Introducing "9 Amazing Cybersecurity Books for 2023": As technology continues to advance, the importance of cybersecurity has become increasingly evident. Whether you are an aspiring cybersecurity professional or simply interested in safeguarding your digital presence, staying updated with the latest knowledge is crucial. In this rapidly evolving field, finding the right resources can be challenging. However, fear not! We have curated a list of nine outstanding cybersecurity books that are sure to keep you informed and prepared for the cyber threats of tomorrow. Dive into these captivating pages and embark on a journey to become a cybersecurity expert in 2023.
Overall Score: 7/10
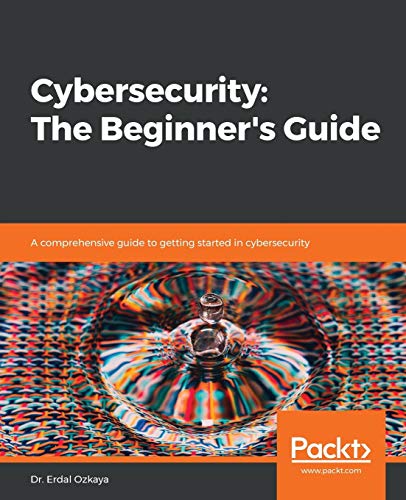
Cybersecurity: The Beginner's Guide is a comprehensive guide designed for those looking to get started in the field of cybersecurity. Featuring a historical introduction to the concept, detailed information on certifications, and expert advice from industry professionals, this book covers a range of topics relevant to anyone considering a career in cyber security. It is written in an easy-to-understand style, making it accessible to readers of all ages. However, some reviews mention issues with the editing and a lack of depth in certain areas. Overall, Cybersecurity: The Beginner's Guide serves as a valuable resource for beginners in the field of cybersecurity, providing essential information and guidance for those looking to transition into this rapidly growing industry.
Key Features
- Comprehensive guide for beginners in cybersecurity
- Historical introduction and detailed information on certifications
- Expert advice from senior industry professionals
Specifications
- Dimension: 7.50Lx0.90Wx9.25H
Pros
- Covers a range of topics relevant to cybersecurity careers
- Easy-to-understand writing style
- Provides valuable information and guidance for beginners
Cons
- Terrible editing and lack of depth in certain areas
- Some inaccuracies and misspellings found in the content
Cybersecurity: The Beginner’s Guide is a valuable resource for those looking to enter the field of cybersecurity. It offers comprehensive information and guidance for beginners, covering various topics including certifications and career planning. The historical introduction and expert advice from industry professionals add an engaging element to the book. However, some reviewers have pointed out issues with editing and a lack of depth in certain areas. Despite these drawbacks, the book serves as a helpful starting point for individuals interested in pursuing a career in cybersecurity. It is recommended as a beginner’s guide, but additional resources may be necessary to further develop one’s knowledge and skills in the field.
Overall Score: 7.5/10
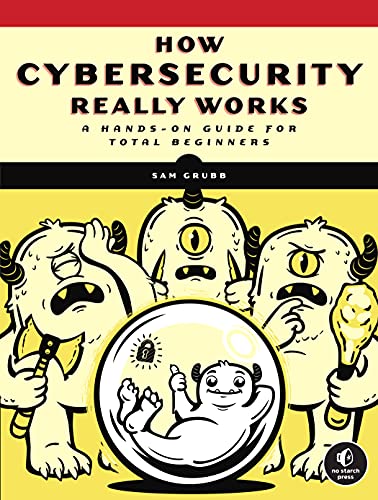
How Cybersecurity Really Works: A Hands-On Guide for Total Beginners is a comprehensive book that introduces basic cybersecurity concepts to beginners. It provides easy-to-understand explanations and serves as a valuable resource for individuals who are new to the world of cybersecurity. While the information in the book can also be found online, the author consolidates important concepts and tips in one place, making it convenient for readers. Some readers found the book lacking in-depth analysis and examples, and it does not cover Linux, servers, tablets, and cellular devices. Overall, it is a recommended read for those looking to gain a foundational understanding of cybersecurity.
Key Features
- Basic cybersecurity concepts
- Hands-on guide for beginners
- Easy-to-understand explanations
Specifications
- N/A
Pros
- Easy to read and understand
- Consolidates important information in one book
- Provides useful explanations for beginners
Cons
- Lacks in-depth analysis and examples
- Does not cover Linux, servers, tablets, and cellular devices
- Kindle format may not be preferred by some
How Cybersecurity Really Works: A Hands-On Guide for Total Beginners is a helpful introductory book for individuals new to cybersecurity. It offers clear explanations and consolidates important information. However, it falls short in providing in-depth analysis and examples. It primarily focuses on Windows and MacOS, neglecting other platforms like Linux and cellular devices. Despite its limitations, it serves as a valuable resource for beginners seeking to understand basic cybersecurity concepts. The book is particularly suitable for those studying undergraduate CyberSec courses or anyone looking to establish a foundational knowledge of cybersecurity.
Overall Score: 9/10
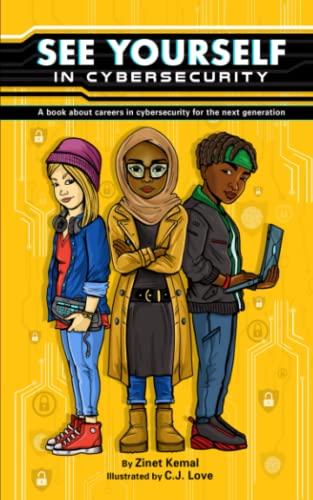
Grab a copy of 'See Yourself in Cybersecurity' for an exciting journey into the world of cybersecurity! This book is designed to inspire and inform the next generation about the various career opportunities available in cybersecurity. With colorful illustrations and playful storytelling, it keeps kids engaged while introducing them to different roles like ethical hacking and digital forensics. The book not only educates but also encourages children to envision themselves as part of this important field, sparking their imagination and curiosity. It also serves as a valuable resource for adults interested in cybersecurity. Written in a concise and easy-to-understand style, 'See Yourself in Cybersecurity' is a fantastic way to learn about this fascinating industry and promote online safety. Highly recommended!
Key Features
- Inspiring and informative journey into the world of cybersecurity
- Colorful illustrations and playful storytelling
- Introduces various roles in the cybersecurity industry
- Encourages imagination and curiosity
- Promotes online safety
Specifications
- Dimension: 5.00Lx0.09Wx8.00H
Pros
- Engaging and exciting for kids
- Helps children envision themselves in cybersecurity
- Easy to understand and well-written
- Promotes diversity in the field
- Provides valuable information for adults
Cons
- Not suitable for advanced or technical readers
‘See Yourself in Cybersecurity’ is a must-have book for anyone interested in the field. It provides an inspiring and informative journey that sparks curiosity, promotes online safety, and encourages children to see themselves as future cyber professionals. The colorful illustrations and playful storytelling make it engaging for kids, while the concise writing style appeals to adults as well. It’s an invaluable resource that breaks down complex concepts in an easy-to-understand manner, making it perfect for introducing the world of cybersecurity to readers of all ages. Whether you’re a parent, educator, or simply curious about the industry, this book is a gem that will leave a lasting impact!
Overall Score: 8/10
Looking to enhance your network security? 'Cybersecurity for Small Networks: A Guide for the Reasonably Paranoid' is a must-read for those concerned about their online safety. Written by Seth, this well-crafted book provides clear explanations and detailed instructions, making it suitable for both beginners and experts. It covers various cybersecurity aspects and aims to equip readers with effective strategies to safeguard their networks. However, some readers found the book lacking in crucial details and were disappointed to discover the need to purchase an additional firewall gadget. Despite this, the book offers valuable insights and practical knowledge. Be ready to invest some time and money in implementing the security model it proposes.
Key Features
- Comprehensive guide for network security
- Clear explanations and instructions
Specifications
- Color: Multicolor
- Dimension: 7.00Lx0.54Wx9.25H
Pros
- Well-written with clear explanations
- Provides valuable insights and practical knowledge
Cons
- Lacks crucial details in some areas
- Requires additional purchase of a firewall gadget
For those seeking to bolster their network security, ‘Cybersecurity for Small Networks: A Guide for the Reasonably Paranoid’ offers valuable information and practical strategies. While criticisms about lacking details and the need for additional purchases are valid, the book still provides significant insights. Just be prepared to invest some time and money to fully implement its proposed security model. Grab a copy and enhance your network’s defenses against potential threats!
Overall Score: 9/10
RMF ISSO: Foundations (Guide) is a comprehensive book that provides valuable resources and information about the NIST Risk Management Framework (RMF) for cybersecurity professionals. The book is authored by Bruce Brown, a well-known expert in the field of information assurance, risk management, and compliance. With easy-to-understand language and clear explanations, this book serves as a perfect guide for beginners as well as experienced IT security practitioners. It covers the roles and responsibilities of an ISSO (Information System Security Officer) and delves into the steps and process involved in the NIST RMF. The book is highly recommended for those looking to gain a deeper understanding of the RMF and ensure compliance with regulatory requirements.
Key Features
- Comprehensive guide to NIST Risk Management Framework (RMF)
- Easy-to-understand language and clear explanations
- Covers roles and responsibilities of an ISSO
- Provides in-depth information on steps and process of RMF
- Valuable resource for beginners and experienced professionals
Specifications
- N/A
Pros
- In-depth coverage of RMF and ISSO responsibilities
- Easy-to-read with great examples for better understanding
- Author has extensive experience in the field
- Provides foundational knowledge at an affordable price
Cons
- Limited specifications
- No customer reviews available
RMF ISSO: Foundations (Guide) is an excellent resource for cybersecurity professionals seeking to understand and implement the NIST Risk Management Framework accurately. With its clear explanations and easy-to-follow format, the book provides a comprehensive overview of the RMF steps and the roles and responsibilities of an ISSO. Bruce Brown’s expertise shines through in this valuable guide, making it an essential companion for both beginners and experienced professionals. While the lack of specifications and customer reviews is a minor drawback, the book’s content outweighs these limitations. Overall, RMF ISSO: Foundations (Guide) is a must-have for individuals looking to enhance their knowledge of cybersecurity and ensure compliance with regulatory requirements.
Overall Score: 8.6/10
Cybersecurity (The MIT Press Essential Knowledge series) is a comprehensive book that provides an introduction to the field of cybersecurity. Written by experts from MIT Press, it offers valuable insights into the latest jargon and terms in the industry, making it ideal for both beginners and professionals. With this book, readers can stay informed about the rapidly evolving world of cybersecurity. The black-colored book has dimensions of 5.06Lx0.47Wx7.06H, making it easily portable. It has received a customer rating of 4.4/5, indicating its popularity and favorable reception from readers.
Key Features
Specifications
- Color: Black
- Dimension: 5.06Lx0.47Wx7.06H
Pros
Cons
Cybersecurity (The MIT Press Essential Knowledge series) is a must-read for anyone interested in the field of cybersecurity. It provides a comprehensive introduction and keeps the readers informed about the latest terms and developments. With its concise and accessible writing style, it is suitable for both beginners and professionals. The glossary of terms provided by MIT Press is particularly helpful for those new to the field. Overall, this book is highly recommended for anyone looking to expand their knowledge and stay up to date with the ever-evolving world of cybersecurity.
Overall Score: 9/10
RMF ISSO: NIST 800-53 Controls is an excellent book that simplifies the NIST 800 risk management framework necessary for security assessment. The author, Bruce, breaks down every stage of the RMF process, making it easy to understand and apply. Whether you're studying for the CAP certification or aiming to become an ISSO, this book provides a comprehensive understanding of the controls and processes involved. It focuses on the most important controls in the control families, removing the barrier of reading through each 800 framework. With clear explanations, this book is essential for anyone in the field of cybersecurity and security control assessment.
Key Features
- Simplifies the NIST 800 risk management framework
- Breaks down each stage of the RMF process
- Focuses on the most important controls in the control families
Specifications
- N/A
Pros
- Clear and digestible explanations
- Comprehensive overview of controls and processes
- Useful for studying CAP certification and becoming an ISSO
Cons
- No specific specifications provided
RMF ISSO: NIST 800-53 Controls is an essential book for anyone working in cybersecurity or security control assessment. Bruce’s ability to simplify complex topics and provide a comprehensive overview of the RMF process is commendable. The book’s focus on the most important controls in the control families makes it a valuable resource. Although it lacks specific specifications, the clear and digestible explanations make up for it. Whether you’re a seasoned professional or new to the field, this book will enhance your understanding and help you excel in your role as an ISSO.
Overall Score: 8/10
Practical Cybersecurity Architecture is a comprehensive guide for cybersecurity architects. It covers all the essential components of creating and implementing robust designs for secure architecture. The book goes beyond the basics and discusses soft issues like finding a champion within an organization and speaking the language of business. It provides valuable references and methodologies for security professionals, making it a must-have in the field of cybersecurity. The conversational tone of the book makes it easy to read and digest the information. While it covers the concepts, standards, and frameworks, it also includes relatable examples and quotations to engage readers. With its practical approach and instructional guidance, Practical Cybersecurity Architecture is an indispensable resource in the cybersecurity industry.
Key Features
- Comprehensive guide for cybersecurity architects
- Discusses soft issues and relatable examples
- Includes references, methodologies, and standards
- Conversational tone for easy reading and understanding
Specifications
- Dimension: 7.50Lx0.95Wx9.25H
Pros
- Valuable resource for practitioners and would-be practitioners
- Instructive, intriguing, and helpful methodologies
- Conversational tone makes the information more digestible
- Practical approach with tips and guidance for application
- Includes relatable examples and useful quotes
Cons
- Could benefit from better editing and proofreading
- Lacks serious, in-depth coverage of security architecture
- May contain unnecessary repetition and overlaps
- Frameworks referenced are not explained or organized well
- Chapters can be long and may lose important points
Practical Cybersecurity Architecture is an indispensable resource in the field of cybersecurity. It covers all the essential components of creating and implementing secure designs, while also addressing soft issues and providing practical guidance. The conversational tone and relatable examples make it an engaging read for professionals in the industry. Although there are some areas for improvement, such as editing and in-depth coverage, the book offers valuable references, methodologies, and standards that can benefit both novice and experienced practitioners. Overall, Practical Cybersecurity Architecture is a recommended read for anyone looking to enhance their understanding and implementation of cybersecurity architecture.
Overall Score: 7/10
Cybersecurity: An Essential Guide to Computer and Cyber Security for Beginners is a comprehensive book that covers various aspects of cybersecurity. It offers an introduction to ethical hacking, risk assessment, social engineering, attack and defense strategies, and cyberwarfare. The book is well-written and easy to comprehend, making it suitable for beginners. It provides valuable information on cybersecurity and computer topics, although some readers expected a deeper analysis. The author uses real-life examples and a touch of humor to explain cybersecurity concepts. With a customer rating of 4.4/5, the book is highly recommended for those looking to gain a basic understanding of cybersecurity.
Key Features
Specifications
- Dimension: 6.00Lx0.29Wx9.00H
Pros
- Simplified and easy to understand
- Provides valuable information on cybersecurity
- Uses real-life examples and humor to explain concepts
- Suitable for beginners
Cons
- Some readers expected a deeper analysis
- Does not cover all necessary beginner material
- Glossary terms not always defined in text
Cybersecurity: An Essential Guide to Computer and Cyber Security for Beginners is a great starting point for those new to cybersecurity. While it may not delve deep into certain topics, it offers valuable information and a clear understanding of cybersecurity concepts. The book’s simplicity and use of real-life examples make it an enjoyable read. However, some readers felt that it lacked in-depth analysis and coverage of all necessary beginner material. Overall, if you’re looking to gain a basic understanding of cybersecurity and its various aspects, this book is highly recommended.
Buyer's Guide: Cybersecurity Books
In the digital age, ensuring the security of our information and systems has become more crucial than ever. To navigate the complex world of cybersecurity, it is essential to stay informed and well-equipped with the right knowledge. Cybersecurity books offer a wealth of information that can help both beginners and experts understand the intricacies of this rapidly evolving field. In this buyer's guide, we present a curated list of cybersecurity books to help you enhance your knowledge and protect yourself in the digital realm.
Understanding Cybersecurity
- "Cybersecurity for Beginners"
- Author: Raef Meeuwisse
- An introductory book that provides a comprehensive overview of cybersecurity concepts, threats, and best practices.
- Suitable for individuals with little to no cybersecurity knowledge.
- Covers essential topics such as cryptography, social engineering, and risk management.
- "The Cybersecurity Canon: Must-Read Books"
- Editors: Allen M. McLean, Winn Schwartau
- A collection of books that have been deemed "must-reads" by cybersecurity professionals.
- Offers a diverse range of perspectives on cybersecurity, providing a holistic understanding of the field.
- Includes classics like "The Cuckoo's Egg" by Clifford Stoll and "The Art of Deception" by Kevin Mitnick.
- "Cybersecurity: The Beginner's Guide"
- Author: Dr. Erdal Ozkaya
- Provides an easy-to-follow introduction to cybersecurity, covering foundational concepts and practical advice.
- Offers real-life examples and case studies to illustrate key concepts.
- Suitable for beginners seeking a comprehensive understanding of cybersecurity principles.
Specialized Topics in Cybersecurity
- "Hacking: The Art of Exploitation"
- Author: Jon Erickson
- Explores the fundamentals of hacking and the techniques used by hackers.
- Covers topics such as buffer overflows, network hacking, and cryptography.
- Key resource for individuals interested in offensive security and understanding hacker mindset.
- "Digital Forensics and Incident Response"
- Authors: Gerard Johansen, Kevin G. Manson, Andrei Miroshnikov
- Focuses on the techniques and methodologies used to investigate cyber incidents and conduct digital forensics.
- Provides insights into the tools and processes used by incident response teams.
- Offers practical guidance on gathering digital evidence and analyzing security breaches.
- "Network Security"
- Authors: Charlie Kaufman, Radia Perlman, Mike Speciner
- Explores the challenges and strategies involved in securing computer networks.
- Covers topics such as network attacks, firewalls, VPNs, and wireless security.
- An essential reference for network administrators and security professionals.
Developing Cybersecurity Skills
- "The Web Application Hacker's Handbook"
- Authors: Dafydd Stuttard, Marcus Pinto
- Focuses on web application security and penetration testing.
- Offers practical insights into identifying vulnerabilities and securing web applications.
- Includes real-world examples, tools, and methodologies used by ethical hackers.
- "Practical Malware Analysis"
- Authors: Michael Sikorski, Andrew Honig
- Provides a hands-on guide to analyzing and understanding malicious software (malware).
- Covers various techniques for reverse engineering malware samples.
- Suitable for individuals interested in malware analysis and incident response.
- "The Practice of Network Security Monitoring"
- Authors: Richard Bejtlich, Brian Carrier
- Explores Network Security Monitoring (NSM) as a proactive defense strategy.
- Offers insights into detecting and responding to network security incidents.
- Provides real-world use cases and practical advice for building effective NSM capabilities.
Frequently Asked Questions about 9 Amazing Cybersecurity Books for 2023
Consider your existing knowledge and desired level of expertise. If you are a beginner, start with introductory books. For specialized topics, choose books that align with your interests or professional goals.
While some books cater to beginners, having a basic understanding of computer networks and information technology would be beneficial.
Yes, cybersecurity books provide valuable insights and knowledge that can contribute to your professional development. However, practical experience and practical training are equally important.
Yes, there’s a wealth of free resources available, such as online courses, tutorials, and blogs. However, cybersecurity books offer a more structured and in-depth approach to learning.
Cybersecurity is a rapidly evolving field, so it is recommended to stay updated by reading new books every few years. However, keeping up with industry news and following reputable online sources can also complement your knowledge.