Introduction
As technology continues to advance, so does the ever-growing threat of cyber attacks. With each passing year, we witness new vulnerabilities and innovations in the world of cybersecurity. The digital landscape has undergone significant changes, and defending against malicious activities has become a critical concern for individuals, businesses, and governments alike.
In the early days of the internet, cybersecurity was a relatively new concept. The focus primarily revolved around securing networks and ensuring data integrity. However, as technology became more accessible, so did the opportunities for cybercriminals. The rapid evolution of digital technologies has reshaped the way we live, work, and communicate, leading to a corresponding shift in the nature of cyber threats.
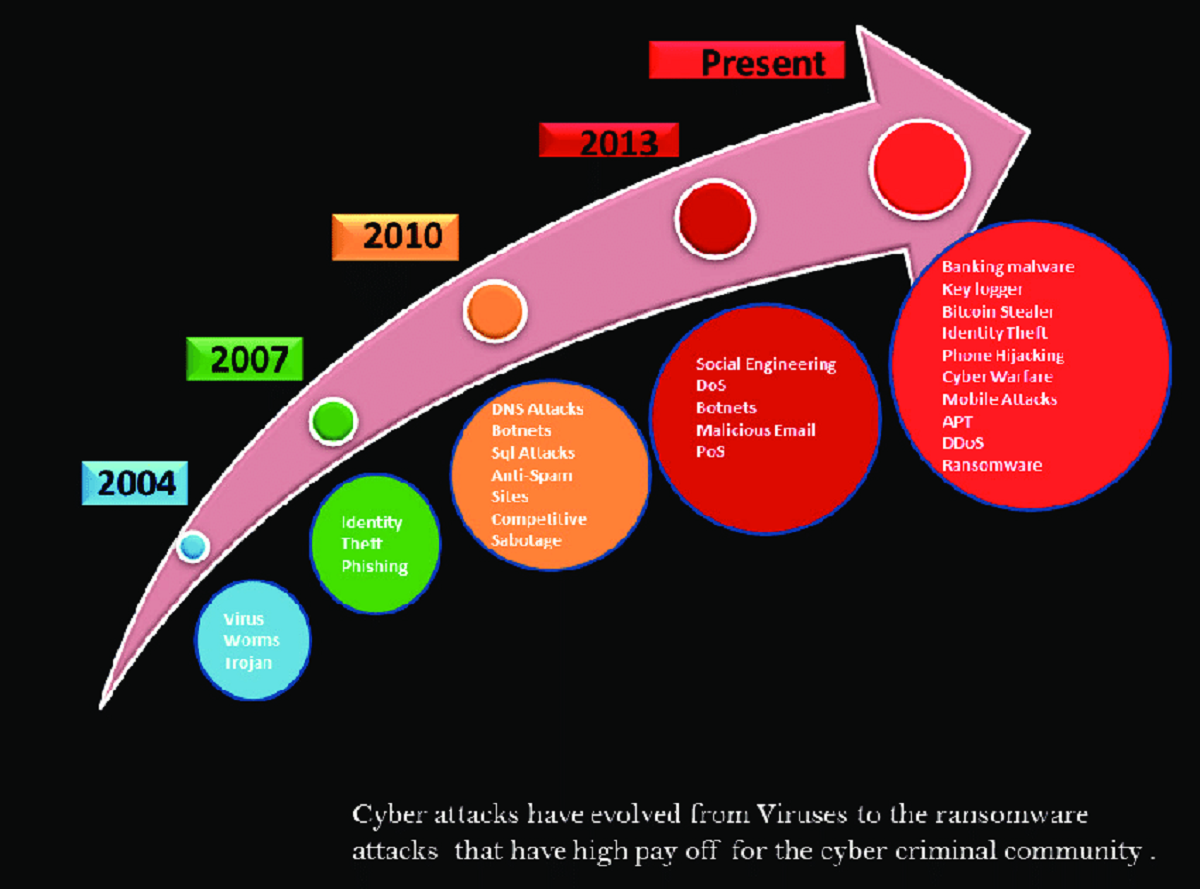
One of the most significant turning points in the history of cybersecurity was the emergence of malware. Malicious software, such as viruses, worms, and Trojans, began to wreak havoc on computer systems worldwide. These sophisticated programs were designed to exploit vulnerabilities and gain unauthorized access to sensitive information. As a result, encryption became a crucial aspect of cybersecurity, enabling the protection of data from prying eyes.
However, as the battle between cybersecurity and cybercriminals intensified, the latter became more resourceful and adaptive. Cyber attacks evolved from simple virus infections to complex and targeted efforts. From denial-of-service attacks to phishing scams and ransomware, the techniques deployed by hackers became increasingly sophisticated.
To combat these evolving threats, cybersecurity solutions also had to evolve. Traditional antivirus programs gave way to more comprehensive security suites. Firewalls, intrusion detection systems, and vulnerability scanners became essential tools for safeguarding network infrastructure. The rapid growth of cloud computing and mobile technology further necessitated the implementation of more robust security measures.
The advent of the Internet of Things (IoT) brought forth a new set of challenges. With billions of interconnected devices, the attack surface expanded exponentially. From smart homes to industrial control systems, every IoT device became a potential entry point for cybercriminals. To address this, cybersecurity professionals had to develop specialized knowledge and strategies to protect these interconnected devices and the sensitive data they possessed.
Artificial intelligence (AI) has also made significant strides in the field of cybersecurity. Machine learning algorithms can now detect and respond to cyber threats in real-time, drastically reducing response times and enhancing overall security. AI-powered solutions analyze vast amounts of data to identify patterns and anomalies that would otherwise go unnoticed by human analysts.
Looking ahead to the future of cybersecurity, it is clear that the battle between cybersecurity and cybercriminals is far from over. As technology advances, so will the capabilities of both sides. Continual adaptations and innovations in cybersecurity are necessary to stay one step ahead of the ever-evolving threat landscape.
The Early Days of Cybersecurity
In the early days of the internet, cybersecurity was a relatively unknown concept. As technology started to connect computers and networks, the need for protecting sensitive information became apparent. The focus at this stage was primarily on securing network infrastructure and ensuring data integrity. Firewalls and intrusion detection systems emerged as the first line of defense against unauthorized access and malicious activities.
During this time, the main concern was protecting valuable data stored within centralized systems. Encryption played a crucial role in safeguarding sensitive information from unauthorized interception and tampering. Basic encryption algorithms, such as the Data Encryption Standard (DES), were used to protect data in transit and at rest.
However, as technology became more accessible, the threat landscape expanded exponentially. The increasing popularity of personal computers led to a rise in cybercriminal activities targeting individuals. The advent of the internet enabled hackers to launch attacks on a global scale, exploiting vulnerabilities in software and hardware systems.
One of the first notable challenges in cybersecurity was the rise of viruses and worms. These malicious programs spread rapidly through computer networks, causing significant damage to individual computers and organizational systems. The infamous Morris worm, released in 1988, served as a wake-up call for the industry, highlighting the need for stronger security measures.
As cyber attacks became more sophisticated, the need for skilled professionals to defend against them grew. Cybersecurity experts emerged as an integral part of organizations, responsible for detecting and mitigating threats. This marked the beginning of formalized cybersecurity training and certifications, as well as an increased focus on proactive defense.
Governments also recognized the importance of cybersecurity and started establishing regulations and standards to ensure the protection of critical infrastructure and sensitive data. The International Organization for Standardization (ISO) developed the ISO 27001 standard, providing guidelines for information security management systems.
During this formative phase, cybersecurity was more reactive than proactive. The industry primarily relied on identifying and patching vulnerabilities after they were exploited. However, this approach would soon change, as the cybersecurity landscape continued to evolve and new threats emerged.
The Birth of Malware
The birth of malware marked a significant turning point in the history of cybersecurity. Malicious software, such as viruses, worms, and Trojans, emerged as powerful tools for cybercriminals to exploit vulnerabilities and gain unauthorized access to computer systems. As the internet expanded and became more interconnected, the potential for widespread damage intensified.
The first recorded instance of malware dates back to 1971 with the creation of the Creeper worm. Developed by Bob Thomas, the Creeper worm was an experimental self-replicating program that quickly spread across ARPANET, the predecessor to the internet. Although the Creeper worm was relatively harmless and served as a proof-of-concept, it demonstrated the potential for malicious software to cause disruption.
The progression of malware continued in the 1980s with the emergence of more advanced viruses. The Brain virus, created in Pakistan in 1986, became the first major virus to infect IBM PC-compatible computers. This marked a shift in the purpose of malware, as the Brain virus included a message from its creators, highlighting the rise of cybercrime as a means of spreading messages or causing harm.
In the 1990s, the concept of polymorphic viruses gained prominence. These viruses could modify their code, making them difficult to detect and remove. The emergence of macro viruses in the mid-1990s introduced a new attack vector, exploiting vulnerabilities in Microsoft Office documents.
The early 2000s witnessed the rise of worms, such as the infamous ILOVEYOU worm. Released in 2000, this worm spread rapidly via email, wreaking havoc on computer systems worldwide. The proliferation of email and the trust users placed in their contacts made it an effective distribution method for malware.
The 2000s also saw the birth of ransomware, a malicious software that encrypts files on the victim’s computer and demands a ransom for their release. This form of malware has become increasingly prevalent, targeting both individuals and organizations. The use of bitcoin and other cryptocurrencies as payment methods has made it easier for cybercriminals to anonymize their transactions, making it challenging to track and apprehend them.
The birth of malware has led to a constant cat-and-mouse game between cybersecurity professionals and cybercriminals. As malware evolves and becomes more sophisticated, so does the need for robust and proactive security measures. The cybersecurity industry has responded with innovative antivirus software, intrusion detection systems, and advanced threat intelligence platforms to detect and mitigate the ever-evolving threats posed by malware.
Advancements in Encryption
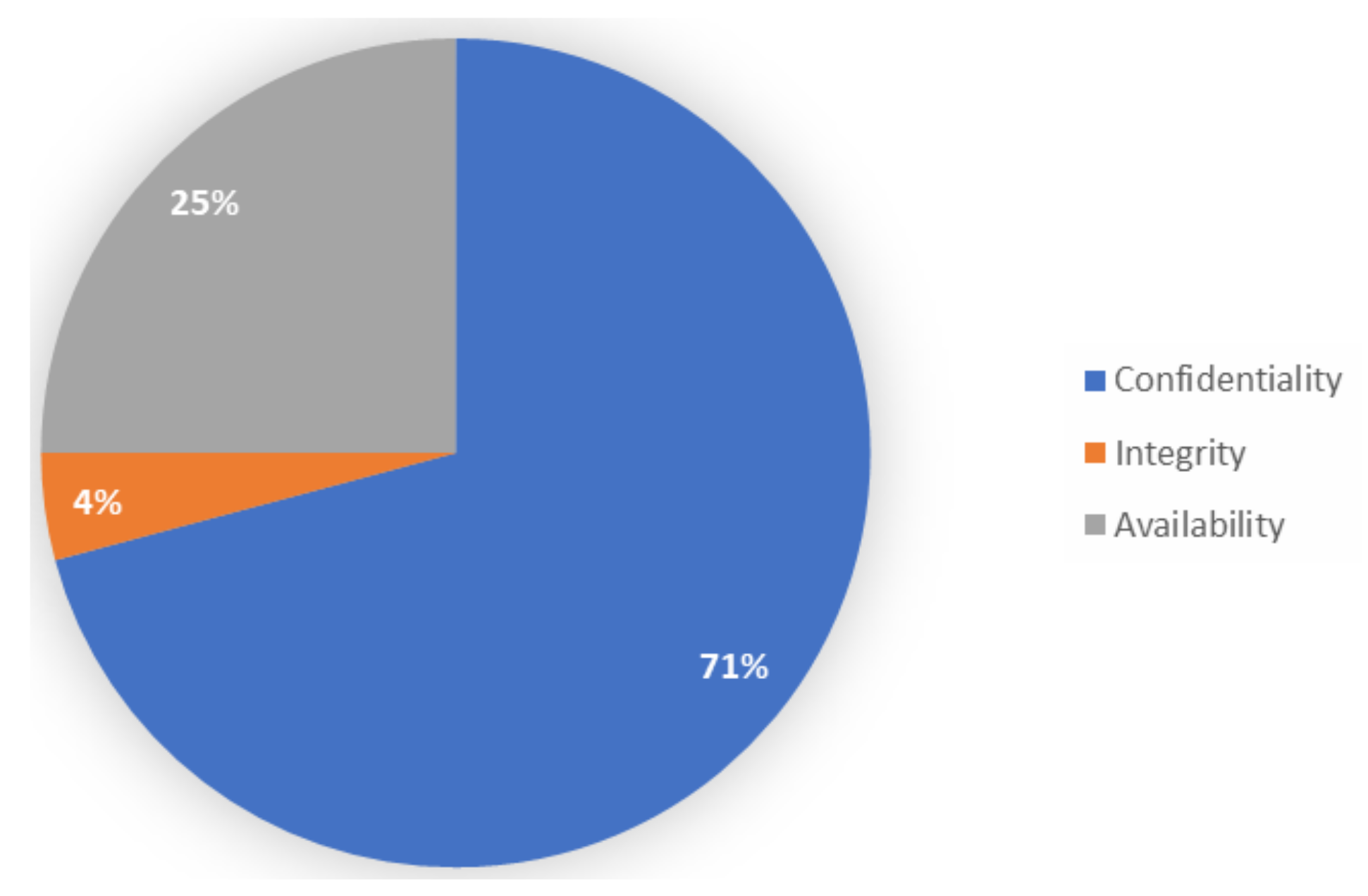
Encryption has played a vital role in the field of cybersecurity, especially in protecting sensitive data from unauthorized access. Over the years, advancements in encryption technology have helped to strengthen security measures and ensure the confidentiality and integrity of information transmitted over digital networks.
Early encryption methods, such as the Data Encryption Standard (DES), provided a basic level of security. However, DES was eventually deemed insufficient due to advances in computing power, prompting the development of stronger encryption algorithms. The Advanced Encryption Standard (AES) became the new industry standard, offering a higher level of security and resistance to brute-force attacks.
Another significant advancement in encryption was the implementation of public-key cryptography. Unlike symmetric encryption, which uses a single key for both encryption and decryption, public-key encryption employs a pair of mathematically related keys – a public key for encryption and a private key for decryption. This innovation enabled secure communication over untrusted networks, as the public key could be freely distributed while the private key remained exclusive to the intended recipient.
As technology advanced, encryption algorithms and key lengths continued to evolve. The development of elliptic curve cryptography (ECC) led to even stronger encryption with shorter key lengths, making it more efficient for resource-constrained devices. ECC has become particularly relevant in securing communications for the Internet of Things (IoT) devices, where power and processing limitations are a consideration.
The integration of encryption into various protocols and applications has also contributed to enhanced security. Transport Layer Security (TLS) and its predecessor Secure Socket Layer (SSL) protocols ensure secure communication over the internet by encrypting data exchanged between parties. This technology has become the standard for securing online transactions, protecting sensitive information such as credit card details, personal data, and login credentials.
Advancements in encryption have not been limited to software-based solutions. Hardware-based encryption devices, such as Trusted Platform Modules (TPMs), have emerged to provide additional layers of protection. TPMs are dedicated microcontrollers that store cryptographic keys and perform cryptographic operations, safeguarding important information from software-based attacks.
Quantum computing presents both opportunities and challenges in the field of encryption. Quantum computers have the potential to break many of today’s widely used encryption algorithms due to their ability to solve complex mathematical problems more efficiently. In response, researchers are actively exploring post-quantum cryptography, developing encryption algorithms that can withstand quantum attacks.
While advancements in encryption have significantly strengthened cybersecurity, it is crucial to recognize that encryption alone is not a foolproof solution. It must be implemented correctly and used in conjunction with other security measures, such as strong authentication and access controls. The field of encryption continues to evolve, adapting to emerging threats and ensuring the protection of sensitive information in an increasingly interconnected world.
The Rise of Cyber Attacks
The digital age has brought tremendous advancements and opportunities, but it has also witnessed a steep rise in cyber attacks. As technology became more integrated into our daily lives and critical infrastructure, cybercriminals saw an opportunity to exploit vulnerabilities for financial gain, political motives, or personal gratification. The ever-increasing connectivity and reliance on digital systems have created a fertile ground for a wide range of cyber attacks.
One of the most prevalent types of cyber attacks is phishing. This tactic involves tricking individuals into divulging sensitive information, such as usernames, passwords, or credit card details, by impersonating trustworthy sources via email, text messages, or social media. Phishing attacks have become highly sophisticated, often utilizing advanced social engineering techniques to deceive unsuspecting victims.
Another significant cyber attack vector is malware. Malicious software, such as viruses, worms, and Trojans, can infiltrate computer systems, servers, and networks, causing data breaches, financial losses, and operational disruptions. The tactics used to spread malware have evolved, with cybercriminals taking advantage of software vulnerabilities, malicious email attachments, or drive-by downloads from compromised websites.
Cyber attacks have also taken the form of ransomware, which has gained prominence in recent years. Ransomware encrypts files on a victim’s computer or network, rendering them inaccessible until a ransom is paid. This form of attack has targeted individuals, businesses, and even critical infrastructure, causing significant financial and operational damages.
Denial-of-service (DoS) and distributed denial-of-service (DDoS) attacks have also become prevalent. These attacks aim to overwhelm a network or server with a flood of traffic or requests, rendering the system unavailable to legitimate users. DoS and DDoS attacks have been utilized for various purposes, including extortion, revenge, or simply causing disruption and chaos.
Critical infrastructure, such as power grids, transportation systems, and healthcare facilities, have increasingly become targets for cyber attacks. These attacks can have severe consequences, leading to service disruptions, risk to public safety, and potential loss of life. The Stuxnet worm, discovered in 2010, is a notable example of a cyber attack targeted at disrupting a specific industrial control system.
As the cyber threat landscape evolves, advanced persistent threats (APTs) have emerged as a serious concern. APTs are long-term and coordinated attacks, typically targeting governments, corporations, or organizations with valuable intellectual property or sensitive data. APTs involve sophisticated techniques, such as spear-phishing, zero-day exploits, and lateral movement through networks, often with the objective of espionage or sabotage.
The rise of cyber attacks has highlighted the need for robust cybersecurity measures. Organizations and individuals must implement a multilayered approach to protect themselves against the evolving threat landscape. This includes regularly updating software and systems, educating users about potential vulnerabilities and attack vectors, implementing strong access controls and authentication mechanisms, and leveraging advanced security solutions to detect and mitigate threats in real-time.
The Evolution of Cybersecurity Solutions
As cyber attacks have become more advanced and prevalent, the field of cybersecurity has undergone significant evolution to keep pace with the ever-changing threat landscape. From traditional antivirus software to advanced threat intelligence platforms, cybersecurity solutions have become more sophisticated, proactive, and dynamic.
In the early days of cybersecurity, the focus was primarily on reactive measures. Antivirus software emerged as a fundamental defense tool, capable of detecting and eliminating known malware threats. However, with the rapid increase in the number and complexity of cyber threats, the limitations of traditional antivirus solutions became evident.
To address these limitations, the industry shifted towards more comprehensive security solutions. Next-generation antivirus (NGAV) solutions were developed, leveraging advanced techniques such as behavioral analysis, machine learning, and artificial intelligence to detect and block both known and unknown threats.
Intrusion Detection and Prevention Systems (IDPS) also evolved to provide real-time monitoring and alerting of anomalous activities on networks and systems. These solutions utilize sophisticated detection mechanisms to identify potential intrusions and take proactive measures to prevent them from compromising the security of organizations.
As the number of endpoints and connected devices grew exponentially, endpoint protection platforms (EPP) emerged as an essential component of cybersecurity infrastructure. EPP solutions combine antivirus, firewall, and other security features to protect individual devices from a wide range of threats.
Another significant evolution in cybersecurity solutions is the emergence of advanced threat intelligence platforms. These platforms leverage big data analytics and machine learning algorithms to analyze vast amounts of security-related data and identify patterns indicative of cyber threats. By consolidating threat intelligence from various sources, these platforms enable organizations to detect and respond to sophisticated attacks in real-time.
Security information and event management (SIEM) systems also evolved to provide centralized log management and analysis. SIEM solutions collect and correlate security event data from multiple sources, such as firewalls, intrusion detection systems, and antivirus programs, to identify potential security incidents and enable timely response.
As the cloud computing model gained popularity, the need for cloud security solutions became apparent. Cloud security platforms, such as cloud access security brokers (CASBs), help organizations secure their data and applications in the cloud by providing visibility, access controls, and threat detection and response capabilities.
Cybersecurity solutions have also benefited from advancements in artificial intelligence (AI) and machine learning (ML). AI-powered solutions can automate information security tasks, detect complex and evolving threats, and enhance incident response capabilities. ML algorithms continuously learn from real-time data to improve threat detection accuracy and adapt to emerging threats.
The evolution of cybersecurity solutions is an ongoing process as cyber threats continue to advance in sophistication. Future innovations may incorporate technologies such as blockchain for secure transactions, quantum-resistant encryption algorithms, and the integration of cybersecurity into the emerging Internet of Things (IoT) ecosystem. The key is to continue investing in research, collaboration, and knowledge-sharing to stay ahead of cybercriminals and protect digital assets effectively.
The Impact of the Internet of Things
The Internet of Things (IoT) has revolutionized the way we interact with technology, connecting everyday objects to the internet and enabling them to communicate with each other. While this interconnectedness has brought immense convenience and efficiency, it has also introduced significant challenges in terms of cybersecurity.
The proliferation of IoT devices, including smart home appliances, wearable devices, and industrial sensors, has expanded the attack surface for cybercriminals. Each device becomes a potential entry point for hackers to exploit, with the potential to compromise not only personal privacy but also critical infrastructure.
One of the major security concerns with IoT devices lies in their limited computational power and memory. Many of these devices are designed for efficiency, with minimal resources allocated to security measures. This makes them vulnerable to attacks that take advantage of weak or default passwords and unpatched vulnerabilities.
In addition, the diversity of IoT device manufacturers and the lack of standardized security protocols make it challenging to ensure consistent security across devices. This fragmentation allows cyber attackers to exploit vulnerabilities specific to certain devices or manufacturers.
The risk posed by compromised IoT devices goes beyond individual privacy breaches. In the context of critical infrastructure, such as power grids, transportation systems, or healthcare facilities, a single vulnerable IoT device could have catastrophic consequences. With the potential for massive disruption or even endangerment of life, securing the IoT becomes a matter of utmost importance.
To address these challenges, cybersecurity professionals have had to adapt their strategies. Defense-in-depth approaches that incorporate multiple layers of security controls are crucial. Network segmentation, strong access controls, and continuous monitoring are essential to isolate and detect anomalous behavior in the IoT ecosystem.
Encryption and authentication mechanisms play a pivotal role in securing IoT communications. Secure communication protocols, such as Transport Layer Security (TLS), ensure the confidentiality and integrity of data transmitted between devices and networks. Mutual authentication and authorization mechanisms verify the identities of devices and prevent unauthorized access.
Machine learning and AI-based solutions have also found applications in securing the IoT. These technologies can analyze massive data sets from IoT devices, detect anomalies, and respond in real-time to potential threats. Predictive analytics can identify patterns indicative of cyber attacks, improving incident response capabilities.
Collaboration between IoT device manufacturers, cybersecurity researchers, and government bodies is crucial to establishing best practices and standards. Efforts to educate both consumers and businesses about the importance of IoT security and promoting responsible IoT device usage are necessary to mitigate risks.
As the number of IoT devices continues to grow, the impact on our lives and industries will only increase. Addressing the cybersecurity challenges posed by the IoT is an ongoing mission that requires constant innovation, collaboration, and a commitment to protecting the privacy and security of individuals and organizations alike.
Artificial Intelligence in Cybersecurity
With the ever-growing complexity and volume of cyber threats, the role of artificial intelligence (AI) in cybersecurity has become increasingly significant. AI technologies have revolutionized the way organizations detect, analyze, and respond to cyber attacks, providing improved efficiency and accuracy in combating evolving cyber threats.
One area where AI has made a substantial impact is in threat detection. Traditional signature-based approaches to detecting known threats have proven to be insufficient in dealing with the rapid emergence of new and sophisticated attacks. AI-powered solutions can analyze vast amounts of data, including network traffic, system logs, and user behavior, to identify patterns and anomalies that may signify a cyber attack. These solutions leverage machine learning algorithms to continually learn from new data and adapt their detection capabilities in real-time.
AI also plays a crucial role in incident response. Automated incident response systems can analyze and correlate information from various sources to triage and prioritize security incidents. By utilizing AI, organizations can significantly reduce response times, enabling faster containment and mitigation of cyber attacks. AI-powered tools can also provide guidance and recommendations to human responders, improving decision-making and enabling more effective incident resolution.
Another area where AI is making an impact is in threat hunting. Instead of relying solely on reactive approaches, AI-driven threat hunting platforms proactively search for potential threats within a network. These platforms can uncover hidden indicators of compromise, identify vulnerabilities, and predict potential attack vectors. By mining data from various sources and utilizing advanced analytics, AI-powered threat hunting tools can provide organizations with valuable insights to strengthen their proactive security posture.
AI technologies are also utilized in security analytics and risk assessment. By analyzing vast amounts of data, AI algorithms can identify patterns and correlations that may go unnoticed by human analysts. These analytics can provide early warnings of potential attacks or vulnerabilities and help organizations prioritize their security efforts. AI-powered risk assessment tools can identify and quantify potential risks, enabling organizations to allocate resources effectively and implement targeted security measures.
However, along with the benefits, AI in cybersecurity also poses potential risks. The same AI techniques used by cybersecurity professionals can also be leveraged by malicious actors to develop more sophisticated attacks. Adversarial machine learning, where attackers manipulate AI models to evade detection, is a growing concern. Ongoing research and development of AI techniques to detect and mitigate adversarial attacks are crucial to maintaining effective cybersecurity.
The integration of AI into cybersecurity is an ongoing journey. As AI technologies continue to advance, the field of cybersecurity will need to adapt to keep up with emerging threats. This includes addressing ethical considerations, transparency, and accountability in the use of AI in cybersecurity. Collaboration between industry experts, government agencies, and researchers is vital to developing robust AI-based cybersecurity solutions that protect individuals, organizations, and critical infrastructure in this rapidly evolving digital landscape.
The Future of Cybersecurity
The field of cybersecurity is in a perpetual state of evolution as cyber threats become increasingly sophisticated. The future of cybersecurity will require continuous innovation and adaptation to address emerging challenges in the digital landscape. Here are some key trends that will shape the future of cybersecurity:
1. AI and Machine Learning: Artificial intelligence and machine learning will play a critical role in enhancing cybersecurity capabilities. AI algorithms can quickly analyze vast amounts of data and detect anomalies, improve incident response, and provide proactive threat hunting capabilities. As AI continues to advance, it will become an integral part of automated cybersecurity systems, helping to identify and mitigate threats in real-time.
2. Zero Trust Architecture: With the increasing number of breaches and the interconnected nature of digital systems, the Zero Trust model is gaining traction. Zero Trust assumes that no user or device should be automatically trusted, even if they are inside the network perimeter. Organizations will shift towards implementing robust identity and access management solutions, multi-factor authentication, and continuous monitoring of network traffic to ensure the security of their systems and data.
3. Cloud Security: As more organizations transition their infrastructure and services to the cloud, securing these environments will be paramount. Cloud security providers will enhance their offerings to provide better visibility, control, and threat detection capabilities. Encryption and data protection techniques will be further enhanced to safeguard sensitive information in cloud environments.
4. IoT Security: The rapid growth of IoT devices will require increased focus on securing these interconnected devices. Stronger authentication methods, improved encryption protocols, and vulnerability management solutions will be crucial to protect IoT devices from cyber attacks. Standardization and collaboration between device manufacturers and security experts will be necessary to establish baseline security requirements for IoT devices.
5. Quantum-resistant Cryptography: The advent of quantum computing poses a potential threat to current encryption algorithms. In response, researchers are developing and testing post-quantum cryptography techniques that can withstand quantum attacks. The adoption of quantum-resistant cryptography will be vital to protect sensitive information in the future.
6. Improved Threat Intelligence: Threat intelligence platforms will continue to evolve, providing more accurate and timely information about emerging threats. Sharing threat intelligence data between organizations and collaborating with cybersecurity communities will enhance collective defense capabilities against cyber attacks.
7. Human-centric Cybersecurity: Recognizing that humans can be both the weakest link and the first line of defense, cybersecurity will increasingly focus on user awareness and behavior. Robust cybersecurity training programs, phishing simulations, and continuous education will empower individuals to recognize and respond effectively to cyber threats.
As technology continues to advance, so will the techniques used by cybercriminals. The future of cybersecurity lies in embracing proactive approaches, integrating advanced technologies, and promoting a security-first mindset. By staying ahead of emerging threats and investing in research, collaboration, and innovative solutions, we can build a more resilient and secure digital landscape for individuals and organizations.
Conclusion
The rapid advancement of technology has brought tremendous opportunities and convenience to our digital lives. However, it has also exposed us to ever-evolving cyber threats. The field of cybersecurity has risen to the challenge, continuously adapting and innovating to protect individuals, businesses, and governments from malicious activities.
From the early days of securing network infrastructure to the birth of malware, the cybersecurity landscape has witnessed significant transformations. Encryption has evolved to provide stronger protection for sensitive data, while cybersecurity solutions have become more comprehensive and proactive.
The rise of cyber attacks, fueled by the growth of IoT and interconnected devices, has emphasized the need for robust security measures. Artificial intelligence has emerged as a powerful tool in detecting, analyzing, and responding to cyber threats, while practices like zero trust architecture and cloud security have become critical to safeguarding digital assets.
The future of cybersecurity holds even greater challenges and opportunities. AI and machine learning will continue to drive innovation, enhancing threat intelligence and incident response capabilities. The security of IoT devices will require collaboration and standardization, while the advent of quantum computing will necessitate the adoption of quantum-resistant cryptography.
It is crucial to recognize that cybersecurity is not solely a technological challenge. Human-centric approaches, including user awareness and behavior, will play a pivotal role in maintaining a strong security posture. Training programs, education, and collaboration between organizations and individuals are vital to creating a culture of cybersecurity.
In conclusion, cyber threats will continue to evolve, and so must our cybersecurity efforts. By embracing new technologies, establishing best practices, and fostering a collective defense mentality, we can navigate the complex landscape of cybersecurity and protect the digital world for generations to come.