Business is good because anyone can start their own business from scratch. People can design and build their products to suit their liking. Then connect with suppliers, manufacturers, and distributors at the speed unimaginable decades ago. Profits trickle in within weeks upon your startup.
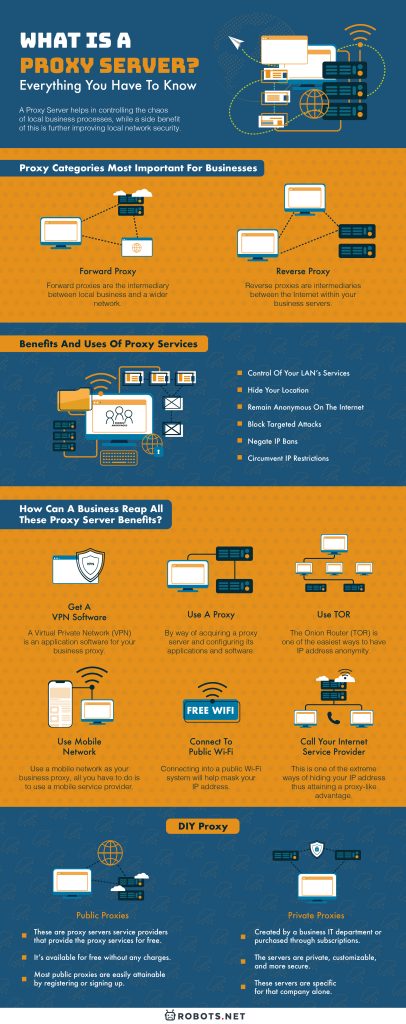
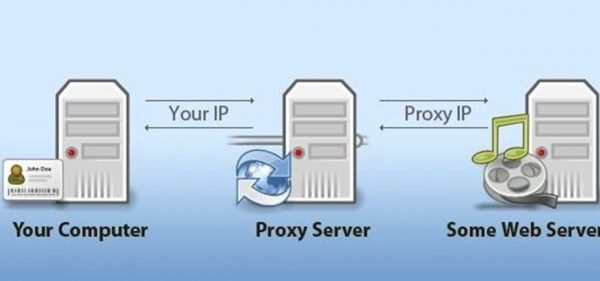
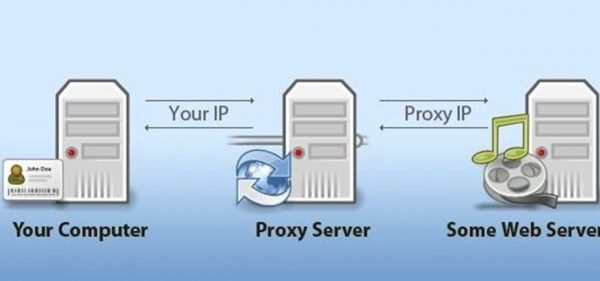
Then there’s the bad side of these ever-growing Internet-based businesses. For example, the lack of security for your customer’s data. Certain regions of the world market are not accessible because of regional censorship. Or worse, they ban your IP address from connecting with certain areas. Well, one solution to these kinds of concerns is having a proxy server. But what is a proxy server and what are its functions?
Don’t worry, we’ll introduce to you what proxy servers are and their uses. If you’re curious to learn how they work, stick around and learn more about them. Now everyone, let’s get started!
What Is A Proxy Server?
Some people might be familiar with what a proxy server is and what its functions are. But for people who are not familiar with proxy servers, here is a video that can help you understand them:
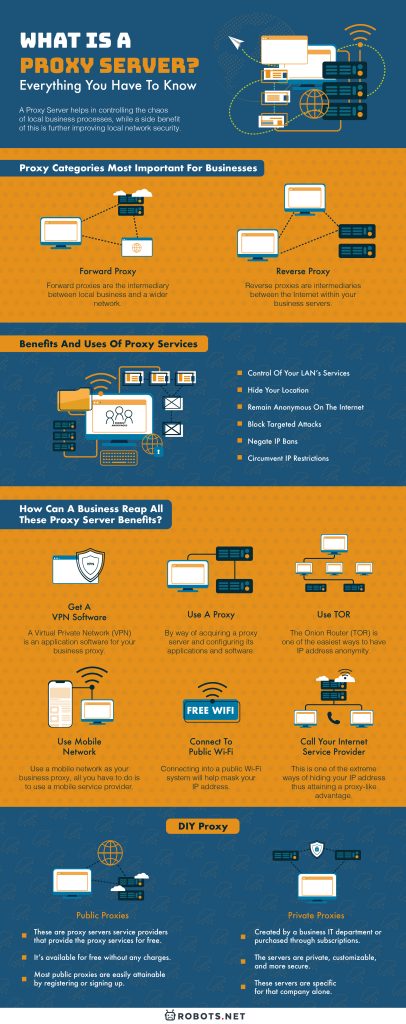
Proxy Categories Most Important For Businesses
Forward Proxy
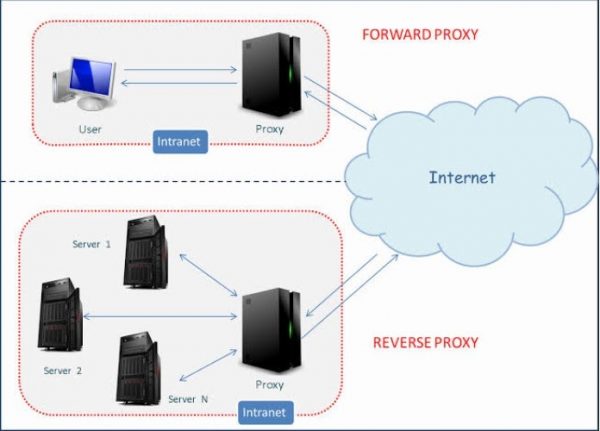
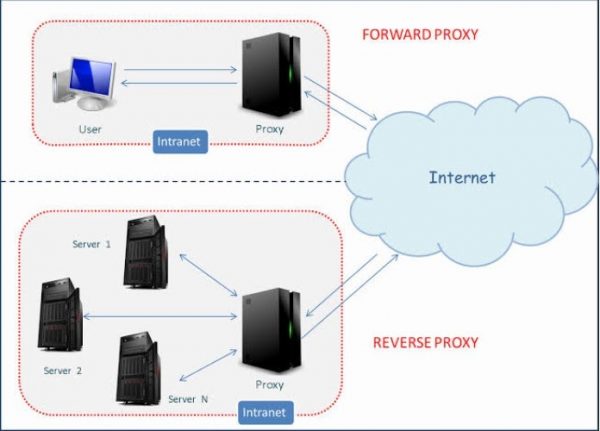
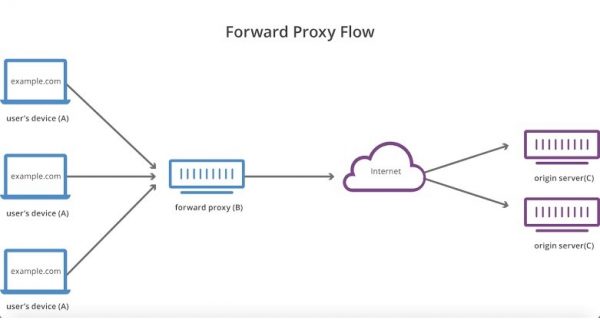
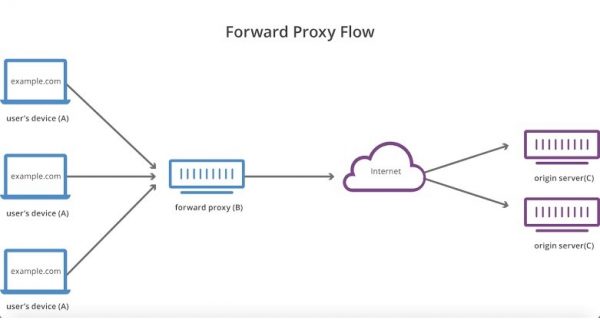
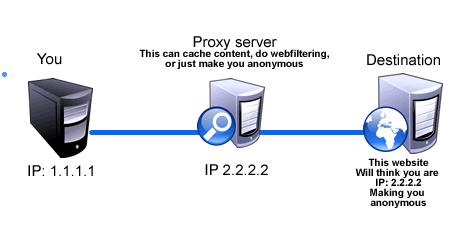
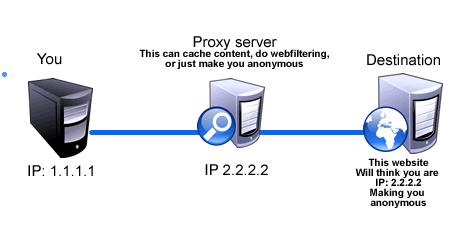
Forward proxies are the intermediary between local business and a wider network. The wider network could either be the Internet or a cloud platform. These proxy applications are client-based, which include regular Internet browsers. These applications can help users access the Internet.
Reverse Proxy
Reverse proxies are intermediaries between the Internet within your business servers. For instance, a reverse proxy could act as a gateway between the Internet or the cloud. Thus providing your corporate LAN network a buffer of security. This gateway could be configured to obscure businesses’ IP addresses or user’s bandwidths.
Why Do Businesses Need To Have Proxy Servers Now More Than Ever?
Being in the business of content writing, research has a great deal of importance. Which is why the Internet is an important tool when researching topics. From finding out what is new and innovative to verifying, your story should be backed up with facts. A couple of quick taps on the keyboard and a writer has all this information on his screen.
That is the power of information in business, this information translates into profits. But what if your business’ source of profit loses money? One possibility could be that your source of information is currently compromised.
In business information, a compromised system can come in different ways. Your office Internet running slow most of the time. Tasks that only a certain group should do is being leaked. Also, malicious activities are being done directly to your corporate servers. All these are a sign that a corporate system server has been compromised.
To reduce these problems, most of the Fortune 500’s top companies use proxy servers. If you’re interested in using a proxy server for your business, why not get a good tower server today? Check out this Fujitsu tower server today and let your business grow with security.
Benefits And Uses of Proxy Services
A proxy server helps in controlling the chaos of local business processes, while a side benefit of this is further improving local network security.
Control Of Your LAN’s Services
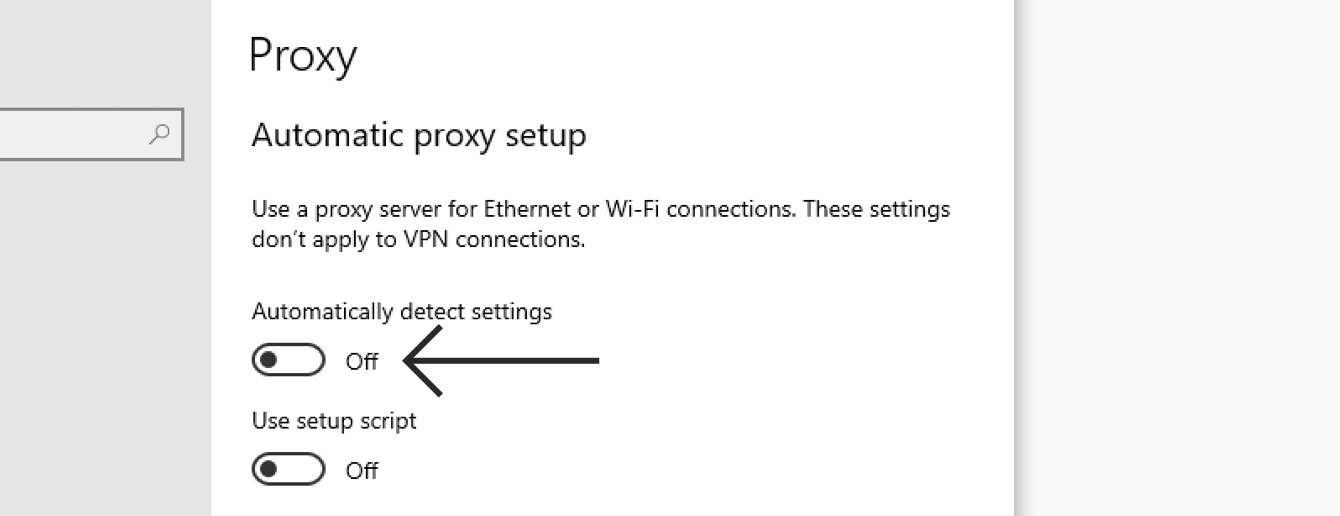
Proxy servers are capable of controlling all aspects of Internet connectivity activities. This would mean, not only do you control what your corporate users see. Administrators also control the amount of information that they see. A business proxy could even control the bandwidth of different users or departments. Thus increasing Internet speeds of those who need them most in the business.
Hide Your Location
Prevention is always the key to protecting your business. Proxies prevent potential malicious operators from gaining access to your servers. This is done by hiding your IP address or obscuring it. In this manner, operators only see the proxy’s IP address and not the business’.
Remain Anonymous On The Internet
Proxies can increase business privacy by keeping its anonymity. Your company’s users scour the Internet for information that they need. But they might encounter malicious software that piggybacks on their searches. This malware can then return to your server and wreak havoc. Proxies can block this malware the minute your users return from the Internet. Thus keeping your business servers unknown to the public and the Internet.
Block Targeted Attacks
Malicious operators need to identify your business-specific IP address. This provides them direct access to your servers. But with the use of proxies, direct targeting of your servers is impossible.
Negate IP Bans
Due to some sweeping generalization, certain regional-based IP addresses are banned in certain locations in the world.
An example would be an IP address from a communist or rogue country. It would be difficult for them to search for information through the Internet. While they may be fine on most Internet sites, others directly block these addresses. This is by the simple implication that the IP address was identified as being from a communist region. Thus simple research about western cough medicines can be blocked.
Having a proxy server can negate these IP address bans. Since you can gain proxy services that are not coming from a blocked region.
Circumvent IP Restrictions
Like negating regional IP address bans. There are IP addresses that are marked as restricted. By using a proxy that masks the IP address of your business can circumvent these restrictions.
How Can A Business Reap All These Proxy Server Benefits?
There many ways of attaining proxy benefits, but here are the best paid and free options listed for you.


Get A VPN Software
A Virtual Private Network (VPN) is an application software for your business proxy. The big difference is that a VPN is a cloud-based application. Thus, proxy server benefits can be attained despite not having a dedicated server for it. Inert to a VPN is its capability to encrypt both incoming and outgoing data. This is essential if you are moving business-critical information while on global locations.
Use A Proxy
Build your proxy server. By way of acquiring a proxy server and configuring its applications and software. The only possible drawback of this option moves slower compared to using a VPN. This is due to a slow local Internet connection or inefficient proxy application configuration. But businesses with a local area network (LAN) can take advantage of other benefits. Such as user control and further security options.
Use TOR
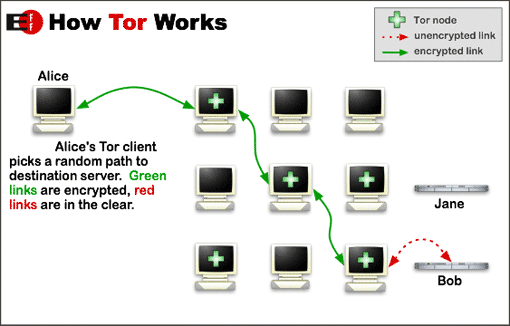
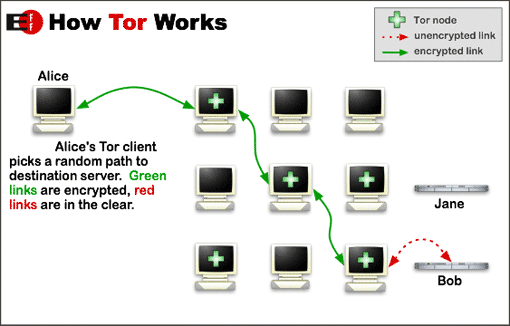
The Onion Router (TOR) is one of the easiest ways to have IP address anonymity and secure your business server and it’s free. But just like most free applications and software, there are drawbacks to its use. One of which is the need for a dedicated IT tech specialist. This is to ensure that you’ll be able to take advantage of TOR as best as possible. Yet, be able to track the app’s activities for malicious intrusions.
Use Mobile Network
A simple change in business processes can also be used to get these benefits. A procedural change such as incorporating a third-party proxy, like your phone’s network. Once again this option is free of charge.
To use a mobile network as your business proxy, all you have to do is to use a mobile service provider. That way businesses are using proxies of their phone’s network. Thus when you use their ISP on your phone, you are already using their network proxies.
Connect To Public Wi-Fi


This one is more for tiny businesses.
As an example. Your business is already raking in the cash and it’s not showing any signs of a slowdown. As such, you’re already afraid someone might start messing with your online business. That would throw out all your hard work and leave you back in the gutters.
Connecting into a public Wi-Fi system will help mask your IP address, thus making your business hard to target. All you have to do is log onto any free or with a small purchase use, public Wi-Fi. Thus every time you’re on business your IP address is never the same.
Call Your Internet Service Provider
This is one of the extreme ways of hiding your IP address thus attaining a proxy-like advantage. If you already know that your business server’s IP addresses are compromised. It’s highly suggested to call your Internet service provider and have them reassign you a new IP address. This will immediately disconnect you from your attacker.
Force An IP Address Change By Unplugging Your Modem
Another extreme way of cutting off a direct attack is by simply disconnecting your modem. If your business can afford to be off-line for a couple of hours, this way is the best. It’s free and it’s easy to do. There’s also a big possibility that when you reconnect your modem will reassign a new IP address. In this manner, you are then protected from new attacks.
DIY Proxy
Bent on building your proxy server? Do you want to have full control of your business’s interaction with the worldwide web? Then, know the difference between public and private proxies.
Public Proxies
1.) What are public proxies?
These are proxy servers service providers that provide the proxy services for free.
2.) What are the benefits of public proxies?
It’s available for free without any charges.
3.) How are public proxies acquired or built?
Most public proxies are easily attainable by registering or signing up.
Private Proxies
1.) What are private proxies?
These are proxy servers created by a business’ IT department or purchased through subscriptions.
2.) What are the benefits of private proxies?
The servers are private, customizable, and more secure.
3.) How are private proxies acquired or built?
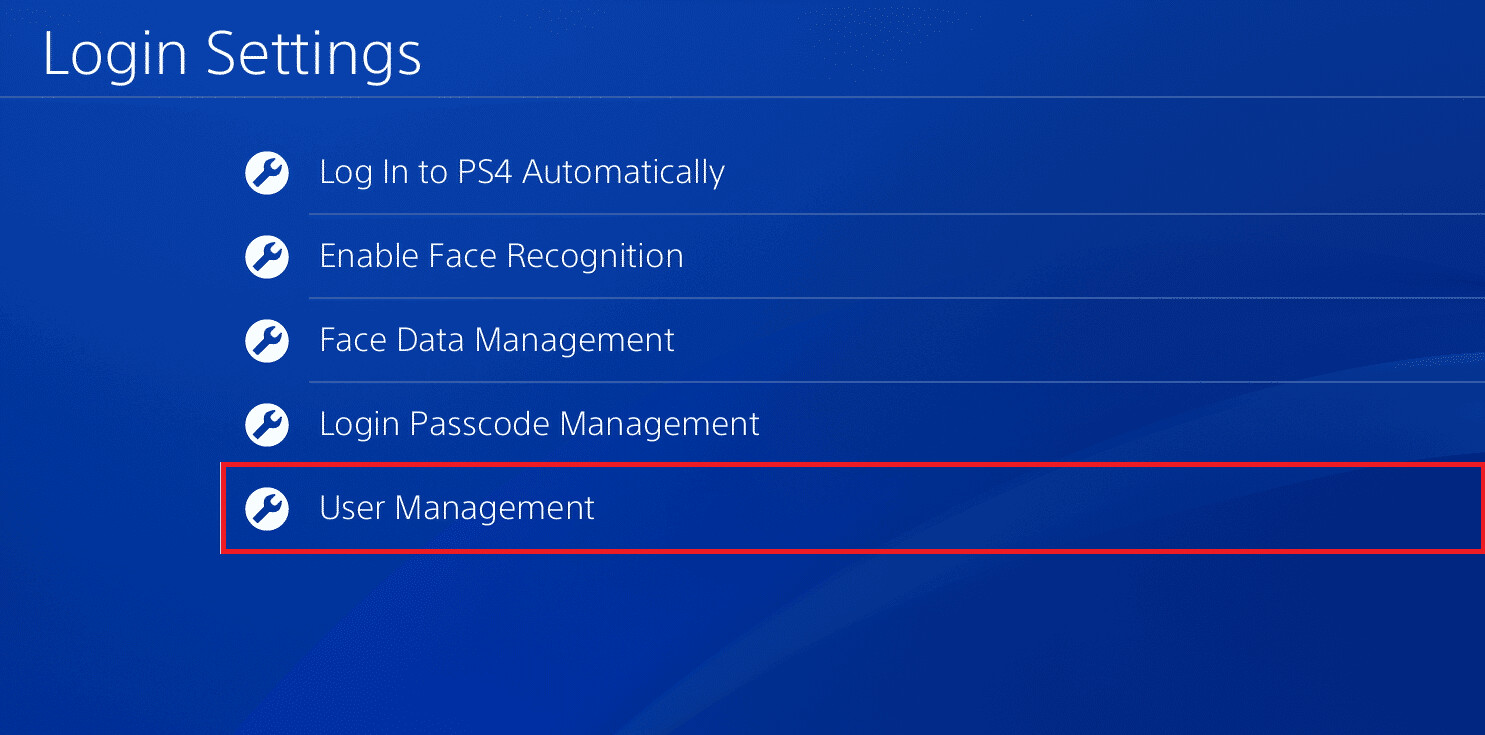
A server unit is configured onsite for the use of only one specific business or company. Then applications and software are then installed. These servers are specific for that company alone. This should include proxy-specific service application software.
Hardware Requirements
Dell PowerEdge T30
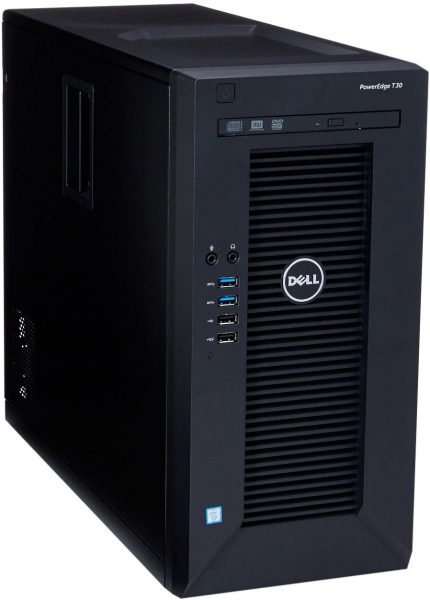
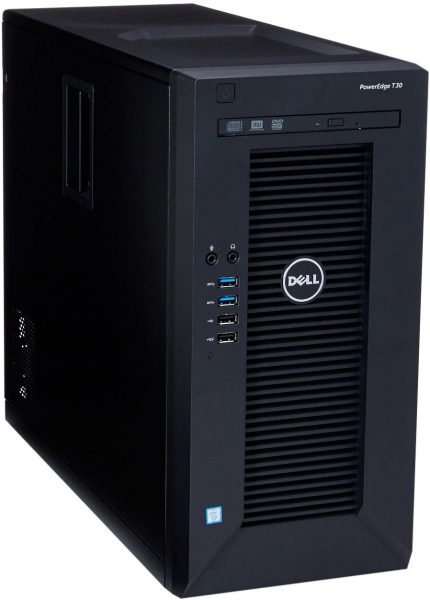
The PowerEdge T30 is Dell’s primary offer for desktop servers. It helps you improve access to information, simplify processes, and get more done in less time. The T30 server helps businesses overcome the complexity of data and applications. The server does this by organizing both apps and data. Take advantage of the processing power and storage density of the T30. It will help your business meet greater efficiency and productivity. Check out this tower now on Amazon and improve your business’ accessibility.
HPE ProLiant MicroServer Gen10


The HPE ProLiant MicroServer Gen10 is HP’s answer to the desktop server market. It has enough processing power to be an application server and a data server in one. With its RAID controller, it’s more than capable of expanding its current array of memory modules. It can provide the extra capability to accept an accompanying NAS unit. For small businesses, this server could prove to be one of the company’s most reliant business assets. Upgrade your servers now and experience a better workflow.
Dell PowerEdge T340
The Dell PowerEdge T340 provides more than the basics. Its components alone are more than sufficient for your businesses’ computing needs. Its top-quality processing power combines with high capacity, high-speed memory. This desktop unit pushes to the top level of server efficiency even if your business has a high processing need. Upgrade your system now by getting this today and increase your company’s productivity.
Software Requirements
Take advantage of the best that your proxy server’s hardware can offer. There is a myriad of software available for installation. Here are some that specifically cater to answer a proxy’s purpose.
SafeIP
SafeIP is a freeware tool that hides your computer’s IP address and replace it with a different one. The tool also offers a browser ID, Wi-Fi, and DNS protection to name a few of its services. Then it also keeps you protected from malicious websites. It is a perfect tool to hide your online identity while browsing.
Squid Proxy Server Software
Squid is a proxy server and web cache daemon. It keeps track of what it has already searched. It has a wide variety of features like speeding up a web server by caching repeated requests. Caching web, DNS, and other computer network lookups. It works for a group of people sharing network resources. It also aids in security by filtering traffic. Squid was originally designed to run on Unix-like systems then adapted to work on Windows.
UltraSurf
UltraSurf is a popular proxy software that lets you access blocked content. The tool can completely hide your identity and protect your privacy on the Internet. Using this tool, you can access any blocked or inaccessible content.
CCProxy
Different from conventional proxy service providers, CCProxy lets you create your proxy server. It lets you share the Internet over LAN in a controlled way. CCProxy can work with DSL, dial-up, optical fiber, satellite, ISDN, and DDN connections. It comes with an account management system. This lets you create accounts and groups for different users on your LAN.
WinGate Proxy Server Software
WinGate is a sophisticated integrated Internet gateway. It acts as a communications server designed to meet the control, security, and email needs. Created for today’s Internet-connected businesses, WinGate Proxy Server shares most types of Internet connection. It allows multiple users to simultaneously surf the web. Users can retrieve their emails or use other Internet programs. All this is done as if they were directly connected to the Internet.
Other Types of Proxy Servers


Anonymous Proxy
An anonymous proxy is a server that functions as a relay between the user and a destination website. It hides the IP address of the user’s machine from the website and may provide encryption on the user side. This is a good proxy to use when you are looking to download torrents from blocked websites.
Distorting Proxy
A distorting proxy is a form of a gateway proxy. It recognizes itself as a proxy server as well. That alters a user’s HTTP (HyperText Transfer Protocol) headers. This is to conceal or disguise the original IP address. This way it can help protect a user’s personal information while that person is browsing the Internet.
Transparent Proxy
A transparent proxy is a server that sits between your computer and the Internet. It redirects your requests and responses without modifying them. Non-transparent proxy is a proxy server that does change your requests and responses.
SOCKS Proxy
A SOCKS server is a general-purpose proxy server. It establishes a TCP connection to another server on behalf of a client. Then routes all traffic back and forth between the client and the server. It works for any kind of network protocol on any port. SOCKS Version 5 adds additional support for security and UDP.
Rotating Proxy
A rotating proxy is a proxy server that assigns a new IP address from the proxy pool for every connection. All done autonomously or by a standby technician. That means you can launch a script to send 10,000 requests to many sites and get 10,000 different IP addresses. Consider this as your last resort proxy. If you’re business is under attack yet you need to continue operations, this is the proxy to go for.
Proxies are the way to go once your business has achieved its profit goals. They ensure you with a full range of security service options. Then there’s the added series of benefits. These come in the form of global access without restrictions and anonymous research. Therefore, businesses are always looking towards incorporating a proxy server these days.