Introduction
Cybersecurity has become a critical concern in today’s interconnected world. With the increasing reliance on digital technologies and the ever-growing threat of cyber-attacks, protecting sensitive information and maintaining the integrity of systems has become vital for individuals, organizations, and governments alike.
Cybersecurity refers to the practice of ensuring the confidentiality, integrity, and availability of information by safeguarding it against unauthorized access, use, disclosure, disruption, modification, or destruction. It involves implementing robust security measures, employing advanced technologies, and adopting best practices to combat cyber threats.
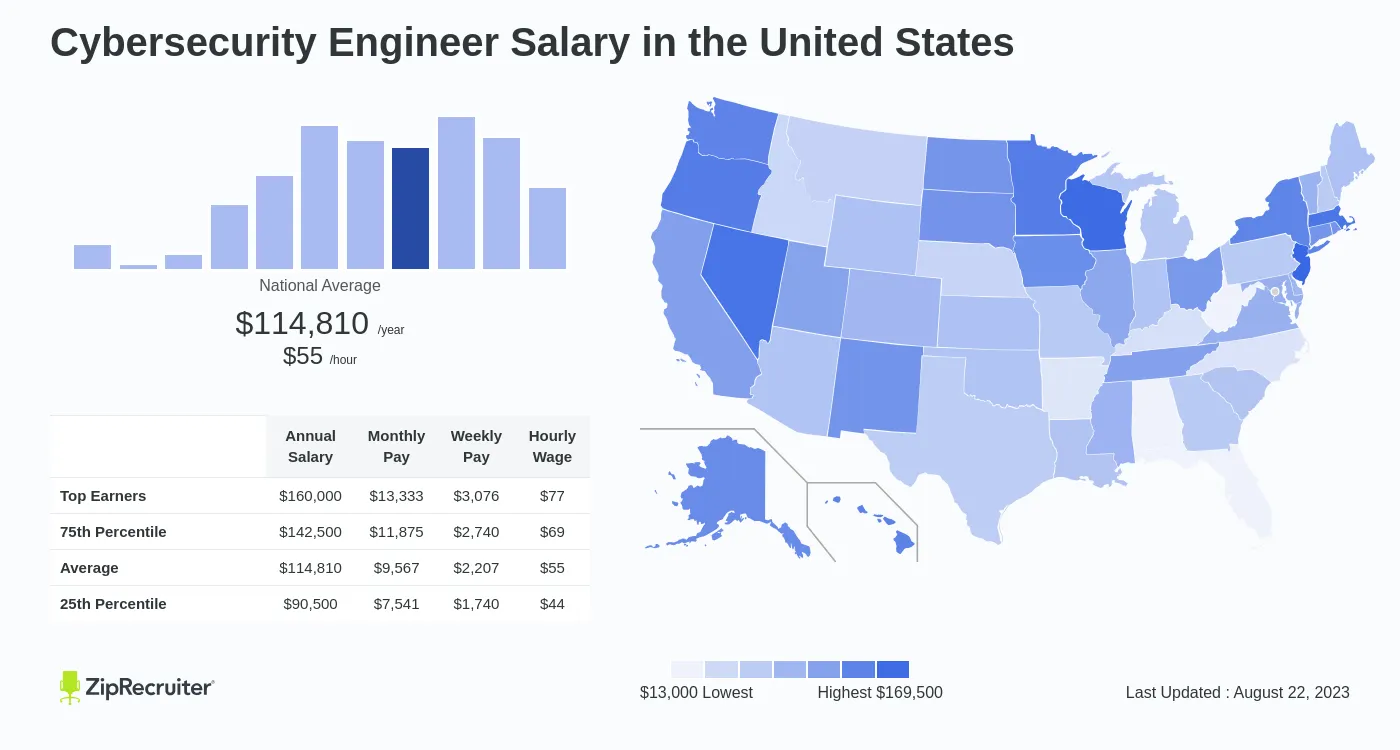
As cyber threats continue to evolve and become more sophisticated, the need for skilled professionals to defend against them is paramount. This is where cybersecurity engineers play a crucial role.
Cybersecurity engineers are specialized professionals responsible for designing, implementing, and managing security measures to protect computer systems, networks, applications, and data from cyber threats. They are on the front lines, working tirelessly to ensure the confidentiality, availability, and integrity of digital assets.
In this article, we will explore the world of cybersecurity engineering, delve into the skills and qualifications required for this role, and examine the various responsibilities and tasks that cybersecurity engineers undertake. We will also touch upon the emerging technologies and trends shaping the field of cybersecurity. So, without further ado, let’s dive into the exciting world of cybersecurity engineering and discover what it takes to become a cybersecurity engineer.
What is Cybersecurity?
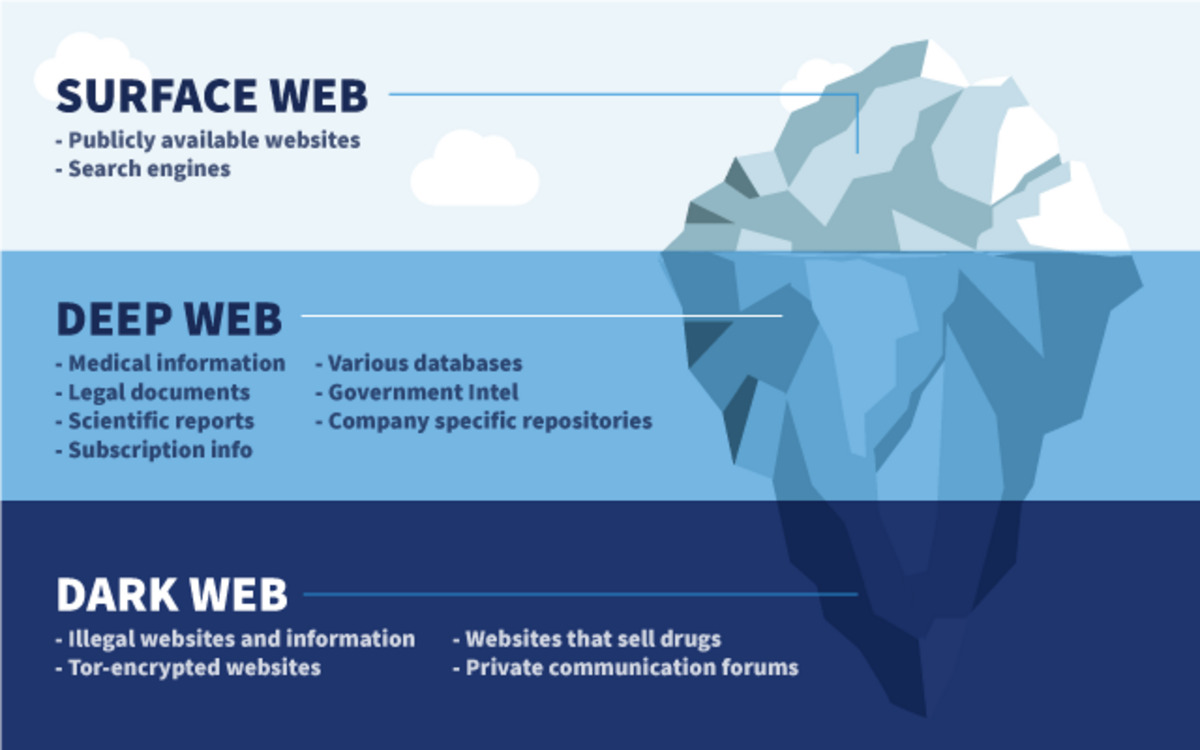
Cybersecurity is the practice of protecting electronic information and systems from unauthorized access, use, disclosure, disruption, modification, or destruction. It encompasses a range of strategies, technologies, and processes designed to safeguard computers, servers, networks, mobile devices, and other digital assets from cyber threats.
In today’s digital age, where almost every aspect of our lives is interconnected through the internet, cybersecurity has become a critical concern. Cybercriminals are constantly evolving and becoming more sophisticated in their methods, posing a significant risk to individuals, businesses, and even governments.
Cyberattacks can take various forms, such as malware infections, phishing scams, ransomware attacks, denial-of-service (DoS) attacks, data breaches, and identity theft. These attacks can result in financial loss, reputational damage, legal consequences, and the compromise of sensitive information.
To combat these threats, cybersecurity employs a multi-layered approach, incorporating a combination of preventive, detective, and responsive measures. These measures include:
- Access Control: Implementing strong authentication mechanisms and authorization policies to ensure that only authorized individuals have access to sensitive data and systems.
- Firewalls: Deploying network firewalls to monitor and filter incoming and outgoing network traffic, preventing unauthorized access and blocking malicious activities.
- Encryption: Encrypting data at rest and in transit to protect it from being intercepted or tampered with by unauthorized individuals.
- Intrusion Detection and Prevention Systems (IDPS): Deploying specialized software and hardware systems to monitor network traffic and detect and prevent malicious activities.
- Security Awareness and Training: Educating users about best practices, such as avoiding suspicious emails and links, creating strong passwords, and updating software regularly.
Overall, cybersecurity aims to proactively identify vulnerabilities, mitigate risks, and respond to cyber incidents promptly. It is a continuous effort that requires ongoing monitoring, analysis, and adaptation to the ever-evolving threat landscape.
Importance of Cybersecurity
Cybersecurity plays a crucial role in safeguarding our digital world and protecting individuals, organizations, and nations from the growing threat of cyber-attacks. Here are some key reasons why cybersecurity is of utmost importance:
- Data Protection: In today’s interconnected world, organizations collect and store vast amounts of sensitive data, including financial information, personal records, and intellectual property. Cybersecurity ensures the confidentiality and integrity of this data, preventing unauthorized access, theft, or tampering.
- Prevention of Financial Loss: Cyber-attacks can have severe financial implications. A single data breach or ransomware attack can result in substantial financial losses, including legal costs, system remediation, customer compensation, and damage to reputation. Implementing robust cybersecurity measures helps mitigate these risks and safeguard financial resources.
- Protection of Privacy: Personal information, such as social security numbers, addresses, and medical records, are valuable assets that need to be safeguarded. Cybersecurity ensures the privacy and protection of this sensitive information, preventing identity theft and other privacy breaches.
- Maintaining Business Continuity: A cyber-attack can disrupt business operations, leading to significant downtime and loss of productivity. By implementing cybersecurity measures, organizations can minimize disruptions and ensure the continuity of their operations.
- Protection of National Security: Cyber-attacks targeting critical infrastructures, government systems, and defense networks can pose a threat to national security. Strong cybersecurity practices and defenses are essential to protect sensitive government information and systems from potential cyber threats.
- Preserving Trust and Reputation: Organizations that prioritize cybersecurity establish trustworthiness with customers, partners, and stakeholders. By safeguarding data and systems, they demonstrate a commitment to protecting sensitive information, earning the trust and confidence of their stakeholders.
- Adapting to Evolving Threats: Cybercriminals are constantly evolving their tactics, making it vital for organizations to stay updated and resilient against new threats. Cybersecurity measures and strategies help organizations adapt to the changing threat landscape, ensuring the ongoing protection of their digital assets.
Overall, effective cybersecurity is essential to protect our digital infrastructure, maintain privacy, preserve financial resources, and ensure the smooth functioning of businesses and governments. By prioritizing cybersecurity, we can minimize the risks of cyber-attacks and create a safer and more secure digital world.
What is a Cybersecurity Engineer?
A cybersecurity engineer is a specialized professional responsible for designing, implementing, and managing security measures to protect computer systems, networks, applications, and data from cyber threats. They play a crucial role in ensuring the confidentiality, integrity, and availability of digital assets.
Cybersecurity engineers work on the front lines, defending against cyber-attacks and staying up-to-date with the latest threats and vulnerabilities. They possess a deep understanding of information security principles, risk management, and various technologies to effectively protect against and respond to cyber threats.
These professionals are involved in various aspects of cybersecurity, including:
- Risk Assessment: Cybersecurity engineers perform risk assessments to identify vulnerabilities and determine the potential impact of cyber threats on computer systems and networks. They analyze the likelihood of various risk scenarios and develop strategies to mitigate these risks.
- Security Architecture Design: They design and implement security architectures that provide the necessary defenses against cyber threats. This involves developing secure network configurations, selecting appropriate security technologies, and integrating security controls into systems and applications.
- Security Implementation: They are responsible for implementing security measures, such as firewalls, intrusion detection systems, encryption protocols, and access control mechanisms. They ensure that security measures are properly deployed and configured to provide effective protection against threats.
- Incident Response: Cybersecurity engineers play a crucial role in incident response, managing and responding to cybersecurity incidents. They investigate security breaches, analyze the impact of incidents, and take appropriate measures to contain and mitigate the damage caused.
- Security Testing: They conduct vulnerability assessments and penetration testing to identify weaknesses in systems and applications. By simulating real-world attacks, they identify vulnerabilities and provide recommendations for remediation.
- Security Monitoring: Cybersecurity engineers monitor network traffic, log data, and security systems to detect and respond to potential security incidents. They analyze system logs, investigate suspicious activities, and take corrective actions to prevent unauthorized access or data breaches.
To be successful as a cybersecurity engineer, individuals must possess strong technical skills, including knowledge of network protocols, server administration, encryption algorithms, and programming languages. They should also stay updated on the latest cybersecurity threats and industry best practices, as the field is constantly evolving.
In addition to technical skills, cybersecurity engineers need to have excellent analytical thinking, problem-solving abilities, and strong communication skills. They often work closely with other IT teams, management, and stakeholders to implement effective security solutions and communicate potential risks.
Overall, cybersecurity engineers play a vital role in protecting organizations and individuals from cyber threats. Their expertise and proactive approach to security are essential in today’s digital landscape where cyber-attacks are becoming increasingly sophisticated.
Skills and Qualifications of a Cybersecurity Engineer
A cybersecurity engineer must possess a diverse range of technical and non-technical skills to effectively protect computer systems and networks from cyber threats. Here are some essential skills and qualifications required for this role:
- Technical Skills: A cybersecurity engineer should have a strong understanding of networking protocols, operating systems, and security tools. They should be proficient in technologies such as firewalls, intrusion detection systems, vulnerability assessment tools, and encryption protocols. Additionally, knowledge of programming languages like Python, Java, or C++ is valuable for scripting and automating security processes.
- Risk Management: Cybersecurity engineers must have a thorough understanding of risk management principles and methodologies. They should be able to conduct risk assessments, identify vulnerabilities, and prioritize security measures based on potential risks. Knowledge of frameworks such as ISO 27001 or NIST Cybersecurity Framework is essential.
- Penetration Testing: Proficiency in conducting vulnerability assessments and penetration testing is crucial. Cybersecurity engineers should be skilled in identifying vulnerabilities in systems and applications and simulating real-world attacks to assess their impact. Knowledge of tools like Burp Suite or Metasploit is advantageous.
- Forensics and Incident Response: Familiarity with digital forensics tools and incident response techniques is essential. Cybersecurity engineers should be able to investigate security incidents, analyze log data, and perform forensic analysis to understand the cause and extent of a breach. They should also be capable of developing incident response plans and leading effective response efforts.
- Security Awareness: Cybersecurity engineers need to possess excellent communication skills and the ability to educate and raise awareness among employees about cybersecurity best practices. They should be able to articulate complex security concepts in a non-technical manner and promote a culture of security within the organization.
- Continuous Learning: The field of cybersecurity is constantly evolving, with new threats and technologies emerging regularly. A cybersecurity engineer should have a strong drive for continuous learning and staying up-to-date with the latest industry trends, threat intelligence, and security tools.
Along with technical skills, certain qualifications and certifications can enhance a cybersecurity engineer’s credibility and expertise. Common certifications in the field include CompTIA Security+, Certified Information Systems Security Professional (CISSP), Certified Ethical Hacker (CEH), and Certified Information Security Manager (CISM). These certifications validate the knowledge and skills of cybersecurity professionals and demonstrate their commitment to the field.
In summary, a cybersecurity engineer should possess a diverse range of technical skills, including knowledge of networking, security tools, risk management, and incident response. They should also have excellent communication skills, a passion for continuous learning, and a commitment to staying updated on industry trends. By combining these skills and qualifications, cybersecurity engineers become effective defenders against the ever-evolving landscape of cyber threats.
Roles and Responsibilities of a Cybersecurity Engineer
A cybersecurity engineer has a wide range of critical responsibilities in ensuring the security of computer systems, networks, and data. Their role involves implementing, managing, and continuously improving security measures to protect against cyber threats. Here are the key roles and responsibilities of a cybersecurity engineer:
- Risk Assessment: Conducting risk assessments to identify vulnerabilities and analyze potential risks to computer systems and networks. They evaluate the likelihood and impact of various risk scenarios and develop strategies and controls to mitigate those risks.
- Security Architecture Design: Designing and implementing secure architectures that provide effective protection against cyber threats. This includes designing secure network configurations, selecting and implementing appropriate security technologies, and integrating security controls into systems and applications.
- Security Implementation: Implementing security measures, such as firewalls, intrusion detection systems, encryption protocols, and access control mechanisms. They ensure that security solutions are properly deployed, configured, and operate effectively to defend against cyber threats.
- Incident Response: Managing and responding to cybersecurity incidents promptly and effectively. They investigate security breaches, analyze the impact of incidents, and take appropriate measures to contain and mitigate the damage caused. This includes developing incident response plans, coordinating with relevant stakeholders, and implementing corrective actions.
- Security Testing: Conducting vulnerability assessments and penetration testing to identify weaknesses in systems and applications. They simulate real-world attacks to assess the potential impact of vulnerabilities and provide recommendations for remediation. This helps in improving the overall security posture of the organization.
- Security Monitoring: Monitoring network traffic, log data, and security systems to detect and respond to potential security incidents. They analyze system logs, investigate suspicious activities, and take proactive measures to prevent unauthorized access, data breaches, or other malicious activities.
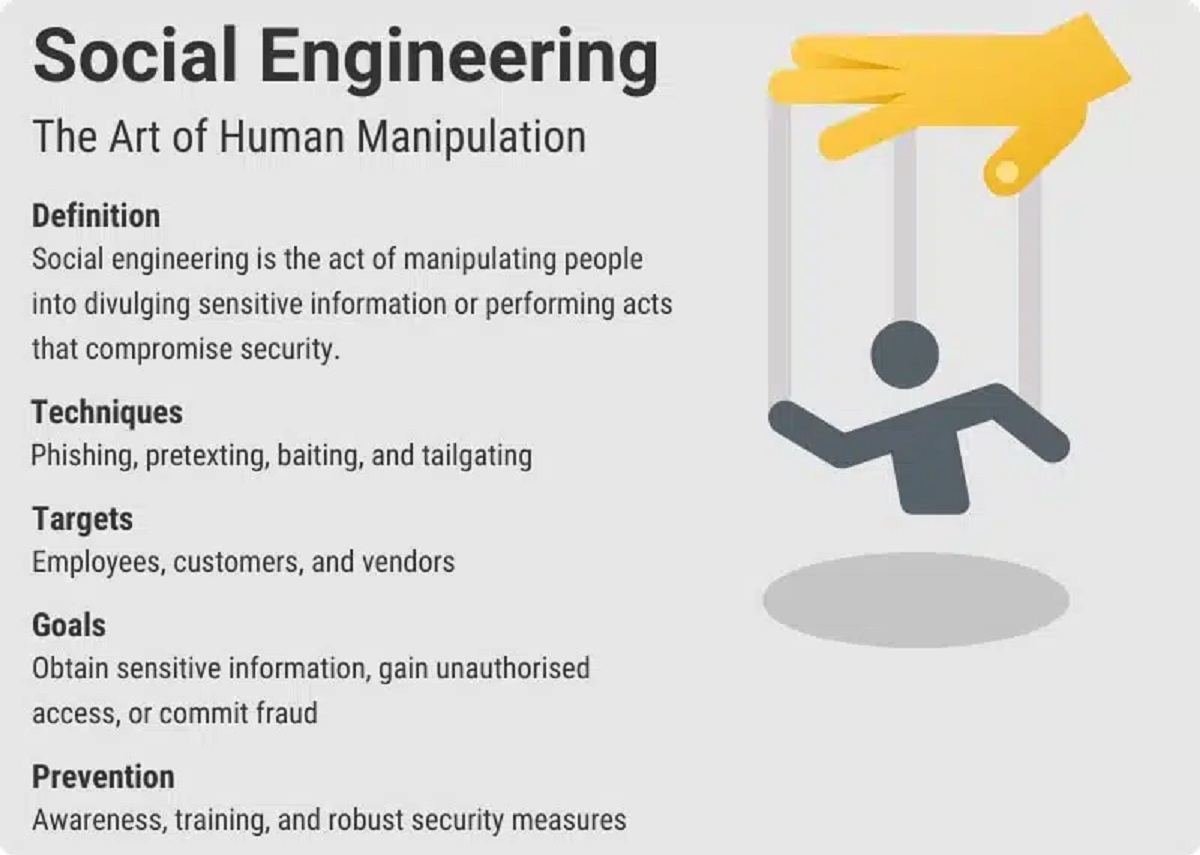
- Security Awareness and Training: Promoting security awareness and education within the organization. They develop and deliver training programs to educate employees on cybersecurity best practices, such as safe browsing habits, password management, and social engineering awareness. They also conduct security awareness campaigns to promote a culture of security.
- Security Policy Development: Developing and implementing security policies, standards, and procedures in alignment with industry best practices and compliance requirements. They ensure that security policies address the specific needs of the organization and provide guidelines for secure operations.
In addition to these responsibilities, a cybersecurity engineer must stay updated on the latest threats, vulnerabilities, and industry best practices. They should continuously evaluate and assess the effectiveness of security controls and propose improvements as needed. Furthermore, collaborating with other IT teams, management, and stakeholders is essential to ensure that security measures align with overall business objectives.
By effectively fulfilling these roles and responsibilities, cybersecurity engineers play a pivotal role in protecting organizations from cyber threats and maintaining the confidentiality, integrity, and availability of critical assets.
Threat Modeling and Risk Assessment
Threat modeling and risk assessment are two essential components of cybersecurity that help organizations identify vulnerabilities, evaluate potential risks, and prioritize security measures. Let’s delve into these two crucial processes in more detail:
Threat Modeling: Threat modeling is the process of identifying and evaluating potential threats and vulnerabilities that could exploit weaknesses in computer systems, networks, or applications. It involves analyzing the architecture, design, and implementation of the system to identify potential entry points for attackers and potential misuse scenarios.
During the threat modeling process, cybersecurity engineers consider various factors, such as identified threats, potential attack vectors, possible motivations of attackers, and the value of the assets being protected. They collaborate with system architects, developers, and stakeholders to gain a comprehensive understanding of the system’s structure and functionality.
The output of a threat modeling exercise typically includes a detailed analysis of potential threats, mitigation strategies, and recommendations for security controls. It helps organizations proactively identify and address vulnerabilities before they can be exploited by malicious actors. Effective threat modeling allows cybersecurity engineers to design and implement strong security architectures and controls that protect against a wide range of threats.
Risk Assessment: Risk assessment is the process of evaluating potential risks and their potential impact on systems, networks, or applications. It involves identifying and analyzing vulnerabilities, assessing the likelihood of threats occurring, and evaluating the potential consequences of these threats.
During a risk assessment, cybersecurity engineers assign risk levels based on the probability of a threat event occurring and the potential impact it could have on the organization. This helps prioritize resources and focus efforts on mitigating risks that pose the greatest potential harm.
Risk assessments consider various factors, such as the sensitivity of the information being protected, the threat landscape, potential vulnerabilities, and regulatory compliance requirements. The assessment can range from a qualitative assessment, using subjective judgment, to a quantitative assessment, involving data-driven analysis.
The results of a risk assessment guide decision-making processes, such as the selection of security measures, implementation of controls, and allocation of resources. It helps organizations make informed decisions based on the identified risks and enables them to allocate resources effectively to address the most critical vulnerabilities and threats.
By incorporating threat modeling and risk assessment into their cybersecurity practices, organizations can proactively identify and mitigate potential threats and vulnerabilities. These processes enable cybersecurity engineers to take a proactive and strategic approach to protect critical systems, networks, and applications from cyber threats.
Network Security Management
Network security management is a critical aspect of cybersecurity that focuses on protecting computer networks from unauthorized access, misuse, and malicious activities. It involves implementing and managing security measures to safeguard network infrastructure, devices, and data. Let’s explore the key components of network security management:
Firewalls: Firewalls are an essential component of network security management. They monitor and control incoming and outgoing network traffic based on predefined security policies. Firewalls help prevent unauthorized access, block malicious activities, and provide a barrier of protection between internal networks and external threats.
Intrusion Detection and Prevention Systems (IDPS): IDPSs are software or hardware systems that monitor network traffic for suspicious activities or signs of potential intrusions. They analyze network packets, log data, and identify threats or policy violations. IDPSs can detect and alert security teams about potential attacks, enabling timely responses and mitigating the impact of security incidents.
Virtual Private Networks (VPNs): VPNs provide secure communication over public networks by creating encrypted tunnels for data transmission. By encrypting data, VPNs ensure that sensitive information remains confidential and protected from interception. VPNs are commonly used to establish secure remote connections for employees accessing company networks from external locations.
Network Segmentation: Network segmentation involves dividing a network into smaller segments or subnetworks to enhance security. By separating different departments, systems, or functionalities, network segmentation limits the impact of a potential breach. If one segment is compromised, it reduces the attacker’s ability to move laterally within the network.
Wireless Network Security: Wireless networks present unique security challenges due to their susceptibility to eavesdropping and unauthorized access. Network security management includes implementing security protocols (such as WPA2) and encryption mechanisms to protect wireless network communications. Regular monitoring and auditing of wireless networks are also essential to detect and address potential vulnerabilities.
Network Access Control: Network access control mechanisms ensure that only authorized devices and users can access the network. This includes implementing strong authentication mechanisms, such as multi-factor authentication, and enforcing access control policies. Network access control helps prevent unauthorized access and restricts potential threats from entering the network.
Logging and Monitoring: Effective network security management involves logging and monitoring activities for early detection of potential security incidents. Centralized logging systems and security information and event management (SIEM) tools are used to collect and analyze logs from network devices, detecting anomalies or suspicious activities that may indicate a security breach or unauthorized access.
By implementing robust network security management practices, organizations can protect their critical network infrastructure, prevent unauthorized access, and mitigate the risk of network breaches. Regular assessments, updates to security controls, and ongoing monitoring ensure that networks remain resilient against evolving cyber threats.
Incident Response and Forensics
Incident response and forensics are crucial components of cybersecurity that focus on effectively managing and investigating security incidents. They are critical processes that help organizations minimize the impact of security breaches, gather evidence, and identify the root cause of incidents. Let’s explore these two important aspects further:
Incident Response: Incident response refers to the coordinated approach taken by organizations to address and manage security incidents effectively. It involves a well-defined plan and a set of procedures to detect, analyze, contain, eradicate, and recover from a security incident.
During an incident response, cybersecurity engineers work diligently to identify and classify the incident, assess the impact and scope of the breach, and contain any further damage. Timely detection and response are essential to minimize the impact and potential loss resulting from the incident.
Incident response typically involves the following key steps:
- Preparation: Establishing an incident response team, defining roles and responsibilities, developing an incident response plan, and implementing appropriate technological and organizational measures.
- Detection and Analysis: Recognizing and identifying potential security incidents, investigating the nature and extent of the incident, and assessing the impact on systems, networks, and data.
- Containment: Implementing immediate and proactive measures to contain the incident and prevent further damage. This may involve isolating affected systems or disconnecting them from the network.
- Eradication: Identifying the root cause of the incident, eliminating the vulnerabilities that allowed the breach, and restoring systems to a secure state.
- Recovery: Returning systems and operations to a normal and secure state. This includes restoring data, repairing affected systems, and implementing necessary measures to prevent similar incidents in the future.
- Post-Incident Analysis: Conducting a thorough analysis of the incident to identify lessons learned, improve incident response capabilities, and enhance future preventive measures.
Forensics: Digital forensics is the process of collecting, analyzing, and preserving digital evidence as part of an incident investigation. Cybersecurity engineers skilled in digital forensics techniques use various tools and methodologies to investigate security incidents, identify the cause, and gather evidence for potential legal proceedings.
Forensic analysis involves:
- Collecting Evidence: Identifying and collecting relevant data from affected systems, networks, or devices while ensuring the integrity and confidentiality of the evidence.
- Preserving Evidence: Employing techniques to ensure the preservation and integrity of collected evidence, including creating forensic images of affected systems or devices.
- Analysis and Reconstruction: Examining collected evidence to reconstruct the sequence of events, identify the attacker’s activities, and determine the extent of the breach.
- Reporting: Documenting findings, preparing reports, and presenting the collected evidence in a format suitable for legal proceedings if required.
The incident response and forensics processes are crucial in providing timely and effective responses to security incidents, mitigating damage, and preventing future incidents. By implementing robust incident response and forensics practices, organizations can enhance their cybersecurity capabilities and strengthen their ability to protect critical assets.
Vulnerability Management and Penetration Testing
Vulnerability management and penetration testing are integral parts of a comprehensive cybersecurity strategy. They help organizations identify and address vulnerabilities in their systems, applications, and networks to enhance overall security. Let’s explore these two essential processes in more detail:
Vulnerability Management: Vulnerability management is the ongoing process of identifying, assessing, prioritizing, and mitigating vulnerabilities in an organization’s digital infrastructure. It involves a systematic approach to detect and address weaknesses that could be exploited by attackers.
The vulnerability management process typically includes the following steps:
- Vulnerability Assessment: Identifying vulnerabilities through automated scanning tools, manual testing, or a combination of both. This involves evaluating the security posture of systems, networks, and applications to uncover potential weaknesses.
- Vulnerability Prioritization: Assessing the severity and potential impact of vulnerabilities to determine their priority for remediation. This involves considering factors such as the likelihood of exploitation, potential impact, and available resources for mitigation.
- Remediation: Implementing appropriate measures to mitigate or eliminate identified vulnerabilities. This may involve applying security patches, configuration changes, or deploying additional security controls to reduce the overall risk.
- Continuous Monitoring: Regularly scanning and monitoring systems and networks to identify new vulnerabilities and ensure that previously remediated vulnerabilities have not resurfaced. This helps maintain a proactive security posture and enables timely response to new threats.
Vulnerability management is an iterative process that requires ongoing monitoring, analysis, and response to emerging threats and vulnerabilities. It enables organizations to prioritize their resources effectively and address vulnerabilities that pose the greatest risk to their systems and data.
Penetration Testing: Penetration testing, also known as ethical hacking, is a controlled and authorized simulated attack on an organization’s systems, networks, or applications to identify weaknesses and evaluate the effectiveness of existing security controls.
Penetration testing typically involves the following phases:
- Planning: Defining the scope, objectives, and rules of engagement for the penetration test. This may include identifying specific targets, resources, or scenarios to test.
- Reconnaissance: Gathering information about the target systems and networks, such as IP addresses, network architecture, and potential vulnerabilities. This phase helps simulate real-world attack scenarios more accurately.
- Attack Execution: Attempting to exploit identified vulnerabilities using various techniques, tools, and methodologies. This phase includes testing for common vulnerabilities, such as SQL injection, cross-site scripting (XSS), or weak authentication mechanisms.
- Evidence Collection: Documenting the steps taken during the attack and collecting evidence of successful exploitation or potential security gaps. This information helps in the analysis and remediation of identified vulnerabilities.
- Analysis and Reporting: Analyzing the results of the penetration test and preparing a detailed report that includes the identified vulnerabilities, the impact of successful exploits, and recommendations for remediation. This report is then shared with relevant stakeholders for mitigation planning.
Penetration testing provides valuable insights into the security posture of an organization’s systems and applications. It helps identify vulnerabilities that may not have been detected through other means, allowing organizations to proactively address weaknesses before they can be exploited by malicious actors.
By implementing effective vulnerability management and conducting regular penetration testing, organizations can identify and remediate vulnerabilities, strengthen their overall security defenses, and enhance their resilience against potential attacks.
Security Operations and Monitoring
Security operations and monitoring play a vital role in maintaining the security of an organization’s digital infrastructure. These processes involve continuous monitoring, analysis, and response to potential security threats and incidents. Let’s explore the key aspects of security operations and monitoring:
Security Operations: Security operations encompass the day-to-day activities and processes that ensure the ongoing security of an organization’s systems, networks, and data. It involves the management and maintenance of security controls, incident response, and the coordination of security-related activities.
Key aspects of security operations include:
- Security Incident Monitoring: Continuous monitoring of network traffic, security logs, and system alerts to detect potential security incidents and anomalous activities. Security operations teams utilize Security Information and Event Management (SIEM) systems, intrusion detection systems (IDS), and other monitoring tools to identify and respond to security events.
- Alert Triage and Analysis: Analyzing security alerts generated by monitoring tools to assess their severity, validity, and potential impact. This involves distinguishing false positives from true positives and prioritizing the response to active security threats.
- Investigation and Response: Investigating and responding to security incidents in a timely and effective manner. This may involve coordinating with other response teams, gathering evidence, containing the incident, and implementing appropriate remediation measures to mitigate the impact and prevent further exploitation.
- Threat Hunting: Proactively searching for signs of potential security threats or malicious activities that may have evaded traditional security controls. Threat hunting involves utilizing advanced analytics, threat intelligence, and proactive techniques to identify and respond to emerging threats before they can cause significant damage.
- Security Tool Management: Managing and maintaining security tools and technologies, such as firewalls, intrusion detection systems, anti-malware software, and vulnerability scanners. This includes keeping these tools up-to-date with the latest signatures, patches, and configurations for optimal performance and effectiveness.
Security Monitoring: Security monitoring involves the continuous observation and analysis of systems, networks, and applications to detect potential security breaches, vulnerabilities, or unauthorized activities. It focuses on proactively identifying and responding to threats, preventing potential security incidents before they occur.
Key aspects of security monitoring include:
- Network Traffic Analysis: Monitoring network traffic patterns to identify anomalies, suspicious activities, or potential indicators of compromise. This helps in detecting and blocking unauthorized access attempts, data exfiltration attempts, or denial-of-service attacks.
- Log Analysis: Analyzing security logs from various systems and devices to identify signs of malicious activities, such as failed login attempts, system misconfigurations, or unusual access patterns. Log analysis provides insights into potential security incidents or areas of vulnerability.
- Endpoint Monitoring: Monitoring endpoints, including computers, servers, and mobile devices, for unusual behavior or signs of compromise. This includes monitoring for malware infections, unauthorized access attempts, or suspicious data transfers.
- Anomaly Detection: Utilizing machine learning algorithms and behavior-based analytics to detect unusual or abnormal activities that may indicate a security threat. Anomaly detection can help identify new and previously unknown threats that may not be captured by traditional signature-based methods.
- Continuous Vulnerability Monitoring: Scanning systems and applications for known vulnerabilities, assessing their severity, and ensuring timely remediation. Continuous vulnerability monitoring helps identify weaknesses before they can be exploited by attackers.
By maintaining effective security operations and monitoring capabilities, organizations can ensure the timely detection and response to security threats, minimizing the potential impact of security incidents. These processes are essential for maintaining the security posture of an organization and protecting sensitive data, systems, and networks.
Security Policy Development and Compliance
Security policy development and compliance are essential components of an effective cybersecurity framework. Security policies serve as guidelines and standards that outline the organization’s expectations and requirements for protecting sensitive information, computer systems, and networks. Let’s explore the key aspects of security policy development and compliance:
Security Policy Development: Security policy development involves creating and maintaining a comprehensive set of policies and procedures that define the organization’s security objectives, protocols, and responsibilities. These policies provide guidelines for establishing a secure environment and promoting good security practices throughout the organization.
Key aspects of security policy development include:
- Policy Framework: Establishing a framework for developing and organizing security policies, including roles and responsibilities for policy development, approval, and revision processes. This ensures that policies align with the organization’s needs and industry best practices.
- Risk Assessment: Conducting risk assessments to identify potential threats and vulnerabilities and determining the appropriate security controls and policies to address the identified risks. Risk assessment helps organizations prioritize the creation of policies based on potential impact and likelihood of occurrence.
- Security Policy Components: Developing policies that cover a range of areas, such as access controls, password management, data classification, incident response, secure coding practices, and acceptable use of IT resources. Each policy should define the desired behavior or action, establish responsibilities, and provide clear guidelines for compliance.
- Policy Communication and Training: Communicating the security policies across the organization to ensure that all employees and stakeholders understand their rights and obligations. This includes conducting security awareness training to educate employees about the importance of adhering to the policies and promoting a culture of security.
- Policy Review and Update: Regularly reviewing and updating security policies to reflect changes in technology, evolving threats, and regulatory requirements. This ensures that policies remain relevant and effective in protecting the organization’s assets.
Compliance: Compliance refers to the process of adhering to applicable laws, regulations, and industry standards related to information security. It involves ensuring that security policies and practices meet the requirements set forth by relevant authorities and regulatory bodies.
Key aspects of compliance include:
- Regulatory Requirements: Understanding and keeping up-to-date with relevant laws, regulations, and industry standards that apply to the organization. This may include standards like the General Data Protection Regulation (GDPR), Payment Card Industry Data Security Standard (PCI DSS), or Health Insurance Portability and Accountability Act (HIPAA).
- Gap Analysis: Assessing the organization’s current security posture and practices against the requirements specified by regulatory standards. This helps identify areas of non-compliance and implement necessary measures to meet the compliance requirements.
- Policy Enforcement: Ensuring that security policies are effectively implemented and enforced throughout the organization. This may include conducting regular audits, monitoring compliance, and implementing appropriate controls to mitigate risks of non-compliance.
- Documentation and Reporting: Maintaining accurate and up-to-date documentation of security policies, procedures, and evidence of compliance. This includes producing regular reports and documentation to demonstrate adherence to compliance requirements to auditors, regulators, or other governing bodies.
- Continuous Monitoring: Implementing processes and systems to monitor and assess ongoing compliance. This involves regular internal audits, vulnerability assessments, and penetration testing to identify and address any non-compliance issues.
By developing robust security policies and ensuring compliance with regulatory requirements, organizations can establish a strong security foundation and mitigate the risk of security breaches. Security policies provide a framework for consistent and best-practice security measures, promoting a culture of security throughout the organization.
Secure Software Development
Secure software development is a critical process that aims to build and deploy applications that are resilient to security threats. It involves implementing security measures throughout the software development life cycle (SDLC) to identify and mitigate potential vulnerabilities. Let’s explore the key aspects of secure software development:
Threat Modeling and Risk Assessment: Incorporating threat modeling and risk assessment early in the software development process helps identify potential security risks and prioritize security requirements. By analyzing potential threats and their impact, developers can design and build security controls to mitigate those risks.
Secure Coding Practices: Following secure coding practices is essential to reduce the likelihood of introducing vulnerabilities in software. This includes avoiding common coding mistakes, such as input validation errors, insecure direct object references, and insecure cryptographic implementations. Adhering to secure coding guidelines, such as those provided by OWASP (Open Web Application Security Project), helps developers adopt best practices.
Authentication and Access Controls: Implementing strong authentication mechanisms, such as multi-factor authentication, and granular access controls ensures that only authorized users can access sensitive functionalities and data. This reduces the risk of unauthorized access and data breaches.
Data Encryption: Incorporating encryption techniques to protect sensitive data at rest and in transit ensures that even if the data is compromised, it remains unreadable to unauthorized entities. Secure software development includes implementing strong encryption algorithms and properly managing encryption keys.
Input Validation and Output Encoding: Validating and sanitizing user inputs helps prevent common vulnerabilities like SQL injection and cross-site scripting (XSS). Proper output encoding ensures that user-supplied data is properly encoded before it is rendered to prevent XSS attacks.
Error Handling and Logging: Implementing effective error handling mechanisms helps protect against information leakage and ensures that error messages do not reveal sensitive information. Secure software development includes detailed logging to facilitate incident response and forensic analysis in the event of a security incident.
Secure Software Development Lifecycle (SDLC): Establishing a secure SDLC involves integrating security practices from the earliest stages of software development. This includes integrating security into requirements gathering, design, development, testing, and deployment. Regular security testing and code reviews throughout the SDLC help identify and address security vulnerabilities in a timely manner, reducing the risk of security incidents.
Secure Third-Party Dependences: Ensuring that third-party libraries and dependencies used within software applications are regularly updated and have a good security track record. It is crucial to perform vulnerability assessments on such dependencies to minimize the risk of incorporating vulnerable components into the software solution.
By following secure software development practices, organizations can reduce the risk of software vulnerabilities and potential cyber-attacks. Introducing security measures from the early stages of development and integrating them throughout the SDLC helps create a proactive security posture, safeguarding critical systems, and protecting sensitive information.
Emerging Technologies and Trends in Cybersecurity
The field of cybersecurity is constantly evolving to keep pace with the ever-changing threat landscape. As technology advances, new techniques and tools emerge to improve security defenses and counteract sophisticated cyber-attacks. Here are some of the emerging technologies and trends shaping the cybersecurity landscape:
Artificial Intelligence (AI) and Machine Learning: AI and machine learning are being leveraged to enhance cybersecurity by analyzing vast amounts of data, identifying patterns, and detecting anomalies. These technologies enable the development of advanced threat detection systems, behavior analytics, and automated incident response, improving real-time threat detection and response capabilities.
Internet of Things (IoT) Security: The proliferation of connected devices introduces new challenges in terms of security. With billions of IoT devices connected to networks, securing these devices and protecting the data they generate has become crucial. Emerging trends in IoT security include device identity management, secure communication protocols, and vulnerability patching mechanisms.
Cloud Security: As organizations increasingly adopt cloud computing services, ensuring the security of cloud environments has become paramount. Cloud security focuses on secure configuration, data protection, access control, and continuous monitoring. Emerging technologies in this area include cloud-native security tools, secure cloud APIs, and encryption technologies designed specifically for cloud environments.
Zero Trust Architecture: Zero Trust is an evolving security model that treats every user, device, and network component as potentially untrusted. Instead of relying on traditional perimeter-based security, this model emphasizes strict access controls, strong authentication, and continuous monitoring. Zero Trust Architecture ensures that network resources are accessed securely, regardless of the location or device being used.
Blockchain Technology: Blockchain, the underlying technology behind cryptocurrencies, is also being explored for its potential applications in cybersecurity. Its decentralized and transparent nature offers possibilities for improving data integrity, secure transactions, and identity management. Blockchain-based solutions are being explored for secure record-keeping, supply chain security, and authentication processes.
Biometric Security: Biometric authentication, such as fingerprint, facial recognition, or iris scanning, offers a more secure and convenient method of user authentication. Biometrics provide an additional layer of security compared to traditional passwords, reducing the risk of unauthorized access to systems and applications.
Cyber Threat Intelligence: The collection, analysis, and sharing of threat intelligence have become crucial for identifying emerging cyber threats. Cyber threat intelligence enables organizations to stay informed about the latest trends, tactics, and vulnerabilities used by threat actors. This knowledge helps organizations proactively update their security controls and defenses.
Privacy and Data Protection: With increasing concerns about data privacy and regulatory requirements, the focus on privacy and data protection has grown significantly. Organizations are adopting privacy-enhancing technologies, secure data handling practices, and complying with regulations like the General Data Protection Regulation (GDPR) to protect customer data and maintain trust.
These emerging technologies and trends in cybersecurity are continually evolving to address new challenges and provide advanced security solutions. By staying updated on these developments and leveraging the latest technologies, organizations can fortify their defenses and proactively protect against ever-evolving cyber threats.
Conclusion
The field of cybersecurity plays a critical role in protecting our digital world from malicious actors and cyber threats. It requires a proactive and comprehensive approach to secure systems, networks, and data from potential vulnerabilities and attacks. Cybersecurity engineers and professionals are at the forefront of this battle, diligently working to identify risks, implement protective measures, and respond to security incidents.
From understanding the importance of cybersecurity to exploring the roles and responsibilities of a cybersecurity engineer, we have delved into various aspects of this field. We have discussed the significance of threat modeling, risk assessment, network security management, incident response, vulnerability management, and secure software development. Each of these areas contributes to building a robust cybersecurity framework that helps organizations combat emerging threats and maintain resilience.
As the technology landscape continues to evolve, emerging technologies and trends are reshaping cybersecurity practices. Artificial intelligence, machine learning, IoT security, cloud security, zero-trust architecture, blockchain technology, and biometric security are just a few examples. These advancements provide new opportunities to enhance cyber defenses and safeguard critical assets.
While technological advancements are crucial, it is equally important to focus on security policy development and compliance. Establishing comprehensive security policies, ensuring adherence to regulations, and promoting a culture of security within organizations are essential for maintaining a strong security posture.
In conclusion, cybersecurity is a rapidly evolving field that requires ongoing learning, adaptability, and a proactive mindset. By staying informed about emerging threats, leveraging the latest technologies, adhering to best practices, and continuously improving security measures, organizations can protect their digital assets and mitigate the potential impact of cyber-attacks. With cybersecurity professionals at the helm, we can strive to create a safer digital environment for individuals, businesses, and societies at large.