Introduction
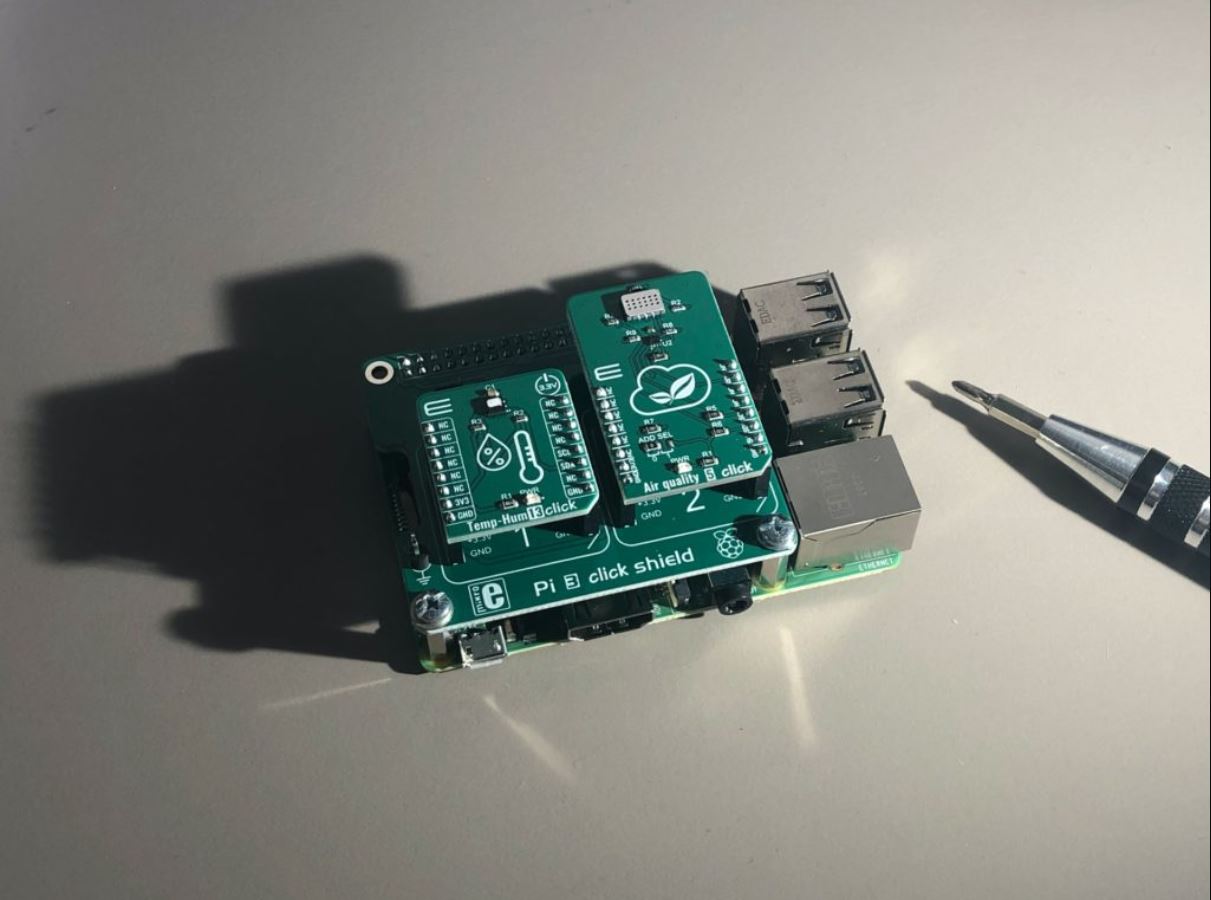
The advancement of technology reshapes the way we live and interact with the world. One significant development in recent years is the proliferation of Internet of Things (IoT) devices. IoT devices are interconnected devices embedded with sensors, software, and network connectivity, allowing them to collect and exchange data. From smart thermostats and wearable devices to home security systems and industrial machinery, IoT devices have become an integral part of our daily lives. While they bring convenience and efficiency, there are also risks associated with their use.
The purpose of this article is to highlight the potential risks and challenges that come with utilizing IoT devices. Understanding these risks is crucial for individuals and businesses alike, as it allows them to make informed decisions and take proactive measures to mitigate any potential harm. From security and privacy concerns to reliability issues and ethical dilemmas, the risks of using IoT devices can have far-reaching implications.
It is important to note that the risks discussed in this article are not meant to deter people from adopting IoT technology, but rather to raise awareness and encourage responsible usage. With proper precautions and safeguards in place, the benefits of IoT devices can be optimized while minimizing the associated risks.
In the following sections, we will explore some of the key risks involved in using IoT devices, including the lack of security and privacy, vulnerability to cyber attacks, data breaches and theft, unauthorized access and control, lack of regulation and standardization, potential for physical harm, dependence on internet connectivity, reliability and compatibility issues, and ethical concerns and misuse of data. By understanding these risks, individuals and organizations can make informed decisions and take the necessary steps to safeguard their privacy, security, and overall well-being.
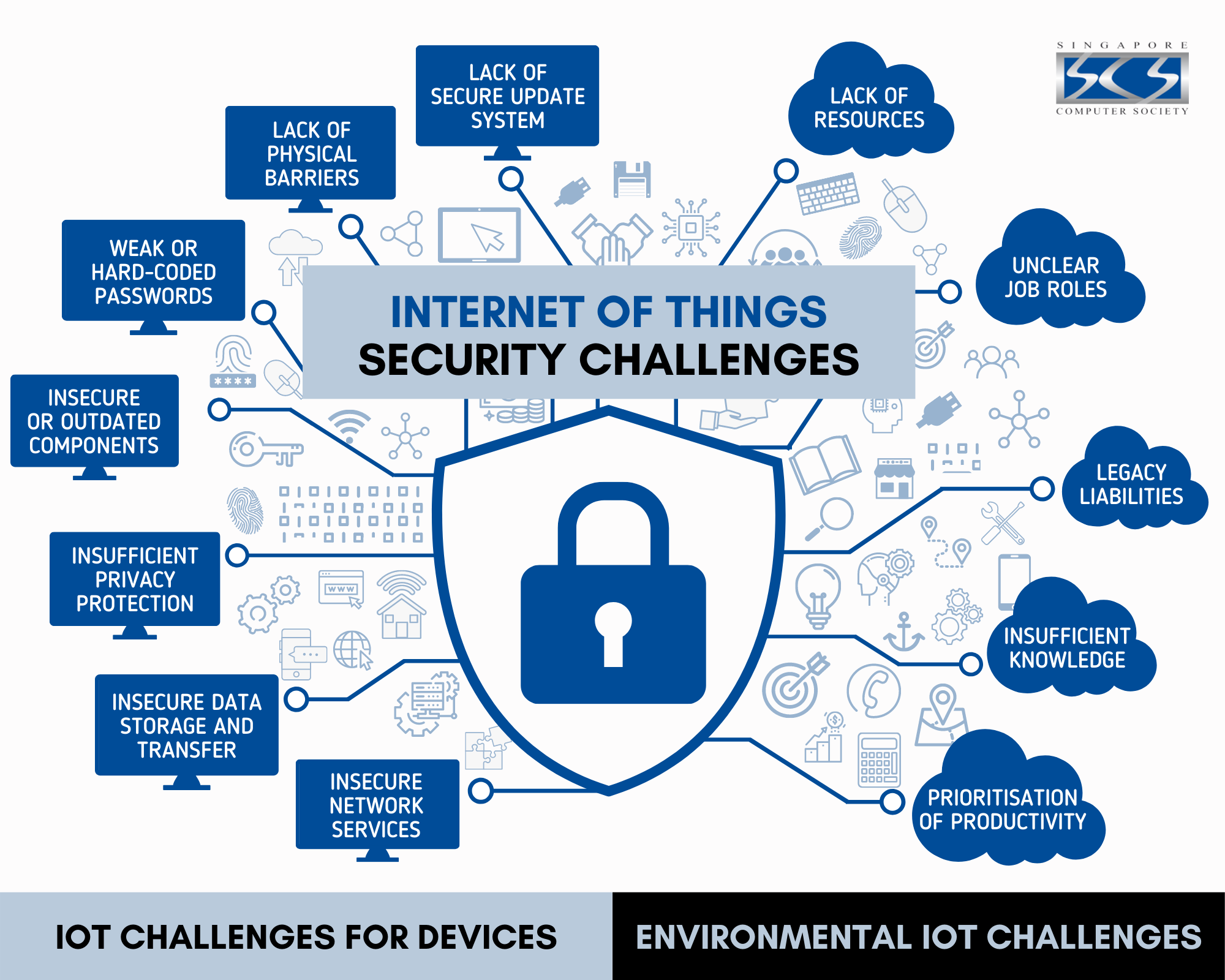
Lack of Security and Privacy
One of the primary concerns surrounding IoT devices is the lack of robust security measures, leaving them vulnerable to cyber threats and privacy breaches. Many IoT devices are designed with limited security features, making them easy targets for hackers and unauthorized access.
Without proper security protocols in place, IoT devices can be exploited to gain access to personal and sensitive information. For example, a smart home device could be compromised, allowing an attacker to remotely control security systems or access personal surveillance footage. This not only compromises people’s privacy but also poses a significant safety risk.
In addition to personal privacy, the lack of security in IoT devices can have severe consequences for businesses and industries. For instance, in the healthcare sector, IoT devices such as connected medical devices and wearable health trackers collect sensitive patient data. If these devices are not adequately secured, the data can be intercepted, leading to privacy breaches, identity theft, or even manipulation of medical records.
Furthermore, the interconnected nature of IoT devices means that a single compromised device can potentially compromise an entire network. This can have far-reaching implications for critical infrastructure systems such as power grids, transportation systems, and manufacturing facilities. The consequences of a security breach in these sectors can be catastrophic, leading to disruption of services, financial losses, and even endangering lives.
To address these security challenges, manufacturers, regulatory bodies, and users need to collaborate to establish and adhere to rigorous security standards. Encryption protocols, strong authentication mechanisms, and regular software updates are essential to mitigate security risks. Additionally, users must be vigilant in monitoring and managing their IoT devices, including changing default passwords, limiting the data collected, and keeping firmware up to date.
While security measures are continually evolving, it is crucial for individuals and organizations to be proactive in safeguarding their IoT devices and ensuring the privacy and security of their data. By recognizing the lack of security and privacy as a significant risk, users can make informed decisions and take necessary precautions to protect themselves and their information from potential cyber threats and privacy breaches.
Vulnerability to Cyber Attacks
IoT devices, due to their interconnected nature and often limited security measures, are highly vulnerable to cyber attacks. These attacks can have serious implications, both for individuals and for critical infrastructure systems.
One common type of cyber attack on IoT devices is a Distributed Denial of Service (DDoS) attack. In this type of attack, a network of compromised IoT devices, known as a botnet, is used to overload a targeted system or network with a massive amount of incoming traffic. This can result in service disruptions, rendering the affected devices or systems unusable. Such attacks not only impact the availability and functionality of the targeted devices but also pose significant challenges for businesses, causing financial losses and damaging reputation.
Another form of cyber attack that IoT devices are vulnerable to is hacking and unauthorized access. Weak or default passwords, outdated firmware, and unpatched vulnerabilities can allow hackers to gain control over the device and potentially use it as a launching pad to infiltrate the entire network. Once infiltrated, attackers can exploit sensitive information, disrupt operations, or even cause physical harm, depending on the nature of the compromised device.
The implications of cyber attacks on IoT devices go beyond individual privacy and security. With the increasing integration of IoT devices in critical infrastructure systems, such as power grids, transportation networks, and healthcare facilities, the potential for large-scale disruptions due to cyber attacks is a significant concern. A successful attack on these systems can lead to widespread power outages, transportation shutdowns, or compromised patient care, resulting in dire consequences for society as a whole.
To mitigate the vulnerabilities associated with cyber attacks on IoT devices, several proactive measures can be taken. Device manufacturers need to prioritize security by implementing strong encryption, implementing regular software updates, and providing clear guidelines for user authentication and access controls.
Furthermore, users must be vigilant in securing their IoT devices. This includes changing default passwords, disabling unnecessary features, and regularly updating device firmware. Additionally, cybersecurity education and awareness campaigns are crucial to ensure that users are knowledgeable about the potential risks and how to protect themselves against cyber attacks.
As the number of IoT devices continues to grow, it is imperative that the security of these devices is prioritized at every step. By recognizing the vulnerability to cyber attacks and taking appropriate measures, we can foster a safer and more secure IoT ecosystem for everyone.
Data Breaches and Theft
Data breaches and theft are major risks associated with the use of IoT devices. These devices collect and transmit vast amounts of personal and sensitive data, making them attractive targets for cybercriminals. When IoT devices are compromised, the data they collect can be exposed, leading to severe consequences for individuals and organizations alike.
One significant concern is the potential theft of personally identifiable information (PII) through IoT devices. Connected devices, such as smart home devices or wearables, often collect information like names, addresses, and even biometric data. If this data falls into the wrong hands, it can be used for identity theft, fraud, or other malicious activities. Moreover, IoT devices can also collect behavioral data, which, when combined with other personal information, allows for detailed profiling and potential exploitation of individuals’ privacy.
Corporate data breaches are also a significant concern. IoT devices have become integral components of many businesses, connecting various systems and facilitating data exchange. If these devices are not properly secured, attackers can gain access to valuable company data, trade secrets, and intellectual property. This can result in financial losses, damage to reputation, and a competitive disadvantage in the market.
Furthermore, IoT devices can also serve as gateways for breaching wider networks. Even if the device itself does not contain valuable information, it can be used as a stepping stone to gain access to other interconnected devices or systems. This can lead to more significant data breaches, affecting not only individuals but also entire networks or organizations.
To mitigate the risks associated with data breaches and theft, it is crucial to implement strong security measures. This includes robust encryption algorithms to protect data both in transit and at rest, regular software updates to address vulnerabilities, and network segmentation to minimize the impact of a potential breach.
Individuals can also take proactive steps to protect their data. This includes reviewing privacy settings of IoT devices, limiting the collection of unnecessary data, and being cautious about the information shared with these devices. Regular monitoring of account activity and promptly reporting any suspicious behavior is essential in detecting and mitigating potential breaches.
Furthermore, regulatory bodies play a vital role in establishing and enforcing data protection laws and standards. These regulations help ensure that organizations and manufacturers follow best practices to protect user data and take appropriate measures in case of a breach.
By understanding the risks and implementing appropriate security measures, individuals and organizations can minimize the chances of falling victim to data breaches and theft. It is crucial to adopt a proactive approach and stay updated with the latest security advancements to safeguard our data and protect our privacy in an increasingly connected world.
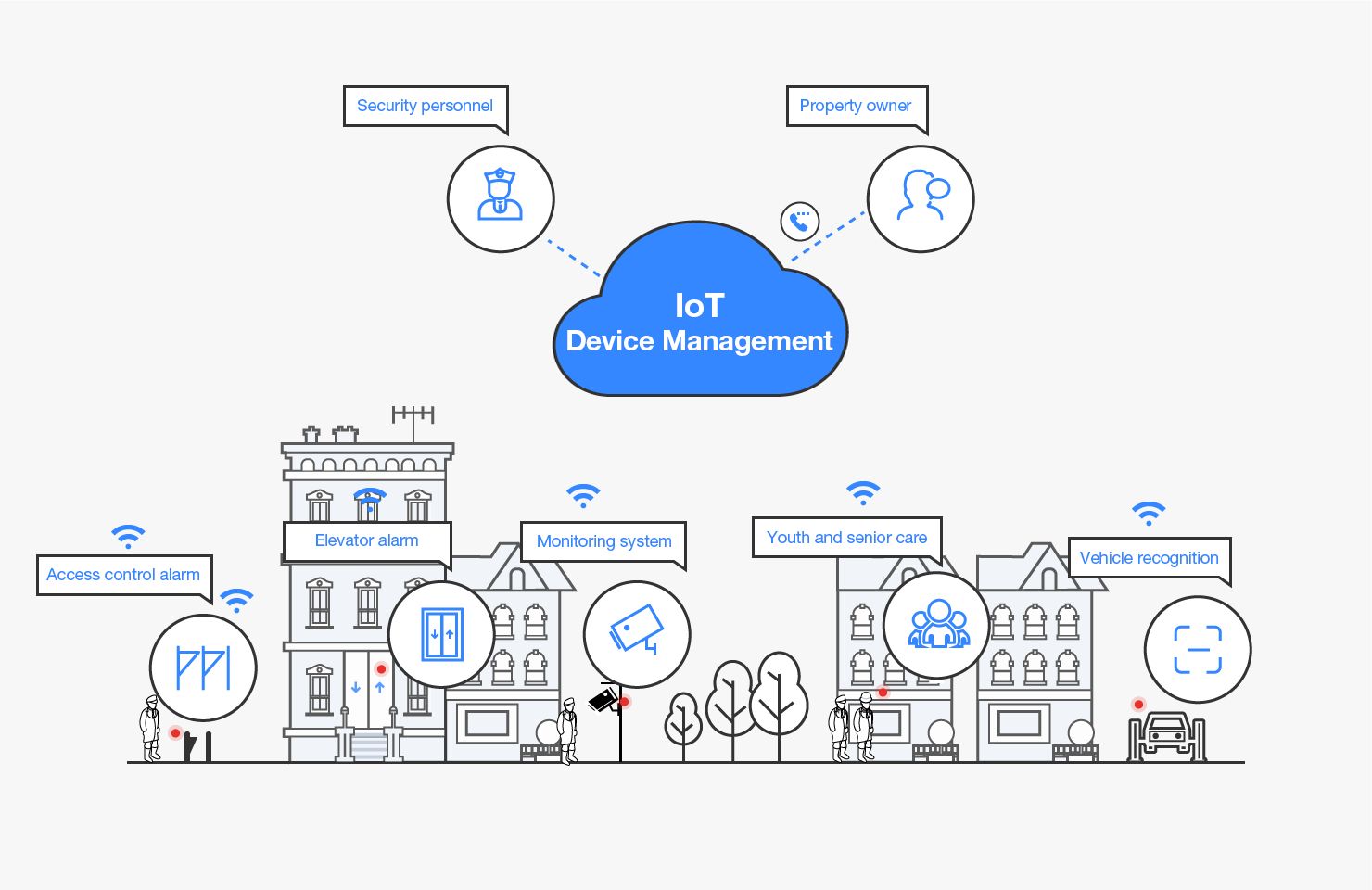
Unauthorized Access and Control
One of the risks associated with IoT devices is the potential for unauthorized access and control. Due to weak security measures and vulnerabilities, these devices can be compromised, allowing attackers to gain control over them remotely.
Unauthorized access to IoT devices can have various implications depending on the type of device being compromised. In the case of smart home devices, unauthorized access can lead to intrusion into people’s private spaces, compromising their security and privacy. Attackers may be able to tamper with security systems, unlock doors, or even manipulate surveillance cameras, posing a direct threat to the safety and well-being of individuals and their property.
Similarly, unauthorized access to IoT devices in healthcare settings can have serious consequences. For instance, connected medical devices such as insulin pumps or pacemakers can be targeted by hackers, potentially leading to life-threatening situations for patients. The ability to remotely control these devices can result in altering prescribed dosages, disabling critical functionalities, or even causing harm to patients.
Moreover, unauthorized control over IoT devices can also be exploited for nefarious purposes. Compromised devices can be used as part of a botnet, a network of infected devices controlled by an attacker. These botnets can be used to launch large-scale cyber attacks or carry out illegal activities, such as cryptocurrency mining or spreading malware.
To mitigate the risks of unauthorized access and control, stringent security measures are essential. Device manufacturers must prioritize security by implementing strong authentication mechanisms, encryption protocols, and regular software updates. Additionally, users should follow best practices such as changing default login credentials, disabling unnecessary features, and keeping devices and firmware up-to-date.
Network segmentation is also crucial in limiting the potential impact of a compromised device. By separating IoT devices from critical systems or sensitive information, the potential for unauthorized access to spread is minimized.
Furthermore, continuous monitoring and anomaly detection can help identify and address any signs of unauthorized access. Users should be vigilant in monitoring device activity, checking for any unusual behavior or unauthorized connections, and promptly reporting them to appropriate authorities or device manufacturers.
As IoT devices become increasingly integrated into various aspects of our lives, it is crucial to recognize the risks associated with unauthorized access and control. By implementing robust security measures and staying informed about the latest vulnerabilities and best practices, we can safeguard ourselves against potential threats and ensure the integrity and safety of our IoT devices and systems.
Lack of Regulation and Standardization
One of the challenges surrounding the use of IoT devices is the lack of comprehensive regulation and standardization. The rapid growth of IoT technology has outpaced the development of necessary guidelines and industry standards, leaving a gap in ensuring consistent quality, security, and interoperability of these devices.
The absence of regulation and standardization poses several risks. Firstly, it leads to a lack of consistency in terms of security practices and protocols. With no standardized security requirements, manufacturers may prioritize cost and convenience over implementing robust security measures, leaving devices vulnerable to cyberattacks and privacy breaches. This lack of uniformity makes it challenging for consumers to assess the security capabilities of different IoT devices and make informed decisions.
Moreover, the lack of regulation can lead to variations in data handling and privacy practices. IoT devices collect and transmit vast amounts of personal and sensitive information, raising concerns about how this data is stored, shared, and protected. Without clear regulations and standards in place, there is a risk that personal data may be mishandled, leading to privacy breaches and potential misuse of information.
The lack of standardization also affects interoperability among different IoT devices. As the number and variety of IoT devices continue to expand, ensuring seamless communication and compatibility between devices from different manufacturers becomes crucial. However, without standardized protocols, achieving interoperability becomes a significant challenge. This can limit the potential benefits and functionalities of IoT devices, hindering their full integration and utilization in various industries and settings.
To address these challenges, industry stakeholders, regulatory bodies, and policymakers need to collaborate to develop comprehensive regulations and establish robust standards for IoT devices. These regulations should cover aspects such as security requirements, data handling practices, and interoperability protocols. By implementing clear guidelines, manufacturers will be incentivized to prioritize security and privacy, providing consumers with reliable and secure devices.
Additionally, standardization efforts can help address the interoperability issue. By establishing common protocols and frameworks, IoT devices from different manufacturers can seamlessly communicate and work together, unlocking the full potential of IoT technology.
Ultimately, the establishment of regulations and standards is crucial to ensure the safe, secure, and effective use of IoT devices. By promoting consistent practices across the industry, users can have greater confidence in the security and reliability of these devices, and the potential risks associated with the lack of regulation and standardization can be minimized.
Potential for Physical Harm
While the benefits of IoT devices are undeniable, their increasing integration into critical systems and everyday life introduces the potential for physical harm. The interconnected nature of these devices and their ability to control physical objects and environments can lead to significant risks and dangers.
One concern is the potential for accidents or malfunctions that can result in bodily harm. For example, in industrial settings, IoT devices are often used to automate processes and control machinery. If these devices fail or are compromised, it can lead to disastrous consequences, such as equipment malfunctions, accidents, or even injuries to workers. Similarly, in smart homes, IoT devices that control electrical appliances or security systems can pose risks if they are not functioning properly or susceptible to hacking attempts.
Medical IoT devices also carry inherent risks. Connected health devices and wearables, such as insulin pumps or pacemakers, have the potential to malfunction or be compromised. This can result in incorrect dosages or disruptions to critical medical functions, leading to severe health complications or even loss of life.
Furthermore, the potential for physical harm extends to the transportation sector. Connected cars and autonomous vehicles rely on IoT technology for navigation, control systems, and safety features. However, if these devices are not properly secured, they can be vulnerable to hacking attempts, potentially leading to accidents and endangering the lives of passengers, drivers, and pedestrians.
To mitigate the potential for physical harm, stringent safety guidelines and protocols need to be established. Manufacturers must prioritize safety in the design and production of IoT devices, implementing fail-safe mechanisms and rigorous testing procedures. Compliance with industry safety standards is crucial to ensure that these devices meet stringent safety requirements.
Furthermore, governmental regulatory bodies need to establish and enforce thorough safety regulations for IoT devices. These regulations should include rigorous certification processes and regular safety audits to guarantee the reliability and safe operation of these devices. Collaboration between manufacturers, users, and regulatory bodies is vital to identify potential risks and implement effective safety measures.
At an individual level, users should exercise caution when integrating IoT devices into their lives. This includes regular monitoring and maintenance of devices, promptly addressing any signs of malfunction or unusual behavior. Following manufacturer guidelines, installing security updates, and seeking professional assistance when needed can contribute to safer usage of IoT devices.
By recognizing the potential risks for physical harm and implementing appropriate safety measures, we can help ensure that IoT devices are utilized in a way that prioritizes the well-being and safety of individuals and the broader community.
Dependence on Internet Connectivity
One of the notable risks associated with the use of IoT devices is the heavy dependence on internet connectivity. IoT devices rely on a stable and reliable internet connection to function properly and deliver their intended benefits. However, this dependence introduces several challenges and vulnerabilities.
First and foremost, any disruption in internet connectivity can render IoT devices useless or limit their functionality. For instance, smart home devices that control lighting, heating, or security systems may become non-responsive during a network outage, causing inconvenience and potentially compromising safety and security.
Moreover, the constant need for internet connectivity means that IoT devices are susceptible to traditional network-related risks, such as network congestion or bandwidth limitations. These issues can impact the performance and responsiveness of IoT devices, leading to delays or inefficiencies in the intended operations. For example, latency or delays in communication can be detrimental in critical scenarios, such as in healthcare settings, where time-sensitive IoT devices play a significant role in monitoring and providing necessary care.
Additionally, the dependence on the internet introduces a potential point of failure for IoT devices. If the internet connection is compromised, it opens up opportunities for unauthorized access, control, or manipulation of these devices. Cybercriminals can exploit vulnerabilities in the network or take advantage of weak security measures to infiltrate IoT devices or disrupt their functionality.
To mitigate the risks associated with dependence on internet connectivity, alternate backup systems can be implemented. For example, local storage capabilities or offline functionalities can allow IoT devices to operate even during temporary internet outages. This ensures that critical operations can continue without interruption and reduces the reliance on constant connectivity.
Users should also be cautious when selecting and configuring IoT devices, ensuring that they have the ability to function in offline mode or offer redundancy options. Additionally, implementing strong security measures, such as utilizing firewalls and encryption protocols, can help protect IoT devices from unauthorized access or manipulation, even if the internet connection is compromised.
Furthermore, broadband providers and network infrastructure stakeholders must work towards ensuring consistent and reliable internet connectivity. By addressing issues related to network congestion, bandwidth limitations, and security vulnerabilities, they can contribute to a more robust IoT ecosystem.
The potential risks and challenges associated with dependence on internet connectivity highlight the need for a comprehensive approach that considers alternative solutions, improved infrastructure, and enhanced security measures. By addressing these concerns, we can maximize the benefits of IoT devices while minimizing the impact of potential disruptions in internet connectivity.
Reliability and Compatibility Issues
Reliability and compatibility issues are common challenges that users encounter when using IoT devices. These issues arise due to the vast range of devices available, varying technological standards, and the rapid evolution of IoT technology.
Reliability issues can arise from the complexity of IoT devices and their reliance on multiple components working together seamlessly. Device malfunctions, firmware bugs, or connectivity problems can occur, leading to a loss of functionality or degraded performance. For example, a smart home device may fail to respond to commands or experience intermittent connectivity, causing frustration for users and undermining the overall benefits of the device.
Compatibility issues are another concern with the proliferation of IoT devices. With different manufacturers, protocols, and communication standards in play, ensuring compatibility between different devices can be challenging. A lack of standardization can result in devices from different manufacturers having difficulties communicating or integrating effectively with each other. This can limit the full potential of IoT devices and hinder the seamless automation and coordination that users expect.
To address reliability and compatibility issues, device manufacturers need to prioritize quality assurance, testing, and ongoing support for their products. Regular firmware updates that address known bugs and vulnerabilities are essential for maintaining device reliability. Additionally, manufacturers should strive to adhere to industry standards and interoperability protocols to enhance compatibility between devices.
For users, proper research and due diligence are vital when selecting IoT devices. Checking reviews, seeking recommendations, and verifying compatibility with existing devices or systems can help mitigate potential issues. Users should also ensure that firmware updates are promptly installed to ensure optimal performance and security.
Furthermore, industry collaborations and standards-setting bodies play a crucial role in addressing reliability and compatibility challenges. The development and adoption of uniform standards and protocols can promote interoperability across different devices and facilitate a more seamless integration of IoT systems.
Working towards a more reliable and compatible IoT ecosystem requires continuous improvement, collaboration, and industry-wide efforts. By prioritizing quality, adhering to standards, and fostering interoperability, we can enhance the user experience and maximize the potential benefits that IoT technology offers.
Ethical Concerns and Misuse of Data
The widespread adoption of IoT devices has raised significant ethical concerns regarding the collection, use, and potential misuse of data. IoT devices generate an enormous amount of personal and sensitive data, ranging from location information and behavioral patterns to health records and biometric data. This data presents both opportunities and risks, highlighting the need for ethical considerations in their usage.
One of the key concerns revolves around consent and privacy. Users may not always be fully aware of the data that IoT devices collect or how it is being used. Lack of transparency and inadequate consent mechanisms can lead to a breach of privacy and user trust. This puts individuals at risk of having their personal information exploited or shared without their knowledge or consent.
The potential for data misuse is another significant ethical concern. IoT devices can become targets for hackers or unauthorized actors seeking to exploit the data they collect. This can lead to identity theft, fraud, or the manipulation of sensitive information for malicious purposes. Moreover, the integration of IoT devices in critical systems such as healthcare or transportation raises concerns about the potential risks and harm that can result from data breaches or unauthorized access.
There is also a risk of data discrimination and unfair profiling based on the data collected by IoT devices. Automated decision-making algorithms that rely on this data can lead to biases and discriminatory outcomes, disadvantaging certain individuals or groups. For example, insurance companies may use health data collected from wearable devices to determine premiums, potentially discriminating against individuals with certain health conditions.
To address these ethical concerns, strict data protection regulations and privacy guidelines are essential. Users need to have control over their data, including the ability to access, modify, or delete it as needed. Transparent data collection practices, understandable privacy policies, and informed consent mechanisms are crucial in ensuring ethical use of IoT devices.
Manufacturers and organizations must also prioritize data security and implement robust measures to protect data from unauthorized access and misuse. This includes encryption, strong authentication protocols, and regular security audits.
Additionally, ethical considerations should be integrated into the design and development of IoT devices. This includes incorporating privacy-enhancing features, minimizing data collection to what is necessary, and designing systems that prioritize user control and autonomy over their personal information.
As users, it is important to be mindful of the data we share and to regularly review privacy settings on IoT devices. By being selective about the data we provide and being vigilant about the devices we use, we can mitigate the risks of data misuse and contribute to a more ethical and responsible use of IoT technology.
Conclusion
The widespread adoption of IoT devices brings numerous benefits and conveniences to our lives. However, it is crucial to acknowledge and address the risks and challenges that come with their use. From security and privacy concerns to compatibility issues and ethical considerations, these risks require our attention to ensure the responsible and safe integration of IoT technology in our daily lives.
The lack of security and privacy measures poses a significant risk, as IoT devices can be vulnerable to cyber attacks and data breaches. Strengthening security protocols, raising awareness, and implementing best practices are necessary to mitigate these risks and protect our personal information.
Moreover, unauthorized access and control of IoT devices can lead to privacy breaches and potential manipulation of critical systems. By prioritizing security, implementing strong authentication mechanisms, and being vigilant about device management, we can reduce the likelihood of unauthorized access and control.
The lack of regulation and standardization further complicates the IoT landscape. Establishing comprehensive regulations and industry standards is essential to ensure consistency, interoperability, and user safety across different IoT devices.
The potential for physical harm should not be overlooked, as IoT devices have the ability to control machinery and affect our safety. By prioritizing safety in design, adhering to industry standards, and implementing fail-safe mechanisms, we can stave off potential accidents and protect individuals from harm.
Dependence on internet connectivity introduces its own set of challenges, such as disruptions in functionality and susceptibility to network-related risks. By considering alternative backup systems and ensuring robust internet connectivity, we can enhance the reliability and availability of IoT devices.
Compatibility issues and reliability concerns can impact user experience and limit the full potential of IoT devices. Prioritizing quality assurance, adhering to interoperability protocols, and promoting collaboration within the industry are crucial steps in addressing these challenges.
Lastly, it is imperative to address the ethical concerns surrounding the use of IoT devices. Transparency, informed consent, data protection, and fairness in data use are vital to ensure the responsible and ethical integration of IoT technology into our lives.
In conclusion, by acknowledging and proactively addressing the risks and challenges associated with IoT devices, we can foster an environment that maximizes their benefits while mitigating potential harm. Through collaboration between users, industry stakeholders, and regulators, we can create a safer, more secure, and ethically conscious IoT ecosystem that enhances our lives and protects our privacy, security, and overall well-being.