Introduction
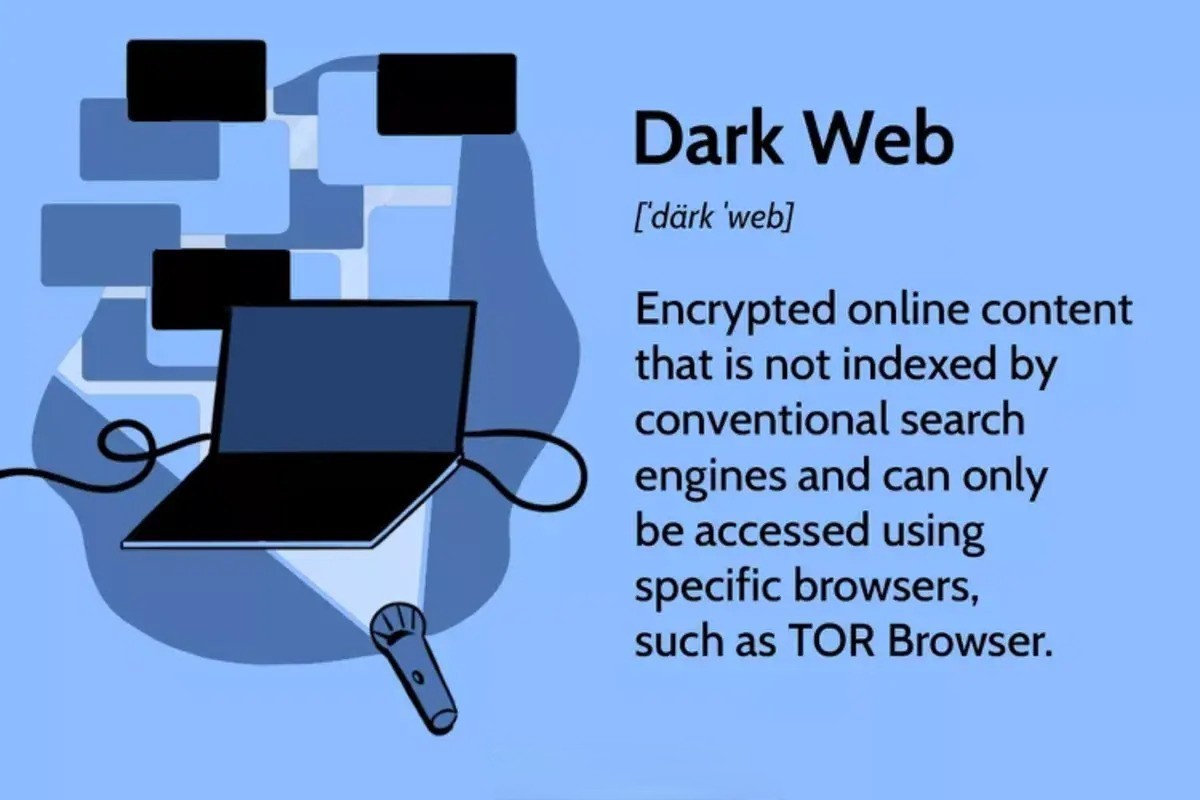
The dark web has gained notoriety in recent years, becoming synonymous with hidden marketplaces, cybercriminal activities, and anonymous browsing. It is a part of the internet that is not indexed by search engines and can only be accessed through specific software and configurations. One such software is the Tor Browser.
The dark web is often misunderstood due to the illegal activities that occur within its depths. However, it’s important to note that not everything on the dark web is illegal. Journalists, activists, and individuals concerned about privacy and censorship often use the dark web to communicate securely and anonymously. Nevertheless, caution should always be exercised when venturing into this hidden realm.
The Tor Browser is a powerful tool that enables users to access the dark web while maintaining their anonymity. It routes internet traffic through a network of volunteer-operated servers, concealing the user’s IP address and encrypting their communications. By using the Tor Browser, individuals can browse websites on the dark web without exposing their identities.
In this article, we will guide you through the process of getting on the dark web using the Tor Browser. We will discuss the setup procedure, ensuring security and anonymity, and offer tips for navigating the dark web safely. It’s essential to follow these guidelines to protect yourself and your personal information when exploring the depths of the internet.
What is the Dark Web?
The dark web is a hidden part of the internet that is not accessible through traditional search engines like Google or Bing. It is a network of websites and online services that can only be accessed through specific software and configurations.
Unlike the surface web, which consists of websites and content that are indexed and easily accessible, the dark web operates on encrypted networks, providing users with a high degree of anonymity. It uses technology like onion routing to hide users’ identities and encrypt their communications.
Within the dark web, there are various hidden websites, known as darknet markets, where illicit goods and services are bought and sold. These can include drugs, weapons, stolen data, and even hacking services. It is important to note, however, that not all activities on the dark web are illegal. Many individuals use it to communicate securely and anonymously or to access information that may be restricted or censored in their countries.
The dark web operates on a different system of domains called “onion domains.” These domains are not accessible through regular browsers, as they have unique addresses that end with “.onion.” To access these sites, users need to use a specialized browser like Tor.
It is essential to understand that while the dark web may harbor illicit activities, it is not representative of the internet as a whole. The vast majority of online content and services exist on the surface web, and the dark web represents only a small portion of the internet.
It is crucial to approach the dark web with caution and understand the risks involved. Engaging in illegal activities can lead to severe consequences, and exposing personal information or engaging with malicious individuals can compromise your privacy and security.
What is Tor Browser?
Tor Browser is a web browser that allows users to access the internet anonymously. It is built on the Tor network, which stands for “The Onion Router.” The Tor network routes internet traffic through a series of volunteer-operated servers, encrypting the data and making it extremely difficult to trace the user’s online activities.
Using Tor Browser, individuals can browse the internet with a higher level of privacy and anonymity. It masks the user’s IP address, making it difficult for websites, internet service providers, and other entities to track their online behavior.
One of the key features of Tor Browser is its ability to access the dark web. By using Tor Browser, individuals can navigate websites on the dark web that are not accessible through regular browsers. It allows users to explore hidden marketplaces, access encrypted messaging services, and browse content that may not be available through traditional means.
Tor Browser is available for multiple operating systems, including Windows, macOS, Linux, and Android. It is free to download and use, with the goal of promoting online privacy and freedom of expression.
When using Tor Browser, it is important to note that while it provides a higher level of anonymity, it does not guarantee complete protection. It is still possible for malicious actors to monitor online activities, especially if users engage in unsafe browsing practices or download suspicious files.
One additional feature of Tor Browser is its emphasis on privacy and security. It automatically blocks websites from tracking users, disables potentially dangerous plugins, and clears cookies and browsing history after each session. These features help maintain privacy and reduce the risk of tracking by third-party entities.
Overall, Tor Browser provides individuals with a means to browse the web and access the dark web securely and anonymously. It is a valuable tool for those who prioritize privacy and wish to explore the depths of the internet while mitigating the risks associated with online activities.
Getting Started with Tor Browser
If you’re ready to explore the dark web and browse the internet anonymously, follow these steps to get started with Tor Browser:
- Download Tor Browser: Visit the official Tor Project website (https://www.torproject.org) and download the appropriate version of Tor Browser for your operating system. Make sure to download it from the official source to avoid any potentially malicious versions.
- Install Tor Browser: Once the download is complete, open the installer and follow the on-screen instructions to install Tor Browser on your device. The installation process is straightforward, and you can customize some settings based on your preferences.
- Launch Tor Browser: After the installation is complete, launch the Tor Browser. You may need to grant permission for the browser to access your network connections. Once the browser is launched, it will connect to the Tor network, encrypting your internet traffic and providing you with anonymity.
- Configure Tor Browser (Optional): Tor Browser comes pre-configured for optimal privacy and security. However, you can customize some settings by clicking on the Tor Browser menu in the top-right corner and selecting “Preferences.” Here, you can adjust privacy settings, control cookie behavior, and more.
- Start Browsing: With Tor Browser up and running, you can start browsing the web anonymously. To access the dark web, enter a “.onion” URL in the address bar or use a directory website that lists dark web sites. Remember to exercise caution and be mindful of the potential risks associated with the dark web.
It’s important to note that Tor Browser may run slower than traditional browsers due to the encryption and multiple relays used to route your internet traffic. This is a trade-off for the increased privacy and anonymity it provides.
Additionally, always keep your Tor Browser up to date to benefit from the latest security enhancements and bug fixes. Regularly check the Tor Project’s website for updates and install them promptly.
By following these steps, you are on your way to exploring the hidden depths of the internet and enjoying a heightened level of online privacy and anonymity.
Setting Up Tor Browser
Setting up Tor Browser is a straightforward process that involves downloading and installing the software. To ensure a smooth setup, follow these steps:
- Select the Right Version: Visit the official Tor Project website (https://www.torproject.org) and download the appropriate version of Tor Browser for your operating system. Make sure to choose the correct version (Windows, macOS, Linux, or Android) to ensure compatibility.
- Download the Installer: Once you’ve selected the correct version, click on the download link to start downloading the Tor Browser installation file. This may take a few minutes depending on your internet speed.
- Run the Installer: Once the download is complete, locate the downloaded file and run the installer. You may need to confirm your system’s security prompts to proceed with the installation.
- Choose Installation Options: During the installation process, you will be presented with some options to customize your installation. You can choose the language, installation location, and whether you want to create shortcuts. Make your desired selections and proceed with the installation.
- Wait for Installation: The installer will now extract and install the necessary files for Tor Browser. This process may take a few minutes. Once the installation is complete, you will see a confirmation message.
- Launch Tor Browser: After the installation, you can launch Tor Browser by clicking on the “Finish” button or locating the Tor Browser icon on your desktop or in the Applications folder.
- Configure Tor Network: Upon launching Tor Browser for the first time, you will be prompted to configure your Tor network settings. By default, Tor Browser connects to the Tor network automatically. Ensure that the settings are correctly configured and click on “Connect” to establish a connection.
After completing these steps, Tor Browser will open, and you will be ready to start browsing the internet anonymously. Tor Browser is pre-configured with privacy settings optimized for secure browsing, so you can enjoy a higher level of anonymity right from the start.
It’s important to note that you should always download Tor Browser from the official Tor Project website to ensure that you are getting the legitimate and safe version. Be cautious of downloading it from unofficial sources, as they may provide modified versions that could compromise your security.
By following these setup instructions, you can ensure a smooth installation and configuration process, allowing you to reap the benefits of Tor Browser and browse the internet anonymously.
Accessing the Dark Web
Accessing the dark web requires the use of Tor Browser, which provides the necessary anonymity and encryption to navigate hidden websites. Here’s a step-by-step guide on how to access the dark web:
- Launch Tor Browser: After installing Tor Browser on your device, open the browser.
- Connect to the Tor Network: When you open Tor Browser, it automatically connects to the Tor network, which is necessary for accessing the dark web. Wait for the connection to be established before proceeding.
- Enter a Dark Web URL: To access a specific dark web website, enter its exact “.onion” address in the address bar. These addresses are unique to the dark web and typically consist of a string of letters and numbers followed by “.onion.”
- Explore Dark Web Directories: If you do not have a specific dark web website in mind, you can explore directories that list popular dark web sites. Some well-known directories include The Hidden Wiki and TorLinks. These directories provide links to various dark web websites, enabling you to browse different categories and find sites of interest.
- Exercise Caution: When accessing the dark web, it’s crucial to exercise caution and be aware of potential risks. The dark web is known for hosting illegal activities, including the sale of drugs and stolen data, so be mindful of the content you encounter. Avoid clicking on suspicious links or engaging in illegal activities.
- Maintain Anonymity: While Tor Browser helps protect your identity, it’s important to take additional measures to maintain your anonymity on the dark web. Avoid providing personal information, use virtual private networks (VPNs) for added security, and ensure that your Tor Browser settings are optimized for privacy.
It’s important to note that not all websites on the dark web are illegal or malicious. Some hidden sites are used for legitimate purposes, such as private communication, whistleblower platforms, and forums for activism and free speech. However, due to the nature of the dark web, it’s wise to approach any site with caution and discernment.
Remember, security and privacy should be your top priority when accessing the dark web. Stay vigilant, avoid engaging in illegal activities, and be mindful of the potential risks associated with exploring this hidden part of the internet.
Ensuring Security and Anonymity
When accessing the dark web, it is crucial to prioritize security and anonymity to protect yourself from potential risks and threats. Here are some important measures to help ensure your online safety:
- Keep Tor Browser Updated: Regularly check for updates to Tor Browser and install them promptly. Updates often include security enhancements and bug fixes, providing better protection against potential vulnerabilities.
- Use VPN Services: Consider using a virtual private network (VPN) in conjunction with Tor Browser. A VPN encrypts your internet connection, adding an extra layer of security and making it even more challenging for anyone to track your online activities.
- Disable JavaScript: Disable JavaScript in your Tor Browser settings. While JavaScript can enhance website functionality, it can also be exploited by malicious actors. Disabling it reduces the risk of potentially harmful scripts running on your device.
- Be Wary of Downloads: Avoid downloading files from unknown sources while browsing the dark web. Malicious files and malware can compromise your device’s security and expose your personal information. Only download files from trusted sources and use strong antivirus software to scan any downloaded files.
- Don’t Disclose Personal Information: Never provide personal information or share personally identifiable details while accessing the dark web. Be cautious of any website or person requesting sensitive information. Remember, the dark web is notorious for illicit activities, and exposing personal information can lead to identity theft or other harmful repercussions.
- Secure Your Device: Ensure that your device has up-to-date security software, including antivirus and firewall protection. Regularly scan your device for malware and other potential threats. Additionally, use strong, unique passwords and enable two-factor authentication for your online accounts.
- Practice OpSec: Operational Security, or OpSec, involves taking measures to protect your identity and activities online. Avoid using personal usernames or identifiable information on the dark web. Adopt pseudonyms or anonymous aliases to maintain your anonymity.
- Be Mindful of Online Behavior: When using the dark web, be cautious of the websites you visit and the interactions you engage in. Avoid clicking on suspicious links or engaging in illegal activities. Trust your instincts and use common sense to protect yourself from potential harm.
By implementing these security measures, you can significantly enhance your online safety while accessing the dark web. However, it’s important to understand that no system or practice can offer absolute security. Always exercise caution and stay informed about the latest security practices to mitigate risks effectively.
Navigating the Dark Web
Navigating the dark web requires some familiarity with its unique ecosystem. Here are some tips to help you navigate and explore this hidden part of the internet:
- Use Dark Web Directories: Dark web directories can serve as a starting point for discovering hidden websites. These directories categorize various dark web sites, making it easier to find specific content or services. Explore directories like The Hidden Wiki or TorLinks to discover different categories of sites.
- Utilize Search Engines: Dark web search engines can help you find specific information or sites of interest. These search engines index hidden services on the dark web, allowing you to search for keywords or topics. However, be cautious when using search engines, as the dark web is filled with illicit content, and not all search results may be legitimate or safe.
- Join Dark Web Communities: Online forums and communities exist on the dark web where users can discuss various topics or share information. These communities can provide insights, advice, and access to exclusive content within the hidden corners of the internet.
- Verify Sites and Sellers: When accessing dark web marketplaces or engaging with services, it’s vital to verify the reputation and trustworthiness of sites and sellers. Look for user reviews, ratings, and feedback to ensure a safer and more reliable experience.
- Be Mindful of Illicit Activities: While not all content on the dark web is illegal, be aware that illicit activities do occur. Exercise caution and avoid engaging in any illegal activities or purchasing illegal goods or services. Remember that illegal actions can have severe legal consequences.
- Exercise Discretion: As you navigate the dark web, be mindful of the information you share and the interactions you have. Protect your identity and avoid disclosing personal information or engaging in discussions that may compromise your safety or security.
- Stay Updated on Security Practices: The dark web is not a static environment; new vulnerabilities and risks emerge regularly. Stay informed about the latest security practices, utilize updated software, and follow online communities or forums dedicated to dark web security.
- Educate Yourself: Take the time to educate yourself about the dark web and its workings. Understand the technology behind it, the risks involved, and the potential legal implications. Educating yourself will help you make informed decisions and stay safe.
Remember, the dark web can be a treacherous place, and caution should always be exercised. While there may be legitimate uses and valuable information available, it’s essential to be aware of the potential risks and adhere to ethical behavior while exploring the hidden corners of the internet.
Tips for Using the Dark Web Safely
Using the dark web can be a daunting experience, but with the right approach, you can navigate it safely. Here are some essential tips to help you use the dark web responsibly and protect your online security:
- Use Strong Anonymity Measures: When accessing the dark web, always use the Tor Browser to maintain anonymity and protect your identity. Combine it with a reliable VPN service for an extra layer of security.
- Stay Up-to-Date with Tor Browser: Keep your Tor Browser updated with the latest version and security patches. Updates often address vulnerabilities and improve overall performance and security.
- Be Cautious of Phishing Attempts: Be wary of any links or messages that ask for personal information. Avoid clicking on suspicious links, as they may lead to phishing websites designed to steal your credentials or compromise your security.
- Secure Your Device: Ensure that your operating system, antivirus software, and other security measures are up to date. Regularly scan your device for malware and potential threats.
- Disable Plugins and JavaScript: Disable unnecessary plugins and JavaScript in your Tor Browser settings. This reduces the risk of potential vulnerabilities and malicious scripts running on your device.
- Use Encryption: Whenever possible, utilize encryption methods for communication and data storage. Encrypted messaging services and virtual private networks (VPNs) can provide an additional layer of protection for your sensitive information.
- Handle Cryptocurrency with Caution: If you engage in financial transactions on the dark web, be cautious when using cryptocurrencies. Understand the risks associated with their use and ensure that you are dealing with reputable and trusted sellers.
- Keep Personal Information Private: Refrain from providing any personal information while using the dark web. Avoid disclosing your real name, address, phone number, or other identifying details.
- Trust Your Instincts: Use good judgment and trust your instincts when navigating the dark web. If something seems suspicious or too good to be true, it likely is. Exercise caution and always prioritize your safety.
- Avoid Illegal Activities: Engaging in any illegal activities on the dark web can have severe legal consequences. Avoid purchasing illegal goods or services, participating in hacking activities, or any actions that may be deemed illegal.
Remember, while these tips can significantly enhance your safety and security, there is no foolproof method to eliminate all risks. Practice discretion, stay informed about current security practices, and always prioritize your online safety when using the dark web.
Conclusion
The dark web, accessed through the anonymous browsing capabilities of Tor Browser, has gained both fascination and notoriety. While it is often associated with illicit activities, it’s important to remember that not everything on the dark web is illegal or malicious. It can be a haven for those seeking privacy, censorship circumvention, and secure communication. However, using the dark web requires caution and adherence to responsible online practices.
In this article, we have explored what the dark web is and how Tor Browser provides the necessary anonymity and encryption to access it. We discussed the importance of setting up Tor Browser correctly, ensuring security and anonymity, and navigating the dark web safely. By following these guidelines, you can minimize the potential risks and protect your online privacy while exploring the depths of the internet.
Remember, always prioritize your online safety and exercise caution when accessing the dark web. Be aware of the potential risks associated with engaging in illegal activities or providing personal information. Regularly update your software, use encryption methods, and stay informed about the latest security practices to mitigate potential threats.
Ultimately, the dark web can be a place of great intrigue, but it’s essential to approach it responsibly. It is a realm that demands both mindfulness and education about the risks and ethical considerations involved. With the right knowledge and precautions, you can explore the dark web with enhanced privacy and security.