Introduction
Welcome to the world of cybersecurity, where protecting sensitive information and digital assets is paramount. In this digital age, where cyber threats are constantly evolving, it has become crucial for individuals and organizations to safeguard their data against potential attacks.
Cybersecurity refers to the practice of protecting computers, servers, mobile devices, electronic systems, and networks from unauthorized access, data breaches, and malicious activities. It involves implementing various measures and protocols to ensure the confidentiality, integrity, and availability of information.
As the number and complexity of cyber threats continue to increase, the need for a structured approach to cybersecurity has become evident. This is where cybersecurity frameworks come into play. A cybersecurity framework is a set of guidelines, best practices, and standards that organizations can adopt to establish, implement, and manage their cybersecurity programs effectively.
Cybersecurity frameworks provide a structured approach to assessing a company’s current security posture, identifying vulnerabilities, and implementing appropriate controls to mitigate risks. They help organizations define security objectives, establish policies and procedures, allocate resources effectively, and measure their progress in securing their systems and data.
Implementing a cybersecurity framework is not just beneficial for large corporations or government agencies; businesses of all sizes can benefit from adopting such a framework. Small and medium-sized enterprises are often targeted by cybercriminals due to their perception of being more vulnerable, making it crucial for them to have robust cybersecurity measures in place.
In this technology-driven era, where cyber threats can arise from various sources and can cause significant financial and reputational damage, having a comprehensive cybersecurity framework is no longer a luxury but a necessity. By proactively implementing cybersecurity frameworks, organizations can stay one step ahead of cybercriminals and ensure the safety and confidentiality of their critical data and systems.
What is cybersecurity?
Cybersecurity is a term that encompasses a range of practices and measures aimed at protecting computers, networks, and digital systems from unauthorized access, data breaches, and malicious activities. It involves safeguarding information and technology assets from cyber threats such as hacking, malware, phishing, and other cyber-attacks.
In today’s interconnected world, where businesses rely heavily on technology and store vast amounts of sensitive data, cybersecurity has become a critical concern. Cybercriminals are constantly finding new and sophisticated ways to exploit vulnerabilities and infiltrate systems, making it essential for organizations and individuals to be proactive in their efforts to protect their digital assets.
Effective cybersecurity involves multiple layers of defense. It includes implementing security controls such as firewalls, antivirus software, and encryption, as well as establishing robust policies and procedures to manage and mitigate risks. It also includes training employees to be aware of potential threats and to follow best practices when it comes to data security.
One key aspect of cybersecurity is the concept of confidentiality, ensuring that sensitive information remains private and only accessible to authorized individuals. This is achieved through strong access controls, encryption techniques, and secure data storage.
Another aspect is integrity, which means ensuring the accuracy and reliability of data. Cybersecurity measures are put in place to detect and prevent unauthorized modifications or tampering of data, ensuring that the information remains intact and trustworthy.
Availability is another crucial element of cybersecurity, ensuring that systems and data are accessible to authorized users when needed. Security measures such as backups, redundancy, and disaster recovery plans are implemented to minimize downtime and ensure continuous availability of services.
Overall, cybersecurity is a dynamic field that requires constant vigilance and adaptability. As technology evolves, so do the threats and vulnerabilities. Staying up to date with emerging threats and implementing robust cybersecurity measures is essential for individuals and organizations to protect themselves against cyber-attacks and ensure the confidentiality, integrity, and availability of their valuable digital assets.
The Importance of Cybersecurity Frameworks
In today’s digital landscape, where cyber threats are becoming increasingly sophisticated and prevalent, the importance of cybersecurity frameworks cannot be overstated. Cybersecurity frameworks provide organizations with a structured and systematic approach to managing and mitigating cyber risks, ensuring the confidentiality, integrity, and availability of their data and systems.
First and foremost, cybersecurity frameworks help organizations establish a strong security foundation. They provide guidelines and best practices for identifying and assessing potential vulnerabilities, implementing appropriate controls, and monitoring and managing risks. By adhering to a cybersecurity framework, organizations can systematically identify and address security gaps, reducing the risk of data breaches and cyber-attacks.
Cybersecurity frameworks also help organizations comply with legal and regulatory requirements. Many industries have specific cybersecurity standards and regulations that organizations must adhere to. The frameworks provide a roadmap for meeting these requirements and ensure that organizations stay in compliance, avoiding potential legal and financial repercussions.
An additional benefit of cybersecurity frameworks is that they assist organizations in demonstrating their commitment to security to clients, partners, and stakeholders. Implementing a recognized framework demonstrates that organizations are actively working to protect sensitive data and are taking cybersecurity seriously. This can enhance their reputation, build trust, and potentially open doors to new business opportunities.
Cybersecurity frameworks also aid in resource allocation and management. By following a framework, organizations can prioritize their resources effectively, focusing on areas of critical importance and addressing vulnerabilities that pose the greatest risk. This helps organizations optimize their cybersecurity investments, ensuring that resources are allocated to the areas that need them most.
Furthermore, cybersecurity frameworks promote consistency and standardization. They provide a common language and a set of well-defined practices that enable organizations to communicate and collaborate effectively with industry peers, regulatory bodies, and other stakeholders. This promotes information sharing and cooperation, facilitating the collective effort to combat cyber threats.
Lastly, cybersecurity frameworks support continuous improvement. They provide a framework for organizations to assess their current security posture, identify areas for improvement, and establish a roadmap for ongoing enhancements. By embracing a framework, organizations can continually evaluate and enhance their cybersecurity capabilities, staying ahead of emerging threats and evolving cyber risks.
In summary, cybersecurity frameworks play a vital role in helping organizations establish and maintain effective cybersecurity practices. They provide a structured approach to managing cyber risks, ensuring compliance with regulations, enhancing reputation, optimizing resource allocation, promoting consistency, and fostering continuous improvement. By implementing a recognized framework, organizations can better protect themselves and their digital assets in an increasingly complex and dangerous cyber landscape.
What is a Cybersecurity Framework?
A cybersecurity framework is a set of guidelines, best practices, and standards that organizations can adopt to establish, implement, and manage their cybersecurity programs effectively. It serves as a blueprint for organizations to develop a comprehensive and robust approach to cybersecurity, tailored to their specific needs and industry requirements.
A cybersecurity framework provides a structured and systematic approach to addressing security risks and safeguarding critical information and assets. It outlines the necessary policies, procedures, and controls that organizations should implement to protect against potential cyber threats.
At its core, a cybersecurity framework helps organizations identify vulnerabilities, assess risks, and implement appropriate security controls. It provides a framework for understanding the organization’s current security posture, defining desired security outcomes, and establishing a roadmap for achieving those outcomes.
These frameworks are typically developed by industry organizations, government agencies, or international standards bodies. They draw from industry best practices and lessons learned from real-world cybersecurity incidents to provide organizations with proven approaches to managing cyber risks.
Moreover, cybersecurity frameworks help organizations align their security practices with universally accepted standards and regulations. They often incorporate industry-specific requirements to provide a tailored approach to cybersecurity for different sectors, such as healthcare, finance, or government.
Cybersecurity frameworks generally cover a wide range of areas, including risk management, incident response, access controls, employee training, network security, data protection, and vendor management. They provide guidance on implementing technical controls, establishing governance structures, and developing policies and procedures to ensure a holistic and robust cybersecurity program.
Some cybersecurity frameworks are generic and can be applied to any organization, while others are industry-specific and address sector-specific risks and regulatory requirements. Organizations can choose the framework that best aligns with their needs and customize it to suit their unique circumstances.
It is important to note that a cybersecurity framework is not a one-size-fits-all solution. Organizations must assess their specific requirements, risk appetite, and resources to determine which framework is most suitable. They may also need to comply with multiple frameworks or standards, depending on their industry and geographical location.
In summary, a cybersecurity framework provides organizations with a structured approach to managing their cybersecurity risks and protecting their information and assets. It offers a set of guidelines, best practices, and standards that organizations can adopt and tailor to their specific needs. By implementing a cybersecurity framework, organizations can establish a comprehensive and robust cybersecurity program that aligns with industry standards, regulatory requirements, and best practices.
Benefits of Using a Cybersecurity Framework
The use of a cybersecurity framework can provide numerous benefits for organizations seeking to protect their digital assets and mitigate cyber risks. Let’s explore some of the key advantages:
- Structure and Guidance: One of the primary benefits of using a cybersecurity framework is that it provides organizations with a structured approach to cybersecurity. It offers a clear roadmap and guidance on implementing security measures, identifying vulnerabilities, and managing risks.
- Compliance and Regulation: Many cybersecurity frameworks align with industry standards and regulatory requirements. By adopting a recognized framework, organizations can demonstrate compliance with relevant laws and regulations, reducing the risk of legal consequences and fines.
- Risk Management: Cybersecurity frameworks emphasize risk management practices. They enable organizations to identify and assess potential risks, prioritize mitigation efforts, and allocate resources effectively. This proactive approach helps organizations mitigate vulnerabilities and minimize the impact of potential cyber incidents.
- Consistency and Standardization: Implementing a cybersecurity framework promotes consistency and standardization in security practices. It establishes a common language and set of guidelines that facilitate communication and collaboration among different teams, departments, and external entities.
- Efficiency and Cost-Effectiveness: A cybersecurity framework helps organizations optimize their security investments. By following a structured approach, organizations can focus their resources on areas of highest risk, ensuring that cybersecurity efforts are targeted and cost-effective.
- Enhanced Reputation: Implementing a cybersecurity framework demonstrates to clients, customers, and other stakeholders that an organization takes cybersecurity seriously. This commitment to protecting sensitive information and ensuring data privacy can enhance the organization’s reputation and build trust among stakeholders.
- Continuous Improvement: Cybersecurity frameworks emphasize the importance of ongoing assessment and improvement. By regularly reviewing and updating security measures, organizations can adapt to evolving threats and stay ahead of cyber risks. This continuous improvement mindset ensures that security practices remain effective and up to date.
It is important to note that while cybersecurity frameworks provide valuable guidance, they are not a one-size-fits-all solution. Organizations should assess their unique requirements, industry regulations, and risk profiles to select and adapt the most suitable framework. Customizing the framework to align with the organization’s specific needs and circumstances will maximize its benefits and ensure a tailored approach to cybersecurity.
In summary, using a cybersecurity framework offers organizations a structured and strategic approach to cybersecurity. It helps organizations manage risks, comply with regulations, optimize resources, enhance reputation, promote consistency, and drive continuous improvement in their security practices.
Types of Cybersecurity Frameworks
Cybersecurity frameworks can be categorized into different types based on their scope, applicability, and the organizations they target. Let’s explore some of the common types of cybersecurity frameworks:
- General Frameworks: These frameworks provide a broad set of guidelines and best practices that can be applied to any organization, regardless of industry or size. Examples of general frameworks include the National Institute of Standards and Technology (NIST) Cybersecurity Framework and the ISO/IEC 27001 standard.
- Industry-Specific Frameworks: These frameworks are tailored to specific industries and address the unique risks and regulatory requirements within those sectors. Examples of industry-specific frameworks include the Payment Card Industry Data Security Standard (PCI DSS) for the payment card industry and the Health Insurance Portability and Accountability Act (HIPAA) Security Rule for the healthcare industry.
- Government-Driven Frameworks: These frameworks are developed and promoted by government agencies to enhance cybersecurity practices and resilience. Examples include the Cybersecurity Capability Maturity Model (C2M2) developed by the U.S. Department of Energy and the UK Government Security Policy Framework.
- International Standards: These frameworks are developed by international standards bodies and are widely recognized and accepted globally. The International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC) have established several cybersecurity standards, such as ISO/IEC 27001, which provides a comprehensive framework for information security management systems.
- Open-Source Frameworks: Open-source cybersecurity frameworks are publicly available and can be customized and modified to suit the specific needs of an organization. Examples include Open Web Application Security Project (OWASP), which provides guidelines for web application security, and Security Content Automation Protocol (SCAP), which offers a standardized approach to automating vulnerability management.
- Consolidated Frameworks: These frameworks consolidate multiple standards and guidelines into a single reference framework, simplifying the adoption and implementation process. One such example is the Control Objectives for Information and Related Technologies (COBIT), which integrates various frameworks and provides a comprehensive approach to IT governance, risk management, and compliance.
It’s important for organizations to select a cybersecurity framework that aligns with their industry requirements, regulatory obligations, and risk appetite. The chosen framework should be adaptable and flexible enough to accommodate the organization’s unique circumstances and specific security needs.
Furthermore, organizations may choose to combine multiple frameworks to address different aspects of cybersecurity comprehensively. It’s not uncommon for organizations to adopt multiple frameworks to meet industry-specific requirements while also adhering to broader general frameworks.
In summary, the types of cybersecurity frameworks vary in scope and applicability. General frameworks provide broad guidance, while industry-specific frameworks address the unique risks of specific sectors. Government-driven frameworks and international standards offer a global approach, while open-source and consolidated frameworks provide customizable options. Careful consideration should be given to selecting the right cybersecurity framework(s) that best align with an organization’s needs, industry requirements, and risk profile.
Common Cybersecurity Frameworks
There are several well-known cybersecurity frameworks that organizations can adopt to enhance their cybersecurity practices. These frameworks provide guidance and best practices for managing cyber risks and protecting sensitive information. Here are some of the common cybersecurity frameworks:
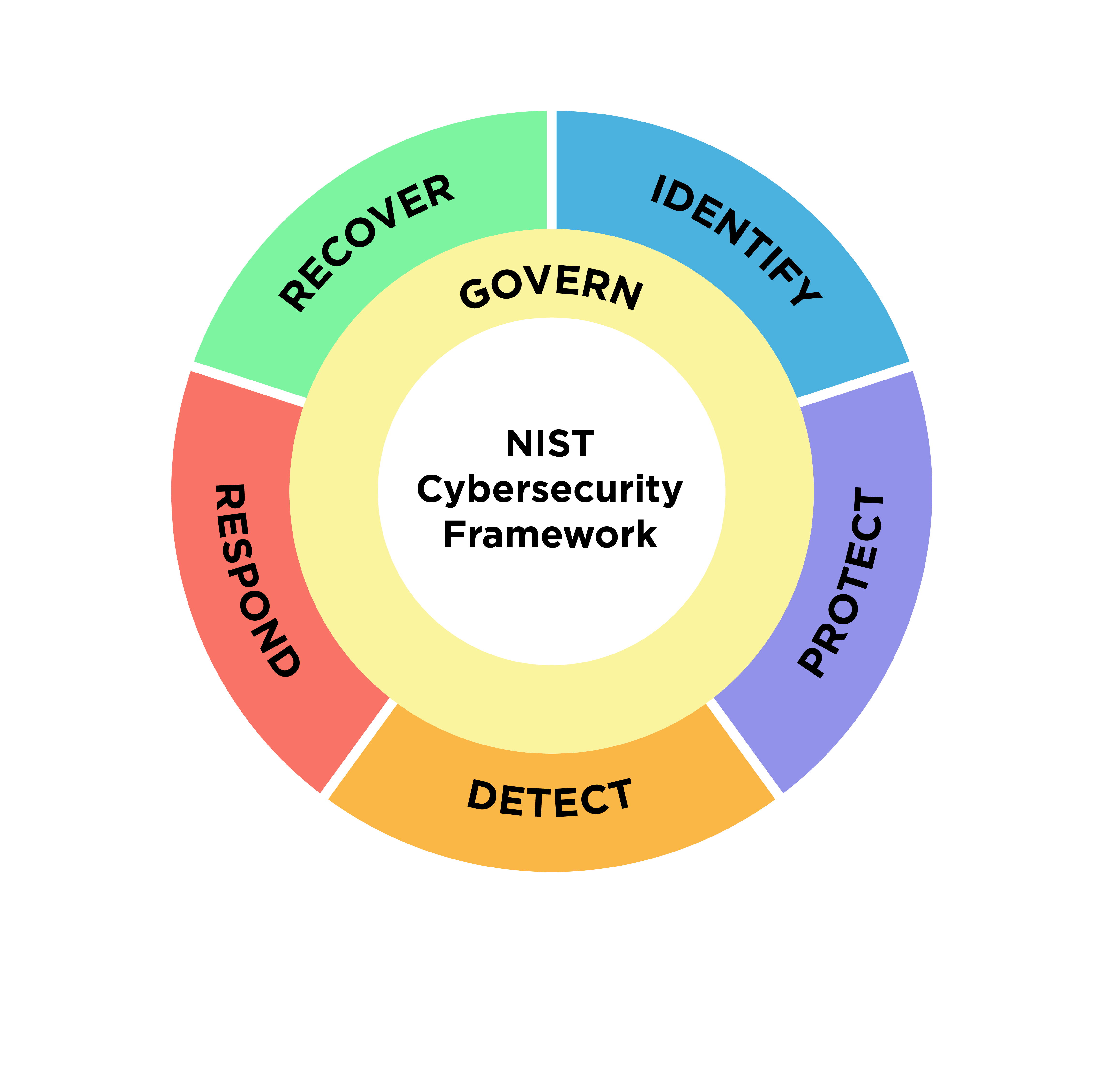
- NIST Cybersecurity Framework (CSF): Developed by the National Institute of Standards and Technology (NIST), the NIST CSF is widely recognized and widely adopted. It offers a risk-focused framework that helps organizations assess their current cybersecurity posture, identify and prioritize vulnerabilities, and establish a tailored cybersecurity program.
- ISO/IEC 27001: This international standard outlines the requirements for establishing, implementing, maintaining, and continuously improving an information security management system (ISMS). It provides a comprehensive framework for managing information security risks within organizations and is applicable to all types of industries and sectors.
- Payment Card Industry Data Security Standard (PCI DSS): Developed by major payment card brands, the PCI DSS is a set of security standards for organizations that handle cardholder data. It provides guidelines for ensuring the secure processing, storage, and transmission of payment card information to prevent fraud and data breaches.
- Health Insurance Portability and Accountability Act (HIPAA) Security Rule: The HIPAA Security Rule outlines the security requirements that covered entities and business associates in the healthcare industry must follow to protect electronic protected health information (ePHI). It focuses on safeguarding patient data and ensuring the privacy and confidentiality of personal health information.
- CIS Controls: The CIS (Center for Internet Security) Controls are a set of prioritized actions that organizations can take to enhance their cybersecurity posture. These controls offer a practical and actionable framework for organizations regardless of industry, helping them manage risks, implement security measures, and protect critical assets.
- COBIT (Control Objectives for Information and Related Technologies): COBIT is a framework that provides best practices for the governance and management of enterprise information and technology. It focuses on aligning IT with business objectives, managing risks, and ensuring the effective use of technology resources to achieve organizational goals.
These cybersecurity frameworks serve as valuable resources for organizations looking to establish a strong cybersecurity foundation. It’s worth noting that these frameworks can be complementary, and organizations can combine aspects of multiple frameworks to address their specific needs and compliance requirements.
When selecting a cybersecurity framework, organizations should consider their industry requirements, regulatory obligations, risk appetite, and available resources. It’s important to evaluate the suitability and feasibility of each framework and customize it to align with the organization’s unique circumstances.
In summary, the adoption of common cybersecurity frameworks such as the NIST CSF, ISO/IEC 27001, PCI DSS, HIPAA Security Rule, CIS Controls, and COBIT can help organizations strengthen their cybersecurity practices and protect their sensitive information. These frameworks provide valuable guidance and best practices for managing cyber risks, ensuring compliance, and enhancing overall security posture.
How to Choose the Right Cybersecurity Framework for Your Organization
Choosing the right cybersecurity framework for your organization is a crucial decision that requires careful consideration. Here are some key factors to take into account when selecting a cybersecurity framework:
- Evaluate Industry Requirements: Determine if your industry has specific cybersecurity regulations or frameworks that you must adhere to. Consider frameworks such as PCI DSS for the payment card industry or HIPAA Security Rule for the healthcare sector. Understanding industry-specific requirements will help narrow down your options.
- Assess Organizational Needs: Evaluate your organization’s unique requirements, risk profile, and cybersecurity objectives. Consider factors such as the sensitivity and volume of the data you handle, your network infrastructure, and your current security capabilities. This assessment will help you identify the specific areas of focus that your chosen framework should address.
- Consider Regulatory Compliance: Determine if your organization is subject to any specific regulations or regional data protection laws. Ensure that the cybersecurity framework you choose aligns with the regulatory requirements you must meet. This will help ensure compliance and avoid potential legal and financial consequences.
- Understand Framework Scope and Applicability: Assess the scope and applicability of each cybersecurity framework. Consider the size and complexity of your organization and whether the framework provides guidance relevant to your specific environment. Determine if the framework is scalable and adaptable to suit your future needs and growth.
- Evaluate Resource Availability: Consider the resources, expertise, and budget available within your organization for implementing the cybersecurity framework. Some frameworks may require a higher level of investment in terms of time, personnel, and financial resources. Ensure that you have the necessary resources to effectively adopt and maintain the framework.
- Engage Stakeholders: Involve key stakeholders within your organization in the decision-making process. This may include IT personnel, security teams, senior management, and legal or compliance professionals. Their input and perspectives will help ensure that the chosen framework aligns with the organization’s goals and requirements.
- Assess Framework Maturity and Industry Acceptance: Consider the maturity and acceptance of the framework within the cybersecurity community. Assess its reputation, adoption rate, and whether it is backed by reputable organizations or government bodies. Frameworks with wider industry acceptance may offer more robust and proven practices.
- Seek Expert Advice: If you are unsure about which cybersecurity framework to choose, consider seeking guidance from cybersecurity consultants, industry associations, or reputable cybersecurity professionals. They can provide insights and recommendations based on their expertise and experience.
Ultimately, selecting the right cybersecurity framework involves finding a balance between compliance requirements, industry standards, organizational needs, and available resources. It’s essential to choose a framework that aligns with your organization’s goals, helps mitigate risks, and enhances your overall cybersecurity posture.
Remember that cybersecurity frameworks are not static; they should be continuously reviewed and updated to address emerging threats and changing technology landscapes. Regularly reassess your cybersecurity framework to ensure it remains relevant and effective in protecting your organization against evolving cyber risks.
In summary, when choosing a cybersecurity framework, consider industry requirements, assess organizational needs, evaluate regulatory compliance, understand framework scope and applicability, evaluate available resources, engage stakeholders, assess maturity and industry acceptance, and seek expert advice. By conducting a thorough evaluation and selecting the right framework, you can establish a strong cybersecurity foundation for your organization.
Implementing a Cybersecurity Framework
Implementing a cybersecurity framework is a comprehensive and ongoing process that requires planning, coordination, and active engagement from across the organization. Here are some key steps to consider when implementing a cybersecurity framework:
- Gather Stakeholder Buy-In: Gain support and buy-in from key stakeholders within the organization, including senior management, IT personnel, and relevant departments. Ensure that all stakeholders understand the importance of cybersecurity and the benefits of adopting a framework.
- Conduct a Baseline Assessment: Assess the organization’s current cybersecurity posture using the framework’s guidelines or assessment tools. Identify existing strengths and weaknesses, and document areas for improvement. This assessment will help set a baseline for progress measurement.
- Define Security Objectives: Establish clear and measurable security objectives that align with the organization’s goals and the requirements of the chosen framework. Set specific targets for enhancing security controls, reducing vulnerabilities, and improving incident response capabilities.
- Develop Policies and Procedures: Create comprehensive security policies and procedures that reflect the principles and controls outlined in the cybersecurity framework. These policies and procedures should address areas such as access controls, data protection, incident response, employee training, and vendor management.
- Allocate Resources: Allocate the necessary financial, human, and technological resources to support the implementation of the cybersecurity framework. This may include investing in security technologies, training employees, hiring additional staff, or engaging external cybersecurity experts or consultants.
- Implement Technical Controls: Deploy appropriate technical measures and controls to enhance the security of the organization’s systems and data. This may include implementing firewalls, antivirus software, intrusion detection systems, data encryption, and multi-factor authentication, among others.
- Educate and Train Employees: Conduct cybersecurity awareness training programs to educate employees about the risks, best practices, and policies outlined in the framework. Promote a culture of cybersecurity awareness and ensure that employees understand their roles and responsibilities in maintaining a secure environment.
- Establish Incident Response Plans: Develop incident response plans and procedures that outline how the organization will detect, respond to, and recover from cybersecurity incidents. This includes establishing protocols for incident reporting, analysis, containment, recovery, and lessons learned.
- Monitor and Evaluate: Continuously monitor and evaluate the effectiveness of the implemented controls and processes. Regularly assess and measure compliance with the cybersecurity framework’s requirements. Perform periodic audits, vulnerability assessments, and penetration testing to identify areas of improvement and address new threats.
- Regularly Update the Framework: Stay up to date with evolving cybersecurity risks and the modifications to the cybersecurity framework. Regularly review and update policies, procedures, and security controls to address new threats, vulnerabilities, and regulatory changes. Maintain a culture of continuous improvement within the organization.
Remember that implementing a cybersecurity framework is an ongoing process that requires commitment, continuous monitoring, and regular updates. It is essential to adapt and evolve the framework as new threats emerge, industry standards change, and the organization grows and evolves.
In summary, implementing a cybersecurity framework involves involving stakeholders, conducting a baseline assessment, defining security objectives, developing policies and procedures, allocating resources, implementing technical controls, educating employees, establishing incident response plans, monitoring and evaluating, and regularly updating the framework. By following these steps and maintaining a proactive and diligent approach, organizations can establish a robust cybersecurity framework to protect their valuable assets and data against emerging cyber threats.
Challenges and Considerations in Using Cybersecurity Frameworks
While implementing a cybersecurity framework can greatly strengthen an organization’s security posture, there are various challenges and considerations that need to be taken into account. These challenges can impact the effectiveness and successful implementation of a cybersecurity framework. Here are some key considerations to keep in mind:
- Complexity and Customization: Cybersecurity frameworks can be complex and require customization to fit an organization’s unique needs. It is crucial to carefully assess the framework’s requirements and determine how it aligns with the organization’s goals, risk profile, and available resources. This may involve tailoring the framework to address specific industry regulations or internal compliance requirements.
- Resource Allocation: Implementing a cybersecurity framework requires a significant allocation of resources, including financial, human, and technological resources. Organizations must ensure they have the right expertise, personnel, and financial backing to effectively implement and maintain the framework. This may involve training employees, hiring dedicated cybersecurity staff, and investing in advanced security technologies.
- Continued Vigilance: Cybersecurity is an ongoing effort and requires continual vigilance. Organizations must remain proactive in monitoring and adapting their security measures to address evolving threats. This includes regularly reviewing and updating cybersecurity policies, procedures, and controls, as well as conducting regular security assessments and audits.
- User Awareness and Engagement: Employee awareness and engagement are critical factors in the successful implementation of a cybersecurity framework. It is essential to provide clear, effective training programs to educate employees about the risks, best practices, and policies outlined in the framework. Employees should be actively involved in reporting potential security incidents and adhering to established security procedures.
- Interoperability: Organizations often face challenges when integrating multiple frameworks or aligning their chosen framework with existing systems and processes. It is important to assess the interoperability of the cybersecurity framework with other systems and frameworks already in place within the organization. This may require adapting and integrating elements of different frameworks to ensure smooth collaboration and consistency.
- Inherent Limitations: It is important to acknowledge that cybersecurity frameworks have inherent limitations. No framework can guarantee absolute security or protect against all cyber threats. Organizations should consider the framework as a foundation and continuously assess and enhance their security measures beyond the framework’s requirements.
- Evolution of Threat Landscape: Cyber threats and attack techniques are constantly evolving. Organizations must remain updated and adaptive to address new threats that may not be explicitly covered by the chosen framework. This requires staying informed about industry trends, emerging threats, and new cybersecurity technologies through continuous learning and information sharing.
- Cost-Benefit Analysis: Organizations must conduct a thorough cost-benefit analysis to determine the financial implications of implementing a cybersecurity framework. This includes assessing the potential return on investment, considering the costs associated with training, implementation, and ongoing maintenance, and evaluating the value the framework brings in terms of risk reduction and compliance.
By understanding and addressing these challenges and considerations, organizations can enhance their chances of successful implementation and maximize the benefits of a cybersecurity framework. It is essential to view the framework as a dynamic and customizable tool that requires continual monitoring, adaptation, and improvement to effectively protect against evolving cyber threats.
In summary, implementing a cybersecurity framework involves navigating challenges such as complexity and customization, resource allocation, continued vigilance, user awareness, interoperability, inherent limitations, the evolving threat landscape, and conducting a cost-benefit analysis. By addressing these considerations, organizations can optimize the implementation of the framework and enhance their overall cybersecurity posture.
The Future of Cybersecurity Frameworks
The field of cybersecurity is constantly evolving as technology advances and cyber threats become more sophisticated. The future of cybersecurity frameworks holds several exciting possibilities to address these challenges and ensure the effective protection of organizations’ digital assets. Here are some key trends and possibilities that may shape the future of cybersecurity frameworks:
- Integration with Artificial Intelligence (AI) and Machine Learning (ML): AI and ML technologies have the potential to revolutionize cybersecurity frameworks. These technologies can be utilized to automate threat detection, enhance incident response capabilities, and analyze large volumes of data to identify patterns and anomalies more effectively. Integrating AI and ML into cybersecurity frameworks can offer proactive and real-time defenses against emerging threats.
- Adaptation to the Internet of Things (IoT): As the number of connected devices continues to grow, cybersecurity frameworks will need to adapt to address the unique challenges posed by IoT devices. Frameworks will need to provide specific guidelines for securing IoT devices, managing data integrity and privacy, and addressing the potential vulnerabilities introduced by this expanding ecosystem.
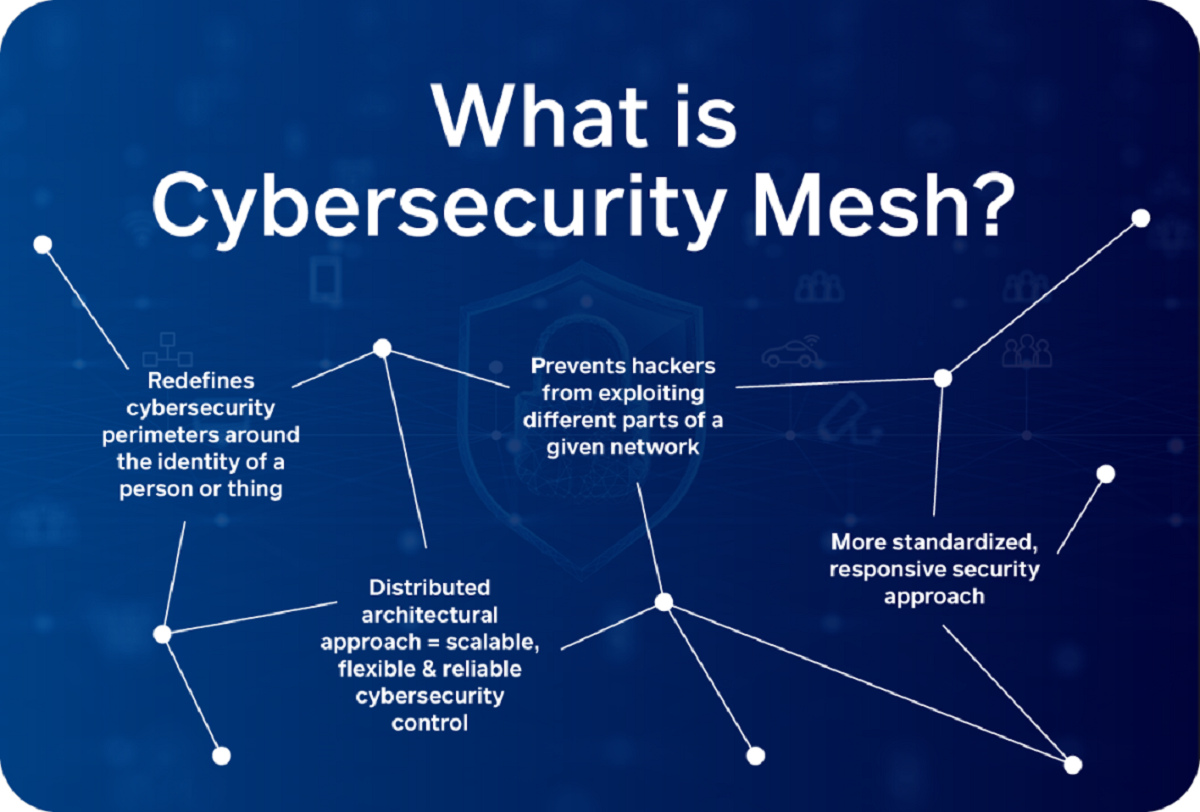
- Shift towards Zero Trust Architecture: The traditional perimeter-based security model is becoming less effective in today’s interconnected world. Cybersecurity frameworks will likely embrace the concept of Zero Trust, which assumes that no user or device can be trusted within the network by default. This will involve implementing rigorous access controls, continuous authentication, and network segmentation to minimize the impact of potential breaches.
- Emphasis on Privacy and Data Protection: With the increasing focus on data privacy and stricter regulations such as the General Data Protection Regulation (GDPR), cybersecurity frameworks will likely place a greater emphasis on privacy and data protection. Organizations will need to adopt frameworks that provide clear guidelines on data handling, encryption, consent management, and breach reporting to comply with evolving privacy regulations.
- Integration of Threat Intelligence: Threat intelligence will play an essential role in future cybersecurity frameworks. By integrating real-time threat intelligence feeds and platforms into frameworks, organizations can leverage up-to-date information on emerging threats and vulnerabilities. This will enable more proactive and targeted cybersecurity measures.
- Focus on Human Factors: Recognizing that human error is a significant contributor to cybersecurity incidents, future frameworks will likely place a greater emphasis on human factors. This will involve incorporating comprehensive training and awareness programs, user behavior analytics, and measures to promote a culture of cybersecurity throughout organizations. Human-centric approaches will be critical in mitigating insider threats and social engineering attacks.
- Global Collaboration and Standardization: Given the global nature of cyber threats, future cybersecurity frameworks will likely promote greater collaboration and standardization among countries, industries, and regulatory bodies. This will encourage the sharing of threat intelligence, best practices, and harmonization of cybersecurity requirements, facilitating a stronger collective defense against cyber threats.
In summary, the future of cybersecurity frameworks holds promising developments such as the integration of AI and ML, adaptation to IoT challenges, the shift towards Zero Trust architecture, emphasis on privacy protection, integration of threat intelligence, focus on human factors, and increased collaboration and standardization. By embracing these trends and possibilities, cybersecurity frameworks can keep pace with evolving cyber risks and provide organizations with effective tools and strategies to safeguard their digital assets.
Conclusion
Cybersecurity is a critical concern in today’s digital world, where cyber threats are constantly evolving and becoming increasingly sophisticated. The adoption of cybersecurity frameworks provides organizations with a structured and systematic approach to protecting their digital assets and mitigating cyber risks.
Throughout this article, we have explored the definition of cybersecurity, the importance of cybersecurity frameworks, various types of frameworks, common frameworks, considerations for choosing the right framework, implementation processes, challenges, and the future of cybersecurity frameworks.
Cybersecurity frameworks offer several benefits, including structure and guidance, compliance with industry standards and regulations, effective risk management, consistency in security practices, efficient resource allocation, enhanced reputation, and continuous improvement.
However, implementing a cybersecurity framework comes with its own set of challenges and considerations. Organizations must carefully assess their needs, allocate sufficient resources, address interoperability issues, maintain vigilance in a constantly evolving threat landscape, and conduct cost-benefit analyses to ensure effective implementation and ongoing success.
Looking to the future, cybersecurity frameworks will continue to evolve and adapt to address emerging technologies and threats. Integration with AI and ML, protection of IoT devices, a shift towards Zero Trust architecture, emphasis on privacy and data protection, integration of threat intelligence, focus on human factors, and global collaboration and standardization will shape the future of cybersecurity frameworks.
In conclusion, implementing a cybersecurity framework is crucial for organizations to protect their valuable assets from evolving cyber threats. By choosing the right framework, customizing it to their specific needs, implementing robust security measures, and staying proactive, organizations can establish a strong cybersecurity foundation and minimize the risks associated with cyber attacks.