Introduction
Cybersecurity has become an increasingly critical concern in our interconnected digital world. With the rapid advancement of technology, the threats and risks associated with cyber attacks have also multiplied. Organizations of all sizes and individuals alike are now vulnerable to a wide range of cybersecurity threats.
But what exactly is cybersecurity? In simple terms, it refers to the practice of protecting computer systems, networks, and data from unauthorized access, attack, or damage. It involves implementing various security measures to safeguard against threats such as theft, hacking, viruses, malware, and other malicious activities.
The importance of cybersecurity cannot be overstated. A single breach can have severe consequences, ranging from financial losses and reputation damage to legal and operational ramifications. Cybersecurity is not just a concern for businesses and organizations; it also affects individuals who use digital platforms for personal purposes.
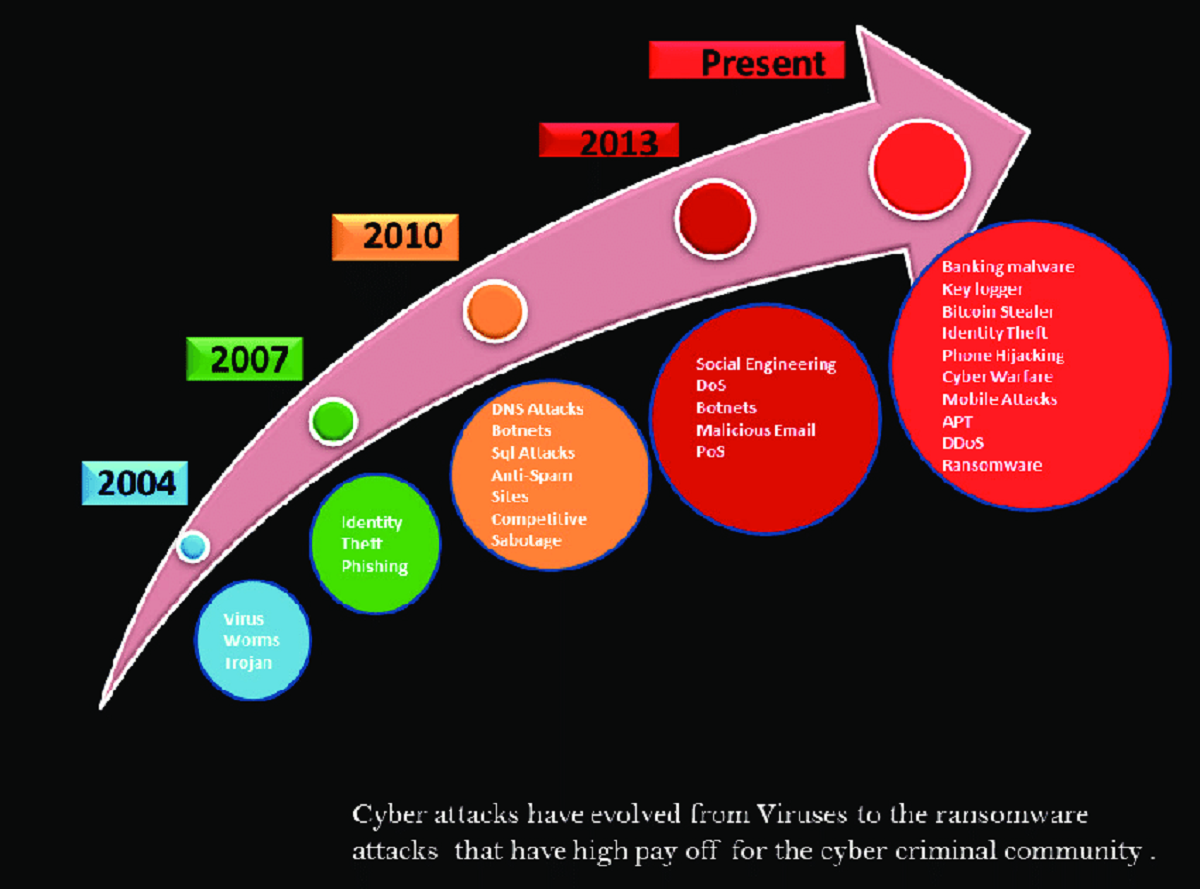
There are different types of cybersecurity threats that individuals and organizations need to be aware of. These include phishing attacks, ransomware, malware, Distributed Denial of Service (DDoS) attacks, and social engineering, among others. Each type of attack poses unique risks and requires specific security measures to mitigate them.
It is crucial to understand the common cybersecurity attacks that we may face. Phishing attacks, for example, involve tricking individuals into revealing sensitive information such as login credentials or credit card details through fraudulent emails or websites. Ransomware attacks encrypt valuable data and demand a ransom for its release. Malware is a broad term encompassing various types of malicious software designed to harm computers and networks. DDoS attacks overload a network or website with traffic, causing it to crash or become inaccessible. Social engineering involves manipulating individuals into divulging confidential information through psychological manipulation or deception.
To combat these and other cybersecurity threats, it is essential to develop effective cybersecurity strategies. This includes implementing security protocols and measures such as firewalls, encryption, multi-factor authentication, and regular software updates. An integral part of any cybersecurity strategy is conducting a risk assessment to identify vulnerabilities and prioritize security measures. This helps allocate resources and efforts where they are most needed.
A strong cybersecurity system consists of several key elements. These include a comprehensive security policy, employee awareness and training programs, proactive monitoring and detection systems, incident response plans, and regular security audits. By incorporating these elements into the cybersecurity framework, organizations and individuals can significantly reduce the likelihood and impact of cyber attacks.
What is Cybersecurity?
Cybersecurity, sometimes referred to as information security, is the practice of protecting computer systems, networks, and data from unauthorized access, use, disclosure, alteration, or destruction. With the increasing reliance on technology and the interconnectedness of digital ecosystems, cybersecurity has become a crucial aspect of our daily lives, both personally and professionally.
The primary objective of cybersecurity is to safeguard digital assets and prevent unauthorized individuals or entities from gaining access to sensitive information. This can be achieved through a combination of technologies, processes, and practices that are designed to detect, prevent, and mitigate potential cyber threats.
Cybersecurity encompasses multiple layers of defense, each working together to create a robust security posture. These layers include network security, application security, endpoint security, data security, cloud security, and user awareness and training. By implementing a multi-layered approach, organizations can minimize the likelihood of successful cyber attacks and protect their valuable assets.
The field of cybersecurity is constantly evolving, as new threats emerge and cyber attackers become more sophisticated in their methods. It encompasses various disciplines, including cryptography, network security, application security, behavioral analysis, incident response, and ethical hacking. Skilled professionals in these areas play a vital role in maintaining a secure digital environment.
Organizations that prioritize cybersecurity understand the potential consequences of a security breach. Not only can cyber attacks result in financial losses, but they can also lead to reputational damage, legal issues, and loss of customer trust. In today’s digital landscape, where data is often considered the most valuable asset, protecting it from unauthorized access has become a top priority.
Individuals also need to be mindful of their own cybersecurity. With the increasing use of online banking, social media, email, and other digital services, personal information can become vulnerable to theft or misuse. Implementing basic cybersecurity practices such as using strong, unique passwords, enabling two-factor authentication, and being cautious of suspicious emails or links can go a long way in safeguarding personal data.
Overall, cybersecurity is a critical component of our technological age. It is not just a responsibility of organizations and governments but also individuals. By understanding the principles of cybersecurity and implementing effective security measures, we can help create a safer and more secure digital environment for everyone.
Why is Cybersecurity important?
In today’s digital age, where technology is pervasive and interconnected, cybersecurity has become a critical factor for individuals, organizations, and nations. The importance of cybersecurity lies in its ability to protect valuable information, maintain trust, and mitigate potential risks. Here are some key reasons why cybersecurity is vital:
Protection of sensitive data: Cybersecurity measures are necessary to safeguard sensitive data from unauthorized access or exploitation. This includes personal information, financial records, intellectual property, trade secrets, and confidential business data. By implementing robust security measures, organizations can ensure the privacy and integrity of their data, preventing significant financial losses and reputational damage caused by data breaches.
Prevention of financial losses and disruption: Cyber attacks can result in significant financial losses for organizations. The costs associated with a security breach include remediation, regulatory penalties, legal fees, customer compensation, and potential loss of business. Furthermore, cyber attacks can disrupt critical services, leading to downtime and decreased productivity. Investing in cybersecurity helps minimize the risk of financial losses and ensures smooth business operations.
Preservation of reputation and customer trust: A cybersecurity breach can damage the reputation of an organization and erode customer trust. News of a data breach can spread quickly, resulting in negative publicity and a loss of confidence from customers, partners, and stakeholders. By prioritizing cybersecurity and protecting customer data, organizations can maintain their reputation and retain the trust of their clients.
Compliance with regulations: Many industries are subject to regulations and compliance requirements regarding data protection and cybersecurity. Non-compliance can lead to severe penalties and legal consequences. By implementing robust cybersecurity measures, organizations can ensure they meet regulatory standards and avoid legal complications.
Protection against cyber threats: The threat landscape is constantly evolving, with cyber attackers becoming more sophisticated in their methods. Cybersecurity helps defend against a wide range of threats, including phishing attacks, malware, ransomware, hacking attempts, and unauthorized access. By continually updating and improving security measures, organizations can stay ahead of potential threats and reduce their vulnerability to cyber attacks.
Protection of national security: Cybersecurity is not only important for individual organizations but also for national security. Governments and critical infrastructure systems, such as power grids, transportation networks, and communication systems, rely heavily on cybersecurity to protect against cyber warfare and state-sponsored attacks. Ensuring the security and resilience of these systems is crucial to maintaining the stability and safety of a nation.
Overall, cybersecurity is essential in today’s digital landscape. It is crucial for protecting sensitive data, preventing financial losses and disruption, preserving reputation and customer trust, complying with regulations, mitigating cyber threats, and safeguarding national security. By investing in cybersecurity measures and staying vigilant against evolving threats, we can create a safer and more secure digital world.
Different types of Cybersecurity threats
In the ever-evolving landscape of cybersecurity, understanding the different types of threats is crucial for implementing effective defense measures. Cybersecurity threats can manifest in various forms, each with its own characteristics and potential damages. Here are some common types of cybersecurity threats:
Phishing: Phishing attacks involve the use of fraudulent emails, messages, or websites to deceive individuals into providing sensitive information such as login credentials, credit card details, or personal data. Phishing attacks rely on social engineering techniques to manipulate victims into unknowingly revealing confidential information.
Ransomware: Ransomware is a type of malicious software that encrypts a victim’s data and demands a ransom to restore access. It often spreads through malicious email attachments, infected websites, or compromised software. Ransomware attacks can cripple businesses and individuals, resulting in significant financial losses and data breaches.
Malware: Malware is a generic term for any malicious software that is designed to disrupt, damage, or gain unauthorized access to a computer system. Common types of malware include viruses, worms, Trojans, spyware, and adware. Malware can be introduced through infected downloads, malicious websites, or exploit vulnerabilities in software.
Distributed Denial of Service (DDoS) attacks: DDoS attacks involve overwhelming a target system with a flood of traffic from multiple sources, causing it to become unavailable or crash. By exploiting network bandwidth or server resources, DDoS attacks disrupt services, resulting in potential financial losses for businesses and an inability to access websites or online services for individuals.
Social engineering: Social engineering attacks exploit human psychology to gain unauthorized access to information or systems. This can involve techniques such as impersonation, manipulation, or deception. Social engineering attacks are often used to trick individuals into revealing passwords, providing access to restricted areas, or easily bypassing security measures.
Advanced Persistent Threats (APTs): APTs are sophisticated and targeted cyber attacks that involve long-term presence and covert operations within a network. APTs are often conducted by skilled cyber attackers, and their main objective is to gain and maintain unauthorized access to sensitive information over an extended period of time.
Insider Threats: Insider threats occur when individuals within an organization, whether intentionally or unintentionally, pose a cybersecurity risk. This can include disgruntled employees, negligent individuals, or individuals who unknowingly fall victim to social engineering attacks. Insider threats can result in data breaches, intellectual property theft, or compromise of sensitive information.
It is essential to be aware of these various types of cybersecurity threats to better prepare and defend against them. By understanding the characteristics and techniques employed by cyber attackers, individuals and organizations can enhance their cybersecurity measures and mitigate potential risks.
Common Cybersecurity Attacks
In today’s interconnected digital landscape, cybersecurity attacks have become a prevalent threat to individuals, organizations, and governments. Understanding the common types of cybersecurity attacks is crucial for implementing effective defense strategies. Here are some of the most common cybersecurity attacks:
1. Phishing Attacks: Phishing attacks involve the use of fraudulent emails, messages, or websites that mimic legitimate entities, aiming to deceive individuals into revealing sensitive information or performing actions that benefit the attackers. These attacks often exploit social engineering techniques to trick victims into providing login credentials, personal information, or financial details.
2. Ransomware: Ransomware attacks occur when malicious software encrypts a victim’s data, rendering it inaccessible until a ransom is paid. This type of attack can cause significant disruptions to businesses and individuals alike, leading to financial losses and potential data breaches.
3. Malware Infections: Malware refers to any malicious software designed to gain unauthorized access, disrupt system operations, or compromise data integrity. Malware can take various forms, including viruses, worms, Trojans, and spyware. These infections often occur through infected downloads, compromised websites, or vulnerabilities in software.
4. Distributed Denial of Service (DDoS) Attacks: DDoS attacks aim to overwhelm a target system or network with a flood of traffic, leading to service disruptions or complete unavailability. Cyber attackers orchestrate DDoS attacks by using multiple compromised devices to flood the target with an overwhelming amount of data, causing system resources to be exhausted.
5. Social Engineering Attacks: Social engineering attacks exploit human psychology to manipulate individuals into revealing confidential information or performing actions that benefit the attackers. These attacks can involve impersonation, deceptive tactics, or psychological manipulation to trick victims into bypassing security measures or disclosing sensitive data.
6. Man-in-the-Middle (MitM) Attacks: In a MitM attack, cyber attackers intercept communication between two parties and eavesdrop or alter the information transmitted. This can be achieved by compromising routers, gaining access to a network, or exploiting vulnerabilities in communication protocols. By doing so, attackers can obtain sensitive information or manipulate data exchanges without the knowledge of the victims.
7. SQL Injection Attacks: SQL injection attacks target web applications that use databases to store or retrieve information. By exploiting vulnerabilities in the application’s input fields, attackers can insert malicious SQL code, allowing them to manipulate or extract sensitive data from the database.
8. Zero-Day Exploits: Zero-day exploits target vulnerabilities in software or hardware that are unknown to the vendor or developers. Cyber attackers discover these vulnerabilities and exploit them before a patch or fix is available, increasing the potential damage and impact of the attack.
9. Insider Threats: Insider threats occur when individuals within an organization, whether intentionally or unintentionally, misuse their access privileges. This can include employees leaking sensitive information, intentionally causing damage, or falling victim to external social engineering attacks.
By being aware of these common cybersecurity attacks, individuals and organizations can better prepare themselves to prevent, detect, and respond to such threats. Implementing security measures, maintaining up-to-date software, educating employees, and practicing good cybersecurity hygiene are essential in combating the ever-evolving landscape of cyber attacks.
Strategies for Effective Cybersecurity
Cybersecurity is an ongoing battle against constantly evolving cyber threats. To effectively protect against these threats, organizations and individuals must adopt proactive strategies and best practices. Here are some key strategies for effective cybersecurity:
1. Implement a Layered Defense: Relying on a single security measure is not enough to defend against sophisticated cyber attacks. Implementing a multi-layered defense approach involves using a combination of technologies, processes, and practices that work together to provide comprehensive protection. This may include firewalls, intrusion detection systems, antivirus software, encryption, and access controls.
2. Stay Updated with Patches and Security Updates: Regularly applying patches and security updates is crucial to address vulnerabilities in software or hardware. Hackers often exploit known vulnerabilities, so keeping systems up-to-date with the latest patches can mitigate the risk of exploitation.
3. Practice Strong Password Management: Weak passwords are a common vulnerability that can lead to unauthorized access. Implementing strong password policies, such as using complex passwords and requiring regular password changes, can significantly enhance security. Additionally, employing multi-factor authentication adds an extra layer of protection.
4. Educate and Train Employees: Human error is a significant factor in many cybersecurity breaches. Regularly educate and train employees on cybersecurity best practices, such as identifying phishing emails, avoiding suspicious websites, and recognizing social engineering techniques. Creating a security-aware culture within an organization can help prevent many cyber attacks.
5. Conduct Regular Security Assessments and Audits: A thorough security assessment can identify vulnerabilities and potential weaknesses in systems and networks. Regular audits and penetration testing can help identify and address security gaps before they are exploited by cyber attackers, ensuring a proactive defense posture.
6. Develop an Incident Response Plan: Having a well-defined incident response plan is essential to minimize the impact of a cybersecurity incident. This plan should outline the steps to be taken in the event of a security breach, including communication protocols, forensic analysis, system recovery procedures, and legal obligations.
7. Backup and Recovery: Regularly backing up critical data is crucial in case of a ransomware attack or data loss. The backups should be stored securely and tested periodically to ensure their integrity and availability for recovery purposes.
8. Stay Informed about Emerging Threats: Cybersecurity threats are constantly evolving. Staying informed about the latest cyber attack trends and emerging threats allows organizations and individuals to adapt their defenses accordingly. Subscribing to security newsletters, attending webinars, and participating in industry forums are effective ways to stay up-to-date.
9. Enforce Strong User Access Controls: Limiting user access privileges to only what is necessary helps minimize the potential attack surface. Implementing role-based access controls, least privilege principles, and regularly reviewing user permissions can significantly reduce the risk of unauthorized access.
By implementing these strategies and best practices, organizations and individuals can establish a strong defense against cyber threats. However, it is important to note that cybersecurity is an ongoing endeavor that requires continuous monitoring, adaptation, and improvement to stay ahead of cyber threats.
Importance of Risk Assessment in Cybersecurity
Risk assessment is a fundamental component of effective cybersecurity practices. It involves identifying, evaluating, and prioritizing potential risks to information systems, networks, and data. Conducting risk assessments is crucial for organizations to understand their vulnerabilities, allocate resources effectively, and implement appropriate security measures. Here are some key reasons why risk assessment is important in cybersecurity:
1. Identify Vulnerabilities: Risk assessments help identify potential vulnerabilities and weaknesses within an organization’s cybersecurity infrastructure. By conducting a thorough assessment, organizations can pinpoint areas of weakness and address them promptly before they can be exploited by malicious actors.
2. Prioritize Security Measures: Not all risks have the same level of impact or likelihood. Risk assessments help organizations understand the potential consequences of specific threats and prioritize security measures accordingly. This ensures that resources are allocated effectively to address the most critical risks.
3. Understand Potential Impact: Risk assessments provide insight into the potential impact of cybersecurity threats. By assessing the likelihood and impact of each risk, organizations can gauge the potential financial, operational, and reputational consequences of a security breach. This information is crucial for informed decision-making and resource allocation.
4. Compliance with Regulations: Many industries are subject to regulatory requirements regarding data protection and cybersecurity. Risk assessments help assess an organization’s compliance with these regulations. By identifying gaps and vulnerabilities, organizations can take appropriate measures to meet compliance standards and avoid potential penalties or legal consequences.
5. Measure Effectiveness of Controls: Risk assessments evaluate the effectiveness of existing security controls and measures in place. By identifying gaps or weaknesses in the current security posture, organizations can make informed decisions about implementing additional controls or improving existing ones to enhance security and reduce risk.
6. Provide Basis for Decision-Making: Risk assessments provide organizations with the necessary information to make informed decisions regarding cybersecurity investments, resource allocation, and risk mitigation strategies. By understanding the potential risks and their consequences, organizations can minimize the element of uncertainty in decision-making.
7. Support Incident Response Planning: Risk assessments inform the development of effective incident response plans. By understanding potential risks, organizations can develop predefined incident response procedures, enabling quick and efficient responses to security incidents. This minimizes the impact and potential damages caused by a cyber attack.
8. Continuous Improvement: Risk assessments are not a one-time activity. They should be conducted on an ongoing basis to keep up with the evolving threat landscape. Regular risk assessments help organizations stay vigilant and adapt their security measures to address emerging threats and new vulnerabilities.
Overall, risk assessment is a vital process in cybersecurity. It helps organizations identify vulnerabilities, prioritize security efforts, understand potential consequences, ensure compliance, measure control effectiveness, support decision-making, plan for incident response, and drive continuous improvement. By incorporating risk assessments into their cybersecurity practices, organizations can effectively manage and mitigate risks, enhancing their overall security posture.
Elements of a Strong Cybersecurity System
A strong cybersecurity system is crucial for protecting sensitive information and mitigating the risks posed by cyber threats. It involves implementing a combination of technical controls, processes, and practices to ensure the confidentiality, integrity, and availability of data. Here are some key elements of a strong cybersecurity system:
1. Robust Network Security: Protecting the network infrastructure is essential. This includes deploying firewalls, intrusion detection and prevention systems (IDS/IPS), secure routers, and secure Wi-Fi networks. Network segmentation is also crucial to prevent unauthorized access and limit the impact of potential breaches.
2. Secure Endpoint Devices: Securing endpoint devices, such as laptops, desktops, mobile devices, and servers, is critical. This involves implementing antivirus and antimalware software, enforcing strong passwords and multi-factor authentication, regularly updating operating systems and applications, and enabling remote device management and tracking.
3. Data Encryption: Encrypting sensitive data is an important safeguard against unauthorized access. Implementing strong encryption methods, both in transit and at rest, protects information from being accessed or intercepted by unauthorized individuals.
4. Regular Security Updates: Keeping software, firmware, and hardware up to date with the latest security patches is crucial for addressing known vulnerabilities. Regularly applying security updates minimizes the risk of exploitation by cyber attackers attempting to exploit outdated software.
5. Access Controls: Implementing granular access controls ensures that only authorized individuals have access to sensitive data and critical systems. This includes role-based access control (RBAC), least privilege principle, and strong authentication mechanisms, such as biometrics or two-factor authentication.
6. Employee Education and Awareness: Educating and training employees on cybersecurity best practices is essential. Regular awareness programs help employees recognize and respond to potential threats such as phishing emails, social engineering attacks, or the use of weak passwords. Encouraging a security-conscious culture among employees is a key defense against breaches caused by human error or negligence.
7. Incident Detection and Response: Implementing robust incident detection and response mechanisms helps to identify and respond to security incidents promptly. This includes deploying intrusion detection and prevention systems (IDPS), Security Information and Event Management (SIEM) systems, and establishing clear incident response plans with defined roles and responsibilities.
8. Regular Backups and Disaster Recovery: Performing regular backups of critical data and implementing reliable disaster recovery plans minimizes the impact of potential data loss or damage caused by cyber incidents. Regularly testing backup restoration procedures ensures that data can be restored effectively.
9. Continuous Monitoring: Implementing continuous monitoring systems allows for proactive threat detection and response. This involves using tools and technologies to monitor network traffic, system logs, and user activities, identifying anomalies and potential breaches in real-time.
10. Compliance with Security Standards: Adhering to relevant cybersecurity frameworks and standards, such as the ISO 27001 or NIST Cybersecurity Framework, ensures that an organization complies with industry best practices and regulatory requirements. Compliance contributes to a strong cybersecurity posture and helps build trust with customers and business partners.
A combination of these elements allows organizations to establish a strong cybersecurity system that can effectively protect against cyber threats, minimize vulnerabilities, detect and respond to incidents promptly, and ensure the integrity and confidentiality of critical data and systems.
Top Cybersecurity Tools and Technologies
In the field of cybersecurity, tools and technologies play a crucial role in detecting, preventing, and mitigating cyber threats. The rapid advancement of technology has resulted in the development of various innovative solutions. Here are some top cybersecurity tools and technologies widely used in the industry:
1. Firewall: Firewalls are essential security appliances that monitor and control incoming and outgoing network traffic based on predefined security rules. They act as a barrier between an internal network and external networks, ensuring that only authorized traffic is allowed in and out.
2. Intrusion Detection and Prevention Systems (IDPS): IDPS tools monitor network traffic for suspicious activities and attempt to identify and prevent intrusions. They detect various types of attacks, such as malware or unauthorized access attempts, and can automatically block or alert security personnel for further investigation and response.
3. Security Information and Event Management (SIEM): SIEM tools collect and analyze security event data from various sources, including logs from network devices, servers, applications, and security systems. They provide real-time visibility into potential security incidents, helping security teams detect, investigate, and respond to threats effectively.
4. Antivirus and Antimalware Software: Antivirus and antimalware software are crucial tools for protecting endpoints from malicious software. They identify and remove viruses, worms, Trojans, and other malware that could compromise the security of systems and data.
5. Vulnerability Scanners: Vulnerability scanners are automated tools that assess systems, networks, and applications for potential security vulnerabilities. They scan for known security weaknesses, misconfigurations, and outdated software versions, allowing organizations to prioritize remediation efforts to mitigate potential risks.
6. Encryption Tools: Encryption tools help protect sensitive data by converting it into a coded format that can only be deciphered using a decryption key. Encryption ensures that even if attackers gain unauthorized access to data, it remains unreadable and useless without the decryption key.
7. Multi-Factor Authentication (MFA): MFA adds an extra layer of security by requiring multiple forms of identification to access systems or accounts. This commonly includes a combination of passwords, biometrics, smart cards, or tokens. MFA helps prevent unauthorized access in case of a compromised password or stolen credentials.
8. Web Application Firewalls (WAF): WAFs protect web applications by filtering and monitoring HTTP traffic between users and web applications. They can prevent attacks such as SQL injections, cross-site scripting (XSS), and other common web vulnerabilities.
9. Security Orchestration, Automation, and Response (SOAR): SOAR platforms provide automation and orchestration capabilities to improve incident response processes. They help streamline and automate repetitive tasks, enabling faster detection, response, and resolution of security incidents.
10. Data Loss Prevention (DLP) Tools: DLP tools monitor and control the movement of sensitive data within an organization. They can prevent unauthorized data transfers, enforce data classification, and detect and block potential data leakage through various channels, such as email or USB devices.
These are just a few examples of the top cybersecurity tools and technologies available today. Each organization’s cybersecurity needs may vary, and it is important to select the appropriate tools that align with specific requirements and risk management strategies.
Best Practices for Personal Cybersecurity
In an increasingly digital world, practicing proper cybersecurity measures is crucial to protect personal information and maintain online safety. Here are some best practices for personal cybersecurity:
1. Use Strong and Unique Passwords: Create complex passwords that are difficult to guess and use a unique password for each online account. Consider using a password manager to securely store and manage your passwords.
2. Enable Two-Factor Authentication (2FA): Enable 2FA whenever possible for an extra layer of security. This typically involves providing a second form of verification, such as a verification code sent to your mobile device, in addition to your password.
3. Keep Software Up to Date: Regularly update your operating system, web browsers, antivirus software, and other applications. These updates often include important security patches that help protect against known vulnerabilities.
4. Be Cautious of Suspicious Emails and Links: Exercise caution when receiving emails from unknown senders and avoid clicking on suspicious links or downloading attachments from untrusted sources. These could be phishing attempts or contain malware.
5. Use Secure Wi-Fi Networks: Avoid connecting to public Wi-Fi networks that may be insecure and potentially expose your personal data. Use password-protected and encrypted Wi-Fi networks or consider using a virtual private network (VPN) for added security.
6. Regularly Back Up Your Data: Back up your important files and data regularly to an external hard drive or cloud storage. In the event of data loss from cyber attacks or hardware failures, having backups ensures that you can recover your essential files.
7. Be Mindful of Social Media Privacy Settings: Review and adjust your privacy settings on social media platforms to control what information is visible to the public and limit access to your personal data. Avoid sharing sensitive information publicly.
8. Be Wary of Social Engineering Tactics: Be cautious of unsolicited phone calls, text messages, or emails that request personal information or financial details. Legitimate organizations will not ask for sensitive information through these methods.
9. Use Antivirus and Antimalware Software: Install reputable antivirus and antimalware software on your devices. Keep the software up to date and regularly scan for any potential threats or malware.
10. Educate Yourself on Current Cybersecurity Trends: Stay informed about the latest cybersecurity threats and scams. Be aware of common attack techniques, such as phishing or ransomware, to recognize and avoid potential risks.
Personal cybersecurity is essential for protecting your identity, financial information, and personal data. By following these best practices, you can significantly reduce the risk of falling victim to cyberattacks and maintain a safer online presence.
Conclusion
Cybersecurity is of utmost importance in our digital age, where technology permeates every aspect of our lives. Understanding the various threats and implementing effective measures is vital for individuals and organizations to protect sensitive information, maintain trust, and mitigate potential risks.
Throughout this article, we have explored the definition of cybersecurity and its significance in safeguarding computer systems, networks, and data from unauthorized access and malicious activities. We have discussed the different types of cybersecurity threats, including phishing, ransomware, malware, DDoS attacks, and social engineering.
Strategies for effective cybersecurity were highlighted, emphasizing the importance of implementing a layered defense, staying updated with security patches, practicing strong password management, and conducting regular security assessments. We also discussed the importance of risk assessment in identifying vulnerabilities and prioritizing security efforts, along with the elements of a strong cybersecurity system.
Additionally, we explored the top cybersecurity tools and technologies that organizations can utilize to enhance their defense capabilities. These tools include firewalls, intrusion detection systems, encryption software, and security information and event management systems, among others.
On a personal level, implementing best practices for personal cybersecurity, such as using strong and unique passwords, enabling two-factor authentication, being cautious of suspicious emails and links, and regularly backing up data, is crucial for individuals to protect their personal information and maintain online safety.
In conclusion, cybersecurity is an ongoing effort that requires constant vigilance, adaptability, and continuous improvement. By staying informed about emerging threats, adopting robust security measures, and fostering a culture of cybersecurity awareness, we can create a safer and more secure digital environment for all.