Introduction
Welcome to the world of home network attached storage (NAS)! In this digital age, where we accumulate vast amounts of data, having a centralized storage solution at home has become increasingly essential. NAS devices offer a convenient and secure way to store, access, and manage your files, whether they are family photos, important documents, or media libraries. Setting up a home NAS can seem daunting at first, but with the right guidance, you can create your own personal cloud storage solution that fits your specific needs.
In this comprehensive guide, we will walk you through the process of setting up a home network attached storage system. From choosing the right NAS device to securing your network, we will cover each step in detail, ensuring that you have the knowledge and confidence to embark on this exciting endeavor.
Whether you are a tech enthusiast looking to expand your home network or a casual user seeking a reliable storage solution, this guide is tailored to meet your needs. By the end of this journey, you will be equipped with the skills to set up and maintain a home NAS that enhances your digital lifestyle.
So, let's dive in and explore the world of home network attached storage, where convenience, accessibility, and security converge to redefine the way you store and access your valuable data.
Choosing the Right NAS Device
When embarking on the journey of setting up a home network attached storage system, selecting the right NAS device is a crucial first step. With a myriad of options available in the market, it’s essential to consider your specific requirements and preferences to make an informed decision.
Factors to Consider:
- Storage Capacity: Assess your storage needs, including current and future requirements. Determine the amount of data you intend to store and consider scalability options for potential expansion.
- Number of Bays: NAS devices come with varying numbers of drive bays, typically ranging from single-bay to multi-bay configurations. Single-bay NAS devices are suitable for basic storage needs, while multi-bay systems offer RAID configurations and increased redundancy.
- Performance and Features: Evaluate the processing power, memory, and additional features such as transcoding, virtualization support, and hardware encryption. Consider the intended usage, whether it’s for media streaming, backup, or hosting applications.
- Connectivity Options: Assess the available ports, including USB, Ethernet, and expansion slots. Consider the compatibility with your existing network infrastructure and the potential for future connectivity needs.
- Manufacturer and Support: Research the reputation of the NAS manufacturer, including the availability of regular firmware updates, technical support, and warranty coverage.
Types of NAS Devices:
There are various categories of NAS devices catering to different user requirements:
- Entry-Level NAS: Ideal for personal use and small businesses, offering basic features and affordable pricing.
- Prosumer NAS: Designed for enthusiasts and power users, providing enhanced performance, scalability, and advanced features.
- Enterprise NAS: Tailored for large-scale storage needs in corporate environments, offering high-performance capabilities, extensive scalability, and enterprise-grade features.
By carefully considering these factors and understanding the types of NAS devices available, you can narrow down your options and select a device that aligns with your storage requirements, performance expectations, and budget constraints.
Choosing the right NAS device sets the foundation for a robust and efficient home network attached storage solution, empowering you to store and access your data seamlessly within your home network environment.
Setting Up the Physical Hardware
Once you have carefully chosen the NAS device that suits your requirements, the next step is to set up the physical hardware in your home environment. This involves positioning the NAS device, connecting it to your network, and ensuring proper ventilation and physical security.
Placement and Ventilation:
Choose an appropriate location for your NAS device, considering factors such as accessibility, ventilation, and proximity to power and network connections. Ensure that the chosen location allows for adequate airflow to prevent overheating, as NAS devices can generate heat during operation. Additionally, consider placing the NAS on a stable surface to minimize vibrations and impact.
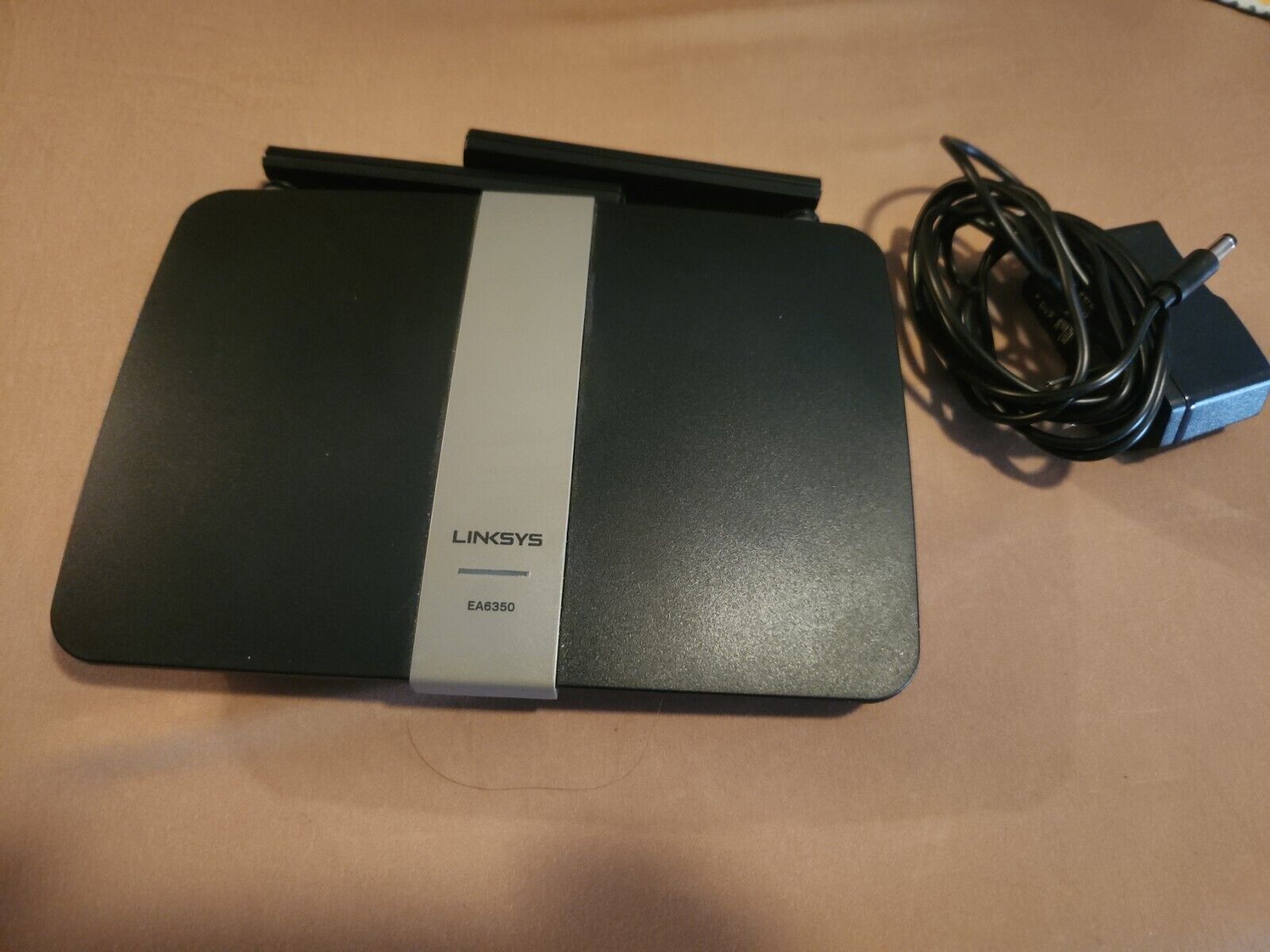
Network Connectivity:
Connect the NAS device to your home network using Ethernet cables or wireless connectivity, depending on the capabilities of your NAS and network infrastructure. Ensure that the network connection is stable and capable of handling the data transfer requirements of your NAS, especially if you plan to use it for media streaming, file sharing, or backup purposes.
Power Supply and Surge Protection:
Connect the NAS device to a reliable power source and consider using surge protectors or uninterruptible power supplies (UPS) to safeguard the device from power fluctuations and outages. This is essential for maintaining the integrity of your stored data and ensuring continuous access to the NAS, especially during unexpected power events.
Physical Security:
Implement measures to secure the physical integrity of your NAS device, especially if it contains sensitive or critical data. This may include using locking cabinets, cable locks, or positioning the NAS in a secure area to prevent unauthorized access or tampering.
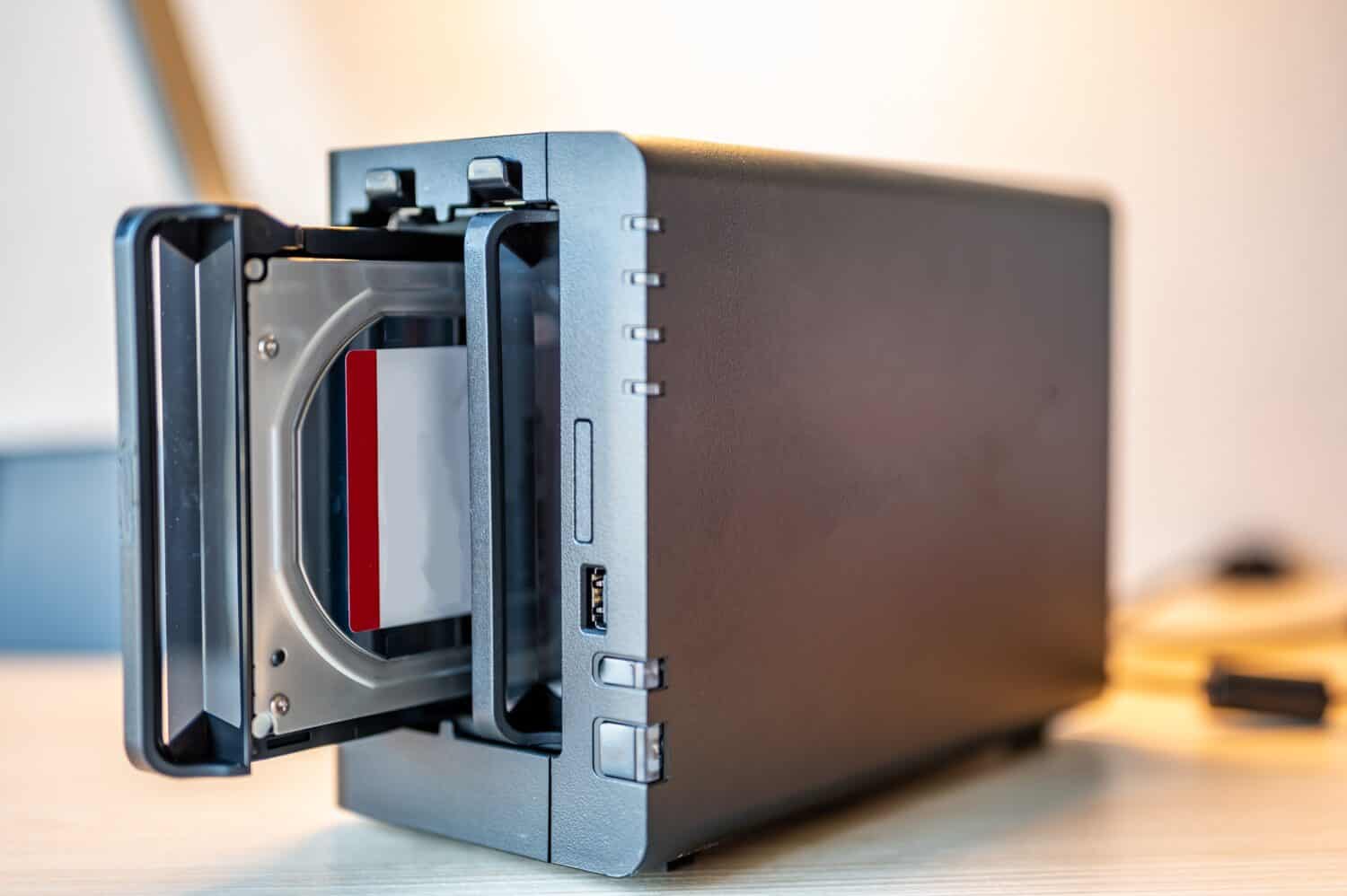
Initial Hardware Configuration:
Follow the manufacturer’s guidelines to perform the initial hardware setup, which may involve installing hard drives, configuring drive bays, and ensuring that all physical connections are secure. Pay attention to any specific hardware setup instructions provided by the manufacturer to ensure proper installation and functionality.
By meticulously setting up the physical hardware of your NAS device, you lay the groundwork for a reliable and efficient storage solution within your home network. Attention to placement, connectivity, power management, and security measures contributes to the overall stability and performance of your home network attached storage system.
Installing and Configuring the NAS Software
With the physical hardware set up, the next pivotal step in establishing your home network attached storage system is installing and configuring the NAS software. This software, often provided by the NAS manufacturer, enables you to manage the storage, access controls, and additional features of your NAS device.
Initial Setup and Access:
Begin by accessing the NAS device through a web-based interface or dedicated software provided by the manufacturer. This interface allows you to perform the initial setup, including configuring network settings, creating user accounts, and defining storage volumes.
Storage Configuration:
Create storage volumes and file systems based on your storage requirements and redundancy preferences. Depending on the NAS device and software, you may have options for RAID configurations, which provide data protection and fault tolerance in case of drive failures. Consider the balance between storage capacity, performance, and redundancy when configuring your storage volumes.
Access Control and Permissions:
Define access controls and user permissions to regulate who can access specific folders, files, or services on the NAS. This step is crucial for maintaining data security and privacy within your home network. Consider creating separate user accounts with tailored permissions for different family members or users within your network.
Remote Access and Cloud Services:
Explore the options for remote access and cloud services provided by the NAS software. Many NAS devices offer features that enable you to access your stored data from outside your home network, providing a convenient way to retrieve files or manage the NAS while on the go. Ensure that you follow best practices for securing remote access to prevent unauthorized entry into your home network.
Additional Features and Applications:
Explore and configure any additional features or applications offered by the NAS software, such as media servers, backup utilities, and third-party integrations. These features can enhance the functionality of your NAS and cater to specific use cases, such as media streaming, automated backups, or hosting personal websites.
By meticulously installing and configuring the NAS software, you unlock the full potential of your home network attached storage system. The software empowers you to manage your data, control access, and leverage additional features, transforming your NAS into a versatile and indispensable asset within your home network environment.
Connecting and Accessing Your NAS
Once the NAS hardware and software are set up, the next crucial step is to establish connections and ensure seamless access to your network attached storage within your home environment. This involves connecting devices to the NAS, accessing files and services, and integrating the NAS into your daily digital activities.
Network Mapping and Drive Mounting:
On your computer or other devices, map the network drive or mount the NAS storage to establish a direct link between your device and the NAS. This allows you to access the NAS storage as if it were a local drive, enabling seamless file operations and data transfers.
Media Streaming and Sharing:
If your NAS supports media streaming, configure the necessary settings to enable streaming of music, videos, and other multimedia content to compatible devices within your home network. This transforms your NAS into a media hub, allowing you to enjoy your digital content on various screens and audio systems throughout your home.
Backup and Synchronization:
Set up backup and synchronization routines to safeguard your important data. Many NAS devices offer built-in backup utilities and support for popular synchronization protocols, allowing you to create redundant copies of your files and ensure data consistency across multiple devices.
Mobile and Remote Access:
Explore the options for accessing your NAS from mobile devices and remote locations. Install dedicated apps or configure remote access features provided by the NAS manufacturer to securely access your stored data while on the go. This extends the utility of your NAS beyond your home network, providing flexibility and convenience in managing your digital assets.
Integration with Applications and Services:
Integrate the NAS into your existing applications and services, such as media players, file management tools, and backup software. Ensure seamless interoperability between your devices and the NAS, allowing for effortless data access and utilization across your digital ecosystem.
By establishing connections and enabling access to your NAS, you seamlessly integrate the storage solution into your digital lifestyle, unlocking its full potential to store, stream, and protect your valuable data within your home network environment.
Securing Your Home Network Attached Storage
Ensuring the security of your home network attached storage (NAS) is paramount to safeguarding your valuable data and maintaining the integrity of your digital environment. By implementing robust security measures, you can mitigate potential risks and fortify your NAS against unauthorized access, data breaches, and other security threats.
Network Segmentation and Firewall Configuration:
Consider segmenting your home network to create a dedicated network zone for your NAS, isolating it from other devices and services. Configure firewall rules to restrict incoming and outgoing traffic to the NAS, enhancing its resilience against external threats and unauthorized access attempts.
Strong Authentication and Access Controls:
Enforce strong password policies for accessing the NAS and implementing multi-factor authentication where available. Create individual user accounts with granular access permissions, ensuring that each user only has access to the data and services relevant to their needs within the NAS environment.
Regular Software Updates and Patch Management:
Stay vigilant about installing software updates and security patches provided by the NAS manufacturer. Regularly updating the NAS software and firmware helps address known vulnerabilities and ensures that the device remains resilient against emerging security threats.
Data Encryption and Secure Transmission:
Enable data encryption for sensitive data stored on the NAS and ensure that data transmission between devices and the NAS occurs over secure channels. Utilize protocols such as HTTPS, SFTP, or VPN connections to encrypt data in transit, preventing unauthorized interception and tampering.
Backup and Disaster Recovery Planning:
Implement comprehensive backup and disaster recovery strategies for your NAS data. Regularly back up critical data to off-site locations or cloud services to mitigate the impact of potential data loss due to security incidents or hardware failures.
Monitoring and Intrusion Detection:
Deploy monitoring tools and intrusion detection systems to actively monitor the NAS for unauthorized access attempts, anomalous activities, and potential security breaches. Set up alerts and notifications to promptly respond to any security incidents within the NAS environment.
Physical Security Measures:
Consider physical security measures to protect the NAS device from theft, tampering, or unauthorized access. This may include securing the physical location of the NAS, implementing access controls, and using locking enclosures or cabinets to safeguard the device.
By diligently implementing these security measures, you fortify your home network attached storage, creating a resilient and secure environment for storing and accessing your data. These proactive steps contribute to the overall integrity and reliability of your NAS within your home network.
Conclusion
Congratulations on successfully navigating the process of setting up your home network attached storage (NAS) system. By following the comprehensive guide provided, you have acquired the knowledge and skills to establish a robust and efficient storage solution within your home network environment.
From the meticulous selection of the right NAS device to the careful configuration of hardware, software, and security measures, you have laid the foundation for a reliable and versatile storage solution tailored to your specific needs.
As you embark on this journey, it’s important to recognize the transformative impact of a well-designed NAS system. Your NAS empowers you to centralize and manage your data, whether it’s for personal use, media streaming, backup, or collaborative work within your household.
Furthermore, the integration of security measures ensures that your data remains safeguarded and accessible within a secure digital environment. By prioritizing security, you have taken proactive steps to protect your valuable data and uphold the integrity of your home network.
As you continue to explore the capabilities of your NAS, consider leveraging its features to streamline your digital activities, enhance media sharing, and reinforce your data management practices. The versatility of a well-configured NAS extends beyond storage, offering opportunities to streamline your digital lifestyle and elevate your home network experience.
Remember that maintaining your NAS, including regular software updates, data backups, and periodic security assessments, is essential to its continued reliability and resilience. By staying proactive and informed, you can ensure that your NAS remains a dependable asset within your home network for years to come.
With your home network attached storage system in place, you have unlocked a world of possibilities for convenient, secure, and accessible data management within your home environment. Embrace the potential of your NAS and continue to explore the myriad ways it can enhance your digital lifestyle.
Thank you for embarking on this journey with us, and we wish you continued success in leveraging your home network attached storage to its fullest potential.