of sensitive data susceptible to interception or tampering.
Moreover, the limited memory of IoT devices may restrict the storage of security certificates or keys necessary for secure communication. This can result in devices using weak or easily guessable keys, which can be exploited by attackers to gain unauthorized access and compromise the device or the network.
Additionally, the limited processing power and memory can hinder the ability to implement secure update mechanisms. IoT devices often require regular security updates to defend against newly discovered vulnerabilities and address software bugs. However, with constrained resources, it may be challenging for device manufacturers to deliver timely security updates, leaving devices exposed to known security flaws.
Furthermore, the limited processing power and memory can impact the ability to detect and mitigate security threats in real-time. Traditional security solutions, such as antivirus software or intrusion detection systems, require substantial computing resources to operate effectively. The lack of processing power in IoT devices prevents the implementation of such solutions on the devices themselves, necessitating alternative security strategies.
Addressing the limitations of limited processing power and memory in IoT devices requires a combination of approaches. Manufacturers can focus on optimizing security algorithms and developing efficient security architectures that work within the constraints of IoT device resources. Additionally, offloading some security operations to external systems or cloud infrastructure can help alleviate the burden on individual devices.
Overall, the limited processing power and memory of IoT devices pose a significant challenge when it comes to implementing robust security measures, making these devices more susceptible to security vulnerabilities and attacks.
Default Credentials and Vulnerabilities
One of the primary reasons why IoT devices pose a greater risk than other computing devices on a network is the prevalence of default credentials and common vulnerabilities. Many IoT devices are shipped with default usernames and passwords that are either well-known or easily obtainable through public documentation or online resources.
Default credentials pose a significant security risk because users often fail to change them, leaving their devices vulnerable to unauthorized access. Attackers can leverage these default credentials to gain entry into the device, potentially compromising the entire network.
In addition to default credentials, IoT devices are also plagued by common vulnerabilities. Some of these vulnerabilities are inherent design flaws or weaknesses in the device’s firmware, others arise from insecure coding practices or lack of rigorous security testing during the development phase.
For example, IoT devices may have vulnerable firmware that can be exploited through known vulnerabilities, enabling attackers to compromise the device or gain unauthorized access to the network. These vulnerabilities may be related to insecure communication protocols, weak encryption implementations, or other security oversights.
Moreover, IoT devices often lack necessary security features, such as secure boot mechanisms or firmware integrity checks. Without these features, it becomes easier for attackers to manipulate the device’s firmware and inject malicious code, compromising the device’s security and potentially affecting the entire network it is connected to.
Additionally, IoT devices may have weak physical security measures. This can include easily accessible ports, lack of tamper-resistant hardware, or inadequate protection against physical attacks. Attackers can exploit these weaknesses to gain physical access to the device, enabling them to bypass security measures and compromise the device’s functionality or gain unauthorized control over it.
Furthermore, outdated or unsupported software components in IoT devices can introduce vulnerabilities. Many devices run on operating systems or firmware that may not receive regular updates or security patches. This lack of regular maintenance leaves the devices exposed to known security flaws that can be exploited by attackers.
To combat the risks posed by default credentials and vulnerabilities, it is crucial for manufacturers to prioritize security during the development phase. This includes implementing secure default settings, enforcing password changes upon initial setup, performing rigorous security testing, and providing regular firmware updates to address vulnerabilities. Additionally, users must be proactive in changing default credentials and keeping their IoT devices updated with the latest security patches.
Overall, the prevalence of default credentials and common vulnerabilities in IoT devices makes them attractive targets for attackers, reinforcing the need for robust security measures and vigilant user behavior.
Lack of Encryption and Privacy Concerns
One significant area of concern when it comes to IoT devices is the lack of encryption and the resulting privacy vulnerabilities. Encryption plays a crucial role in ensuring the confidentiality and integrity of data transmitted between IoT devices and the network. However, many IoT devices lack robust encryption mechanisms, making them more susceptible to privacy breaches.
Without encryption, the data exchanged between IoT devices and the network can be intercepted by unauthorized parties. This can lead to unauthorized access to sensitive personal information, such as personal health data, financial information, or private conversations. Additionally, it can compromise the integrity of the data, allowing attackers to modify or manipulate the information being transmitted.
Privacy concerns also arise from the sheer volume and diversity of data collected by IoT devices. These devices are often equipped with sensors that continuously collect data about users’ behaviors, preferences, and surroundings. This data, when collected without appropriate encryption or privacy protections, can be exploited by unauthorized individuals or organizations for nefarious purposes.
Furthermore, IoT devices often rely on cloud infrastructure or third-party services to store and analyze data. This introduces additional privacy risks, as users are entrusting their personal information to external entities. Without encryption or strong privacy controls, this data may be vulnerable to unauthorized access or misuse by these entities or malicious actors seeking to exploit vulnerabilities in the cloud or third-party systems.
Another concern is the potential for data aggregation and profiling. IoT devices can generate vast amounts of data, and when combined, these data streams can provide detailed insights into users’ behavior patterns, habits, and preferences. This data can be used to create comprehensive profiles that violate users’ privacy and can be exploited for targeted advertising, surveillance, or other invasive practices.
Addressing the lack of encryption and privacy concerns requires a multi-faceted approach. Manufacturers need to prioritize the implementation of robust encryption mechanisms throughout the entire lifecycle of the device, from data transmission to data storage. Additionally, privacy-by-design principles should be adopted, ensuring that devices are designed with privacy protections from the ground up.
Users also need to be aware of the privacy implications of using IoT devices and take steps to protect their privacy. This includes reviewing privacy policies, keeping devices updated with the latest firmware, and considering the implications of sharing personal data with IoT devices and related services.
Overall, the lack of encryption and the associated privacy concerns make IoT devices vulnerable to privacy breaches, emphasizing the need for comprehensive security measures that prioritize data protection and user privacy.
Lack of Regular Security Updates
A significant security challenge with IoT devices is the lack of regular security updates. Many IoT devices are designed to be low-cost and focused on delivering specific functionalities, which often results in inadequate support for ongoing security measures.
Regular security updates are crucial for protecting IoT devices against emerging threats and vulnerabilities. Hackers constantly evolve their techniques and exploit new vulnerabilities, making it imperative for devices to receive timely updates that address these evolving risks. However, many IoT devices do not have mechanisms in place to receive and install regular security patches.
One reason for the lack of regular security updates is the fragmented nature of the IoT industry. Numerous manufacturers produce IoT devices with varying operating systems, firmware versions, and update mechanisms. This lack of standardization makes it challenging to establish a unified approach for delivering security updates across different devices.
Furthermore, IoT devices often have limited processing power and memory, as well as constrained network connectivity. These limitations can hinder the delivery and installation of security updates. In some cases, the devices may not have the capacity to run the update process or store the necessary update files, leaving them susceptible to unpatched vulnerabilities.
Another contributing factor is the long lifespan of many IoT devices. Unlike smartphones or computers, which are frequently upgraded or replaced, IoT devices tend to have longer lifespans. As a result, manufacturers may lose interest in supporting older devices with security updates as they prioritize newer product models.
The lack of regular security updates leaves IoT devices exposed to known vulnerabilities and exploits. This not only puts the affected devices at risk but can also have broader implications for the entire network they are connected to. Compromised IoT devices can be used as entry points for cybercriminals to launch attacks, gain unauthorized access to other devices or networks, and potentially cause significant disruptions.
To address the lack of regular security updates, manufacturers need to prioritize ongoing support for their IoT devices throughout their lifecycle. This means establishing mechanisms for delivering timely security patches and updates, even for older device models. Additionally, manufacturers should consider implementing automatic update mechanisms to ensure that devices receive critical security updates without relying on user intervention.
Users also play a role in maintaining the security of their IoT devices by regularly checking for updates, applying patches promptly, and retiring devices that are no longer supported by the manufacturer.
Overall, the lack of regular security updates in IoT devices is a critical security concern. It is essential for manufacturers to prioritize ongoing support and deliver timely updates to protect against emerging threats and vulnerabilities.
Use of Third-Party and Untrusted Apps
The use of third-party and untrusted apps is another factor that contributes to the increased risk of IoT devices compared to other computing devices on a network. Many IoT devices allow users to extend functionality by installing additional apps or connecting to third-party services. While this flexibility enhances the user experience, it also introduces potential security vulnerabilities.
One concern with third-party apps is the lack of rigorous security testing. Unlike official app stores for smartphones, IoT app ecosystems often lack centralized control and comprehensive security vetting processes. As a result, apps available for IoT devices may not undergo thorough security assessments, making them potential vehicles for delivering malware or exploiting vulnerabilities.
Furthermore, the use of third-party apps can lead to the inadvertent disclosure of sensitive information. Many IoT devices require users to provide access permissions and grant certain privileges to third-party apps. This can include granting access to personal data, network resources, or even physical control over the device. If these permissions are not carefully managed, it can result in unintended consequences, including unauthorized data collection or malicious actions by the app.
Moreover, connecting IoT devices to untrusted or insecure services can also compromise the security and privacy of the device and the network. IoT devices often rely on cloud services or other networked systems for data storage, analysis, or remote access. These services may have their own security vulnerabilities or operational shortcomings that can be exploited by attackers to gain unauthorized access or compromise the integrity of the data.
In some cases, IoT devices may even be susceptible to supply chain attacks through third-party apps or services. If a malicious actor gains access to the development or deployment pipeline of an IoT app, they can insert malicious code or compromise the security of the app, leading to potential security breaches and unauthorized access to the device or network.
To mitigate the risks associated with third-party and untrusted apps, users should exercise caution when installing apps on IoT devices. It is important to verify the credibility and trustworthiness of app developers and conduct appropriate research before granting unnecessary permissions to an app.
Manufacturers also have a responsibility to establish app vetting processes and implement security mechanisms that prevent unauthorized or malicious apps from being installed on their devices. This includes implementing measures such as code signing, digital certificates, and secure app repositories.
Overall, the use of third-party and untrusted apps in IoT devices introduces potential security vulnerabilities. Users should be vigilant and make informed decisions when installing apps, and manufacturers must prioritize the implementation of robust security measures to safeguard against potential threats.
Conclusion
The proliferation of IoT devices has brought numerous benefits and advancements to various industries. However, the security risks associated with these devices should not be overlooked. IoT devices pose a greater risk than other computing devices on a network due to various factors.
IoT devices have an expanded attack surface, with each interconnected device potentially serving as an entry point for hackers. The lack of robust security measures in many IoT devices further exacerbates the risks. Limited processing power and memory hinder the implementation of advanced security features, while default credentials and common vulnerabilities make IoT devices easy targets for attackers.
The lack of encryption and privacy concerns with IoT devices can lead to unauthorized access, data breaches, and the potential for misuse of sensitive personal information. Furthermore, the absence of regular security updates leaves IoT devices exposed to known vulnerabilities and exploits.
Another area of concern is the use of third-party and untrusted apps, which introduces potential security vulnerabilities and privacy risks. Users need to be cautious when installing apps and granting access permissions, and manufacturers must implement app vetting processes and security mechanisms to mitigate these risks.
To mitigate the security risks associated with IoT devices, a comprehensive approach is required. Manufacturers must prioritize security during the design and development phase, implementing robust security measures and providing regular security updates. Users must actively engage in best security practices, such as changing default credentials, keeping devices updated, and being mindful of app installations. Standardization and industry regulations can also play a role in promoting better security practices across the IoT ecosystem.
In conclusion, the unique characteristics of IoT devices, coupled with the aforementioned security challenges, make them more vulnerable to attacks and privacy breaches. By addressing these concerns, we can ensure safer and more secure usage of IoT devices, enabling us to fully harness the benefits of this transformative technology.