Introduction
Welcome to the world of junk email, where your inbox is bombarded with unwanted and unsolicited messages. Junk email, also known as spam, has become a pervasive issue in the digital age. It is an unfortunate side effect of the convenience and connectivity that the internet provides. Dealing with this deluge of unwanted messages can be frustrating, time-consuming, and even present security risks.
Junk email refers to any unsolicited or unwanted messages that are sent to your email address. These messages often come in the form of advertisements, offers for dubious products or services, phishing attempts, or scams. They clutter your inbox and can make it difficult to find and manage legitimate messages. Not only does junk email waste your time, but it can also pose risks to your personal information and computer security.
There are various forms of junk email that you may encounter. Some common types include:
- Advertisement spam: These messages are sent to promote products, services, or websites, often with the intention of making a sale or generating revenue for the sender.
- Phishing emails: Phishing emails are disguised as legitimate messages from reputable organizations such as banks, social media platforms, or online retailers. The aim is to trick you into revealing sensitive information such as login credentials or financial details.
- Malware-infected emails: These emails contain attachments or links that, when clicked or opened, can download malware onto your device, compromising your security and privacy.
- Chain letters: Chain letters are messages that encourage you to forward them to others. They often include false promises of good luck or dire consequences if you break the chain.
The effects of junk email can be detrimental. It not only clutters your inbox but also wastes your valuable time sifting through and deleting these unwanted messages. Additionally, engaging with or falling victim to phishing attempts or malware-infected emails can lead to identity theft, financial loss, or damage to your personal and professional reputation.
Junk email is sent through various methods, including:
- Email address harvesting: Spammers use automated software to scrape the internet for email addresses, often finding them on websites, forums, or social media platforms.
- Purchased or traded lists: Spammers acquire email addresses by purchasing or trading lists with other spammers.
- Botnets: Spammers may control networks of infected computers, known as botnets, to send out massive volumes of junk email.
- Phishing: Phishers trick individuals into unknowingly providing their email addresses, which are then used for spamming purposes.
Protecting yourself from junk email requires a combination of proactive measures and cautious online behavior. In the subsequent sections, we will explore best practices for dealing with junk email, avoiding scams, and safeguarding your online presence. Let’s dive in!
Definition of Junk Email
Junk email, commonly known as spam, refers to unsolicited and unwanted messages that are sent to your email address. These messages are typically sent in bulk and are often of a commercial or promotional nature, although they can also include phishing attempts or malicious content.
The term “junk email” accurately describes the nature of these messages—they are essentially digital clutter that fills your inbox and distracts from important or legitimate communication. These unsolicited messages can come from a variety of sources, including individuals, businesses, or even automated systems.
It’s important to note that not all unsolicited emails are considered junk email. For example, if you have willingly subscribed to a newsletter or mailing list, you may receive emails that you technically didn’t request, but they are not considered spam because you gave your consent to receive them. However, when these unsolicited emails become overwhelming or unwanted, you can take steps to unsubscribe or mark them as spam to prevent them from filling your inbox.
Junk email can take different forms. One common type is advertisement spam, where emails are sent to promote products, services, or websites. These messages often contain persuasive language and enticing offers, aiming to encourage recipients to make a purchase or visit a particular website.
Another form of junk email is phishing emails. These messages are designed to trick recipients into providing sensitive information, such as login credentials or financial details. Phishers often impersonate trusted organizations, such as banks, social media platforms, or popular online retailers, and create emails that appear legitimate. The goal is to deceive individuals into revealing their personal information, which can then be used for identity theft or fraudulent activities.
Junk email can also contain malware-infected attachments or links. Clicking on these attachments or links can lead to the download and installation of malicious software on your device. This malware can compromise your privacy, steal sensitive information, or even take control of your computer.
The volume of junk email can vary greatly. While some individuals may only receive occasional spam messages, others may find their inboxes inundated with a constant stream of junk email. The prevalence and persistence of junk email make it crucial to take measures to protect yourself, your personal information, and your computer systems.
In the following sections, we will explore the various forms of junk email, the effects it can have on individuals and businesses, as well as effective strategies to combat and prevent this digital nuisance.
Common Forms of Junk Email
Junk email comes in various forms, each with its own purpose and characteristics. Understanding these common forms can help you better recognize and deal with spam in your inbox. Here are some of the most prevalent types of junk email:
- Advertisement Spam: This is perhaps the most recognizable form of junk email. Advertisement spam includes unsolicited messages promoting products, services, or websites. These emails often tout incredible deals, exclusive offers, or limited-time discounts. They may also feature catchy subject lines designed to grab your attention and entice you to open the email.
- Phishing Emails: Phishing emails are crafted to deceive recipients into disclosing sensitive information or performing actions that benefit the sender. These messages typically impersonate trusted sources such as banks, social media platforms, or online retailers. Phishers use psychological tactics and persuasive techniques to create a sense of urgency or legitimacy, prompting individuals to click on malicious links or provide personal information like passwords or social security numbers.
- Malware-Infected Emails: Another dangerous form of junk email is those containing malware attachments or links. Clicking on these attachments or links can lead to the installation of malicious software on your device. The malware can then compromise your data, invade your privacy, or even turn your device into a part of a botnet, which spammers can use to send even more junk email.
- Chain Letters: Chain letters have been around for years, and they have simply taken on a digital form. These emails often come with a story or a plea to forward the message to others. They may carry superstitious beliefs, false promises of good luck, or warnings of misfortune if the chain is broken. While harmless in nature, they contribute to the overall clutter of your inbox and should be avoided.
- Survey or Contest Emails: In an attempt to gather personal information or scam individuals, spammers often send emails claiming that you have won a prize or that you can participate in a survey or contest. These messages are designed to trick you into providing valuable information such as your name, address, or credit card details. It’s important to be cautious when receiving such emails and to verify the legitimacy of the sender before taking any action.
These are just a few examples of the many forms of junk email that individuals and businesses encounter on a daily basis. It’s worth noting that spammers continually adapt their tactics to evade filters and gain attention, so new forms of spam emails may emerge over time.
In the next section, we will explore the effects of junk email, shedding light on why it’s important to take steps to prevent and manage this unwanted digital clutter.
Effects of Junk Email
Junk email can have a range of negative effects on individuals, businesses, and the overall online ecosystem. Understanding these effects is crucial to fully grasp the importance of actively managing and protecting yourself against spam. Here are some of the main effects of junk email:
- Time Wasting and Productivity Loss: Dealing with junk email can be incredibly time-consuming. Sorting through spam messages, deleting them, and managing your inbox can eat up valuable time that could be better spent on important tasks. The constant influx of junk email can also distract you from focusing on your work or daily activities, leading to a loss of productivity.
- Email Clutter: The sheer volume of junk email can quickly overwhelm your inbox and bury important messages. This clutter makes it difficult to find and respond to legitimate emails in a timely manner. It can also lead to missed opportunities or important communications getting lost in the sea of spam.
- Financial Scams and Losses: One of the most concerning effects of junk email is the risk of falling victim to financial scams. Phishing emails, in particular, can trick individuals into providing sensitive information, such as banking details or credit card numbers. This information can be used for identity theft or fraudulent activities, leading to significant financial losses and potential long-term consequences.
- Privacy Invasion: Junk email can also invade your privacy. Some spam messages may try to collect personal information by tricking you into clicking on links or opening malicious attachments. Once your privacy has been compromised, your personal information may be sold or misused by spammers or even other cybercriminals.
- Spread of Malware and Viruses: Opening attachments or clicking on links in junk email can expose your computer or device to malware and viruses. This can result in data breaches or system compromises, posing a threat to both your personal and professional information.
- Overloading Email Servers: The massive volume of junk email being sent can overwhelm email servers and impact their performance. This not only affects individuals’ ability to send and receive legitimate emails promptly but also disrupts the overall efficiency of email communication networks.
- Reputation Damage: If your email account becomes compromised and starts sending out spam without your knowledge, it can result in your email address being blacklisted. This can lead to your legitimate emails being blocked or marked as spam by other recipients, potentially damaging your online reputation.
These effects highlight the importance of taking proactive measures to protect yourself from junk email. By implementing strategies to reduce spam, you can minimize the negative impact it has on your time, productivity, privacy, and security.
In the next section, we will explore how junk email is sent and the methods used by spammers to flood inboxes with unwanted messages.
How Junk Email is Sent
Junk email, or spam, is sent using various methods and techniques that allow spammers to inundate inboxes with their unwanted messages. Understanding how junk email is sent can shed light on the strategies used by spammers and help individuals and organizations better protect themselves. Here are some common methods by which junk email is sent:
- Email Address Harvesting: Spammers often use automated software to scrape the internet in search of email addresses. These programs can scan websites, forums, social media platforms, and other online sources to collect email addresses. Once obtained, these email addresses are added to spam mailing lists, allowing spammers to send mass emails to a wide range of recipients.
- Purchased or Traded Lists: Some spammers acquire email addresses through the purchase or trade of email lists. These lists, compiled by third parties, may include email addresses of individuals who have previously shown interest in specific products, services, or industries. By purchasing or trading these lists, spammers gain access to a ready-made audience for their spam campaigns.
- Botnets: A botnet is a network of infected computers controlled by a single entity. Spammers often utilize botnets to distribute junk email on a massive scale. By infecting computers with malware, spammers can gain control over them, turning them into spam-sending machines. These botnets can collectively send out millions of spam messages, overwhelming email servers and flooding inboxes.
- Phishing: Phishers use a combination of social engineering and technical tricks to trick individuals into providing their email addresses. They may create websites or online forms that appear legitimate, enticing users to enter their email addresses. Once obtained, these email addresses can be used for spamming purposes.
- Email Spoofing: Spammers may employ email spoofing techniques to send junk email. Email spoofing involves forging the sender’s email address, making it appear as if the message is coming from a different sender. By using legitimate-looking email addresses as the “From” field, spammers attempt to bypass spam filters and increase the chances of their messages being opened.
- Mass Emailing Software: Spammers also utilize specialized software that enables them to send mass emails easily. These software tools allow spammers to create templates, customize email content, and send messages to numerous recipients simultaneously. By automating the process, spammers can quickly reach a large number of email addresses in a short period.
It’s important to note that spamming techniques continue to evolve, and spammers are constantly adapting their methods to bypass spam filters and deceive recipients. As a result, protecting yourself from junk email requires a layered approach that includes email filtering, spam detection tools, and user awareness.
In the next section, we will explore effective strategies to protect yourself from junk email and reduce its impact on your inbox and online activities.
How to Protect Yourself from Junk Email
Protecting yourself from junk email, or spam, is essential to maintaining a clean and organized inbox, safeguarding your personal information, and preventing potential security risks. While it is impossible to completely eliminate all spam, there are several effective strategies you can implement to reduce its impact. Here are some steps you can take to protect yourself from junk email:
- Use a Reliable Email Service Provider: Choose an email service provider that has robust spam filtering capabilities. Established providers often employ advanced algorithms and technologies to detect and filter out spam before it reaches your inbox. Research and opt for providers with a good reputation for spam protection.
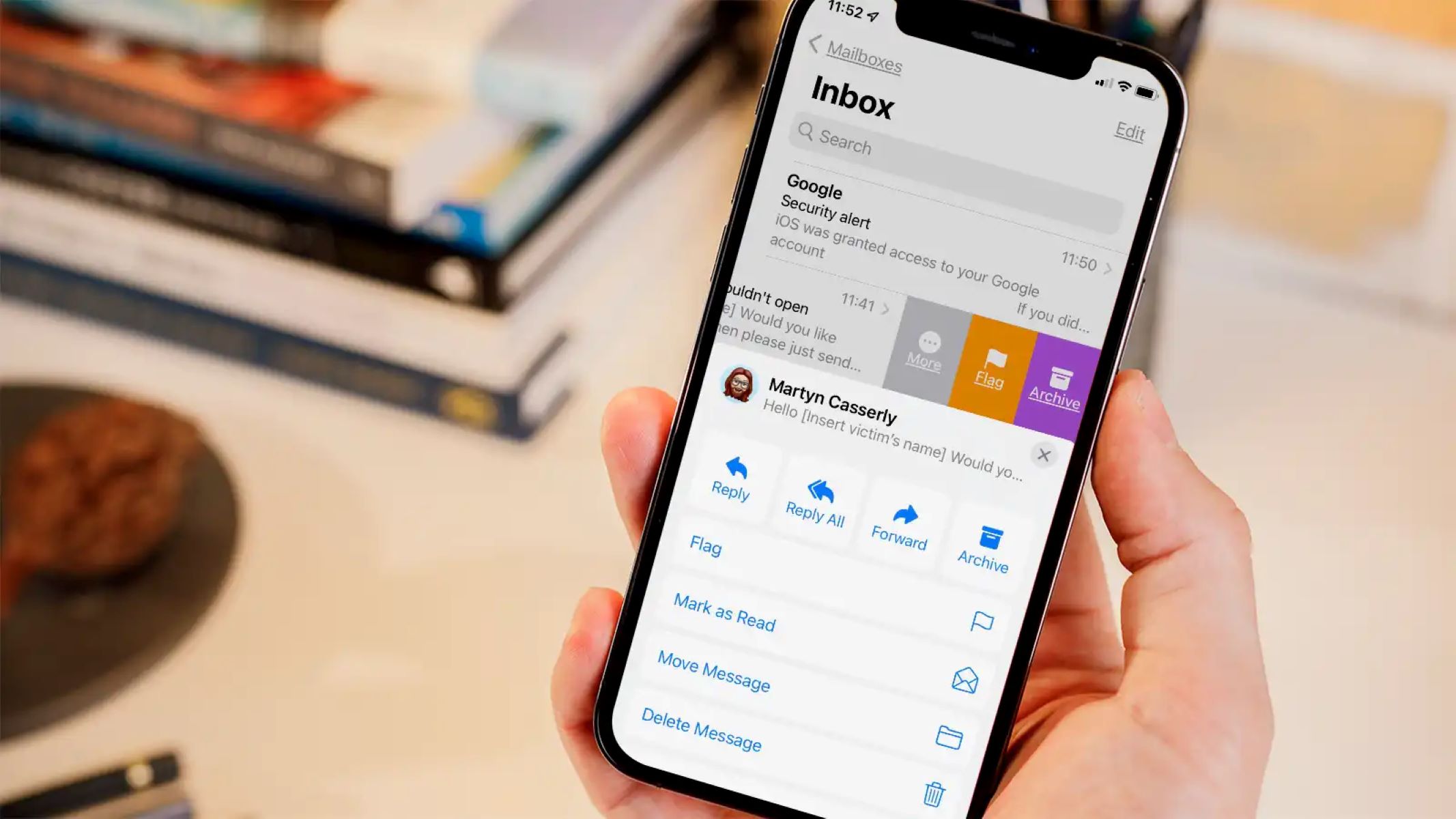
- Enable Spam Filters: Make sure that your email account’s spam filters are enabled. These filters analyze incoming messages and mark or automatically move suspected spam emails to a separate spam or junk folder. Regularly check your spam folder, as legitimate emails may occasionally be marked as spam in error.
- Avoid Publishing Your Email Address Publicly: Be cautious about sharing your email address publicly, especially on websites, online forums, and social media platforms. Spammers use automatic tools to scrape the internet for email addresses, so limiting their exposure can reduce the amount of spam you receive.
- Be Selective with Newsletter Subscriptions: Exercise caution when subscribing to newsletters, mailing lists, or online services. Only subscribe to reputable sources that you trust and that have a clear privacy policy. Verify that they have strict data protection measures in place to prevent your email address from being sold or shared with spammers.
- Use Disposable Email Addresses: Consider using disposable email addresses for online registrations or when signing up for services that may send you promotional emails. Disposable email services provide you with a temporary email address that forwards messages to your actual inbox. If you start receiving spam, you can easily discard the disposable address without affecting your main email account.
- Be Cautious with Links and Attachments: Exercise caution when clicking on links or opening attachments, especially in emails from unknown or suspicious senders. Links or attachments in spam emails may contain malware or lead to phishing websites. Ensure that you have up-to-date antivirus and anti-malware software installed on your computer or device to detect and block potential threats.
- Don’t Respond to or Engage with Spam: It’s essential not to respond to or engage with spam messages. Replying to spam or clicking on unsubscribe links in suspicious emails can confirm to spammers that your email address is active, leading to an increase in spam. Instead, mark the email as spam or simply delete it.
- Regularly Update Your Devices and Software: Keep your devices, operating systems, and software up to date with the latest security patches. Regular updates help protect your devices from known vulnerabilities that spammers and hackers exploit to gain access to your email and personal information.
By implementing these preventive measures and making them a part of your regular online habits, you can significantly reduce the amount of junk email you receive and minimize the associated risks.
In the next section, we will explore strategies for avoiding junk email scams and how to identify and handle suspicious messages.
Avoiding Junk Email Scams
Junk email scams can be incredibly deceptive and pose serious risks to your personal and financial security. It’s essential to be aware of the common tactics used by scammers and to remain vigilant when it comes to identifying and avoiding these scams. Here are some strategies to help you steer clear of junk email scams:
- Be Skeptical: Develop a healthy skepticism when it comes to emails that seem too good to be true. Offers or claims that promise extraordinary benefits, tremendous riches, or unrealistic rewards are often red flags for scams.
- Verify the Sender: Check the sender’s email address and verify that it matches the organization or service they claim to represent. Be cautious of emails that have generic or misspelled email addresses, as legitimate organizations usually use professional and consistent email addresses.
- Pay Attention to Grammar and Spelling: Scammers often make mistakes in grammar, spelling, or formatting. Poorly written emails may indicate a scam attempt, as legitimate organizations typically maintain a high level of professionalism in their communications.
- Avoid Urgent Requests: Be wary of emails that create a sense of urgency or pressure you to take immediate action. Scammers often use time-sensitive language or threats to manipulate individuals into making hasty decisions.
- Don’t Share Personal Information: Legitimate organizations will not request your personal or financial information via email. Be cautious of emails that ask for sensitive details such as passwords, social security numbers, credit card information, or login credentials. Providing such information could lead to identity theft or financial loss.
- Verify Suspicious Links: Hover your mouse over hyperlinks in emails to see the actual destination URL before clicking on them. If the URL appears suspicious or doesn’t match the purported sender, do not click on it. Instead, manually type the URL in a new browser window to navigate to the legitimate website, if necessary.
- Double-Check Offers, Contests, or Prizes: Be cautious of emails claiming that you’ve won a contest or prize, especially if you didn’t participate in any such activities. Verify the legitimacy of the offer by contacting the organization directly through their official website or customer service number.
- Use Email Filters and Anti-Spam Software: Enable email filters and use anti-spam software to automatically detect and block suspicious emails. These tools can help identify and flag potential scam emails, minimizing the risk of falling victim to junk email scams.
- Educate Yourself: Stay informed about the latest scamming techniques and common indicators of phishing and fraud. Familiarize yourself with legitimate practices of reputable organizations, such as how they typically communicate with their customers, so you can quickly identify suspicious emails.
Remember, scammers are constantly evolving their tactics, so it’s important to remain vigilant and skeptical while engaging with your email. If you suspect an email to be a scam, it’s best to err on the side of caution and not respond or provide any personal information.
In the next section, we will explore best practices for handling and managing junk email to maintain an organized and secure inbox.
Best Practices for Dealing with Junk Email
Dealing with junk email can be an ongoing challenge, but by implementing best practices, you can effectively manage and minimize its impact on your inbox and online experience. Here are some recommended strategies for dealing with junk email:
- Regularly Check and Empty your Spam Folder: Keep an eye on your spam folder to ensure that legitimate emails are not mistakenly captured as spam. Review the messages in your spam folder periodically and delete them. This helps minimize the chance of missing important emails that may have been marked incorrectly as spam.
- Use the Block or Unsubscribe Option: Many email providers offer options to block or unsubscribe from specific senders or types of emails. If you consistently receive junk email from a particular sender, use these options to prevent future emails from reaching your inbox.
- Report Spam: Most email providers have a feature that allows you to report a message as spam. By reporting spam, you contribute to the improvement of spam filters and help protect other users from similar junk email in the future.
- Create Custom Filters: Take advantage of the filtering options provided by your email service provider. Create filters that automatically move incoming emails from specific senders or with particular keywords to dedicated folders, keeping your inbox organized and reducing the visibility of junk email.
- Be Cautious with Forwarding: Before forwarding emails to others, ensure that the content is legitimate and relevant. Forwarding junk email to others can contribute to the spread of spam and potentially expose recipients to scams or malware.
- Keep your Email Address Private: Be selective about sharing your email address and avoid posting it publicly on websites or social media platforms. This reduces the chances of your email address being harvested by spammers.
- Use Disposable Email Addresses: Consider using disposable email addresses when signing up for online services or subscriptions. By using a disposable address for specific sites, you can easily dispose of it if it starts receiving excessive junk email.
- Stay Informed: Keep yourself updated on the latest spamming tactics and emerging trends. Educate yourself on common strategies used by scammers and stay aware of new techniques to avoid falling victim to junk email scams.
- Regularly Review and Update Email Settings: Take the time to review your email settings periodically. Check for any changes in spam filtering policies, security options, or privacy settings provided by your email service provider. Adjust these settings to suit your preferences and enhance your protection against junk email.
- Use Email Authentication Methods: Enable and implement email authentication methods like SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail). These protocols help verify the authenticity of incoming emails and reduce the chance of receiving spoofed or forged messages.
By following these best practices, you can effectively manage your inbox, reduce the impact of junk email, and maintain a safe and productive email experience.
Now that we’ve explored best practices for dealing with junk email, let’s conclude with a summary of the key points discussed.
Conclusion
Junk email, or spam, is an ongoing challenge in the digital age, cluttering our inboxes, wasting our time, and posing potential security risks. In this article, we examined the definition of junk email and explored its common forms, such as advertisement spam, phishing emails, malware-infected messages, chain letters, and survey or contest emails.
We also discussed the effects of junk email, including time wastage, email clutter, financial scams, privacy invasion, spread of malware, overloading of email servers, and reputation damage. Understanding these effects emphasizes the importance of actively managing and protecting ourselves against junk email.
We explored how junk email is sent, including methods like email address harvesting, purchased or traded lists, botnets, phishing, email spoofing, and mass emailing software. Recognizing these methods helps us understand the strategies used by spammers and reinforces the need for robust preventive measures.
To protect ourselves from junk email, we discussed strategies such as using reliable email service providers, enabling spam filters, avoiding public sharing of email addresses, being selective with newsletter subscriptions, and using disposable email addresses. We also highlighted the significance of being cautious with links and attachments, not responding to or engaging with spam, and regularly updating devices and software for enhanced security.
We delved into avoiding junk email scams by being skeptical, verifying senders, paying attention to grammar and spelling, avoiding urgent requests, refraining from sharing personal information, verifying suspicious links, and educating ourselves about common scamming techniques.
We then explored best practices for dealing with junk email, including regularly checking and emptying the spam folder, using the block or unsubscribe option, reporting spam, creating custom filters, being cautious with forwarding, keeping email addresses private, using disposable email addresses, staying informed, and regularly reviewing and updating email settings.
By implementing these strategies and being proactive in our approach, we can effectively manage and reduce the impact of junk email, ensuring a clean, organized, and secure experience in our email communication and online interactions.
Stay informed, stay vigilant, and take actions to protect yourself from the deluge of junk email in an ever-evolving digital landscape. Together, we can minimize the disruption caused by spam and keep our inboxes focused on what truly matters.