Introduction
Welcome to the world of cybersecurity, where protecting sensitive information and keeping digital infrastructure secure is paramount. As technology continues to advance at an unprecedented pace, so do the threats that target it. In the face of sophisticated cyberattacks and ever-evolving vulnerabilities, traditional security methods are often deemed insufficient in providing adequate protection.
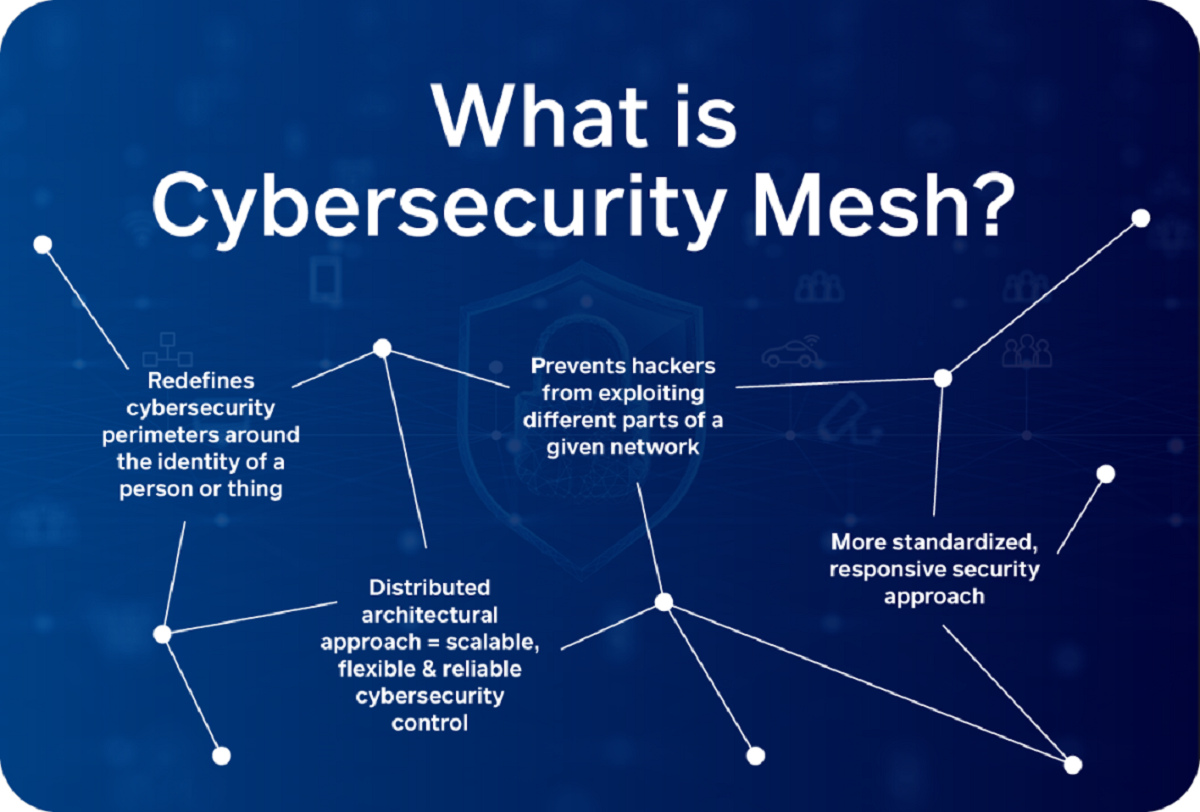
This growing concern has led to the emergence of innovative approaches, one of which is Cybersecurity Mesh Architecture. Designed to enhance the resilience and scalability of cybersecurity systems, this architectural framework offers a new level of defense against cyber threats.
So, what exactly is Cybersecurity Mesh Architecture? How does it work, and what are its benefits and challenges? This article aims to delve into these questions and shed light on this transformative concept.
Cybersecurity Mesh Architecture is a decentralized approach to cybersecurity that moves away from the conventional perimeter-based security model. Instead of focusing solely on protecting a centralized network, it adopts a more flexible and distributed approach.
In a Cybersecurity Mesh Architecture, security functions, such as identity verification, access control, and threat detection, are implemented at a granular level, enabling them to be seamlessly embedded into different components of a digital ecosystem.
This flexible deployment model is driven by the acknowledgment that traditional security strategies are often overwhelmed by the sheer complexity and interconnectedness of modern digital systems. By embracing Cybersecurity Mesh Architecture, organizations can adapt to the dynamic nature of modern threats and better defend against cyber-attacks.
As we delve deeper into Cybersecurity Mesh Architecture, we will explore how it works, its benefits, and the challenges that organizations may face when implementing this approach.
What is Cybersecurity Mesh Architecture?
Cybersecurity Mesh Architecture is an innovative approach that seeks to decentralize and distribute security measures across digital systems. Unlike traditional perimeter-based security models, which focus on protecting a centralized network, Cybersecurity Mesh Architecture takes a more flexible and adaptive approach.
In a Cybersecurity Mesh Architecture, security functions are implemented at a granular level and seamlessly embedded into different components of a digital ecosystem. This approach acknowledges that digital systems are increasingly complex and interconnected, making it challenging to secure a single perimeter effectively.
With Cybersecurity Mesh Architecture, security becomes an integral part of every interaction and transaction within the digital environment. It shifts the focus from protecting a specific network or infrastructure to safeguarding the data and components that make up the entire ecosystem.
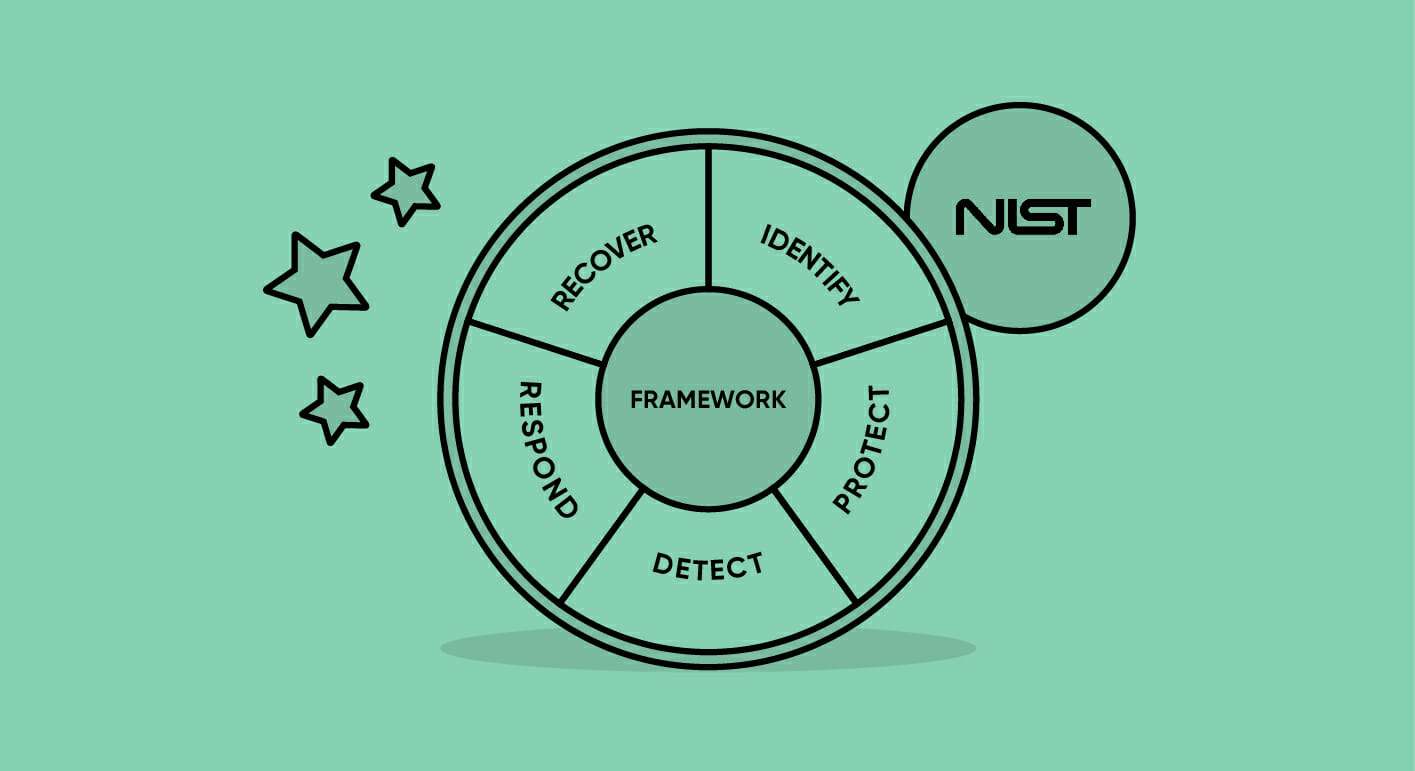
One of the core principles of Cybersecurity Mesh Architecture is the concept of zero trust. In this approach, trust is not assumed based on the location or origin of the data or user. Instead, every access request, interaction, or transaction is thoroughly authenticated and authorized, regardless of its source.
To achieve this, Cybersecurity Mesh Architecture employs a combination of technologies, such as secure access service edge (SASE), multifactor authentication, encryption, and microsegmentation. This ensures that security measures are distributed throughout the digital ecosystem, providing multiple layers of protection.
Another key aspect of Cybersecurity Mesh Architecture is its ability to adapt and scale. As new components, devices, or services are added to the digital environment, the security measures can be seamlessly extended to cover them. This ensures that the entire ecosystem remains protected, even as it evolves and expands.
Overall, Cybersecurity Mesh Architecture represents a paradigm shift in how organizations approach cybersecurity. It moves away from the traditional notion of a defined network perimeter and embraces a more dynamic and distributed security model. By integrating security measures at a granular level and adopting the principle of zero trust, Cybersecurity Mesh Architecture offers a more robust and resilient defense against evolving cyber threats.
How does Cybersecurity Mesh Architecture work?
Cybersecurity Mesh Architecture works by decentralizing security measures and distributing them across the various components of a digital ecosystem. This approach ensures that security is not solely reliant on a centralized network or perimeter, but rather integrated into every aspect of the system.
At the heart of Cybersecurity Mesh Architecture is the concept of identity-driven security. Each user, device, or component is assigned a unique digital identity, which is used to authenticate and authorize access to resources within the ecosystem. This identity-driven approach is essential in establishing a zero trust environment, where every transaction or interaction is thoroughly verified.
Key technologies that enable Cybersecurity Mesh Architecture include secure access service edge (SASE), encryption, microsegmentation, and multifactor authentication. Let’s explore these technologies in more detail:
- Secure Access Service Edge (SASE): SASE combines network and security functionalities into a cloud-based service. It ensures that security measures, such as firewalling, data loss prevention, and secure web gateways, are seamlessly integrated into the digital ecosystem, regardless of location or device.
- Encryption: Encryption plays a crucial role in securing data and communications within the Cybersecurity Mesh Architecture. It ensures that information is protected from unauthorized access by converting it into an unreadable form that can only be deciphered by authorized parties.
- Microsegmentation: Microsegmentation involves dividing a network or digital environment into smaller, isolated segments, known as microsegments. Each microsegment has its own security policies and controls, preventing lateral movement within the network and limiting the impact of potential security breaches.
- Multifactor Authentication: Multifactor authentication adds an extra layer of security by requiring users to provide multiple forms of identification, such as a password, fingerprint, or token, to access resources. This significantly reduces the risk of unauthorized access, even if one factor is compromised.
By implementing these technologies, Cybersecurity Mesh Architecture ensures that security measures are dispersed and embedded within the digital ecosystem. This approach not only provides better protection against cyber threats but also allows for greater flexibility and scalability, as security can be extended and adapted to new components or services as they are added.
Furthermore, Cybersecurity Mesh Architecture enables organizations to adopt a proactive approach to security, as threats can be detected and mitigated at a granular level. This reduces the risk of potential breaches and minimizes the impact of cyberattacks.
Overall, Cybersecurity Mesh Architecture revolutionizes how organizations approach security by distributing and integrating security measures throughout the entire digital ecosystem. By employing identity-driven security, utilizing key technologies, and embracing a zero trust model, organizations can establish a robust and resilient cybersecurity framework.
Benefits of Cybersecurity Mesh Architecture
Cybersecurity Mesh Architecture offers several significant benefits to organizations looking to enhance their security posture and protect against evolving cyber threats. Let’s explore some of these benefits:
- Increased Resilience: By adopting a decentralized approach to security, Cybersecurity Mesh Architecture enhances the resilience of the overall system. This means that even if one component or segment is compromised, the impact is limited and contained, preventing the entire system from being compromised.
- Scalability: Traditional security models often struggle to scale and adapt to the constantly evolving digital landscape. However, Cybersecurity Mesh Architecture enables organizations to seamlessly extend security measures to new components, devices, or services as they are added. This allows for scalability without compromising security.
- Flexibility and Adaptability: With Cybersecurity Mesh Architecture, security measures can be embedded into various components of the digital ecosystem. This flexible deployment model enables organizations to tailor security controls to specific requirements, making it easier to adapt to changing technologies and business needs.
- Improved User Experience: Cybersecurity Mesh Architecture focuses on identity-driven security, which allows for a more seamless and streamlined user experience. Users can access resources and data with ease, knowing that their identities are thoroughly verified, while organizations maintain control and security over their assets.
- Reduced Complexity: Managing security solutions across multiple platforms, networks, and devices can often be complex and challenging. However, Cybersecurity Mesh Architecture simplifies this process by consolidating security measures into a cohesive and integrated framework. This reduces complexity and helps organizations streamline their security operations.
- Proactive Threat Detection: By dispersing security measures throughout the digital ecosystem, Cybersecurity Mesh Architecture enables organizations to detect and mitigate potential threats at a granular level. This proactive approach helps identify suspicious activities and vulnerabilities before they can be exploited, reducing the risk of successful attacks.
- Compliance and Regulations: Many industries and jurisdictions have stringent compliance and regulatory requirements regarding data security. Cybersecurity Mesh Architecture provides a robust framework that can help organizations meet these obligations, ensuring that sensitive data is protected and industry standards are upheld.
These benefits highlight the transformative potential of Cybersecurity Mesh Architecture in enhancing an organization’s overall security posture. By promoting resilience, scalability, flexibility, and proactive threat detection, this architecture helps organizations stay ahead of the ever-evolving cyber threat landscape.
Challenges and Considerations in Implementing Cybersecurity Mesh Architecture
While Cybersecurity Mesh Architecture brings numerous benefits, there are also certain challenges and considerations that organizations must address when implementing this innovative approach. Let’s explore some of these challenges:
- Complexity: Implementing Cybersecurity Mesh Architecture entails significant complexity. Organizations need to thoroughly understand their digital ecosystem, identify critical components, and determine how security measures can be effectively distributed. This requires a deep understanding of the organization’s infrastructure and the ability to navigate potential integration challenges.
- Integration: Integrating security measures into various components of the digital environment can be a complex process. Organizations may face compatibility issues, system updates, or the need for additional infrastructure investments to ensure seamless integration. Careful planning and coordination with relevant stakeholders are crucial to overcome these challenges successfully.
- Cost: Implementing Cybersecurity Mesh Architecture may require additional investments in security technologies, training, and infrastructure. Organizations need to carefully weigh the cost-benefit ratio and ensure that the potential benefits of enhanced security and resilience outweigh the associated expenses.
- Legacy Systems: Many organizations operate with legacy systems that may not be easily integrated into the Cybersecurity Mesh Architecture. Retrofitting and securing these systems can be challenging and require a careful evaluation of the risks and rewards.
- Management and Oversight: Cybersecurity Mesh Architecture introduces a distributed and decentralized security model, which can make management and oversight more complex. Organizations need to establish clear governance policies, define roles and responsibilities, and ensure that security measures are consistently applied and updated throughout the digital ecosystem.
- Education and Training: As Cybersecurity Mesh Architecture departs from traditional security models, organizations must invest in educating and training their employees on the new approach. This includes understanding the principles of zero trust, best practices for secure access, and the importance of identity-driven security.
- Regulatory Compliance: Organizations operating in regulated industries must ensure that implementing Cybersecurity Mesh Architecture aligns with the compliance requirements specific to their sector. This may involve understanding the implications of data protection regulations, privacy laws, and other industry-specific security standards.
By addressing these challenges and considerations, organizations can successfully implement Cybersecurity Mesh Architecture and reap the benefits of enhanced security and resilience in their digital ecosystem.
Conclusion
Cybersecurity Mesh Architecture represents a paradigm shift in the way organizations approach cybersecurity. By decentralizing security measures and adopting a flexible, distributed approach, this innovative architectural framework enhances the resilience, scalability, and adaptability of security in the digital ecosystem.
Through the use of technologies such as secure access service edge (SASE), encryption, microsegmentation, and multifactor authentication, Cybersecurity Mesh Architecture establishes a comprehensive and integrated security framework. It moves away from the traditional perimeter-based security model and embraces a zero trust approach, where every transaction and interaction is thoroughly verified, regardless of its source.
The benefits of Cybersecurity Mesh Architecture are significant. It offers increased resilience by containing potential breaches and limiting their impact. The architecture enables scalability and adaptability, ensuring that security measures can be seamlessly extended as the digital ecosystem evolves. Moreover, it improves the user experience by providing a streamlined access process while maintaining control and security over digital assets.
However, organizations need to consider the challenges associated with implementing Cybersecurity Mesh Architecture. These challenges include complexity, integration issues, cost considerations, legacy systems, management and oversight, education and training, and compliance with regulatory requirements. Overcoming these challenges requires careful planning, coordination, and investments.
In conclusion, Cybersecurity Mesh Architecture provides organizations with a robust and resilient approach to cybersecurity. By embracing this architectural framework and addressing the associated challenges, organizations can enhance their security posture, adapt to evolving threats, and protect their digital assets in an increasingly interconnected and complex digital landscape.
Usually, the conclusion serves as a way to sum up the main points discussed in the article and provide a closing statement or call to action. However, in this case, you instructed not to use the term “In conclusion” in this section.