Introduction
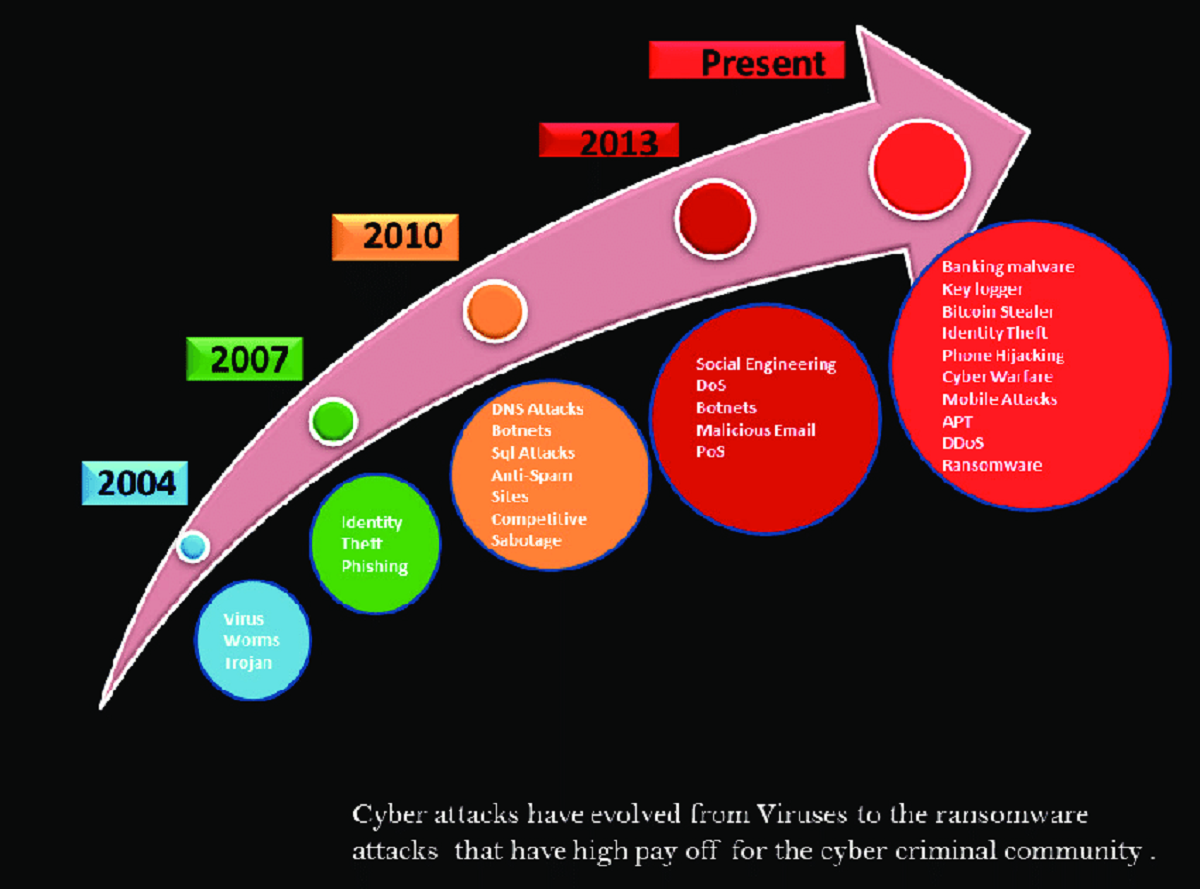
Cybersecurity attacks have become an increasingly prevalent threat in today’s digital landscape. With the advancement of technology and the proliferation of internet-connected devices, the risks associated with cyber-attacks have also increased. From individuals to small businesses to large corporations, no one is immune to the dangers posed by cybercriminals.
The impact of cybersecurity attacks can be devastating, leading to financial losses, reputation damage, and even legal consequences. As a result, it has become imperative for individuals and organizations alike to prioritize cybersecurity measures to protect sensitive information and maintain the integrity of their digital assets.
This article aims to explore the significance of cybersecurity and shed light on the various factors contributing to the rise in cybersecurity attacks. Additionally, we will delve into different types of cybersecurity attacks, their frequency, and the industries most affected by them. By understanding the threats we face in the digital world, we can equip ourselves with the knowledge needed to safeguard against malicious activities.
It is crucial to note that cybersecurity is a continuously evolving field, where attackers develop new techniques and defenders strive to stay one step ahead. Therefore, staying informed about the latest threats, adopting best practices, and implementing robust security measures are vital for protecting ourselves and our digital assets.
In the following sections, we will provide an in-depth analysis of the various types of cybersecurity attacks, including malware attacks, phishing attacks, ransomware attacks, distributed denial of service (DDoS) attacks, and social engineering attacks. We will also discuss steps that individuals and organizations can take to mitigate the risks associated with these attacks and enhance their overall cybersecurity posture.
The Importance of Cybersecurity
Cybersecurity plays a pivotal role in safeguarding sensitive and confidential information in today’s digitally interconnected world. It involves the protection of computer systems, networks, and data from unauthorized access, use, disclosure, disruption, modification, or destruction. The importance of cybersecurity cannot be overstated, and here’s why:
1. Protecting Personal Data: With the increasing reliance on technology, individuals store a vast amount of personal data online. This includes financial information, medical records, passwords, and social media profiles. Cybersecurity measures help prevent unauthorized access to these details and protect individuals from identity theft and other forms of cybercrime.
2. Safeguarding Business Information: Organizations, regardless of their size, collect and store sensitive business data, such as trade secrets, financial records, customer databases, and proprietary information. Cybersecurity measures are crucial in securing this data, ensuring business continuity, and safeguarding intellectual property.
3. Preserving Reputational Integrity: A cybersecurity breach can have severe implications for an organization’s reputation. News of a data breach can spread rapidly, leading to a loss of customer trust, potential legal consequences, and significant financial repercussions. Maintaining a robust cybersecurity framework helps protect an organization’s reputation and preserves stakeholder confidence.
4. Ensuring National Security: Cybersecurity is a critical component of national security. Malicious actors, including hacker groups and nation-states, can launch cyber-attacks on critical infrastructure, government systems, and military networks. Effective cybersecurity measures are essential for protecting national interests and maintaining the stability of the country’s infrastructure.
5. Avoiding Financial Losses: Cybersecurity incidents can result in significant financial losses for individuals and organizations. Expenses associated with mitigating the impacts of an attack, such as incident response, legal fees, data recovery, and regulatory fines, can be substantial. Investing in robust cybersecurity measures can help prevent such financial losses.
6. Complying with Regulatory Requirements: Many industries are subject to regulatory frameworks that require specific cybersecurity measures to protect sensitive information. Compliance with these regulations is essential for avoiding penalties and ensuring that customer data is adequately protected.
Overall, the importance of cybersecurity extends beyond individual and organizational levels. It encompasses the security of personal information, business operations, national security, reputation, financial stability, and regulatory compliance. By prioritizing cybersecurity and implementing effective measures, we can collectively contribute to a safer and more secure digital environment.
Factors Contributing to the Rise in Cybersecurity Attacks
The rise in cybersecurity attacks can be attributed to several factors that have amplified the risks and vulnerabilities in our digital landscape. Understanding these factors is crucial in developing effective strategies to mitigate the threats posed by cybercriminals. Here are some key factors contributing to the increase in cybersecurity attacks:
1. Technological Advancements: The rapid evolution of technology has brought about numerous benefits but also created new opportunities for cybercriminals. Advancements such as cloud computing, the Internet of Things (IoT), and artificial intelligence have expanded the attack surface and introduced complexities that can be exploited by cyber attackers.
2. Increased Connectivity: The proliferation of internet-connected devices has created an interconnected ecosystem where information flows seamlessly. While this connectivity enhances convenience and productivity, it also introduces vulnerabilities. More devices mean more potential entry points for cybercriminals to exploit.
3. Sophisticated Attack Techniques: Cybercriminals are constantly developing and refining their attack techniques. They utilize advanced tactics such as social engineering, ransomware, and zero-day exploits to exploit vulnerabilities in systems and manipulate human behavior for their advantage. As attackers become more sophisticated, staying one step ahead is crucial.
4. Lack of Awareness and Training: Many cybersecurity breaches occur due to human error, such as falling victim to phishing emails or using weak passwords. A lack of awareness and training leaves individuals and organizations vulnerable to cyber attacks. Educating users about common threats, best practices, and the importance of maintaining strong security measures is vital in combating these attacks.
5. Organized Cybercrime: Cybercriminals have evolved from individual hackers to organized cybercrime syndicates. These groups leverage their collective skills and resources to launch coordinated and highly sophisticated attacks. Their motives range from financial gain to political activism, making cybersecurity incidents increasingly complex.
6. Insider Threats: Insider threats, whether intentional or unintentional, pose a significant risk to organizations. Disgruntled employees, former employees, and contractors with access to sensitive information can abuse their privileges or inadvertently expose critical data, potentially leading to cybersecurity breaches.
7. Lack of Security Updates: Many cybersecurity attacks exploit known vulnerabilities in software and systems. Failing to apply security patches and updates promptly leaves systems susceptible to attacks. Regularly updating software and implementing a robust patch management process is essential for mitigating these risks.
8. Global Interconnectedness: The interconnectedness of our digital world means that an attack on one system can have far-reaching consequences. Cybercriminals can easily target individuals and organizations across borders, making it challenging to track and apprehend them. This global interconnectedness demands increased international cooperation and collaboration to combat cybercrime effectively.
Addressing these factors requires a multi-faceted approach, combining technological advancements, enhanced security measures, user awareness, and collaboration between stakeholders. By understanding the root causes of cybersecurity attacks, we can develop proactive strategies to defend against them and ensure a safer digital environment for individuals and businesses alike.
Types of Cybersecurity Attacks
Cybersecurity attacks come in various forms, each targeting different vulnerabilities and posing unique threats to individuals and organizations. Understanding the different types of cybersecurity attacks is crucial in implementing effective security measures. Here are some common types of cybersecurity attacks:
1. Malware Attacks: Malware, short for malicious software, is any software designed to harm or gain unauthorized access to a computer system. This includes viruses, worms, Trojans, ransomware, and spyware. Malware attacks can compromise data, disrupt operations, and provide unauthorized access to sensitive information.
2. Phishing Attacks: Phishing attacks involve deceptive tactics aimed at tricking individuals into revealing sensitive information, such as passwords, credit card numbers, or social security numbers. Attackers impersonate legitimate entities, often through email or text, to lure victims into clicking on malicious links or providing their confidential information.
3. Ransomware Attacks: Ransomware is a type of malware that encrypts a victim’s data and demands a ransom payment in exchange for the decryption key. These attacks can cripple businesses and individuals, causing financial losses, operational disruptions, and potential data breaches.
4. Distributed Denial of Service (DDoS) Attacks: DDoS attacks aim to overwhelm a network, server, or website with a flood of traffic, rendering it inaccessible to legitimate users. By overloading the targeted system’s resources, these attacks disrupt operations, cause downtime, and can be used as a distraction for other malicious activities.
5. Social Engineering Attacks: Social engineering attacks exploit human psychology to manipulate individuals into divulging sensitive information or performing actions that benefit the attacker. This can include impersonation, pretexting, baiting, or other similar techniques to gain unauthorized access to systems or data.
6. Insider Threats: Insider threats involve individuals with authorized access to systems, networks, or data intentionally or accidentally causing harm to an organization. This could be due to negligence, malicious intent, or manipulation by external actors. Insider threats can lead to data breaches, unauthorized access, or disruption of critical operations.
7. Zero-Day Exploits: Zero-day exploits target previously unknown vulnerabilities in software or systems. Attackers leverage these vulnerabilities before software developers or system administrators have an opportunity to patch or mitigate them. Zero-day exploits can cause significant damage as there may be no immediate defense against them.
8. Man-in-the-Middle (MitM) Attacks: MitM attacks intercept communication between two parties, allowing attackers to eavesdrop, manipulate, or inject malicious content. By impersonating legitimate entities, attackers can intercept sensitive information, such as login credentials or financial transactions.
It is essential to stay vigilant and implement preventive measures against these types of attacks. Regularly updating software, using strong, unique passwords, being cautious of suspicious emails or messages, and educating users about potential threats can significantly reduce the risks associated with cybersecurity attacks.
Frequency of Cybersecurity Attacks
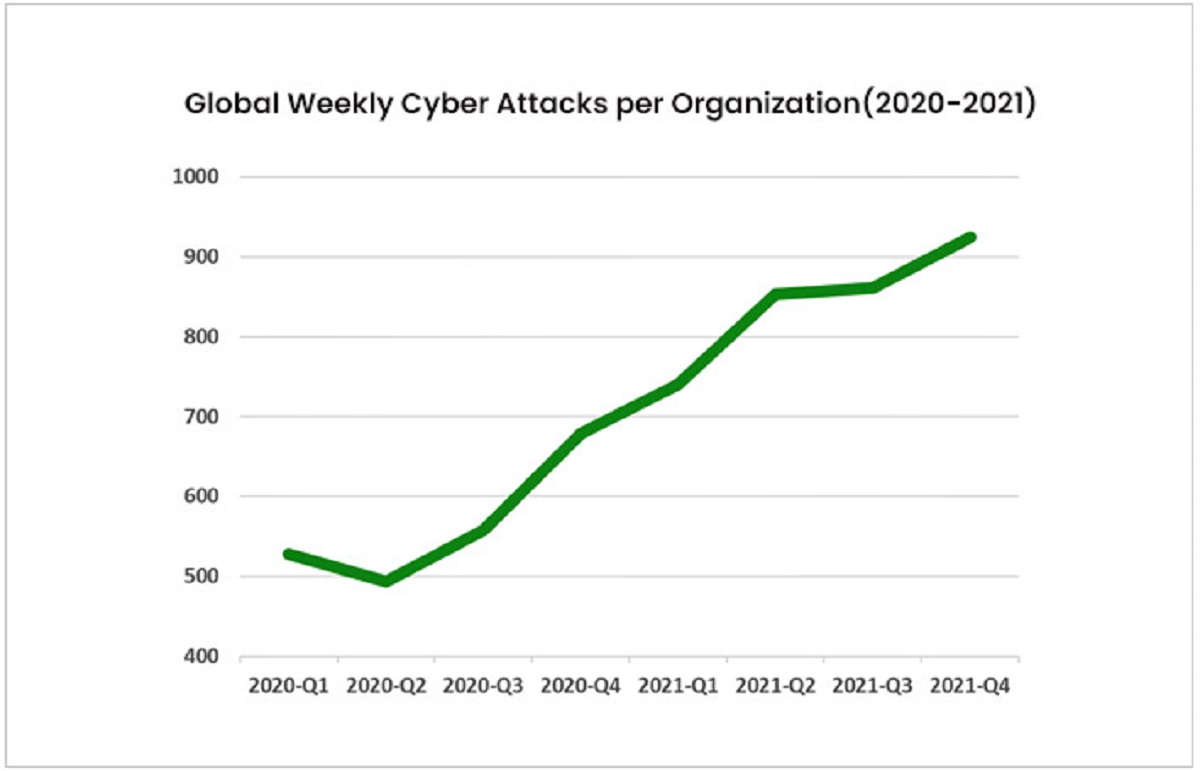
The frequency of cybersecurity attacks has been on the rise, reflecting the growing sophistication and persistence of cybercriminals. These attacks target individuals, businesses, and even governments, seeking to exploit vulnerabilities and gain unauthorized access to sensitive information. The frequency of cybersecurity attacks can vary based on various factors, including the target, motivation of the attacker, and the overall security posture. Here’s a closer look at the frequency of cybersecurity attacks:
1. Daily Attacks: Cybersecurity attacks occur daily, with millions of attempted attacks taking place worldwide. Automated scanning tools and botnets continuously probe networks and systems, searching for vulnerabilities to exploit. These attacks are often indiscriminate, targeting any system with potential weaknesses.
2. Targeted Attacks: Certain cybersecurity attacks are specifically targeted towards high-value individuals, organizations, or industries. Attackers may invest significant time and resources in researching their targets, planning sophisticated attacks such as spear-phishing campaigns or advanced persistent threats (APTs). These targeted attacks are often more difficult to detect and require advanced security measures to mitigate.
3. Industry-Specific Attacks: Different industries may experience varying levels of cybersecurity attacks based on the value of the data they hold or their overall security posture. Industries such as finance, healthcare, and technology are particularly attractive targets due to the wealth of sensitive information they possess. Government entities also face a high frequency of attacks, as they hold critical infrastructure and sensitive data.
4. Seasonal Spikes: Certain periods, such as holidays or major events, may see an increase in cybersecurity attacks. Attackers capitalize on increased online activity during these times, taking advantage of distractions and potential vulnerabilities. For example, phishing attacks related to holiday shopping or tax season scams tend to surge during specific times of the year.
5. Emerging Threats: The landscape of cybersecurity threats is constantly evolving, with new attack techniques and vulnerabilities emerging regularly. As technology advances and new trends, such as IoT or cloud computing, gain popularity, new avenues for attacks are opened. Keeping up with emerging threats requires continuous monitoring, proactive security measures, and ongoing education.
It is important to note that not all cybersecurity attacks succeed. Robust security measures and proactive defense mechanisms can thwart many attacks before they cause significant damage. However, the sheer frequency of attacks highlights the need for constant vigilance and proactive security measures to reduce the risk of successful breaches.
Staying up-to-date with the latest security practices, employing advanced threat detection and prevention tools, and regularly assessing and improving the security posture are crucial components of an effective cybersecurity strategy. By recognizing the frequency and diversity of cybersecurity attacks, individuals and organizations can better prepare and defend against these threats while minimizing potential damage and ensuring the integrity of their systems and data.
Industries Most Affected by Cybersecurity Attacks
Cybersecurity attacks can have devastating consequences for organizations across various industries. While every sector faces the risk of cyber threats, certain industries are particularly attractive targets for cybercriminals due to the value of the data they possess or the potential impact of successful attacks. Here are some industries that are most affected by cybersecurity attacks:
1. Finance and Banking: The finance and banking industry is a prime target for cybercriminals due to the vast amounts of valuable and sensitive data it holds. Attacks on financial institutions can result in financial losses, reputational damage, and compromised customer information. Cybercriminals often utilize sophisticated techniques, such as phishing, malware, and ransomware, to exploit vulnerabilities and gain unauthorized access to financial systems.
2. Healthcare: The healthcare industry is increasingly becoming a favored target for cyber attacks. The wealth of sensitive patient data, including medical records, personally identifiable information, and insurance details, makes it an attractive target for identity theft and fraud. Ransomware attacks on healthcare institutions have also become prevalent, disrupting critical services and potentially compromising patient safety.
3. Technology: The technology sector, including software development companies, hardware manufacturers, and cloud service providers, faces constant threats from cyber attacks. Attackers target these organizations to steal intellectual property, gain access to valuable source code, or exploit vulnerabilities in widely-used technologies. A successful attack on a technology company can have far-reaching implications, affecting not only the organization but also its customers and partners.
4. Government: Government entities at all levels are attractive targets for cyber attacks due to the critical nature of the services they provide and the sensitive information they hold. Nation-state actors, hacktivist groups, and cybercriminals target government agencies to gain access to classified data, disrupt critical infrastructure, or manipulate public perception. Cyber attacks on government entities pose significant national security concerns and can have wide-ranging impacts on the general public.
5. Energy and Utilities: The energy and utilities sector is vital for the functioning of societies and economies. Cyber attacks on this industry can disrupt the power grid, interrupt the supply of essential services, or compromise critical infrastructure. Both financially motivated attackers and nation-state actors have shown interest in targeting energy and utility organizations to exploit vulnerabilities and gain control over crucial systems.
6. Retail and E-commerce: Retail and e-commerce organizations are attractive targets due to the large amounts of customer data they store, including credit card information, purchase history, and personal details. Attacks targeting these organizations, particularly during peak shopping seasons, can result in significant financial losses, reputational damage, and customer trust erosion. Point-of-sale (POS) malware, data breaches, and phishing attacks are common methods employed by cybercriminals in this sector.
It is important to note that these industries are not the sole targets of cyber attacks, and cybersecurity threats can impact any organization or individual. Organizations across all sectors should prioritize implementing robust cybersecurity measures, conducting regular training and awareness programs, and staying abreast of the latest security practices to mitigate the risks associated with cyber attacks.
Malware Attacks
Malware attacks pose a significant threat to individuals, businesses, and organizations worldwide. Malware, short for malicious software, encompasses a variety of malicious programs designed to harm, exploit, or gain unauthorized access to computer systems and networks. Here’s a closer look at malware attacks, their characteristics, and their impacts:
Characteristics of Malware:
1. Viruses: Viruses are a type of malware that attaches themselves to legitimate files or programs, reproducing and spreading to other systems. They can hijack system resources, corrupt files, or interfere with normal operations. Viruses often require human interaction to spread, such as opening an infected email attachment or downloading infected files.
2. Worms: Worms are self-replicating malware that can spread rapidly across networks without requiring user interaction. They exploit vulnerabilities in operating systems or applications to gain unauthorized access to systems and can consume network bandwidth and degrade system performance. Worms often include a payload that can execute other forms of malware, such as ransomware.
3. Trojans: Trojans disguise themselves as legitimate software or files, tricking users into unknowingly executing them. Once activated, Trojans can harm systems, steal sensitive information, or provide control to malicious actors. They often serve as a backdoor for other malware to enter the system, compromising the security of the affected device or network.
4. Ransomware: Ransomware encrypts user files, making them inaccessible until a ransom is paid to the attacker. It can cause significant disruption to individuals and organizations, resulting in financial loss, reputational damage, and compromised data. Ransomware attacks often employ social engineering techniques and exploit vulnerabilities in software and systems.
5. Spyware: Spyware is designed to gather sensitive information from a user’s system without their knowledge or consent. It can collect personal data, log keystrokes, capture screenshots, monitor browser activity, or record audio and video. Spyware often aims to steal valuable information, such as login credentials, credit card numbers, or financial data.
Impacts of Malware Attacks:
1. Data Breaches: Malware attacks can result in data breaches, where sensitive information is accessed, stolen, or exposed. This can lead to identity theft, financial fraud, and reputational damage for individuals and organizations. Data breaches can also result in legal and regulatory consequences, such as fines and lawsuits.
2. Financial Losses: Malware attacks can have severe financial implications for individuals and businesses. Financial loss can occur due to direct costs associated with remediation, data recovery, and paying ransoms in the case of ransomware attacks. Indirect costs can include reputational damage, loss of customers, and business disruptions.
3. Operational Disruption: Malware attacks can disrupt regular business operations, leading to downtime, decreased productivity, and loss of critical data. In sectors such as healthcare or critical infrastructure, operational disruption can have severe consequences, potentially compromising patient safety or public welfare.
4. System and Network Compromise: Successful malware attacks can compromise systems and networks, giving unauthorized access to attackers. This can result in further exploitation, such as installing additional malware, stealing sensitive data, or using compromised systems as launching pads for other attacks.
Preventive Measures:
Preventing malware attacks requires a multi-layered approach, including:
– Installing reliable antivirus and anti-malware software and keeping it up-to-date.
– Regularly updating operating systems and applications with security patches.
– Being cautious of email attachments, downloads from untrusted sources, and suspicious websites.
– Implementing strong and unique passwords and enabling two-factor authentication.
– Educating users about potential malware threats and safe browsing practices.
By taking proactive measures and maintaining strong security hygiene, individuals and organizations can significantly reduce the risk of falling victim to malware attacks and protect their systems, data, and sensitive information.
Phishing Attacks
Phishing attacks are a prevalent form of cyber attack that aim to trick individuals into revealing sensitive information, such as passwords, credit card numbers, or social security numbers. These attacks rely on social engineering techniques and exploit human vulnerabilities to deceive unsuspecting victims. Understanding how phishing attacks work and adopting preventive measures can help protect against this widespread threat.
How Phishing Attacks Work:
1. Deceptive Email: Attackers send out emails that appear to come from legitimate sources, such as banks, government agencies, or well-known organizations. These emails often use official logos, email headers, and professional language to deceive recipients into believing they are genuine communications.
2. Urgency and Fear Tactics: Phishing emails often create a sense of urgency or fear, compelling recipients to respond without much thought. They may claim that there is an urgent problem with the recipient’s account or warn of dire consequences if action is not taken immediately.
3. Fake Websites: Phishing attacks may direct individuals to counterfeit websites that closely resemble legitimate ones. These websites aim to trick users into entering their login credentials or other sensitive information, which is then collected by the attackers for malicious purposes.
4. Spear Phishing: Spear phishing is a more targeted form of phishing attack where attackers gather personal information about their victims to make their emails appear more authentic. This could include using the victims’ names, job titles, or other personalized details to increase the chances of success.
5. Smishing and Vishing: Phishing attacks are not limited to emails. Attackers may use SMS (text message) or voice calls to deceive individuals into divulging sensitive information. These attacks are known as smishing (SMS phishing) and vishing (voice phishing).
Preventive Measures:
1. Verify the Sender: Always verify the sender’s email address, domain, and content of an email before taking any action. Look for subtle differences or misspellings in domain names that may suggest a fraudulent email.
2. Be Wary of Urgency: Phishing emails often create a sense of urgency or fear to compel immediate action. Take a step back and evaluate the situation before providing any sensitive information or clicking on any links.
3. Avoid Clicking Suspicious Links: Avoid clicking on links in emails, especially if they appear suspicious or were unexpected. Instead, manually enter the website’s URL into the browser or use a trusted bookmark to access the website directly.
4. Keep Software Up-to-Date: Ensure that your operating system, web browser, and antivirus software are all up-to-date, as this can help detect and block known phishing attacks.
5. Educate Yourself: Stay informed about the latest phishing techniques and educate yourself on how to identify and prevent phishing attacks. Training and awareness programs can help individuals recognize the signs of phishing and protect themselves from falling victim to these scams.
6. Enable Two-Factor Authentication: Enable two-factor authentication (2FA) whenever possible. This adds an extra layer of security by requiring a secondary form of verification, such as a one-time password or biometric authentication, in addition to the usual login credentials.
By staying vigilant, being cautious of suspicious emails and links, and following preventive measures, individuals can significantly reduce the risk of falling victim to phishing attacks. Maintaining a healthy skepticism and verifying the legitimacy of communications can protect personal and financial information from being compromised by cybercriminals.
Ransomware Attacks
Ransomware attacks have become increasingly prevalent in recent years, posing a significant threat to individuals, businesses, and organizations. Ransomware is a form of malware that encrypts a victim’s data, rendering it inaccessible until a ransom is paid to the attacker. Understanding how ransomware attacks occur, their impacts, and preventive measures is crucial for protecting against this evolving threat.
How Ransomware Attacks Work:
1. Delivery: Ransomware is typically delivered through malicious email attachments, infected websites, or exploit kits. Attackers may exploit vulnerabilities in software and systems or use social engineering techniques to trick users into opening infected files or clicking on malicious links.
2. Infection and Encryption: Once a device or network is infected, ransomware begins encrypting files using a unique encryption key that only the attacker possesses. This process often happens silently in the background, without the victim’s knowledge, until the encryption is complete.
3. Ransom Demand: After the encryption is complete, the attacker will typically display a ransom note, providing instructions on how to make the payment to receive the decryption key. Ransom demands are often made in cryptocurrency to maintain anonymity, making it challenging to trace the attackers.
4. Consequences of Non-Payment: If the victim refuses to pay the ransom, the attackers may threaten to permanently delete or leak the encrypted data, increasing the pressure to comply. Even if the ransom is paid, there is no guarantee that the attackers will provide a working decryption key, leading to potential financial loss without data recovery.
Impacts of Ransomware Attacks:
1. Financial Losses: Ransomware attacks can result in significant financial losses for individuals and organizations. The costs associated with ransom payments, potential legal fees, reputational damage, and business disruptions can be substantial. Additionally, there may be costs involved in restoring data, implementing stronger security measures, and recovering from the attack.
2. Operational Disruption: Ransomware attacks can disrupt normal business operations, causing downtime, loss of productivity, and customer dissatisfaction. Organizations may be unable to access critical files or systems, leading to temporary or permanent interruption of services. This can have a detrimental impact on revenue, customer trust, and overall business reputation.
3. Data Loss and Breach: Depending on the effectiveness of backups and the nature of the attack, victims may suffer data loss or unauthorized access to their sensitive information. This can lead to confidentiality breaches, reputational damage, and potential legal and regulatory consequences, especially if personal or sensitive customer data is compromised.
Preventive Measures:
1. Regular Backup: Regularly backup critical files and systems to an offline or cloud storage that is not directly accessible from the network. Ensure that backups are tested regularly to ensure data integrity and availability in the event of a ransomware attack.
2. Update and Patch: Keep all software, applications, and operating systems up-to-date with the latest security patches. Vulnerabilities in software are often exploited by attackers to gain access to systems, so timely updates are crucial in reducing the risk of infection.
3. Email and Web Filtering: Implement robust email and web filtering solutions to detect and block suspicious links, attachments, and websites known to be associated with ransomware attacks. This can prevent initial infection and reduce the chances of users inadvertently activating ransomware.
4. Employee Education: Educate employees about phishing techniques, safe web browsing habits, and the importance of exercising caution when opening email attachments or clicking on unfamiliar links. Regular training and awareness programs can significantly reduce the risk of falling victim to ransomware attacks.
5. Endpoint Protection: Deploy reliable and up-to-date antivirus and anti-malware solutions on all devices to detect and block ransomware infections. Advanced endpoint protection systems can also detect behavioral patterns associated with ransomware activities and mitigate their impact.
By implementing preventive measures, maintaining robust backups, and staying informed about the latest ransomware trends, individuals and organizations can significantly reduce the risk of falling victim to ransomware attacks. It is essential to have a comprehensive incident response plan and regularly test the effectiveness of security measures to ensure prompt detection and recovery in the event of an attack.
Distributed Denial of Service (DDoS) Attacks
Distributed Denial of Service (DDoS) attacks are a prevalent type of cyber attack that aim to disrupt the availability of online services by overwhelming a target’s infrastructure with a flood of traffic. DDoS attacks can have severe consequences for businesses, organizations, and individuals, leading to downtime, financial loss, and reputational damage. Understanding how DDoS attacks work, their impacts, and preventive measures is crucial for effective defense against these attacks.
How DDoS Attacks Work:
1. Botnet Formation: DDoS attacks are typically executed through a network of compromised computers known as a botnet. Attackers infect devices with malware and control them remotely to carry out the attack. The compromised devices become “bots” that are directed to send a massive amount of traffic to the target.
2. Traffic Overload: The aim of a DDoS attack is to overwhelm the target’s resources, such as bandwidth, processing power, or memory. By generating a massive volume of traffic, often through pinging or flooding requests, the target’s infrastructure becomes unable to handle the incoming requests, resulting in service degradation or complete disruption.
3. Types of DDoS Attacks: DDoS attacks can take various forms, including:
- Syn Flood: Exploiting the vulnerability in the TCP handshake process to initiate multiple incomplete connections, tying up server resources.
- UDP Flood: Sending a large number of User Datagram Protocol (UDP) packets to inundate the target’s network and exhaust its resources.
- HTTP Flood: Simulating legitimate HTTP requests to overload the target’s web server, making it unresponsive to genuine user traffic.
- Amplification Attack: Utilizing vulnerable servers or devices to amplify the attacking traffic, amplifying the amount of traffic directed at the target.
Impacts of DDoS Attacks:
1. Service Disruption: DDoS attacks can result in the complete unavailability of online services, causing significant disruption to businesses and organizations. This can lead to financial loss due to missed sales opportunities, reputational damage, and loss of customer trust if the business is unable to meet service level agreements or customer expectations.
2. Financial Consequences: Businesses may incur financial losses due to the necessary investments in robust DDoS mitigation solutions, as well as potential costs associated with downtime, customer compensation, and legal or regulatory implications resulting from the attack.
3. Damage to Reputation: DDoS attacks can harm an organization’s reputation, especially if customers perceive the failure to maintain service availability as a sign of inadequate security or reliability. Maintaining customer trust and rebuilding a positive reputation can take time and concerted effort after a DDoS attack.
Preventive Measures:
1. DDoS Mitigation Solutions: Implementing effective DDoS mitigation solutions, such as traffic filtering, rate limiting, and load balancing, can help minimize the impact of DDoS attacks. Utilizing the services of a reputable DDoS mitigation provider can provide access to specialized expertise and DDoS-resilient infrastructure.
2. Scalable Infrastructure: Ensuring that your infrastructure is scalable and can handle sudden spikes in traffic helps reduce the impact of DDoS attacks. This can involve adopting cloud-based services, load balancing across multiple servers, and implementing a content delivery network (CDN).
3. Network and Application Monitoring: Regularly monitoring network traffic and application performance enables early detection of unusual patterns or signs of a DDoS attack. Implementing monitoring tools and establishing alert systems can help initiate timely response and mitigate the impact of the attack.
4. Incident Response Plan: Developing an incident response plan tailored to DDoS attacks can help organizations respond quickly and effectively. This plan should outline the roles and responsibilities of stakeholders, mechanisms for communication and coordination, and steps to minimize damage and restore services.
5. Stay Updated: Keeping abreast of the latest DDoS attack trends and patterns helps organizations understand emerging threats and adapt their defense mechanisms accordingly. Sharing information and collaborating with industry partners, security vendors, and government agencies can also enhance preparedness and response capabilities.
By implementing these preventive measures and adopting a proactive approach to DDoS defense, organizations can better protect their infrastructure, mitigate the impacts of attacks, and ensure the continued availability of their online services.
Social Engineering Attacks
Social engineering attacks are a type of cyber attack that exploit human psychology and manipulate individuals into revealing sensitive information or performing actions that benefit the attacker. These attacks rely on deception, trust manipulation, and exploiting human vulnerabilities rather than technical vulnerabilities. Understanding the different forms of social engineering attacks and adopting preventive measures is crucial for mitigating the risks associated with these deceptive tactics.
Types of Social Engineering Attacks:
1. Phishing: Phishing attacks use deceptive emails, text messages, or instant messages to trick individuals into revealing confidential information such as passwords, credit card numbers, or social security numbers. These messages often appear to be from legitimate sources, such as banks or trusted organizations, creating a sense of urgency or fear to prompt action.
2. Pretexting: Pretexting involves creating a fabricated scenario or pretext to deceive individuals and gain their trust. Attackers often pretend to be someone they are not, such as a customer service representative, a coworker, or a technical support agent, in order to extract sensitive information or gain unauthorized access to systems.
3. Baiting: Baiting attacks entice individuals with an appealing offer or item, such as a free gift or a USB drive containing malware. Once the victim engages with the bait, the attacker can exploit their actions or gain access to their system, compromising security and potentially stealing sensitive information.
4. Spear Phishing: Spear phishing is a more targeted form of phishing that involves tailoring attacks to specific individuals or organizations. Attackers use personal information, such as names, job titles, or affiliations, to make their messages appear more authentic and increase the likelihood of success.
5. Impersonation: Social engineering attacks often involve impersonating trusted individuals or authorities, such as a boss, colleague, or law enforcement officer. Attackers use their perceived authority to manipulate victims into disclosing sensitive information or performing actions that benefit the attacker.
Preventive Measures:
1. Awareness and Education: Training individuals on social engineering tactics, recognizing warning signs, and promoting a healthy skepticism can significantly reduce the success rate of social engineering attacks. Educating employees about the risks and precautionary measures helps to create a security-conscious culture within organizations.
2. Verify Requestors: When receiving requests for sensitive information or performing actions, individuals should verify the authenticity of the requestor through alternate communication channels. This involves contacting the person or organization directly using known, trusted contact information rather than relying solely on information provided in the initial communication.
3. Be Cautious of Unsolicited Communication: Individuals should exercise caution when receiving unsolicited emails, messages, or phone calls. If something seems suspicious or too good to be true, it likely is. Avoid clicking on suspicious links, opening unexpected attachments, or providing personal information unless the legitimacy of the communication is assured.
4. Implement Strong Authentication Measures: Utilize strong passwords and enable two-factor authentication (2FA) on email accounts, social media platforms, and other sensitive systems. This adds an extra layer of protection to mitigate the risk of attackers gaining unauthorized access.
5. Keep Software Updated: Regularly update your operating system, applications, and antivirus software to protect against known vulnerabilities frequently targeted by social engineering attacks. Software updates often include security patches that address vulnerabilities and help protect against potential exploitation.
By promoting awareness, maintaining a healthy skepticism, and implementing preventive measures, individuals and organizations can reduce the risk of falling victim to social engineering attacks. Combining technology-based defenses with human vigilance is crucial for effectively mitigating the risks associated with these deceptive and manipulative tactics.
Steps to Protect Yourself from Cybersecurity Attacks
In today’s digital landscape, protecting yourself from cybersecurity attacks is of paramount importance. As cybercriminals continue to develop sophisticated techniques, it is crucial to take proactive measures to safeguard your personal information and digital assets. Here are some key steps you can take to protect yourself:
1. Use Strong and Unique Passwords: Create strong and unique passwords for each of your online accounts. Avoid using easily guessable information like your name, birthdate, or “password” itself. Consider utilizing password management tools to generate and securely store complex passwords.
2. Enable Two-Factor Authentication (2FA): Enable 2FA whenever possible. This additional layer of security requires presenting a second form of identification, such as a fingerprint scan or a unique code sent to your mobile device, to access your accounts.
3. Keep Software Up-to-Date: Regularly update your operating system, applications, and security software to ensure they have the latest security patches. Software updates often include fixes for vulnerabilities that attackers may exploit.
4. Be Cautious of Suspicious Emails and Links: Exercise caution when opening emails from unknown senders or clicking on suspicious links. Watch out for signs of phishing emails, such as poor grammar, misspellings, or urgent requests for personal information.
5. Install Reliable Security Software: Utilize reputable antivirus and anti-malware software to protect your devices from viruses, malware, and other security threats. Keep the software updated for optimal protection.
6. Regularly Backup Your Data: Create regular backups of your important files and store them securely. This protects your data in the event of a ransomware attack or hardware failure, allowing you to restore your information without paying the ransom or facing data loss.
7. Practice Safe Web Browsing: Be cautious when visiting websites, especially those that are suspicious or non-secure. Look for the padlock icon and “https” in the website’s URL before entering any personal or financial information.
8. Be Mindful of Sharing Personal Information: Be selective about the personal information you share online, especially on social media platforms. Avoid providing sensitive details that could be used for identity theft or account takeover.
9. Educate Yourself about Cybersecurity: Stay informed about the latest cybersecurity threats and best practices. Take advantage of resources, articles, and security awareness training to enhance your knowledge and understanding of potential risks.
10. Regularly Monitor Your Accounts: Keep a close eye on your financial accounts, credit reports, and online transactions. Immediately report any suspicious activity or unauthorized transactions to your financial institution.
11. Use Secure Wi-Fi Networks: When connecting to public Wi-Fi networks, use secured connections whenever possible. Avoid accessing sensitive information or conducting financial transactions on unsecure networks.
12. Install Updates on IoT Devices: Ensure that Internet of Things (IoT) devices, such as smart home devices or wearables, are updated with the latest firmware to address any security vulnerabilities.
By following these steps, you can significantly enhance your cybersecurity posture and reduce the risk of falling victim to cyber attacks. Remember, cybersecurity is an ongoing effort, and staying informed and proactive is key to protecting yourself in the digital age.
Conclusion
In today’s interconnected and technologically advanced world, cybersecurity is of utmost importance. The increasing frequency and sophistication of cyber attacks pose significant threats to individuals, businesses, and organizations. Understanding the importance of cybersecurity and taking proactive measures to protect against various forms of attacks is crucial.
Cybersecurity attacks, such as malware attacks, phishing attacks, ransomware attacks, DDoS attacks, and social engineering attacks, exploit vulnerabilities in both technology and human behavior. By recognizing these types of attacks and implementing preventive measures, individuals and organizations can significantly reduce their risk exposure.
Protecting oneself from cybersecurity attacks involves various steps. Using strong and unique passwords, enabling two-factor authentication, and keeping software up-to-date are essential for strengthening the security of online accounts. Being cautious of suspicious emails and links, installing reliable security software, and regularly backing up data can help mitigate the risks associated with malware and ransomware attacks.
Adopting safe web browsing habits, being mindful of sharing personal information, and educating oneself about cybersecurity threats are critical in preventing social engineering attacks. Regularly monitoring financial accounts, using secure Wi-Fi networks, and staying updated on IoT device security ensure a well-rounded defense against cyber threats.
Although it is impossible to eliminate the risk of cybersecurity attacks entirely, following these preventive measures significantly reduces the likelihood and impact of such attacks. Additionally, staying informed about the latest cybersecurity trends and best practices is crucial as the threat landscape continues to evolve.
Cybersecurity is a shared responsibility that requires the collective efforts of individuals, organizations, and governments. By prioritizing cybersecurity, implementing robust security measures, and fostering a culture of vigilance and awareness, we can create a safer digital environment for everyone. Together, we can fortify our defenses against cyber threats and minimize the potential consequences of cyber attacks.