Introduction
The Dark Web is a concept that has gained notoriety in recent years. It is often portrayed as a shadowy underworld, a hidden realm where anonymity prevails, and illicit activities flourish. But what exactly is the Dark Web, and how do people access it?
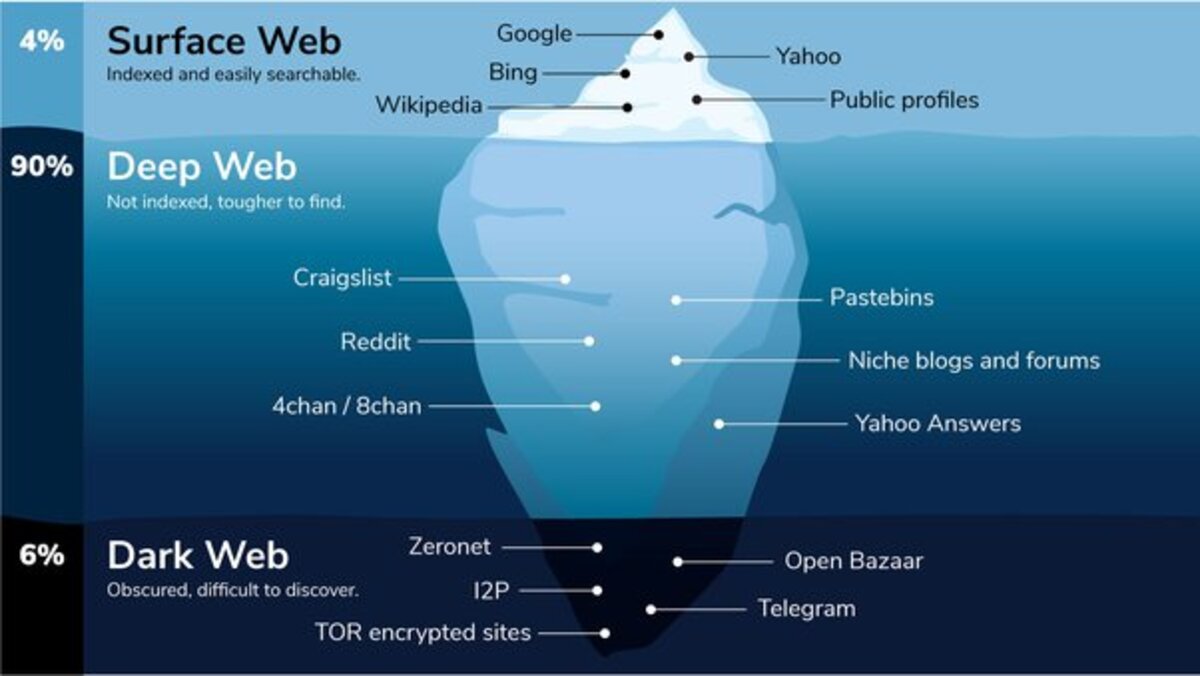
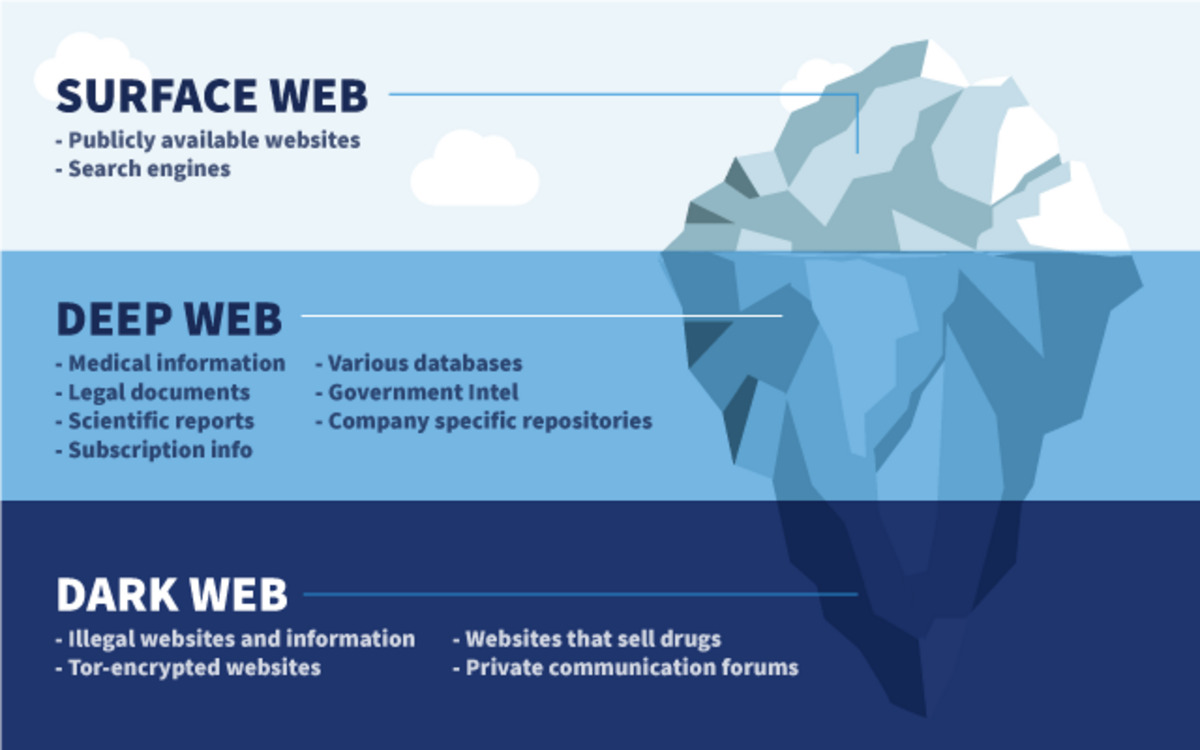
The Dark Web refers to a part of the internet that is not indexed by traditional search engines. It exists on encrypted networks and requires specific software and configurations to access. On the Dark Web, users can remain anonymous, communicating and conducting transactions without revealing their true identities. While the Dark Web is often associated with illegal activities, it is not inherently illegal itself. It is a space where anonymity, privacy, and freedom of expression can be both a boon and a curse.
In this article, we will explore the world of the Dark Web, how people access it, the tools they use, and the potential risks involved. It is important to note that accessing the Dark Web carries significant legal and security implications, so caution and discernment are crucial when navigating this clandestine realm.
What is the Dark Web?
The Dark Web is a part of the internet that is intentionally hidden and accessible only through special software. Unlike the surface web that we commonly use, which is indexed by search engines and easily accessible, the Dark Web exists on encrypted networks that provide anonymity to its users. It is a subset of the deep web, which includes all websites that are not indexed by search engines.
One of the most popular anonymity tools used on the Dark Web is Tor (The Onion Router). Originally developed by the U.S. Navy, Tor routes internet traffic through a series of volunteer nodes, making it extremely difficult to trace the identity and location of users. This makes the Dark Web attractive to individuals seeking privacy, such as whistleblowers, journalists, and activists living under oppressive regimes.
Within the Dark Web, there are several marketplaces, forums, and communication platforms that facilitate a wide range of activities. While some of these activities are legal, such as privacy-focused discussions and alternative social networks, the Dark Web is also notorious for hosting illegal marketplaces offering drugs, stolen data, counterfeit documents, hacking services, and other illicit goods and services.
It’s important to understand that the Dark Web is a vast and complex space with a diverse range of websites and services. Not all websites on the Dark Web are engaged in illegal activities. There are legitimate businesses using the anonymity provided by the Dark Web to operate safely and securely. However, it is the illegal activities that often garner the most attention and contribute to the Dark Web’s dark reputation.
The Dark Web is a double-edged sword. While it provides a refuge for those who seek privacy and security, it also harbors cybercriminals, terrorists, and malicious actors. It is a place where individuals can buy and sell illegal goods, hire hackers, and engage in activities that would be unthinkable on the surface web. Navigating the Dark Web is a risky endeavor, and individuals must tread cautiously to avoid falling victim to scams, cyberattacks, or legal consequences.
How to Access the Dark Web
Accessing the Dark Web involves a series of steps to ensure anonymity and confidentiality. Here, we will explore the primary methods used to access this hidden part of the internet.
1. Using Tor: The most popular method to access the Dark Web is by using the Tor browser. Tor is a free and open-source software that anonymizes internet traffic by routing it through multiple servers around the world. To access the Dark Web with Tor, users need to install the Tor browser, which is specifically designed to access .onion sites – websites with addresses that end in .onion rather than .com or .net. The Tor browser encrypts users’ data and routes it through a network of volunteer-operated servers, making it difficult to track their activities back to their IP address.
2. Tails: Tails (The Amnesic Incognito Live System) is a privacy-oriented operating system that can be run from a USB stick or DVD. It is designed to leave no traces on the computer and routes all internet traffic through the Tor network. Tails ensures that users can access the Dark Web from any computer without leaving behind any digital footprints.
3. I2P (Invisible Internet Project): Similar to Tor, I2P is an anonymous network layer that allows users to create and access websites anonymously. It uses a decentralized peer-to-peer network to encrypt and route traffic, protecting the privacy and anonymity of its users.
4. Freenet: Freenet is a decentralized platform designed to enable the sharing of information without censorship. It allows users to access websites within the Freenet network, including those within the Dark Web, without revealing their identities. Freenet operates on a similar principle to other anonymity networks by routing and encrypting traffic through multiple nodes.
5. VPNs (Virtual Private Networks): While VPNs are not specifically designed for accessing the Dark Web, they can add an extra layer of security and privacy. A VPN creates an encrypted connection between the user’s device and a remote server, hiding the user’s IP address and encrypting their internet traffic. This can help to minimize the risk of surveillance and protect against potential threats when accessing the Dark Web.
It is important to note that accessing the Dark Web is not without risks. The content and activities on the Dark Web are largely unregulated, making it a haven for cybercriminals and illegal activities. Individuals who choose to explore the Dark Web should proceed with caution, as they may encounter explicit, illegal, or disturbing content. Additionally, legal consequences can arise from engaging in unlawful activities on the Dark Web, as law enforcement agencies worldwide are actively monitoring and cracking down on illegal online activities.
Using Tor to Access the Dark Web
Tor (The Onion Router) is a crucial software tool used to access the Dark Web. Developed by the U.S. Navy, Tor provides anonymity and privacy by encrypting and routing internet traffic through a network of volunteer-operated servers called nodes. Here, we will delve into the process of using Tor to access the Dark Web.
1. Installing Tor: To begin, users need to download and install the Tor browser. It is available for Windows, macOS, Linux, and Android platforms. The Tor browser is specifically designed to access .onion sites, which are unique addresses used in the Dark Web. It is essential to download Tor only from the official website to ensure the integrity and security of the software.
2. Connecting to the Tor Network: Once installed, open the Tor browser. It automatically connects to the Tor network and establishes a secure connection. The connection process may take a few moments as the browser connects to multiple nodes to ensure anonymity.
3. Browsing the Dark Web: With the Tor browser successfully connected to the Tor network, users can navigate the Dark Web by entering .onion website addresses into the browser’s address bar. It is important to note that .onion sites are not accessible through traditional search engines.
4. Staying Safe on the Dark Web: While Tor provides some level of anonymity, it is not foolproof. Users must take additional measures to protect their privacy and security. It is advisable to disable any browser plugins or extensions, as they may compromise anonymity. Additionally, being cautious about the sites visited and the information shared is crucial, as many entities on the Dark Web are involved in illegal activities. Users must exercise discretion and avoid engaging in illegal or unethical practices.
5. Regular Updates: Tor is continuously updated to patch security vulnerabilities and improve its performance. It is important to keep the Tor browser up to date, as outdated versions may have known security flaws that could compromise anonymity.
Using Tor provides users with an additional layer of privacy and security when accessing the Dark Web. However, it is important to remember that Tor is not invincible, and users should exercise caution and adhere to safe browsing practices to protect themselves from potential threats and legal ramifications.
The Role of VPNs in Accessing the Dark Web
While Tor is the primary tool used to access the Dark Web, the use of a Virtual Private Network (VPN) can add an extra layer of security and privacy. A VPN creates a secure and encrypted connection between the user’s device and a remote server, effectively hiding the user’s IP address and encrypting their internet traffic. Here, we explore the role of VPNs in accessing the Dark Web.
1. Enhanced Anonymity: When accessing the Dark Web, combining Tor with a VPN can provide an additional layer of anonymity. By encrypting internet traffic and hiding the user’s IP address, a VPN makes it even more challenging for anyone to trace the online activities back to the user. This dual-layer protection is especially useful in countries with strict internet surveillance or in situations where individuals want to avoid potential tracking by government agencies or malicious actors.
2. Protection Against ISP Monitoring: Internet Service Providers (ISPs) have the ability to monitor users’ online activities. By using a VPN, users can effectively prevent their ISPs from tracking and logging their internet usage. This can be particularly important when accessing the Dark Web, where privacy is a top priority.
3. Encryption of Traffic: VPNs encrypt all the user’s internet traffic, ensuring that even if it is intercepted by a third party, it remains unreadable and inaccessible. This is especially crucial when accessing the Dark Web, where sensitive information may be exchanged. By encrypting the traffic, VPNs provide an additional layer of security, protecting against potential eavesdropping or data theft.
4. Bypassing Geographic Restrictions: In some cases, certain websites or services on the Dark Web may be geographically restricted or blocked. By using a VPN, users can bypass these restrictions by connecting to a server located in a region where access is allowed. This allows individuals to freely explore the content on the Dark Web without any limitations imposed by geographical boundaries.
5. Protection against Malicious Actors: VPNs not only provide anonymity and encryption but also protect against potential threats from malicious actors. By masking the user’s IP address, a VPN makes it difficult for hackers to target the user’s device or launch attacks. This can help safeguard sensitive information and prevent unauthorized access to personal data.
While VPNs offer several benefits when accessing the Dark Web, it is essential to choose a reputable and trustworthy VPN provider. Not all VPNs are created equal, and some may log user data or compromise privacy. Users should conduct thorough research, read reviews, and select a VPN service that aligns with their privacy and security requirements.
Common Misconceptions about the Dark Web
The Dark Web is often shrouded in mystery and surrounded by misconceptions. Misunderstandings about this hidden part of the internet contribute to its dreaded reputation. Here, we debunk some common misconceptions about the Dark Web to provide a clearer understanding of what it truly entails.
1. Everything on the Dark Web is illegal: While the Dark Web is indeed home to illegal activities and illicit marketplaces, it is important to note that not everything on the Dark Web is illegal. Just like the surface web, the Dark Web is a diverse landscape containing various types of websites and services, legal and illegal alike. There are legitimate uses for the Dark Web, such as anonymous forums, alternative social networks, and privacy-focused communication platforms.
2. The Dark Web is only for hackers and criminals: While criminals and hackers do operate on the Dark Web, they do not represent the entire user base. The Dark Web’s anonymity and privacy also attract journalists, whistleblowers, activists from oppressive regimes, and individuals seeking secure methods of communication. It is a refuge for those who value privacy and freedom of speech.
3. Accessing the Dark Web will get you in trouble with the law: Accessing the Dark Web itself is not illegal. It is the activities conducted on the Dark Web that can lead to legal consequences. Engaging in illegal activities, such as purchasing drugs or participating in cybercrime, is what exposes individuals to potential legal problems. Merely browsing the Dark Web out of curiosity does not necessarily make one a criminal.
4. The Dark Web is more dangerous than the surface web: While it is true that the Dark Web harbors illegal activity and malicious actors, that does not automatically make it more dangerous than the surface web. Just as with the surface web, exercising caution, being vigilant, and practicing safe browsing habits help mitigate potential risks. Individuals who do not involve themselves in illegal activities while on the Dark Web are unlikely to encounter any danger.
5. The Dark Web is inaccessible without special tools: While it is true that accessing the Dark Web requires specific software like Tor, it is not an inaccessible realm limited to technologically advanced users. With the right tools and instructions, anyone can navigate the Dark Web. It is important to approach it with knowledge and caution, but it is not an exclusive domain accessible only to a select few.
Debunking these misconceptions is crucial to gaining a better understanding of the Dark Web. While it does have its dark side, it is also a place where privacy, security, and freedom of speech hold value. With proper awareness and discernment, individuals can explore the Dark Web without falling victim to misconceptions and unnecessary fear.
Dangers and Risks Associated with the Dark Web
While the Dark Web offers anonymity and a refuge for privacy-conscious individuals, it is essential to understand the dangers and risks that come with navigating this hidden part of the internet. Here, we explore some of the potential dangers and risks associated with the Dark Web.
1. Illicit Activities: The Dark Web is notorious for hosting illegal marketplaces that trade drugs, stolen data, counterfeit documents, hacking tools, and other illicit goods and services. Engaging in such activities puts individuals at risk of becoming embroiled in illegal transactions, leading to legal consequences.
2. Cybercrime: The Dark Web is a hotspot for cybercriminals who offer hacking services, sell stolen data, and launch cyberattacks. By navigating the Dark Web, individuals risk becoming victims of cybercrime, including identity theft, fraud, and ransomware attacks. Cybercriminals often target unsuspecting users who access the Dark Web without proper security measures in place.
3. Scams and Fraud: The lack of regulation on the Dark Web makes it an ideal breeding ground for scams and fraud. Individuals may encounter fake marketplaces, fraudulent sellers, and misleading services. Trust is limited, and there is a high risk of falling victim to scams, losing money, or having personal information compromised.
4. Malware and Viruses: Malicious actors on the Dark Web may distribute malware, viruses, and other malicious software. Innocent-looking websites or downloads can contain harmful code designed to steal personal information or compromise security. Accessing the Dark Web without proper precautions increases the risk of infecting your device or network with malware.
5. Exposing Personal Information: The anonymity provided by the Dark Web can be a double-edged sword. While it may protect your identity, it can also lead to a false sense of security. Sharing personal information on forums, marketplaces, or communication platforms puts individuals at risk of exposure. It is crucial to be cautious with the information shared and to use pseudonyms and alternative email addresses whenever possible.
6. Law Enforcement Monitoring: Despite its hidden nature, law enforcement agencies worldwide are actively monitoring the Dark Web. Engaging in illegal activities, such as buying or selling drugs or participating in cybercrime, can lead to being targeted by law enforcement. Authorities have successfully shut down illegal marketplaces and arrested individuals engaged in criminal activities on the Dark Web.
In light of these dangers and risks, it is imperative to exercise caution and be aware of the potential consequences when accessing the Dark Web. Proper security measures, such as using a secure operating system, keeping software up to date, utilizing reputable anti-malware software, and employing encryption and VPN services, can help mitigate some of the risks associated with exploring the Dark Web.
Legal Implications of Accessing the Dark Web
Accessing the Dark Web carries significant legal implications, mainly due to the illicit activities and illegal marketplaces that exist within its hidden depths. It is important to understand the potential legal consequences associated with navigating the Dark Web. Here, we explore the legal implications to consider when accessing the Dark Web.
1. Engaging in Illegal Activities: Accessing the Dark Web provides an opportunity to engage in a wide range of illegal activities, from purchasing drugs and weapons to participating in cybercrime. It is crucial to be aware that involvement in such activities can result in criminal charges and serious legal consequences.
2. Possession of Illegal Content: While browsing the Dark Web, individuals may encounter illegal content such as child pornography or illegal hacking tools. Accessing or possessing such content is illegal in most jurisdictions and can lead to severe legal penalties, including imprisonment and a permanent criminal record.
3. Intellectual Property Violations: The Dark Web is also known for hosting websites that offer pirated software, digital media, and copyrighted material without permission from the rightful owners. Downloading or distributing copyrighted content on the Dark Web can result in legal action and substantial fines for copyright infringement.
4. Anonymous Reporting: In some jurisdictions, merely accessing the Dark Web may raise suspicion, regardless of whether illegal activities are involved. Law enforcement agencies may monitor Dark Web activity and target individuals they suspect to be engaged in illicit activities. The mere presence on the Dark Web could lead to investigation or surveillance by law enforcement.
5. International Jurisdiction: The Dark Web operates across international boundaries, making it complex to determine the jurisdiction under which laws apply. However, engaging in illegal activities on the Dark Web can lead to extradition to another country where the offense is punishable. International cooperation between law enforcement agencies has increased, making it more likely for individuals to face legal consequences even if they accessed the Dark Web from a different jurisdiction.
Navigating the Dark Web without engaging in illegal activities is not inherently criminal. However, it is essential to exercise caution and be aware of the potential legal risks. Even unintentional involvement in illegal activities, such as accidental access to illegal content or unknowingly participating in a scam, can have severe legal repercussions. It is advisable to consult with legal professionals and understand the applicable laws and regulations before accessing the Dark Web to ensure compliance and avoid legal entanglements.
Conclusion
The Dark Web remains a mysterious and complex part of the internet. It holds both intrigue and danger, offering anonymity and privacy to those who seek it, but also harboring illicit activities and potential legal risks. Despite its reputation, it is crucial to approach the Dark Web with proper understanding and caution.
We have explored what the Dark Web is and how it can be accessed through tools like Tor and VPNs. We debunked common misconceptions and shed light on the potential dangers and risks associated with the Dark Web, such as engaging in illegal activities, encountering cybercrime, falling victim to scams and fraud, and facing legal implications. It is important to remember that not everything on the Dark Web is illegal, but engaging in illegal activities can lead to serious legal consequences.
If one chooses to explore the Dark Web, it is essential to prioritize personal safety and protect one’s privacy. This can be achieved through the use of secure software, adherence to safe browsing practices, and the understanding that anonymity does not guarantee invincibility.
Ultimately, accessing the Dark Web should be approached with discernment and a thorough understanding of the potential risks involved. It is crucial to navigate this hidden realm with caution, making informed decisions and being aware of the potential legal ramifications.
In a world where privacy and security are increasingly valued, the Dark Web provides an alternative to the surveillance and control often experienced on the surface web. However, individuals must weigh the benefits against the risks and determine whether the potential rewards of accessing the Dark Web align with their personal values and risk tolerance.
Remember, the Dark Web is not a place to be taken lightly. It requires a level of technical understanding, responsible behavior, and adherence to lawful activities. Proceeding with caution can help individuals navigate the Dark Web landscape without falling into its dark underbelly.