Introduction
The security of our online activities has become increasingly important in today’s digital landscape. Virtual Private Networks (VPNs) have emerged as a popular tool for safeguarding our browsing, data transmission, and online identity. However, not all VPN protocols offer the same level of security. In this article, we will explore the various VPN protocols and focus on one in particular, which is no longer considered secure.
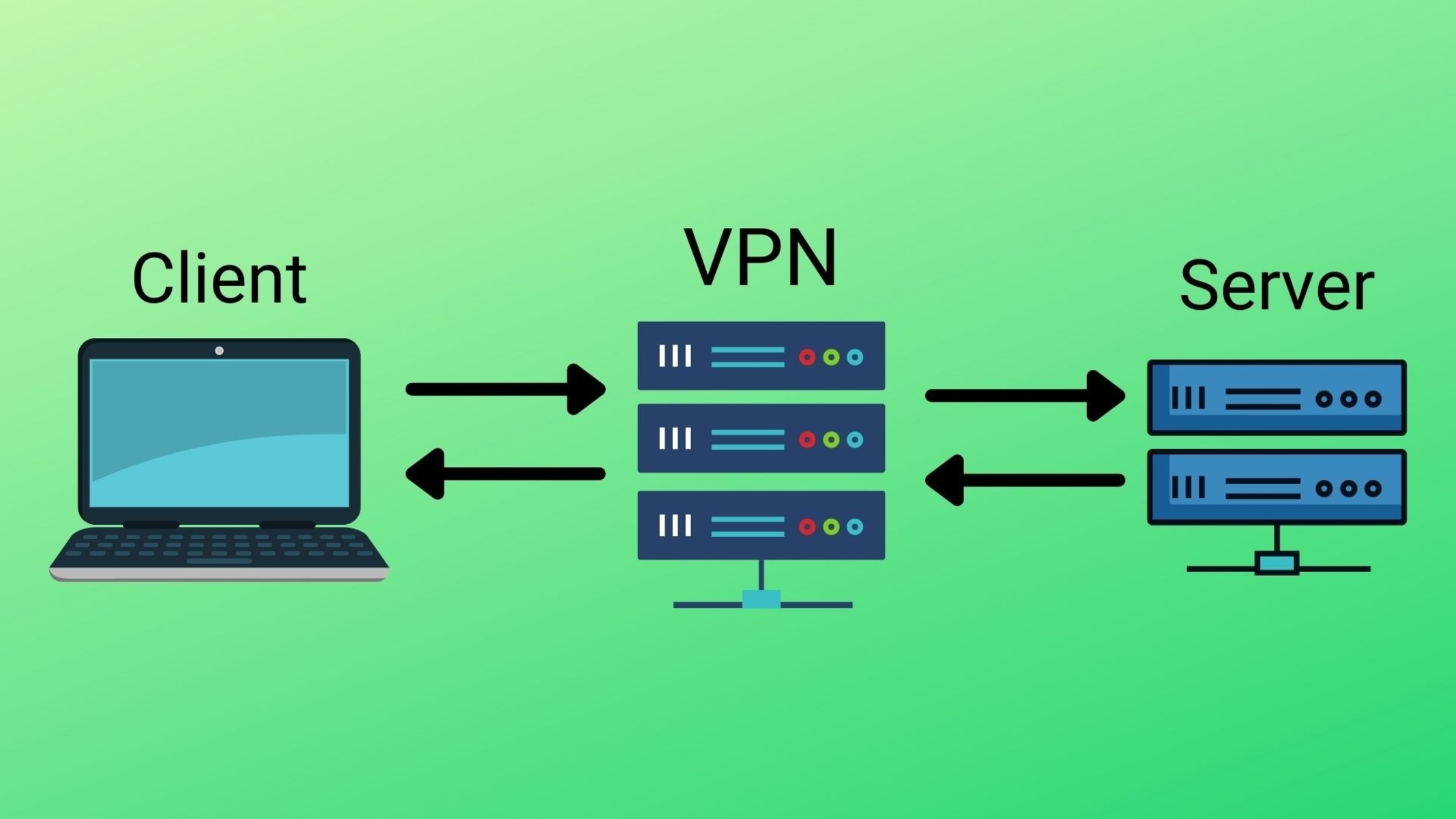
VPN protocols serve as the backbone of secure communication channels between a user’s device and the VPN server. They employ encryption methods to ensure that data transmitted over the internet remains confidential and protected from prying eyes. Over time, certain protocols have been found to have vulnerabilities, rendering them no longer secure.
It is important for users to stay informed about the security levels of different VPN protocols to make informed decisions about their online security and privacy. Let’s delve into the world of VPN protocols and identify which one is no longer considered secure.
PPTP (Point-to-Point Tunneling Protocol)
PPTP, or Point-to-Point Tunneling Protocol, was one of the first VPN protocols to gain popularity due to its ease of setup and compatibility with multiple operating systems. Developed by Microsoft, it was widely used in the 1990s and early 2000s. However, PPTP has long been considered an outdated and insecure protocol.
One of the main reasons PPTP is no longer considered secure is due to its weak encryption. It uses 128-bit encryption, which was once considered strong, but has since been surpassed by more robust encryption algorithms. This level of encryption can be easily cracked by determined hackers and government surveillance agencies, compromising the privacy and security of user data.
Furthermore, PPTP suffers from several vulnerabilities, making it an attractive target for attackers. For starters, it uses the outdated Microsoft Challenge Handshake Authentication Protocol (MS-CHAP) for authentication, which has been found to be susceptible to cracking. This allows attackers to intercept and decipher user credentials, granting them unauthorized access to user connections.
In addition, PPTP has weak defenses against common network attacks such as man-in-the-middle attacks. Its lack of built-in integrity checks makes it vulnerable to tampering, allowing attackers to modify or intercept the transmitted data without detection. This undermined the core principle of VPNs, which is to ensure the integrity and confidentiality of data.
Due to these security vulnerabilities, major VPN providers have discontinued support for PPTP in their software, and many operating systems and devices have also removed it as a supported protocol. Users are advised to refrain from using PPTP as their VPN protocol of choice and opt for more secure alternatives that offer stronger encryption and better overall security.
L2TP/IPSec (Layer 2 Tunneling Protocol with Internet Protocol Security)
L2TP/IPSec, or Layer 2 Tunneling Protocol with Internet Protocol Security, is a VPN protocol that combines the best features of both L2TP and IPSec. L2TP provides the tunneling mechanism, while IPSec offers the encryption and security features. It is widely supported by major operating systems and devices, making it a popular choice for VPN connections.
L2TP/IPSec utilizes 256-bit encryption, which is highly secure and resistant to brute-force attacks. The robust encryption ensures that all data transmitted through the VPN connection remains confidential, protecting it from unauthorized access and surveillance. Furthermore, L2TP/IPSec supports a variety of encryption algorithms, giving users the flexibility to choose their preferred level of security.
In terms of authentication, L2TP/IPSec employs the robust IPSec protocols, such as IKEv2 (Internet Key Exchange version 2), for establishing secure connections. IKEv2 provides strong authentication methods, including certificate-based authentication and pre-shared keys, ensuring that only authorized users can access the VPN server.
One of the advantages of L2TP/IPSec is its ability to bypass firewalls and NAT (Network Address Translation) devices, making it suitable for users behind restrictive network settings. Since L2TP uses UDP (User Datagram Protocol) as a transport protocol, it can easily traverse firewalls that only allow certain ports or packet types. This improves accessibility and ensures seamless connectivity for VPN users.
However, it is worth noting that L2TP/IPSec does have some drawbacks. It can be slower than other VPN protocols due to the overhead introduced by the additional layers of encryption and encapsulation. Additionally, L2TP does not provide built-in support for data integrity checking, which means it is more susceptible to data tampering compared to protocols like OpenVPN.
Despite these limitations, L2TP/IPSec remains a popular choice for VPN connections, especially on older devices or networks that do not support more advanced protocols. It offers a reliable and secure option for users looking to protect their online activities and ensure the privacy of their data.
IKEv1 (Internet Key Exchange version 1)
IKEv1, or Internet Key Exchange version 1, is an older version of the IKE (Internet Key Exchange) protocol used to establish secure connections in IPsec-based VPNs. It is commonly used in legacy systems and some VPN implementations, although it is gradually being replaced by newer versions such as IKEv2.
One of the key features of IKEv1 is its ability to negotiate security associations, including encryption algorithms, authentication methods, and key management protocols. These negotiations ensure that both the client and the VPN server agree upon a set of security parameters, establishing a secure and encrypted connection.
IKEv1 also provides support for authentication through various methods, including digital certificates and pre-shared keys. This ensures that only authorized users can establish a VPN connection and access the resources on the network. Furthermore, IKEv1 offers robust key management capabilities to create and manage session-specific encryption keys.
However, despite its strengths, IKEv1 has several security vulnerabilities that make it less secure than newer protocols. One of the main vulnerabilities is the vulnerability to man-in-the-middle attacks during the initial key exchange. This means that an attacker could intercept the key exchange process and potentially alter the security parameters, compromising the integrity and confidentiality of the VPN connection.
In addition, IKEv1 does not provide built-in support for perfect forward secrecy (PFS), which is a security feature that ensures the confidentiality of past VPN sessions even if the long-term secret keys are compromised. Without PFS, if an attacker gains access to the long-term keys, they can decrypt all past and future VPN sessions, posing a significant security risk.
Due to these vulnerabilities, it is recommended to use newer versions of the IKE protocol, such as IKEv2, which address these security concerns. However, in situations where compatibility with legacy systems or devices is a requirement, IKEv1 may still be used. In such cases, it is essential to implement additional security measures, such as robust authentication and strong encryption algorithms, to minimize the risk of exploitation.
Overall, while IKEv1 served as a foundational VPN protocol, its security weaknesses make it less suitable for use in modern VPN deployments. It is advisable to transition to newer protocols that offer stronger security features and better resistance against evolving threats.
OpenVPN (Open Virtual Private Network)
OpenVPN is an open-source VPN protocol that has gained widespread popularity due to its robust security features and flexibility. It is known for its strong encryption, extensibility, and cross-platform compatibility, making it a preferred choice for many VPN users and service providers.
OpenVPN uses the OpenSSL library to provide encryption, ensuring the confidentiality and integrity of data transmitted through the VPN connection. It supports various encryption algorithms, including AES (Advanced Encryption Standard) and Blowfish, allowing users to choose the level of security that suits their needs. With OpenVPN, users can trust that their data remains protected from unauthorized access and eavesdropping.
One of the remarkable features of OpenVPN is its versatility. It can operate over both UDP (User Datagram Protocol) and TCP (Transmission Control Protocol), offering flexibility in different network conditions. UDP is preferred for faster and more efficient performance, especially for streaming and gaming applications. TCP, on the other hand, ensures reliable delivery of packets, making it suitable for scenarios where connection reliability is paramount.
Furthermore, OpenVPN supports various authentication methods, including certificates, username/password combinations, and pre-shared keys. This multi-factor authentication ensures that only authorized users can access the VPN server, greatly enhancing security. OpenVPN also incorporates robust key management mechanisms, providing secure generation, distribution, and revocation of encryption keys.
OpenVPN’s open-source nature allows for continuous security audits and community contributions, ensuring that any vulnerabilities are quickly identified and resolved. Additionally, being open-source fosters transparency and trust, as the code can be independently verified by security experts and users.
Thanks to its flexibility and extensive documentation, OpenVPN is compatible with a wide range of devices and operating systems. It supports major platforms such as Windows, macOS, Linux, Android, and iOS, making it accessible to users on various devices. This cross-platform compatibility makes it a popular choice for individuals, businesses, and organizations seeking a secure VPN solution.
While OpenVPN offers many advantages, setting it up might involve a more technical configuration process compared to other VPN protocols. This can be a challenge for less tech-savvy users, but the benefits of OpenVPN’s security capabilities and wide support outweigh the initial setup complexity.
Overall, OpenVPN stands out as a highly secure and versatile VPN protocol. Its strong encryption, authentication methods, cross-platform compatibility, and open-source nature make it an excellent choice for users who prioritize security and reliability in their VPN connections.
WireGuard
WireGuard is a modern and innovative VPN protocol that has gained significant attention for its simplicity, speed, and strong security capabilities. It was designed to address the shortcomings of traditional VPN protocols and provide a more efficient and secure solution for VPN connections.
One of the key features of WireGuard is its lightweight codebase. The protocol is implemented in just a few thousand lines of code, making it easy to audit, understand, and maintain. This simplicity not only reduces the chances of security vulnerabilities but also contributes to its impressive performance.
WireGuard utilizes state-of-the-art cryptography algorithms to ensure the integrity and confidentiality of data. It relies on the Noise protocol framework, which combines modern encryption primitives such as Curve25519 for key exchange and ChaCha20 for encryption. The use of strong cryptographic algorithms enhances security and protects users’ transmitted data from unauthorized access or surveillance.
Additionally, WireGuard benefits from its minimalistic approach to secure tunneling. By avoiding complex and outdated mechanisms found in other protocols, such as IPsec or SSL/TLS, WireGuard achieves faster connection establishment and lower latency. The streamlined design helps to maximize speed and efficiency while maintaining robust security.
WireGuard also supports seamless roaming, allowing users to switch between networks without interrupting VPN connections. This feature is particularly useful for users who frequently switch between Wi-Fi networks or transition between different network connections, such as from a Wi-Fi hotspot to a cellular network.
Furthermore, WireGuard has built-in support for both IPv4 and IPv6, enabling it to seamlessly work in networks using either IP version. This flexibility ensures that users can enjoy the benefits of WireGuard regardless of the IP protocol used by their network.
Although WireGuard is relatively new compared to other VPN protocols, it has gained significant attention and has been extensively reviewed by the security community. Its innovative approach and strong security design have contributed to its growing popularity among VPN providers and users alike.
WireGuard’s simplicity and efficiency make it an attractive choice for both individual users and organizations seeking a secure VPN solution. Its transparency, combined with its focus on speed and security, position WireGuard as a leading contender in the VPN protocol landscape.
Conclusion
In this article, we have explored several VPN protocols, each with its own strengths and weaknesses in terms of security. While it is crucial to understand the different VPN protocols available, it is even more important to prioritize security when selecting a VPN protocol to ensure the protection of our online activities and data.
PPTP, once popular for its ease of use, is no longer considered secure due to its weak encryption and vulnerabilities that make it susceptible to attacks.
L2TP/IPSec offers a combination of tunneling and encryption, providing strong security and compatibility. However, its lack of built-in data integrity checking and potential performance issues should be taken into consideration.
IKEv1, although an older protocol, provides secure connection establishment and key management. However, its vulnerabilities to man-in-the-middle attacks and the lack of perfect forward secrecy make it less secure compared to newer protocols such as IKEv2.
OpenVPN, an open-source protocol, offers robust encryption, authentication options, and platform compatibility. Its transparency, community audits, and versatility make it a popular choice among security-conscious users.
WireGuard, a modern VPN protocol, stands out for its simplicity, strong security, and efficient performance. Its lightweight design, use of modern cryptography algorithms, and support for seamless roaming make it an exciting contender in the VPN landscape.
In the end, the choice of VPN protocol depends on individual needs and priorities. It is essential to consider factors such as encryption strength, authentication methods, platform compatibility, and support for additional security features like perfect forward secrecy. By selecting a secure and reliable VPN protocol, users can establish a trusted connection and enjoy enhanced privacy and security in their online activities.