Introduction
These days, our personal information is more vulnerable than ever. With the rise of cybercrime, a growing concern is the presence of our data on the Dark Web. The Dark Web is a hidden part of the internet where illegal activities occur, including the buying and selling of stolen personal information. If you suspect that your information is on the Dark Web, it’s important to act swiftly and take the necessary steps to protect yourself.
But what exactly is the Dark Web, and how does your information end up there? In this article, we will explore what the Dark Web is, the common ways your information lands on it, signs that your data may be on the Dark Web, and most importantly, what you can do if you find yourself in this unfortunate situation.
The Dark Web is a part of the internet that is not indexed by search engines, making it inaccessible to regular internet users. It requires specific software, such as Tor, to access its websites. Due to its anonymity, it has become a haven for illegal activities, including identity theft, data breaches, and the sale of personal information.
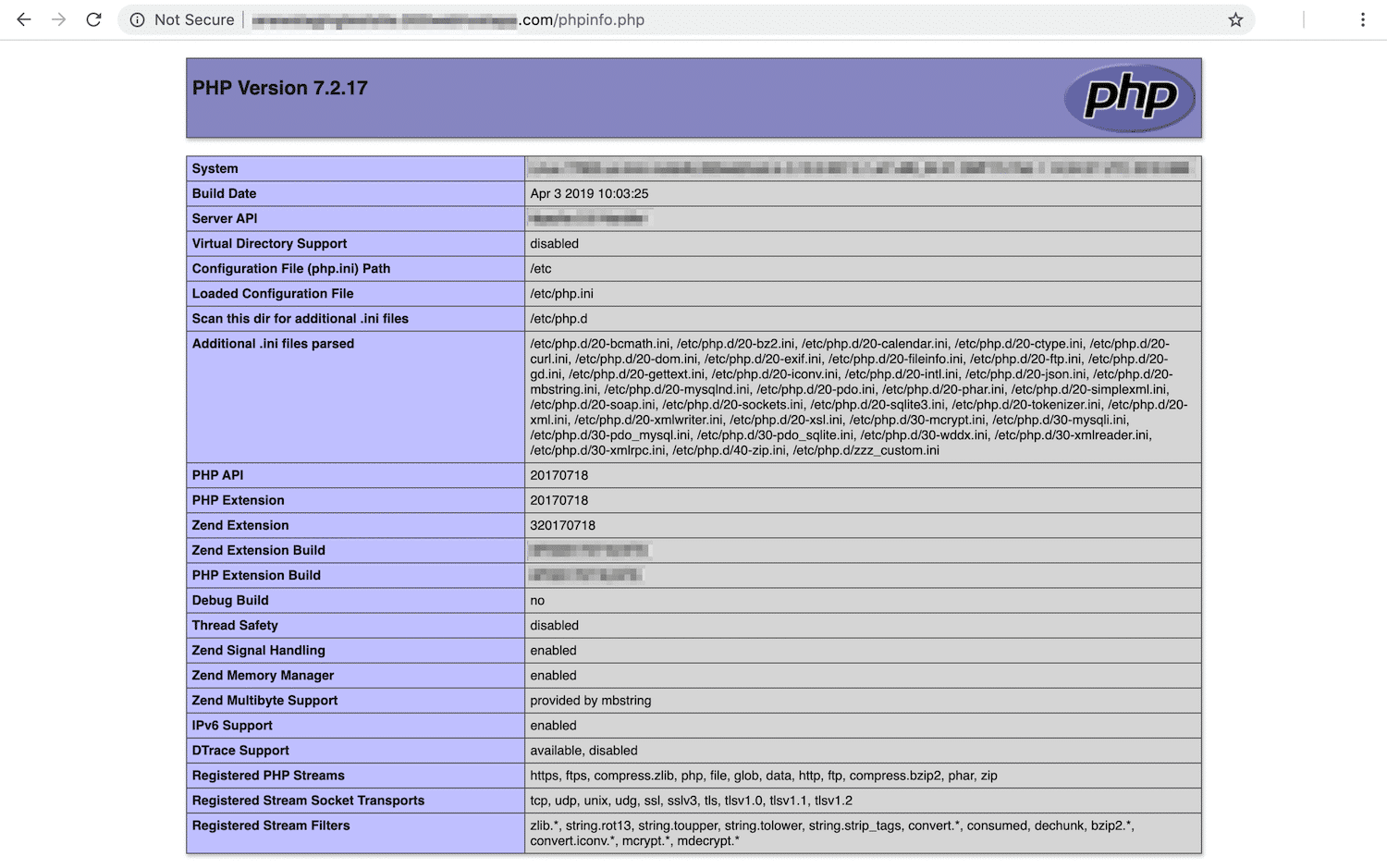
There are several ways that your information can end up on the Dark Web. One common method is through data breaches. Hackers target websites and gain access to their databases, which contain valuable user information like email addresses, passwords, and even credit card details. This stolen data is then sold on the Dark Web.
Another way your information can end up on the Dark Web is through phishing scams. These scams trick you into providing your personal information, such as login credentials or credit card details, on a fraudulent website. Cybercriminals then use this information to exploit your accounts or sell it on the Dark Web.
What is the Dark Web?
The Dark Web is a term that refers to a hidden part of the internet. Unlike the surface web, which can be accessed through search engines like Google, the Dark Web is not indexed and requires specific software to access its websites. This software provides users with the ability to browse the internet anonymously, making it difficult to trace their online activities.
One of the most commonly used software to access the Dark Web is Tor (The Onion Router). Tor routes users’ internet traffic through a series of encrypted relays, effectively masking their IP addresses and providing them with a higher level of privacy and anonymity.
Within the Dark Web, there are various websites and online communities that exist, many of which are involved in illegal activities. These activities may include selling drugs, weapons, stolen data, hacking services, and even engaging in human trafficking. The nature of the Dark Web has made it a popular platform for individuals and criminal organizations to operate beyond the reach of law enforcement.
In addition to its illicit activities, the Dark Web also serves as a haven for whistleblowers and activists who seek to share information without fear of censorship or surveillance. The anonymity offered by the Dark Web can protect those individuals from retaliation and provide a platform for free speech and expression.
It is important to note that not everything on the Dark Web is illegal or malicious. There are legitimate uses for the hidden web, such as anonymous communication and accessing blocked websites in countries with heavy censorship. However, the illegal activities that take place on the Dark Web have gained significant attention due to their impact on individuals and society as a whole.
It is essential to understand that accessing the Dark Web comes with significant risks. The anonymity it provides can attract cybercriminals, hackers, and individuals seeking to exploit others. Therefore, it is crucial to exercise caution and prioritize personal safety and security when dealing with the Dark Web.
How Does Your Information End Up on the Dark Web?
There are several ways that your personal information can end up on the Dark Web, exposing you to potential identity theft and other malicious activities. Understanding these methods can help you take necessary precautions to protect your data. Here are the most common ways your information can find its way to the Dark Web:
- Data Breaches: One of the main sources of personal information on the Dark Web is data breaches. Cybercriminals target organizations, ranging from small businesses to large corporations, and infiltrate their databases to steal valuable user information. This stolen data, including email addresses, usernames, passwords, and even credit card details, is then sold on the Dark Web for malicious purposes.
- Phishing Scams: Phishing scams are fraudulent attempts to obtain sensitive information, such as passwords, credit card details, or social security numbers, by posing as a trustworthy entity. These scams often appear as deceptive emails, text messages, or websites designed to trick unsuspecting victims into providing their personal data. Once obtained, this information can be sold or exploited on the Dark Web.
- Malware Infections: Malware, such as viruses, Trojans, and keyloggers, can infect your devices and covertly collect your personal information, including login credentials and financial data. Cybercriminals can use this stolen data to their advantage or sell it on the Dark Web to other malicious actors.
- Dark Web Trading: Some individuals willingly trade or sell their personal information on the Dark Web. This can include anything from login credentials to credit card details. These sellers may have obtained the information illegally, through hacking or other malicious activities, and are looking to profit from it.
- Insider Threats: Occasionally, individuals within organizations may have unauthorized access to sensitive data. These insiders may exploit this access to steal and sell valuable information on the Dark Web. This type of threat highlights the importance of implementing robust security measures and strict access controls within organizations.
It’s crucial to understand that even if you take all necessary precautions to protect your personal information, there is still a chance that it may end up on the Dark Web. However, by staying vigilant, practicing good cybersecurity habits, and promptly responding to any signs of compromise, you can minimize the risk and mitigate the potential damage caused by your information falling into the wrong hands.
Signs That Your Information is on the Dark Web
Discovering that your personal information has made its way to the Dark Web can be a distressing experience. However, early detection is key to mitigating potential harm and taking proactive steps to protect yourself. Here are some signs that may indicate your information is on the Dark Web:
- Unusual Account Activities: If you notice unexplained activities on your online accounts, such as unfamiliar purchases, withdrawals, or changes to your personal information, it could be a sign that your information has been compromised and is being misused on the Dark Web.
- Notifications from Security Services: Some security services and identity theft protection companies monitor the Dark Web for signs of compromised information. If you receive a notification from such a service informing you that your information has been found on the Dark Web, it’s important to take immediate action to secure your accounts and personal data.
- Receiving Breach Notifications: Organizations that experience data breaches often notify affected individuals about the incident. If you receive a breach notification from a company you have an account with, it’s essential to take it seriously and follow the recommended steps to protect your information.
- Identity Theft Reports: If you discover that someone has fraudulently used your identity or opened accounts in your name, it could indicate that your personal information is circulating on the Dark Web. Instances of denied credit or loans you did not apply for are red flags that warrant immediate investigation.
- Suspicious Communications: If you start receiving phishing emails, messages, or phone calls that appear to have legitimate information about you, it could indicate that your data is in the hands of cybercriminals. Be cautious and do not provide any personal information in response to such communications.
- Online Reputation Damage: Another sign that your information may be on the Dark Web is a sudden decrease in your online reputation. If your social media accounts are hacked, suspicious posts are made in your name, or you receive messages from people claiming to have seen your personal information for sale, it’s important to investigate the source and take appropriate action.
If you notice any of these signs or have concerns about your personal information being on the Dark Web, it’s crucial to act quickly. By promptly investigating and taking the necessary steps to secure your accounts and personal data, you can minimize the potential damage and protect yourself from further harm.
What To Do if Your Info is on the Dark Web
Discovering that your personal information is on the Dark Web can be alarming, but it’s important to remain calm and take immediate action to protect yourself. Here are the steps you should follow if you find out that your information is on the Dark Web:
- Stay Calm and Do Not Panic: It’s natural to feel anxious and stressed upon discovering that your information is on the Dark Web. However, it’s crucial to stay calm and approach the situation with a clear mind. Panic can cloud your judgment and hinder your ability to respond effectively.
- Take Stock of the Damage: Assess the extent of the potential damage by identifying which specific information has been compromised. Determine if it includes login credentials, financial data, or any other sensitive details that could be used for fraudulent activities.
- Change Your Passwords: Immediately change the passwords for all your online accounts, especially those associated with sensitive information. Create strong, unique passwords using a combination of letters, numbers, and special characters. Avoid using the same password for multiple accounts.
- Enable Two-Factor Authentication: Implement two-factor authentication (2FA) for all applicable accounts. 2FA adds an extra layer of security by requiring an additional verification step, such as entering a code sent to your phone, in addition to your password.
- Monitor Your Financial Accounts: Regularly review your bank statements, credit card transactions, and other financial accounts for any unauthorized activity. If you spot any suspicious transactions, report them to your financial institution immediately.
- Contact Your Financial Institution: Notify your bank, credit card companies, and any other relevant financial institutions about the potential compromise of your information. They can guide you on additional security measures and help monitor your accounts for any fraudulent activity.
- Freeze Your Credit: Consider placing a freeze on your credit file with the major credit bureaus. This prevents fraudsters from opening new accounts or obtaining credit in your name without your consent. Contact each credit bureau for detailed instructions on how to initiate a credit freeze.
- File a Report with Law Enforcement: Contact your local law enforcement agency and report the incident. Provide them with all relevant information, including any evidence of the compromise. This step is crucial for documenting the incident and potentially aiding in the investigation.
- Monitor Your Online Presence: Keep a close eye on your online presence, including social media accounts and online directories. Be cautious of any unusual activities or posts that could indicate someone is impersonating you or using your personal information.
- Consider Using a Dark Web Monitoring Service: Explore the option of subscribing to a reputable dark web monitoring service. These services scan the Dark Web for your compromised information, alert you to any findings, and offer steps to mitigate the damage.
By following these steps, you can take immediate action to protect your personal information and mitigate the potential risks associated with your data being on the Dark Web. Remember to stay vigilant and regularly monitor your accounts and online presence for any suspicious activity.
Stay Calm and Do Not Panic
Discovering that your personal information is on the Dark Web can be a distressing experience. However, it is crucial to stay calm and composed in order to approach the situation rationally and effectively. Panicking can cloud your judgment and hinder your ability to take the necessary steps to protect yourself. Here’s what you should keep in mind:
Assess the Situation: Take a moment to assess the situation and understand the potential risks associated with your information being on the Dark Web. Determine the type of information that has been compromised and consider the potential consequences. This will help you prioritize your actions and respond appropriately.
Understand That You’re Not Alone: Remember that you are not alone in experiencing this issue. Countless individuals have fallen victim to cybercrime and have successfully taken steps to mitigate the damage. Seek comfort in the fact that there are resources available to help you through this situation, including online support communities and cybersecurity professionals.
Focus on Taking Action: Instead of dwelling on the negative emotions, direct your energy towards taking immediate action to safeguard your information and prevent any potential misuse. Stay positive and motivated to actively protect yourself and regain control over your personal data.
Follow a Methodical Approach: Panic can lead to impulsive decisions and hasty actions, which may not yield the desired results. It is important to approach the situation methodically and follow a step-by-step plan to handle the issue effectively.
Seek Professional Help if Needed: If you find it challenging to stay calm and navigate through the situation on your own, consider seeking professional help. Cybersecurity experts, identity theft professionals, and counselors can provide guidance and support during this stressful time.
Remember that staying calm and composed is key to effectively addressing the situation. By maintaining a level-headed approach, you can make informed decisions and take the necessary steps to protect your information and minimize the potential damage caused by its presence on the Dark Web.
Take Stock of the Damage
After discovering that your information is on the Dark Web, it’s essential to take stock of the potential damage that may have occurred. By assessing the situation thoroughly, you can understand the extent of the compromise and determine the necessary actions to protect yourself. Here’s how you can take stock of the damage:
Identify the Compromised Information: Determine which specific pieces of your personal information have been compromised. This could include your email address, usernames, passwords, social security number, credit card details, or any other sensitive data. Knowing exactly what information is at risk will help you prioritize your next steps.
Review Your Financial and Online Accounts: Carefully review your financial statements, such as bank accounts, credit cards, and other accounts linked to your finances. Look for any unauthorized transactions, suspicious activities, or changes to your account information. Similarly, assess your online accounts, including social media platforms and email, for any signs of suspicious activities or unauthorized access.
Consider the Potential Consequences: Think about the potential consequences of your information falling into the wrong hands. This could include unauthorized access to your accounts, identity theft, financial loss, or the possibility of your personal data being used for fraudulent activities. Understanding the potential risks will help you take appropriate actions to protect yourself.
Assess Potential Damage to Your Reputation: If your personal data has been exposed on the Dark Web, it may lead to reputational damage. Consider how the compromised information could be used against you, such as impersonation, posting false information, or engaging in fraudulent activities in your name. Be aware of any signs that your online reputation is being compromised.
Document and Gather Evidence: It’s important to document any evidence or suspicious activities related to the compromise. Take screenshots, save emails or messages, and gather any other relevant information that can assist in the investigation or help you in resolving the issue with authorities, financial institutions, or credit bureaus.
Keep Records of Your Actions: Throughout the process of addressing the breach, keep a record of the steps you’ve taken, including dates, times, and individuals you’ve contacted. This documentation can be useful for reference purposes and can help support any legal or financial proceedings that may arise later.
By taking stock of the damage, you can gain a clearer understanding of the potential risks and impact of the compromise. This information will empower you to take the necessary actions to protect yourself, mitigate any harm, and restore your peace of mind.
Change Your Passwords
One of the crucial steps to take when your information is on the Dark Web is to change your passwords. By updating your passwords, you can minimize the risk of unauthorized access to your accounts and protect your information. Follow these steps to effectively change your passwords:
- Start with High-Priority Accounts: Begin by changing the passwords for your high-priority accounts, such as email, online banking, and social media platforms. These accounts often contain sensitive information and can be prime targets for cybercriminals.
- Create Strong, Unique Passwords: When changing your passwords, ensure that you create strong, unique passwords for each account. Use a combination of upper and lowercase letters, numbers, and special characters. Avoid using easily guessable information, such as your name or birthdate, and never reuse passwords across multiple accounts.
- Consider Using a Password Manager: A password manager can help you generate and securely store complex passwords. It can also remember them for you, eliminating the need to remember numerous passwords. This simplifies your password management and reduces the risk of using weak or repetitive passwords.
- Implement Two-Factor Authentication (2FA): Enable two-factor authentication (2FA) wherever possible. 2FA adds an extra layer of security by requiring an additional verification step, such as a unique code sent to your mobile device, in addition to your password. This provides an added level of protection against unauthorized access.
- Regularly Update Your Passwords: Changing your passwords should not be a one-time event. Make it a habit to update your passwords periodically, ideally every three to six months. Regularly changing your passwords can further enhance your security and reduce the risk of compromise.
- Secure Password Recovery Options: Review and update the password recovery options for your accounts. Ensure that the associated email addresses and phone numbers are accurate and under your control. This helps prevent unauthorized individuals from attempting to reset your passwords or gain access to your accounts through recovery methods.
- Monitor Your Accounts: After changing your passwords, closely monitor your accounts for any suspicious activities. Keep an eye on login history, email notifications, and any changes made to your account settings. If you notice any unauthorized access or suspicious activities, take immediate action to secure your accounts and report the incidents to the respective service providers.
Remember, changing your passwords regularly and using strong, unique passwords are essential practices to protect your accounts and personal information. By taking this step, you strengthen your security posture and make it significantly more challenging for cybercriminals to gain unauthorized access to your sensitive data.
Enable Two-Factor Authentication
Enabling two-factor authentication (2FA) is an important step to enhance the security of your online accounts. By adding an extra layer of verification, 2FA provides an additional barrier that can significantly reduce the risk of unauthorized access. Here’s what you need to know about enabling and using 2FA:
Understand Two-Factor Authentication: Two-factor authentication adds an extra step to the login process, requiring two separate factors to verify your identity. Typically, this involves something you know (like a password) and something you have (like a unique code generated by an app or sent to your mobile device).
Choose the Right 2FA Method: There are several methods available for implementing 2FA, so choose the option that suits you best. Common methods include verification codes sent via SMS, authentication apps like Google Authenticator or Authy, hardware tokens, or biometric factors like fingerprint or facial recognition.
Enable 2FA on Important Accounts: Start by enabling 2FA on your most critical accounts, such as email, online banking, and social media. These accounts often contain sensitive information and serve as gateways to other platforms. Secure them first to establish a stronger foundation for your online security.
Follow the Setup Instructions: Each platform or service may have slightly different steps for enabling 2FA. Refer to the account settings or security options and follow the instructions provided. The setup process usually involves linking your account with a phone number, installing an authentication app, or using a hardware token.
Generate Backup Codes: Many 2FA methods offer backup codes that you can use if you don’t have access to your primary authentication method. These codes are usually one-time-use and can help you regain access to your account if you lose your phone or encounter any issues with your primary method of authentication.
Maintain Access to Authentication Methods: Ensure that you have access to your chosen 2FA method at all times. Keep your authentication app updated, back up your codes, and securely store any hardware tokens. It’s also important to keep your phone number up to date so that you can receive SMS verification codes if necessary.
Be Prepared for Verification: When 2FA is enabled, be prepared for an extra step during the login process. This might involve entering a verification code from an app, receiving a code via SMS, or using a biometric factor. The inconvenience is worth the increased security it provides.
Regularly Review and Update: Periodically review your 2FA settings and make any necessary updates. Remove any inactive or unused 2FA methods, update phone numbers, and ensure that you have the latest version of the authentication app. Regular maintenance helps keep your 2FA implementation effective and up to date.
Enabling two-factor authentication significantly enhances the security of your accounts by adding an additional layer of protection. By taking advantage of this security measure, you greatly reduce the risk of unauthorized access to your personal information and mitigate the potential impact of a data breach or password compromise.
Monitor Your Financial Accounts
When your information is on the Dark Web, it’s crucial to monitor your financial accounts closely. By regularly reviewing your account activity, you can detect any unauthorized transactions or suspicious activities early on and take immediate action to mitigate damage. Here’s how you can effectively monitor your financial accounts:
Review Account Statements: Take the time to carefully review your bank statements, credit card statements, and any other financial account statements you have. Look for any unfamiliar transactions, charges, or withdrawals that you did not authorize or recognize.
Set Up Account Alerts: Many financial institutions offer account alert services that notify you of any unusual activities on your accounts. Set up alerts for transactions above a certain threshold, changes to personal information, or any suspicious activity. These alerts can help you stay informed and take prompt action if necessary.
Monitor Online Access: Regularly log into your online banking and financial accounts to check for any unauthorized access. Keep an eye out for any changes to your account settings, contact information, or added beneficiaries that you did not authorize.
Use Mobile Banking Apps: Mobile banking apps can be convenient tools for monitoring your financial accounts on the go. Install the official mobile apps provided by your financial institutions and regularly check for any suspicious transactions or activities.
Check Credit Card Usage: If you have credit cards, monitor your usage and closely review your credit card statements. Look for any unauthorized charges or fraudulent activities. Contact your credit card company immediately if you notice anything questionable.
Keep Passwords Updated: Regularly update the passwords for your financial accounts, ensuring they are strong and unique. Avoid using easily guessable information and never reuse passwords across multiple accounts. Strong passwords are vital in protecting your financial information.
Report Suspicious Activities: If you notice any suspicious activities or unauthorized transactions on your financial accounts, report them to your financial institution immediately. They will guide you on the necessary steps to resolve the issue and recover any losses.
Consider Account Monitoring Services: Some financial institutions offer account monitoring services that can alert you to any unusual activities or potential fraud. Consider enrolling in such services to enhance your account security and receive proactive notifications of any concerning transactions.
Stay Informed About Security Measures: Educate yourself about the security measures provided by your financial institutions. Familiarize yourself with their fraud protections, policies, and customer support services. Being informed empowers you to take the appropriate actions in case of any fraudulent activities.
By regularly monitoring your financial accounts, you can quickly identify and respond to any suspicious activities or unauthorized transactions. Timely detection and action are crucial in minimizing the potential financial impact of having your information on the Dark Web.
Contact Your Financial Institution
When you discover that your information is on the Dark Web, it is imperative to contact your financial institution as soon as possible. Promptly notifying them helps protect your financial accounts and minimizes the potential impact of any fraudulent activities. Here’s what you need to do when contacting your financial institution:
Notify Your Bank, Credit Card Companies, and Other Financial Institutions: Reach out to your bank, credit card companies, and other relevant financial institutions immediately after discovering the compromise. Inform them about the situation and provide any relevant details regarding your compromised information.
Explain the Situation Clearly: Clearly explain to the customer service representative that your personal information has been exposed on the Dark Web. Describe the potential risks and any suspicious activities you have noticed to ensure that they understand the urgency and seriousness of the situation.
Ask to Freeze or Monitor Your Accounts: Inquire about the option to freeze your accounts temporarily to prevent any unauthorized transactions. Freezing your accounts ensures that no one can access or conduct activity without your permission. Alternatively, ask if they offer account monitoring services to detect and alert you to any suspicious activities.
Follow their Guidance on Security Measures: Financial institutions are well-equipped to handle security incidents and can provide you with valuable guidance and recommendations. Follow their instructions on any additional security measures you should implement, such as changing passwords, enabling two-factor authentication, or providing any necessary documentation to safeguard your accounts.
Report Any Unauthorized Transactions: If you notice any unauthorized transactions or fraudulent activities on your financial accounts, report them to your financial institution immediately. They will guide you on the necessary steps to initiate a dispute, investigate the matter, and potentially recover any financial losses.
Keep Documentation and Records: Maintain thorough records of your interactions with your financial institution. Keep copies of any correspondence, notes of conversations, transaction dispute forms, or case numbers provided to you. These records can serve as evidence and help you in the event of any further complications or disputes.
Be Diligent in Account Monitoring: After notifying your financial institution, continue to monitor your accounts closely for any suspicious activities. Regularly review your statements, log into your online accounts, and promptly address any concerns or discrepancies that you detect.
Stay Informed about Security Policies: Familiarize yourself with the security policies and fraud protections offered by your financial institution. Stay updated on any changes, and educate yourself about the steps they take to safeguard your accounts. This knowledge empowers you to take proactive measures to protect your financial well-being.
Contacting your financial institution promptly is crucial in securing your accounts and minimizing the potential damage caused by having your information on the Dark Web. By following their guidance and addressing the situation proactively, you enhance your chances of recovering from any fraudulent activities and restoring the integrity of your financial accounts.
Freeze Your Credit
When your information is on the Dark Web, it’s important to take steps to protect your credit and prevent identity theft. One effective measure is to freeze your credit, also known as a security freeze. By freezing your credit, you restrict access to your credit report and make it more difficult for fraudsters to open new accounts in your name. Here’s how you can freeze your credit:
Understand What a Credit Freeze Does: A credit freeze restricts access to your credit report, making it challenging for potential creditors to view your credit history and issue new lines of credit in your name. It does not impact your existing accounts or credit score.
Contact the Major Credit Bureaus: Contact each of the three major credit bureaus – Equifax, Experian, and TransUnion – to initiate a credit freeze. You can do this online, over the phone, or through mail, depending on the bureau’s specific procedures.
Provide the Requested Information: When requesting a credit freeze, be prepared to provide personal information such as your full name, Social Security number, date of birth, and address. The credit bureaus will require this information to authenticate your identity and initiate the freeze.
Keep a Record of Your Pin or Password: After placing a credit freeze, each credit bureau will provide you with a unique PIN or password. Keep this information in a safe and secure location, as you will need it to lift or thaw the freeze temporarily if you require access to your credit.
Understand the Impact of a Credit Freeze: While a credit freeze offers robust protection, it can also temporarily hinder your ability to apply for new credit. If you plan to apply for a loan or open new accounts, you will need to lift the freeze temporarily for the duration of the application process.
Consider a Credit Freeze for Your Minor Children: Identity thieves may also target the personal information of minors. If you have children, consider freezing their credit to prevent fraudulent activity and protect their identities until they are of age to establish credit.
Monitor Your Existing Accounts: While a credit freeze provides an additional layer of protection, it’s essential to remain vigilant and monitor your existing accounts for any suspicious activities. Regularly review your bank statements, credit card transactions, and other financial accounts for any unauthorized transactions or signs of identity theft.
Be Mindful of Lifting the Freeze: If you need to temporarily lift the credit freeze, such as when applying for credit or financing, ensure you do so for a specific time frame and with a trusted entity. Thawing the freeze for longer than necessary or with unknown parties can increase the risk of your information being compromised.
Freezing your credit is a proactive step to protect your financial well-being and prevent unauthorized access to your credit information. It provides peace of mind by adding an extra layer of security, making it significantly more challenging for identity thieves to misuse your personal data.
File a Report with Law Enforcement
Discovering that your information is on the Dark Web is a serious matter that warrants reporting to law enforcement agencies. Filing a report can initiate an investigation and potentially aid in apprehending the individuals responsible. Here’s what you should know about reporting the incident to law enforcement:
Contact Your Local Law Enforcement Agency: Begin by contacting your local law enforcement agency to report the compromise of your personal information. Provide them with as much information as possible, including details about the incident, any evidence you have gathered, and any suspicious activities related to the compromise.
File a Police Report or Incident Report: Depending on the jurisdiction and the nature of the incident, you may need to file a police report or an incident report. Provide relevant details to law enforcement officers, such as the type of personal information compromised, any financial losses suffered, and any other pertinent information regarding the breach.
Cooperate Fully with the Investigation: Once the report is filed, cooperate fully with the law enforcement agency handling the case. This may involve providing additional information, documentation, or assisting in any way necessary in the investigation process. The information you provide could be instrumental in identifying and apprehending the individuals responsible.
Obtain a Copy of the Police Report: Request a copy of the police report or incident report filed regarding the compromise of your information. This document is important for your records and may be required by credit bureaus, financial institutions, or other entities involved in resolving any fraudulent activities resulting from the breach.
Keep Communication Channels Open: Maintain regular communication with the law enforcement agency assigned to your case. Follow up periodically to inquire about the status of the investigation and provide any additional information that may have come to light. Staying in touch ensures your case continues to receive attention and increases the chances of a successful resolution.
Inform Them of Any Developments: If you discover any new information or suspect any additional fraudulent activities related to the compromise, promptly inform the law enforcement agency. Sharing ongoing developments can provide valuable leads and contribute to building a stronger case against the individuals responsible for the breach.
Document All Communication: Maintain a record of all communication with law enforcement, including dates, times, names of officers or investigators, and any relevant information discussed. This documentation can be essential in the event of any disputes, follow-up inquiries, or the need for additional assistance with your case.
Be Patient and Persistent: Resolving a case involving the compromise of personal information can be a complex and time-consuming process. Be patient yet persistent with the law enforcement agency conducting the investigation. Continue to provide any requested information and follow their guidance until the issue is resolved satisfactorily.
By reporting the compromise of your information to law enforcement, you contribute to the efforts to bring those responsible to justice. Your cooperation and prompt action can potentially prevent further harm to yourself and help protect others from falling victim to similar cybercrimes.
Monitor Your Online Presence
When your personal information is on the Dark Web, it’s crucial to monitor your online presence closely. By staying vigilant and aware of any changes or suspicious activities, you can take immediate action to protect your reputation and prevent further compromise. Here’s how you can effectively monitor your online presence:
Search for Your Name: Conduct regular searches using search engines to see what information appears when you search for your name. Look for any unusual or unauthorized sites, social media profiles, or online content that may be associated with your name.
Set Up Google Alerts: Set up Google Alerts for your name, email address, and other relevant personal information. This way, you will receive notifications whenever your information appears online, enabling you to promptly address any potential issues or unauthorized appearances.
Review Your Social Media Accounts: Regularly review the privacy settings on your social media accounts to ensure they are appropriately configured. Take note of any changes to your account settings, contact information, or privacy settings that you did not authorize. Remove any unfamiliar connections or followers from your profiles.
Monitor Your Digital Footprint: Be mindful of what you share online and consider the potential impact on your privacy and security. Regularly review your past posts, photos, and comments on social media platforms and remove any content that might reveal too much personal information or compromise your security.
Be Wary of Phishing Attempts: Stay vigilant for phishing attempts through emails, messages, or other communication channels. Be cautious of clicking on links or providing personal information in response to unsolicited requests. Verify the legitimacy of messages before taking any action.
Google Yourself: Regularly search for your name on Google to see how you are being represented online. Pay attention to any negative or false information that may have appeared. Consider reaching out to website administrators or content creators to request the removal or correction of inaccurate information.
Secure Your Online Accounts: Strengthen the security of your online accounts by using strong, unique passwords, enabling two-factor authentication (2FA), and regularly updating your security settings. This reduces the risk of unauthorized access and protects your online presence.
Be Cautious with Personal Information Requests: Be cautious when providing personal information online or responding to requests for data. Verify the credibility and legitimacy of the recipient before sharing any sensitive information. Be especially wary of requests for financial or personally identifiable information.
Report Impersonation or Fake Accounts: If you come across any accounts impersonating your identity or using your personal information without permission, report them to the respective social media platforms. Provide evidence and relevant information to expedite the removal of these accounts.
Keep Your Software Updated: Ensure that your devices and applications are running the latest versions and have up-to-date security patches. Regularly update your antivirus software and enable automatic updates to protect against malware and viruses that could compromise your online presence.
By actively monitoring your online presence, you can quickly identify any unauthorized appearances or potential threats. Taking proactive steps to secure your online accounts and address any issues promptly helps protect your reputation and minimizes the risk of further compromise.
Consider Using a Dark Web Monitoring Service
When your personal information is on the Dark Web, considering the use of a Dark Web monitoring service can provide an added layer of protection and early detection. These services continuously scan the Dark Web for compromised information and alert you if your data is found. Here’s what you need to know about Dark Web monitoring services:
How Dark Web Monitoring Works: Dark Web monitoring services utilize specialized tools and technologies to scan the hidden corners of the internet, including Dark Web marketplaces, forums, and websites, for potential exposures of your personal information. They leverage advanced algorithms to identify and match your compromised data.
Receive Timely Alerts: When a Dark Web monitoring service detects your compromised information, they will promptly notify you through alerts. These alerts can be sent via email, SMS, or through their dedicated platform, ensuring you receive the necessary information to take immediate action.
Types of Information Monitored: Dark Web monitoring services typically track a wide range of personal information, such as email addresses, usernames, passwords, social security numbers, credit card details, and more. Depending on the service, they may also monitor specific information related to your industry or organization.
Take the Necessary Steps to Protect Yourself: Dark Web monitoring services not only notify you of compromised information but also provide guidance on the appropriate steps to take. They may advise you to change passwords, enable two-factor authentication (2FA), freeze your credit, or contact relevant authorities or financial institutions.
Consideration for Personal and Business Use: Dark Web monitoring services are available for both personal and business use. Personal monitoring helps safeguard your personal identity, whereas business monitoring focuses on protecting your company’s sensitive data, intellectual property, and employee information.
Evaluate Service Features and Reputation: When considering a Dark Web monitoring service, evaluate their features, reputation, and track record. Look for services that offer comprehensive monitoring, timely alerts, a user-friendly interface, and positive customer reviews. Research their data protection policies to ensure the privacy and security of your information.
Cost of Dark Web Monitoring: Dark Web monitoring services typically operate on a subscription-based model. The cost may vary depending on the level of monitoring, features offered, and the number of individuals or accounts being monitored. Evaluate pricing options and choose a plan that aligns with your needs and budget.
Supplement Security Measures: Dark Web monitoring services should be seen as a supplement to your overall security measures. They do not guarantee complete protection but serve as an additional layer to detect potential compromises. It’s essential to maintain good cybersecurity practices and regularly update your passwords, enable 2FA, and stay vigilant for phishing attempts.
Consider using a Dark Web monitoring service to proactively monitor your compromised information on the Dark Web. These services can alert you to potential threats, allowing you to take swift action to protect yourself and mitigate the risks associated with having your information on the Dark Web.
Conclusion
Discovering that your personal information is on the Dark Web can be a distressing and alarming experience. However, by taking swift and decisive action, you can protect yourself from the potential risks and minimize the impact of having your information exposed. The key takeaway points to remember are:
In this article, we explored what the Dark Web is, how your information ends up on it, signs to look out for, and the steps you should take if your information is compromised. We emphasized the importance of staying calm and not panicking, as well as the significance of assessing the damage and changing your passwords.
We highlighted the crucial role of enabling two-factor authentication (2FA) and monitoring your financial accounts for any unauthorized activities. Additionally, we stressed the importance of contacting your financial institution, freezing your credit, filing a report with law enforcement, and closely monitoring your online presence.
We also mentioned the option of utilizing Dark Web monitoring services as an additional layer of protection. These services can help detect and notify you of compromised information, allowing you to take immediate action to secure your accounts and minimize the potential risks.
Remember, taking proactive steps to safeguard your personal information and stay vigilant online is essential in the digital age. Implement strong security measures, practice good cybersecurity habits, and regularly monitor your accounts and online presence to stay one step ahead of cybercriminals.
While it’s impossible to eliminate all risks completely, by following the guidelines and recommendations outlined in this article, you can significantly reduce the likelihood and impact of your information being exposed on the Dark Web. Stay informed, stay cautious, and stay proactive in protecting your digital identity.