Introduction
Welcome to the world of online privacy and security. With the rise of internet surveillance and data breaches, it’s no wonder that people are becoming more concerned about protecting their online activities and identities. Enter the Tor Browser, a powerful tool designed to offer privacy and anonymity to internet users.
Developed by the Tor Project, the Tor Browser is a modified version of the Mozilla Firefox web browser that connects to the Tor network. It allows users to browse the internet while keeping their online activities hidden from prying eyes, including internet service providers, government agencies, and even malicious hackers.
The Tor Browser is renowned for its ability to anonymize internet traffic by routing it through a series of cryptographic relays, making it difficult for anyone to trace back the user’s online activities to their physical location or identity. This makes it a popular choice for those seeking to protect their privacy or exercise their right to free speech.
Moreover, the Tor Browser provides access to the dark web, a part of the internet that is not indexed by search engines and requires special software to access. While the dark web has gained notoriety for its association with illegal activities, it also serves as a platform for promoting anonymity, whistleblowing, and human rights.
In this article, we will explore the safety of using the Tor Browser. We will delve into its features, examine its anonymity and security measures, assess the trustworthiness of the Tor network, discuss its ability to bypass censorship, and highlight its limitations and vulnerabilities. Additionally, we will provide some practical tips to minimize potential risks when using the Tor Browser.
What is the Tor Browser?
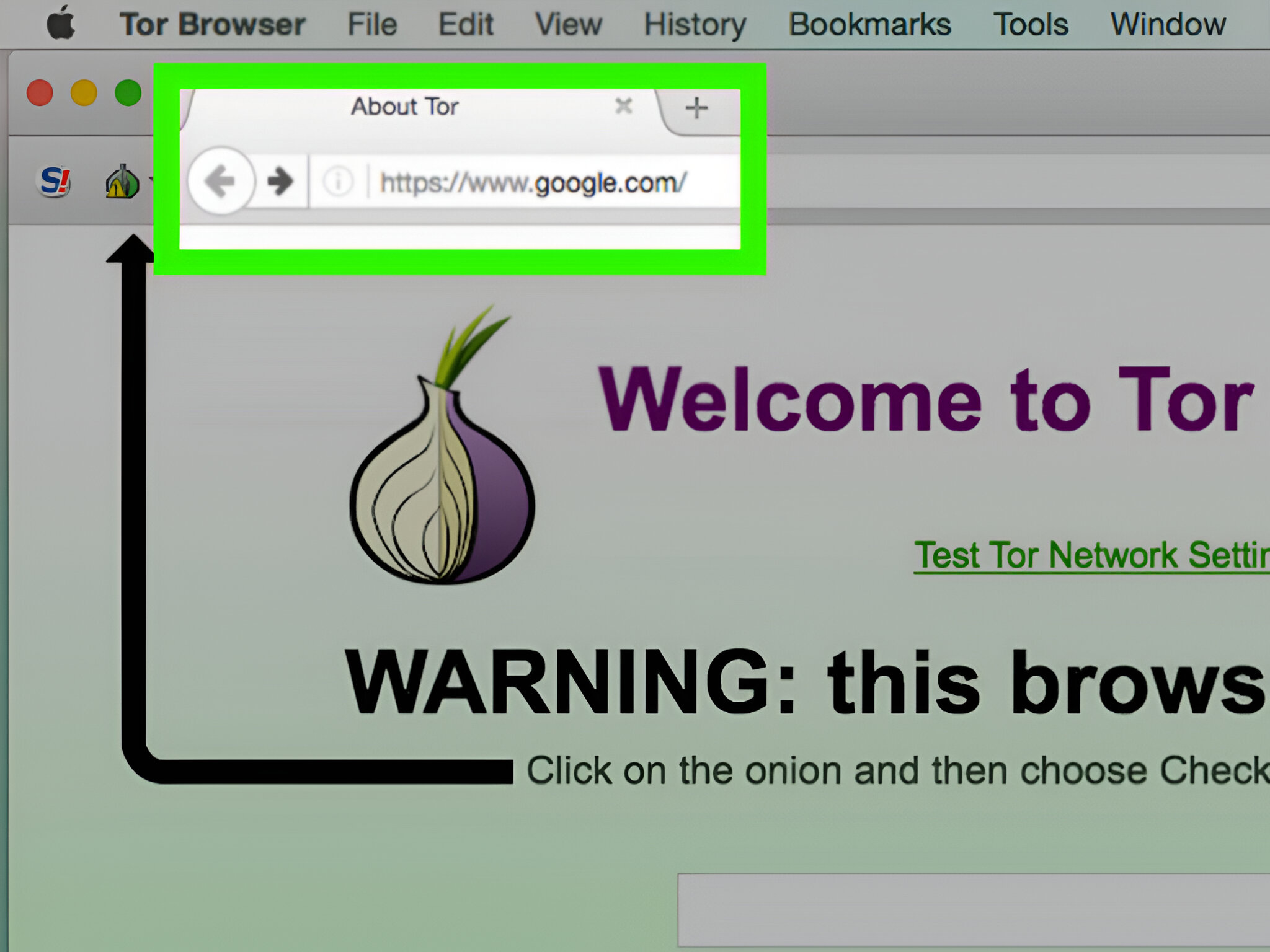
The Tor Browser is a web browser that allows users to browse the internet anonymously. It is based on the Mozilla Firefox browser and is specifically modified to provide enhanced privacy and security features. The key difference between the Tor Browser and other browsers is its connection to the Tor network.
The Tor network is a decentralized network of volunteer-operated servers or “relays” that work together to anonymize internet traffic. When you use the Tor Browser, your internet traffic is routed through a random selection of relays, encrypting your data and making it nearly impossible for anyone to track your online activities back to you.
Unlike other browsers, the Tor Browser employs a technique known as “onion routing.” This technique involves encapsulating data in layers of encryption like the layers of an onion. Each relay decrypts one layer until the final relay delivers the request to the intended website, safeguarding your identity and location every step of the way.
Another core feature of the Tor Browser is its ability to access the dark web. The dark web is a part of the internet that is not accessible through regular search engines. It requires special software, such as the Tor Browser, to access websites on the dark web. While the dark web has gained a reputation for illegal activities, it also serves as a platform for anonymous communication, whistleblower websites, and information sharing without censorship.
In addition to its privacy and anonymity features, the Tor Browser incorporates security measures to protect users from various online threats. It includes built-in defenses against tracking cookies, browser fingerprinting, and other techniques used to identify and track internet users. It also automatically clears your browsing history and cookies when you close the browser, leaving no trace of your activity on your device.
Overall, the Tor Browser is a powerful tool for internet privacy and security. By connecting to the Tor network and using its advanced encryption and routing techniques, users can browse the internet with a high degree of anonymity and protect their online activities from surveillance and monitoring.
Is the Tor Browser anonymous?
The Tor Browser is designed to provide users with a high level of anonymity while browsing the internet. It achieves this through the use of the Tor network and various privacy-enhancing features.
When you use the Tor Browser, your internet traffic is routed through a series of relays, making it extremely difficult to trace back to your physical location or identity. Each relay in the Tor network only knows the IP address of the relay it received the data from and the IP address it will send the data to next. This layered approach to routing data helps to anonymize your online activities.
Furthermore, the Tor Browser allows users to access the internet using a different IP address each time they connect. This helps to further protect your anonymity by preventing websites and online services from identifying and tracking you based on your IP address.
It is important to note, however, that while the Tor Browser provides a strong level of anonymity, it does not guarantee complete anonymity. No security tool or software can offer complete anonymity, as there are always potential vulnerabilities and risks.
One limitation of the Tor network is the possibility of a malicious exit relay. An exit relay is the final relay in the Tor network that delivers your data to its intended destination. If a malicious actor operates an exit relay, they could potentially monitor or modify your traffic. To mitigate this risk, the Tor network employs encryption and several safeguards, but there is always a small chance that a malicious exit relay could compromise your anonymity.
Additionally, while your internet traffic is anonymized through the Tor network, it is important to remember that your activities can still be traced if you engage in actions that reveal your identity, such as logging into personal accounts or providing personal information on websites. It is crucial to exercise caution and practice good online security hygiene even when using the Tor Browser.
In summary, the Tor Browser offers a high level of anonymity by routing your internet traffic through the Tor network and utilizing various privacy-enhancing features. While it is not completely foolproof and risks exist, it remains a powerful tool for protecting your online privacy and browsing the internet with a reduced risk of surveillance and tracking.
How secure is the Tor Browser?
The Tor Browser is designed with security in mind and incorporates several features to protect users from various online threats. However, it’s important to understand the limitations and vulnerabilities that exist.
One key aspect of the Tor Browser’s security is its use of encryption. When you use the Tor Browser, your internet traffic is encrypted and routed through multiple relays, making it difficult for anyone to intercept and decipher your data. This encryption helps to protect your communications from being intercepted or tampered with by malicious actors.
The Tor Browser also includes built-in defenses against tracking techniques, such as browser fingerprinting. Browser fingerprinting is a method used to identify and track internet users based on unique characteristics of their browser and device. The Tor Browser helps to mitigate this by making all users appear more similar, making it harder for websites to distinguish individual users.
Additionally, the Tor Browser provides a secure connection to websites that utilize HTTPS encryption. This ensures that your communications with websites are encrypted and cannot be easily intercepted or modified by third parties.
However, it’s important to note that the Tor Browser, like any software, is not immune to vulnerabilities and attacks. Zero-day exploits (previously unknown vulnerabilities), malware, and targeted attacks can still pose a threat to the security of the browser and its users.
Moreover, while the Tor network itself is designed to protect the privacy and security of users, it is not under the complete control of the Tor Project. The relays that make up the Tor network are operated by volunteers, and although there are measures in place to ensure their integrity, there is a possibility of compromised relays that could potentially compromise user security.
Therefore, it is crucial for users of the Tor Browser to keep their software up to date with the latest security patches and to exercise caution when accessing websites or downloading files. Users should also consider additional security measures such as using a virtual private network (VPN) in conjunction with the Tor Browser for an added layer of protection.
In summary, the Tor Browser incorporates various security features, including encryption, defenses against tracking techniques, and secure connections to websites. While it provides a robust level of security, it is important for users to stay vigilant, keep their software up to date, and take necessary precautions to minimize potential risks.
Can you trust the Tor network?
Trust is a critical factor when it comes to using the Tor network and relying on its services for privacy and anonymity. While the Tor network has been a valuable tool for countless users, it’s important to understand its limitations and make informed decisions about placing trust in it.
The Tor network is operated by a global community of volunteers who run relays, contributing their bandwidth and resources to make the network function. The code that powers the Tor network is open-source, allowing anyone to examine it for vulnerabilities and potential backdoors. This transparency has been a key factor in building trust among users.
Furthermore, the Tor Project, the organization behind the development and maintenance of the Tor network, has a strong reputation for prioritizing user privacy and security. They have taken steps to ensure the integrity and trustworthiness of the network by implementing mechanisms to detect and mitigate certain types of attacks and abuses.
However, it’s important to note that the Tor network, like any complex system, is not without its vulnerabilities and potential risks. While the network itself may be robust, there are other factors that can impact the trustworthiness of the Tor network.
One concern is the presence of potential malicious relays within the Tor network. Despite the efforts made to screen and monitor the relays, there is a possibility that some relays may be operated by malicious actors with the intent to intercept or tamper with users’ traffic. To minimize this risk, the Tor network implements encryption and routing techniques to protect users’ data even if a relay is compromised.
Another consideration is the possibility of external entities trying to infiltrate the network or compromise its security. Government agencies and intelligence organizations have been known to deploy tactics to target the Tor network in an effort to de-anonymize users. However, the Tor Project continuously works to identify and address these threats to maintain the integrity of the network.
Ultimately, whether or not you can trust the Tor network depends on your individual risk tolerance and the specific threat model you’re facing. While the Tor network provides a high level of anonymity and privacy, it is always important to consider the potential risks and take necessary precautions.
It’s recommended to stay informed about the latest developments and security practices related to the Tor network. By staying vigilant and employing good security practices, you can make informed decisions about whether to place trust in the Tor network and how to use it effectively to protect your online privacy.
Can Tor bypass censorship?
One of the key benefits of the Tor network is its ability to bypass censorship and access websites and services that may be blocked or restricted in certain countries or regions. However, the effectiveness of Tor in bypassing censorship can vary depending on the specific circumstances and methods employed by censors.
The Tor network achieves censorship circumvention by encrypting and routing internet traffic through a series of relays, making it difficult for censors to monitor or block access to specific websites or services. When you use the Tor Browser, your connections are typically hidden from external surveillance and censorship mechanisms.
This makes Tor particularly useful in regions where governments or other entities censor internet access, block specific websites, or monitor online activities. By using Tor, users may be able to access blocked content and services, communicate freely, and exercise their right to access information without fear of censorship or reprisal.
However, it’s important to note that some governments and organizations have taken measures to block or disrupt Tor traffic within their jurisdictions. They may employ advanced techniques to detect and throttle Tor connections or even block access to Tor relays. In such cases, Tor may not be as effective in bypassing censorship.
Another consideration is the availability of bridge relays within the Tor network. Bridge relays are unlisted or privately shared relays that can help users bypass censorship by providing alternative entry points into the Tor network. These bridges are designed to be more difficult to detect and block by censors.
It’s essential to stay updated with the latest information on bridge relays and their availability, particularly in regions where censorship is prevalent. The Tor Project regularly provides updated information and guidance on accessing and utilizing bridge relays in these circumstances.
It’s worth noting that while Tor can generally provide effective circumvention of censorship, there may be cases where the risks and consequences of accessing blocked content outweigh the benefits. Users should carefully assess the potential risks and consider the legal, social, and political implications before deciding to access censored content using Tor.
Overall, the Tor network can be a powerful tool for bypassing censorship, providing users with the ability to access blocked websites and services while protecting their privacy and anonymity. However, the effectiveness of Tor in circumventing censorship can vary depending on the specific circumstances and countermeasures employed by censors.
Limitations and vulnerabilities of the Tor Browser
While the Tor Browser offers unique privacy and anonymity features, it is important to be aware of its limitations and vulnerabilities. Understanding these can help users make informed decisions and take necessary precautions when using the Tor Browser.
One limitation of the Tor Browser is its potential impact on browsing speed. Because of the multiple relays that the traffic passes through, there can be a noticeable decrease in browsing speed compared to using a regular browser. This slowdown is a trade-off for the enhanced privacy and anonymity provided by the Tor network.
Another limitation is the compatibility issues with certain websites and services. Some websites may block or restrict access to users coming from the Tor network due to concerns about abuse or suspicious activities. This can be frustrating for users who rely on the Tor Browser for anonymity but need to access specific resources or services that are not Tor-friendly.
Furthermore, the Tor Browser does not provide complete protection against other weaknesses on the user’s device. For example, if your device is infected with malware, or if you have other software vulnerabilities, your privacy and security may still be at risk. It is important to maintain good security hygiene, such as keeping your operating system and other software up to date, and using reliable antivirus tools.
Additionally, the Tor Browser is not a solution for complete online anonymity if you engage in activities that can reveal your identity. For instance, if you provide personal information or log into accounts that can be linked back to you, your anonymity may be compromised. It’s important to be mindful of what you do online and exercise caution to avoid unintentionally exposing your identity.
Moreover, the Tor Browser is not designed to protect against end-to-end encryption vulnerabilities on websites themselves. If the website you are accessing is not properly secured, your data could still be intercepted or compromised despite using the Tor Browser. Users should ensure that they only access websites using HTTPS connections to maximize their security.
Finally, it’s worth noting that while the Tor network is continuously monitored and maintained by the Tor Project for potential vulnerabilities, no system can claim to be completely invulnerable. New attacks or vulnerabilities may emerge, requiring prompt updates and patches from the Tor Project to address them.
Understanding these limitations and vulnerabilities can help users make informed decisions and take appropriate precautions while using the Tor Browser. By staying vigilant, keeping software up to date, and employing good security practices, users can minimize potential risks and make the most of the privacy and anonymity provided by the Tor network.
Risks and precautions when using the Tor Browser
While the Tor Browser is a powerful tool for protecting online privacy and anonymity, it is crucial to be aware of the risks involved and take necessary precautions to mitigate them. Understanding and addressing these risks can help users navigate the Tor network safely:
1. Malicious exit relays: Although rare, there is a possibility of a malicious exit relay intercepting your traffic. To mitigate this risk, ensure that you only access websites using HTTPS to enable end-to-end encryption, reducing the likelihood of interception.
2. Downloading files and opening attachments: Be cautious when downloading files or opening attachments while using the Tor Browser. Malicious files can still pose a threat to your device, compromising your privacy and security. only download files from trusted sources and scan them for malware before opening them.
3. Phishing attacks: Stay vigilant against phishing attempts that may target you while using the Tor Browser. Be cautious about sharing sensitive information or clicking on suspicious links. Verify the websites or services you are using to prevent falling for phishing scams.
4. Timing attacks and correlation attacks: While the Tor network anonymizes your internet traffic and IP address, sophisticated adversaries may attempt timing attacks or correlation attacks to deanonymize users. To mitigate these risks, consider using additional security measures, such as VPN services or virtual machines, to further obfuscate your online activities.
5. Avoid logging into personal accounts: To maintain your anonymity, avoid logging into personal online accounts or providing personal information while using the Tor Browser. Logging into accounts linked to your real identity can compromise your anonymity and privacy.
6. Be mindful of website credibility: Be cautious when accessing websites on the Tor network, as not all websites are trustworthy. Websites on the dark web, in particular, can host illegal activities and scams. Exercise caution and use common sense when visiting unfamiliar websites.
7. Reveal as little identifying information as possible: Minimize the amount of personally identifiable information you share while using the Tor Browser. Be cautious about revealing personal details, such as your name, address, or contact information, as this information can be used to compromise your privacy and anonymity.
8. Keep your Tor Browser up to date: The Tor Project regularly releases updates and security patches to address vulnerabilities and improve the overall security of the Tor Browser. It is crucial to keep your browser updated to ensure you benefit from the latest security enhancements.
By understanding and following these precautions, users can minimize potential risks and stay safer while using the Tor Browser. Remember that no security tool can provide absolute protection, so it is essential to use the Tor network responsibly and stay informed about the latest security practices.
Conclusion
The Tor Browser offers users a powerful tool for enhancing online privacy and anonymity. With its ability to route internet traffic through the Tor network, the browser provides a layer of encryption and obfuscation that helps protect users from surveillance, censorship, and tracking.
While the Tor Browser is not without its limitations and vulnerabilities, it remains a popular choice for those seeking to protect their online activities. It offers a way to bypass censorship, access the dark web, and browse the internet with a reduced risk of identification.
However, it is important to approach the use of the Tor Browser with a clear understanding of its capabilities and limitations. Users should be aware of the potential risks, such as the presence of malicious exit relays and the possibility of targeted attacks. By practicing good security hygiene, users can mitigate some of these risks and make the most of the privacy and anonymity features that the Tor Browser provides.
It’s also important to note that the Tor Browser is just one tool in a larger arsenal of privacy and security measures. It should be used in conjunction with other best practices, such as using strong and unique passwords, enabling two-factor authentication, and regularly updating software.
In summary, the Tor Browser offers an important solution for individuals seeking to protect their online privacy and navigate the internet with a reduced risk of surveillance and tracking. By understanding its features, practicing caution, and taking necessary precautions, users can leverage the benefits of the Tor Browser and enjoy a safer and more private online experience.