What is the TOR Browser?
The TOR (The Onion Router) Browser is a powerful tool designed to provide users with enhanced privacy and anonymity while browsing the internet. It is based on the concept of onion routing, where data is encrypted and transmitted through a series of network nodes, or relays, before reaching its destination. This process helps to conceal the user's IP address and browsing activities, making it difficult for anyone to track their online behavior.
The TOR Browser is built on the Firefox browser and comes pre-configured with privacy-focused settings and security features. It is available for various operating systems, including Windows, macOS, Linux, and Android, making it accessible to a wide range of users.
When you use the TOR Browser, your internet traffic is routed through a global network of volunteer-operated servers, which are designed to prevent anyone from monitoring your connection. This decentralized approach to internet browsing helps to protect your online privacy and allows you to access websites that may be blocked or censored in your region.
One of the key features of the TOR Browser is its ability to access .onion websites, which are part of the dark web. These websites are not indexed by traditional search engines and are often associated with anonymity and privacy. While the dark web is often portrayed in a negative light due to its association with illicit activities, it also serves as a platform for whistleblowers, journalists, and individuals seeking to communicate without fear of censorship or surveillance.
In summary, the TOR Browser is a valuable tool for individuals who prioritize online privacy and wish to browse the internet without leaving a digital footprint. Its robust security features and commitment to user anonymity make it a popular choice for those seeking a more private and secure browsing experience.
Installing the TOR Browser
Installing the TOR Browser is a straightforward process that allows users to quickly set up and access the powerful privacy features it offers. Whether you're using a Windows, macOS, Linux, or Android device, the TOR Browser is readily available for download from the official TOR Project website. Here's a step-by-step guide to help you get started with installing the TOR Browser on your preferred operating system:
Windows
- Begin by opening your preferred web browser and navigating to the official TOR Project website.
- Once on the website, locate the download section and select the Windows option to initiate the download of the TOR Browser installer.
- After the download is complete, locate the installer file in your downloads folder and double-click to launch the installation process.
- Follow the on-screen instructions to complete the installation, and choose your preferred language and installation location when prompted.
- Once the installation is finished, launch the TOR Browser and begin exploring the internet with enhanced privacy and anonymity.
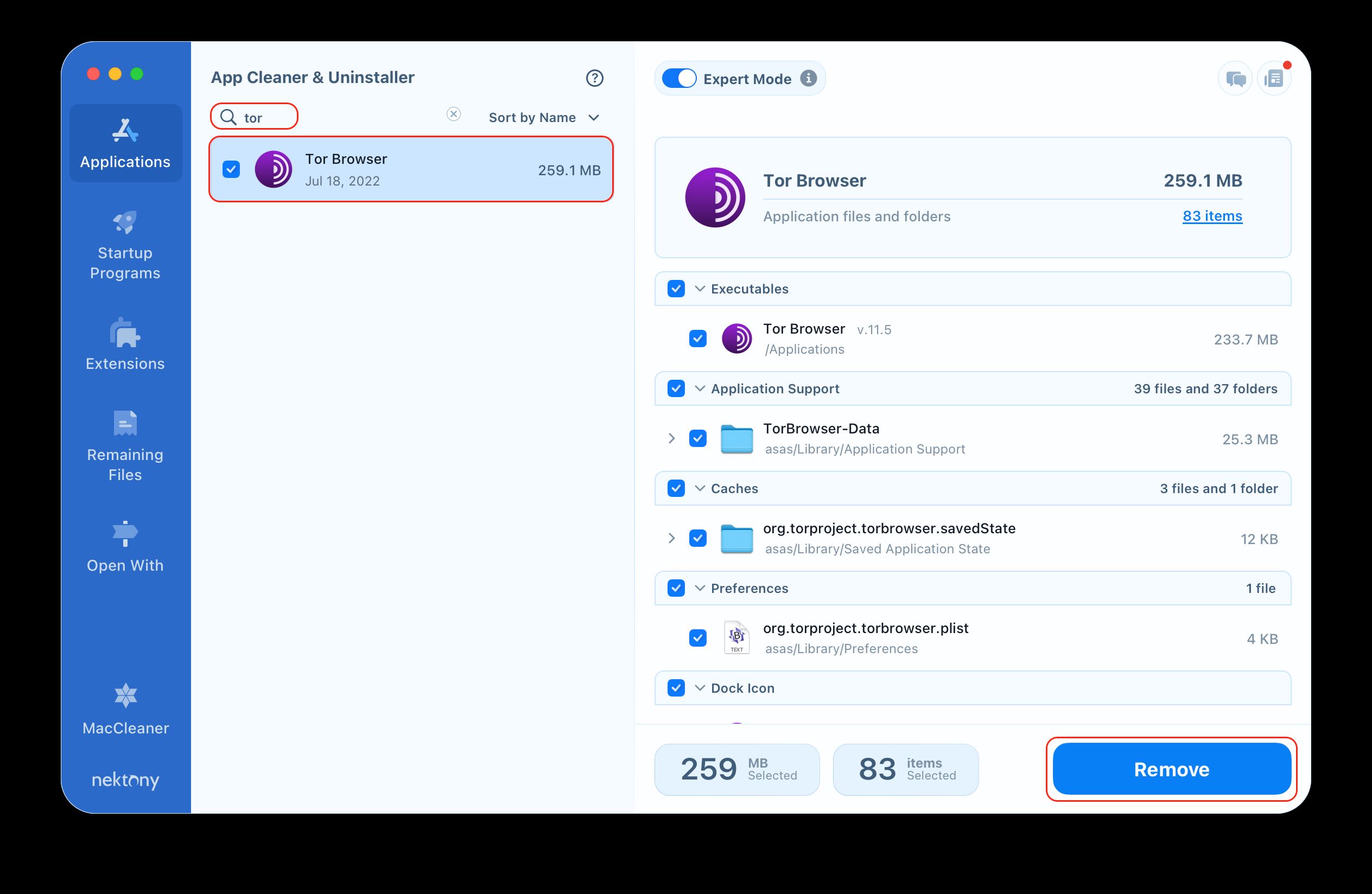
macOS
- Visit the official TOR Project website using your web browser on your macOS device.
- Look for the download section and select the macOS option to download the TOR Browser installer.
- Once the download is complete, open the installer file and drag the TOR Browser icon to your Applications folder to complete the installation.
- Launch the TOR Browser from your Applications folder and start enjoying the privacy features it provides.
Linux
- On your Linux system, open a web browser and go to the official TOR Project website.
- Locate the download section and choose the Linux option that corresponds to your distribution (e.g., Debian, Ubuntu, Fedora).
- Follow the provided instructions to add the TOR Browser repository to your package manager and install the browser using the appropriate commands.
- Once the installation is complete, launch the TOR Browser and begin browsing the internet with enhanced privacy and security.
Android
- Open the Google Play Store on your Android device and search for "TOR Browser."
- Locate the TOR Browser app in the search results and tap the "Install" button to download and install it on your device.
- Once the installation is complete, open the TOR Browser app and start using it to browse the internet anonymously on your mobile device.
By following these simple steps, users can easily install the TOR Browser on their preferred devices and take advantage of its robust privacy and anonymity features. Whether you're using a desktop or mobile device, the TOR Browser provides a seamless installation process, allowing you to browse the internet with enhanced privacy and security.
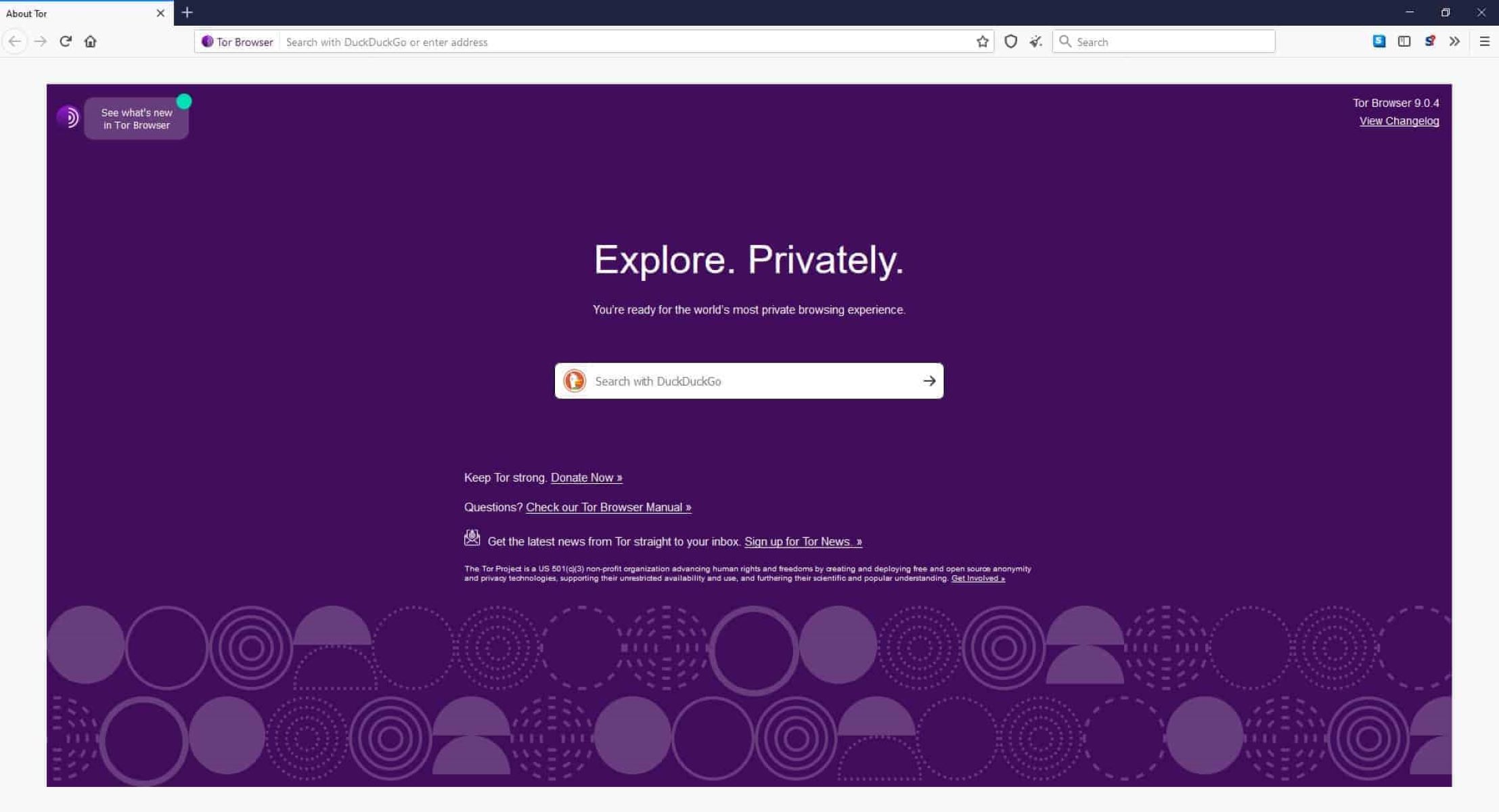
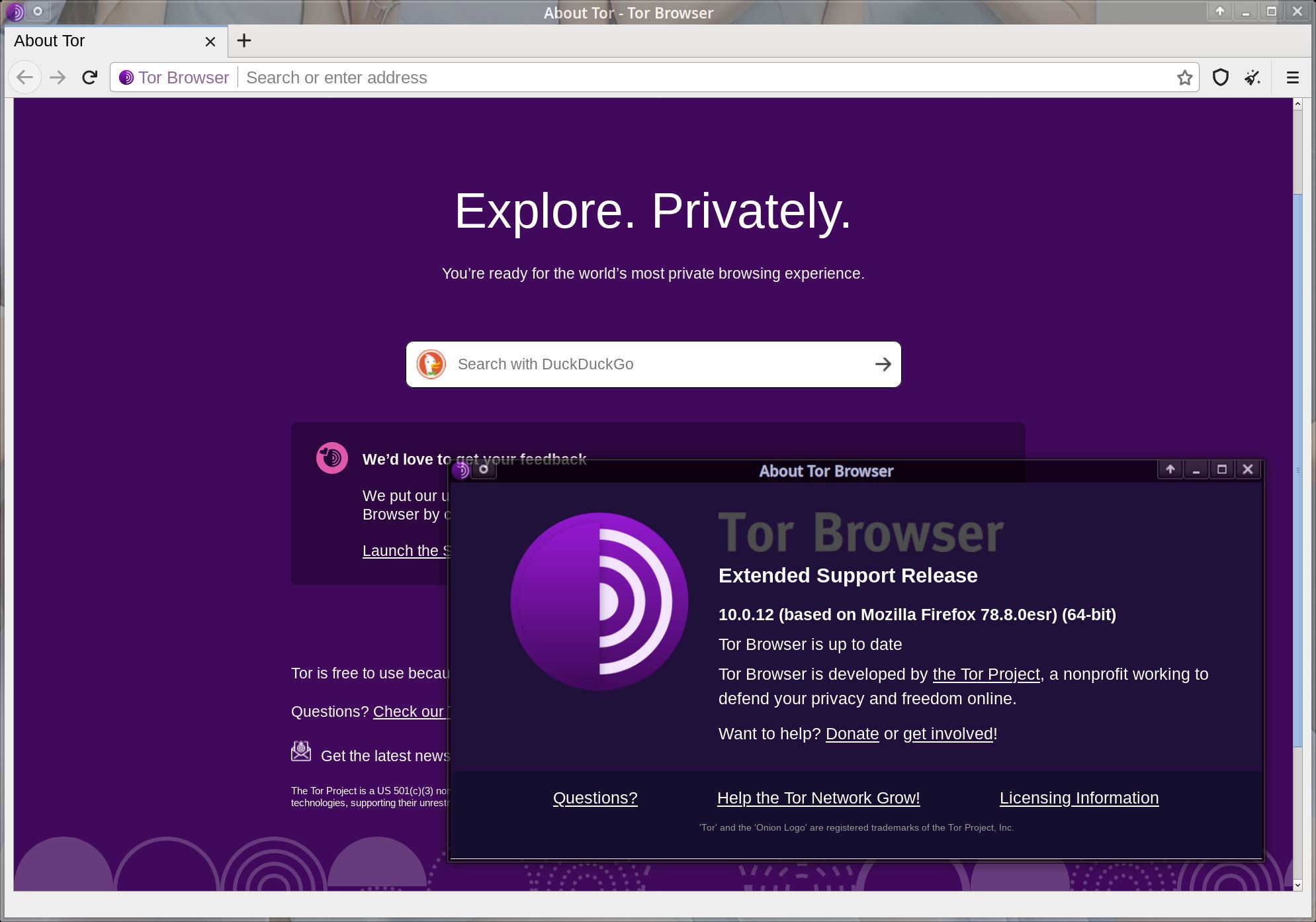
Navigating the TOR Browser
Navigating the TOR Browser is an essential aspect of maximizing its privacy and security features while exploring the internet. Upon launching the TOR Browser, users are greeted with a familiar interface, as it is based on the Firefox browser. However, there are key differences and additional functionalities that cater to the TOR network's unique characteristics.
User Interface
The TOR Browser's user interface is designed to be intuitive and user-friendly, allowing users to seamlessly access its privacy-enhancing features. The browser's toolbar provides quick access to essential functions, including navigating back and forward, refreshing pages, and managing bookmarks. Additionally, the TOR Browser incorporates a security slider, which allows users to adjust the browser's security settings based on their specific browsing needs.
TOR Circuit Establishment
One of the distinctive features of the TOR Browser is its ability to establish TOR circuits to anonymize internet traffic. When a user accesses a website, the TOR Browser creates a circuit by routing the connection through multiple relays, obscuring the user's original IP address. This process is crucial for maintaining anonymity and preventing websites from tracking the user's online activities.
Accessing .onion Websites
The TOR Browser enables users to access .onion websites, which are part of the dark web and are not indexed by traditional search engines. These websites often host content that is not easily accessible through standard web browsers. By entering .onion URLs into the TOR Browser's address bar, users can explore this hidden part of the internet while leveraging the browser's privacy features.
Managing Security Settings
In addition to its default privacy and security features, the TOR Browser allows users to fine-tune their security settings based on their preferences. Users can access the browser's security settings to customize features such as script blocking, cookie management, and HTTPS enforcement. These options empower users to tailor their browsing experience while maintaining a high level of privacy and security.
Private Browsing Mode
Similar to mainstream browsers, the TOR Browser offers a private browsing mode that does not retain browsing history, cookies, or site data after the session is closed. This feature is particularly valuable for users who seek to maintain a minimal digital footprint and prevent websites from tracking their online behavior.
Navigating the TOR Browser involves leveraging its unique functionalities to ensure a secure and private browsing experience. By familiarizing themselves with the browser's interface, TOR circuit establishment, access to .onion websites, security settings, and private browsing mode, users can harness the full potential of the TOR Browser while safeguarding their online privacy and anonymity.
Using TOR for Anonymity
Utilizing the TOR Browser for anonymity is a fundamental aspect of its functionality, empowering users to browse the internet without revealing their true identity or location. The TOR network achieves this by routing internet traffic through a series of encrypted relays, obscuring the user's IP address and making it challenging for adversaries to trace their online activities.
When a user accesses the internet through the TOR Browser, their connection is routed through a randomized pathway of relays, known as a TOR circuit. This process ensures that the user's original IP address is concealed, as each relay only knows the IP address of the preceding and subsequent relays in the circuit. As a result, websites and online services are unable to discern the user's true location or identity, bolstering their anonymity.
Furthermore, the TOR Browser's utilization of onion routing adds an additional layer of security and anonymity. Data transmitted through the TOR network is encrypted in multiple layers, akin to the layers of an onion, hence the name "onion routing." As the data passes through each relay in the TOR circuit, a layer of encryption is peeled off, revealing the routing information for the subsequent relay. This intricate process ensures that the user's internet traffic remains confidential and indistinguishable, enhancing their anonymity and privacy.
In addition to concealing the user's IP address, the TOR Browser facilitates access to websites that may be censored or restricted in certain regions. By leveraging the TOR network, users can circumvent internet censorship and access online content without revealing their true location, thereby safeguarding their freedom of information and expression.
It is important to note that while the TOR Browser provides robust anonymity features, users should exercise caution and employ best practices to maximize their privacy. This includes refraining from sharing personally identifiable information, avoiding the download of potentially malicious content, and being mindful of the websites visited while using the TOR Browser.
By harnessing the TOR Browser for anonymity, users can navigate the internet with a heightened sense of privacy and security. The TOR network's sophisticated routing and encryption mechanisms, coupled with the browser's user-friendly interface, empower individuals to browse the web without compromising their anonymity or exposing their digital footprint.
Security Features of the TOR Browser
The TOR Browser is renowned for its robust security features, which are meticulously designed to safeguard users' online activities and protect their privacy. These features are instrumental in creating a secure and anonymous browsing environment, empowering individuals to explore the internet without compromising their digital footprint.
Encryption and Anonymity
At the core of the TOR Browser's security architecture is its utilization of strong encryption and anonymization techniques. When a user accesses the internet through the TOR network, their data is encrypted and routed through a series of relays, obscuring their IP address and making it exceedingly difficult for adversaries to intercept or trace their online communications. This encryption ensures that sensitive information remains confidential and inaccessible to unauthorized entities, bolstering the user's privacy and security.
No Persistent Tracking
The TOR Browser is engineered to prevent persistent tracking of users' browsing activities. By default, the browser does not store browsing history, cookies, or site data after a session is terminated. This approach mitigates the risk of third-party tracking and minimizes the accumulation of digital footprints, enhancing users' privacy and anonymity while they navigate the web.
Security Slider
A distinctive feature of the TOR Browser is its built-in security slider, which empowers users to customize their security settings based on their specific browsing requirements. The security slider offers different levels of protection, allowing users to adjust the browser's security and privacy features to align with their preferences. This flexibility enables users to strike a balance between security and functionality, tailoring their browsing experience to suit their individual needs.
Protection Against Browser Fingerprinting
Browser fingerprinting is a technique used to track and identify users based on unique characteristics of their web browsers. The TOR Browser incorporates measures to mitigate browser fingerprinting, reducing the likelihood of users being uniquely identified and tracked across websites. By minimizing the exposure of identifying information, the browser enhances users' anonymity and shields them from pervasive tracking techniques.
Automatic HTTPS Everywhere
The TOR Browser includes the HTTPS Everywhere extension, which automatically encrypts connections to websites whenever possible. This feature ensures that data transmitted between the user's browser and websites is encrypted, mitigating the risk of eavesdropping and enhancing the overall security of online communications.
In summary, the TOR Browser's security features are integral to its mission of providing a private, secure, and anonymous browsing experience. By leveraging advanced encryption, privacy-enhancing settings, and protection against tracking techniques, the browser empowers users to navigate the internet with confidence, knowing that their online activities are shielded from prying eyes and potential threats.