Introduction
The Internet of Things (IoT) has revolutionized the way we interact with technology, connecting devices and enabling them to communicate with each other via the internet. From smart homes to wearable devices, IoT has transformed various industries, making our lives more convenient and efficient. However, with the increasing interconnectivity comes a significant concern: cybersecurity.
As we rely more and more on IoT devices, it becomes crucial to prioritize their security to protect sensitive information and ensure privacy. The intersection of IoT and cybersecurity has given rise to the necessity of implementing effective measures to safeguard against potential risks and vulnerabilities. Understanding the importance of IoT cybersecurity and the challenges it presents is essential for individuals and organizations alike.
This article will explore the concept of IoT in cybersecurity, the potential risks involved, the challenges faced, and effective solutions and best practices to secure IoT devices.
By gaining an understanding of these key aspects, individuals and businesses can take proactive steps to address the cybersecurity concerns associated with IoT, ensuring a safe and secure environment for the deployment and usage of IoT devices.
What is the Internet of Things (IoT)?
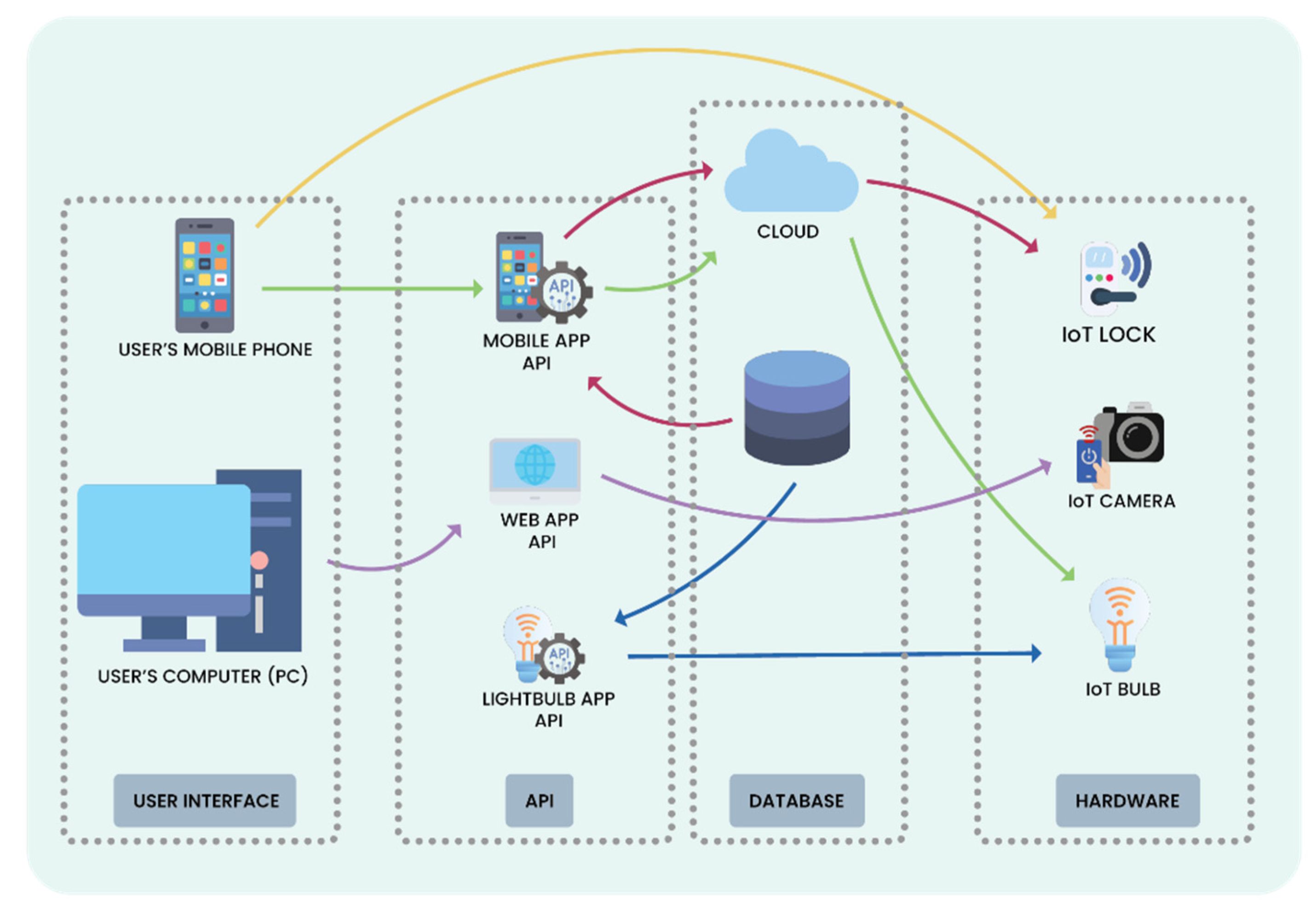
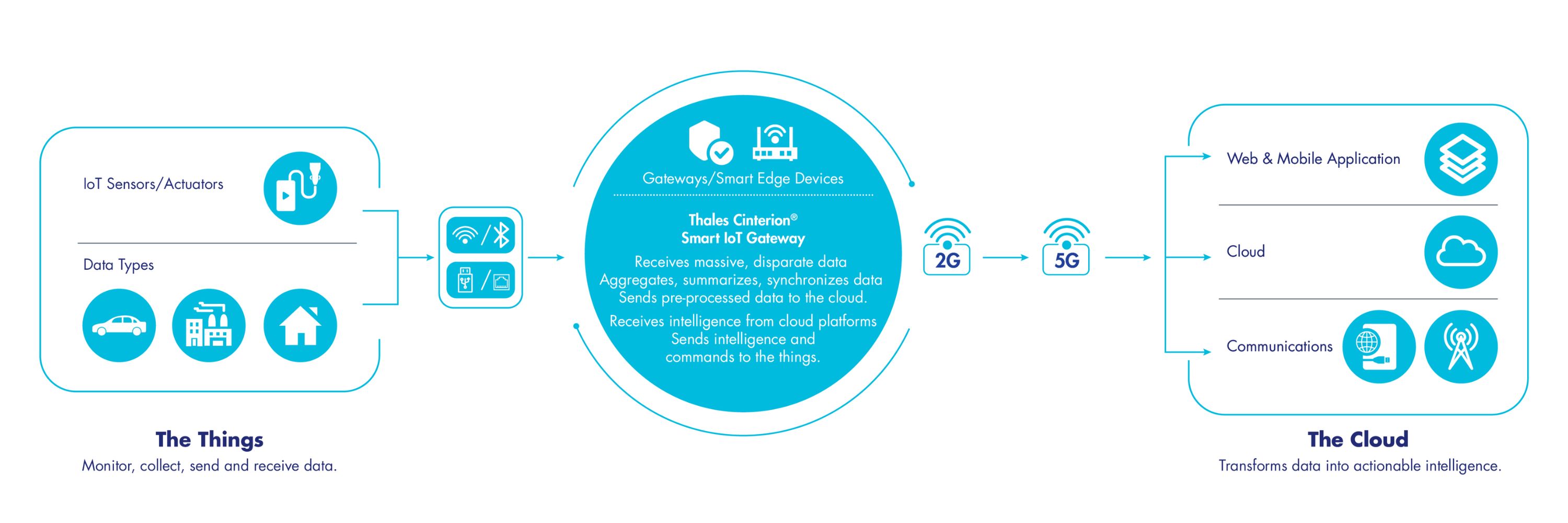
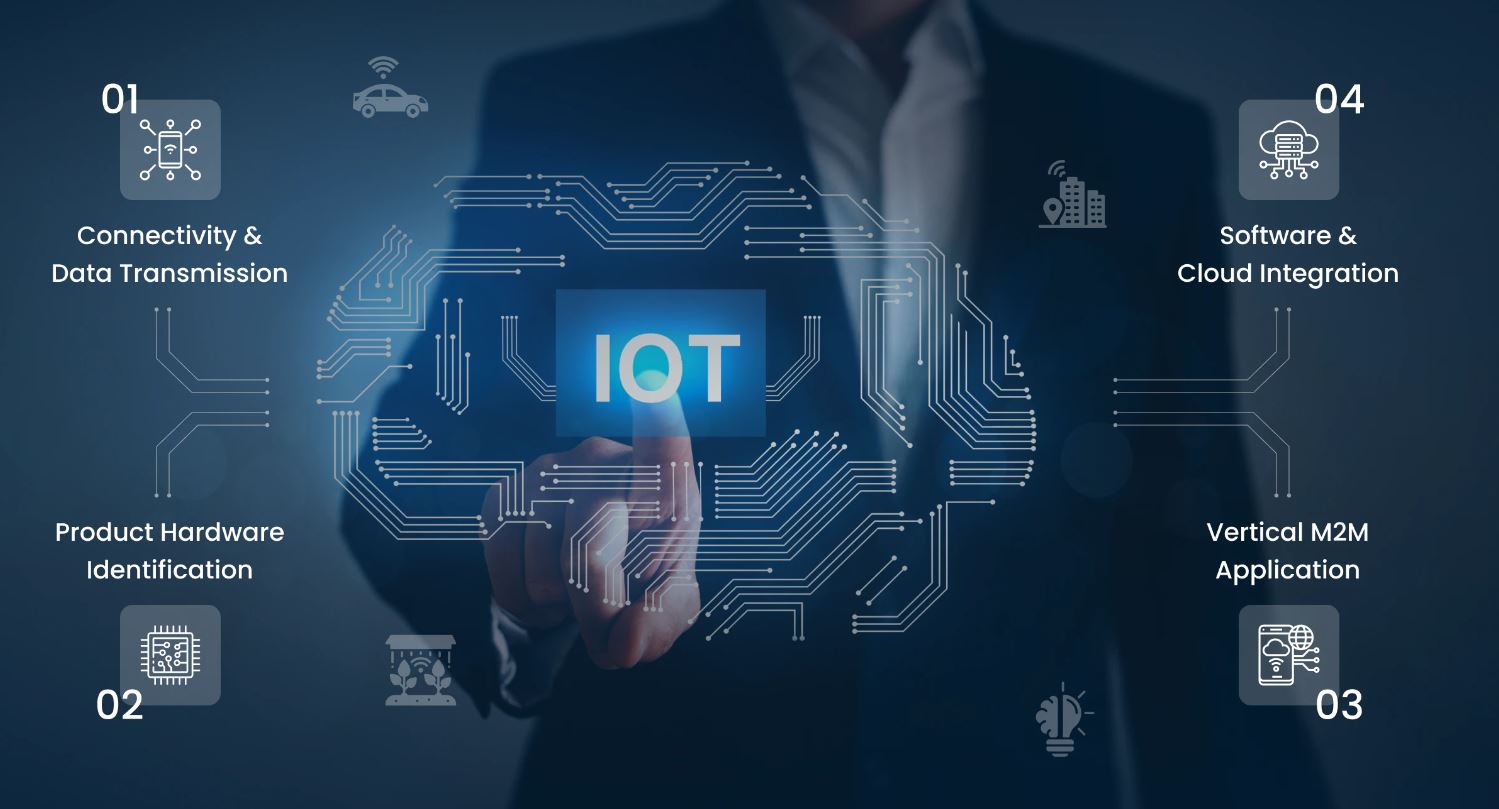
The Internet of Things (IoT) refers to a network of interconnected physical devices, vehicles, appliances, and other objects that are embedded with sensors, software, and network connectivity to enable them to gather and exchange data. These devices, often referred to as “smart” devices, can include anything from smartphones and wearables to home appliances and industrial machinery.
The core principle of IoT is to connect and share information between these devices, allowing them to communicate and interact with each other autonomously, with minimal human intervention. This interconnectedness enables numerous possibilities and applications in various fields, such as healthcare, transportation, agriculture, manufacturing, and more.
IoT devices collect vast amounts of data through sensors and transmit it over the internet, where it can be analyzed and utilized to improve efficiency, enhance decision-making processes, and create innovative solutions. This data-driven approach has the potential to transform industries by enabling real-time monitoring, predictive maintenance, and personalized experiences.
For example, in a smart home, IoT devices like thermostats, security cameras, and lighting systems can be connected and controlled remotely through a smartphone or a virtual assistant. These devices can collect data about energy consumption, occupancy patterns, and environmental conditions, allowing homeowners to optimize energy usage, improve security, and enhance their overall living experience.
Similarly, in healthcare, IoT devices like fitness trackers and remote patient monitoring systems can gather health data and provide insights to healthcare professionals, enabling preventive care, remote monitoring of chronic conditions, and faster response to emergencies.
The possibilities with IoT are vast, and it is estimated that by 2025, there will be more than 41 billion connected IoT devices worldwide, generating an immense amount of data.
However, with this increased connectivity and data exchange comes the need for robust security measures to protect against potential threats and vulnerabilities. The next section will delve into the importance of IoT in cybersecurity.
The Importance of IoT in Cyber Security
The growing adoption of IoT devices has introduced new cybersecurity challenges that cannot be ignored. IoT devices, with their interconnected nature and access to sensitive data, have become attractive targets for cybercriminals. This makes it crucial for individuals and organizations to understand the importance of IoT in cybersecurity.
One of the primary reasons why IoT is essential in cybersecurity is the sheer number of devices connected to the internet. With billions of IoT devices in use, the attack surface for potential cyber threats expands significantly. Each connected device represents a potential entry point for hackers to access networks and compromise security.
Furthermore, IoT devices often have limited computing power and resources, making them more vulnerable to attacks. They may lack robust security features or have outdated firmware that leaves them susceptible to exploitation. This highlights the necessity for strong cybersecurity measures to protect these devices and the data they handle.
Moreover, IoT devices are used in various critical sectors, including healthcare, energy, transportation, and infrastructure. Any breach or compromise of these devices can have severe consequences, including compromising patient data, disrupting essential services, or causing physical harm. The importance of securing IoT devices in these sectors cannot be overstated.
Additionally, IoT devices are often integrated into existing networks and systems, creating potential entry points for cyber attacks. If a vulnerable IoT device is connected to an enterprise network, it can become an entry point for attackers to bypass traditional security measures and gain unauthorized access to sensitive data or launch other attacks.
The interconnected nature of IoT devices also means that a compromise in one device can lead to a domino effect, compromising the security of other devices and systems. This highlights the critical need for comprehensive security strategies and measures to protect the entire IoT ecosystem.
By recognizing the importance of IoT in cybersecurity, individuals and organizations can take proactive steps to mitigate the risks associated with IoT devices. This involves implementing strong authentication protocols, encryption methods, intrusion detection systems, and regular firmware updates to safeguard IoT devices.
The next section will discuss the potential risks and vulnerabilities associated with IoT devices in more detail, emphasizing the need for robust cybersecurity solutions.
Potential Risks and Vulnerabilities in IoT
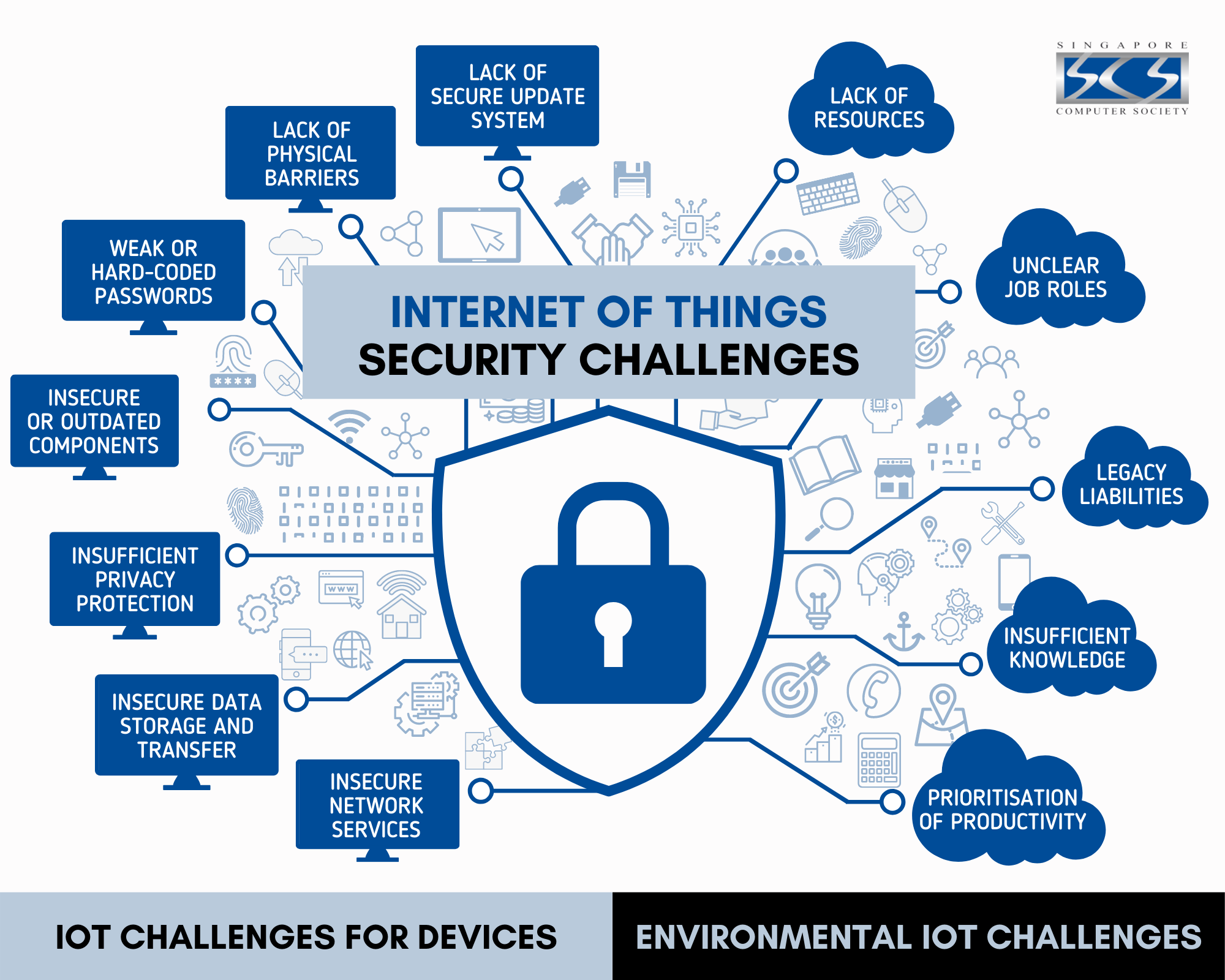
The rapid growth of the Internet of Things (IoT) has brought forth various potential risks and vulnerabilities that need to be addressed to ensure the security of IoT devices and the data they handle. Understanding these risks and vulnerabilities is crucial in developing effective cybersecurity strategies for IoT ecosystems.
One of the primary risks in IoT is the lack of robust security measures in many devices. Due to cost and resource constraints, manufacturers may prioritize functionality over security, leaving vulnerabilities that can be exploited by attackers. Weak or default passwords, unencrypted communication, and insecure firmware are common security gaps that hackers can exploit to gain unauthorized access to IoT devices.
Another significant risk is the potential for data breaches and privacy violations. IoT devices collect and transmit vast amounts of data, often including personal and sensitive information. If these devices are not adequately protected, hackers can intercept, tamper with, or steal the data, leading to identity theft, financial fraud, or other privacy breaches. Additionally, the aggregation of data from multiple devices can lead to the creation of comprehensive profiles that violate users’ privacy.
Furthermore, IoT devices can also be vulnerable to various types of attacks, such as denial-of-service (DoS) attacks and botnet attacks. In a DoS attack, hackers overwhelm a device or network with a flood of requests, causing it to become unresponsive or crash. Botnet attacks involve infecting multiple IoT devices with malware and using them to launch coordinated attacks or carry out malicious activities without the device owner’s knowledge.
Physical attacks on IoT devices are also a concern. As many IoT devices are deployed in public spaces or industrial settings, they can be physically tampered with or stolen. Manipulating devices or extracting data directly from them poses a significant risk, especially in sectors such as transportation or infrastructure where the physical integrity of these devices is crucial.
Additionally, the complexity of IoT ecosystems, with multiple devices and communication protocols, introduces challenges in detecting and preventing attacks. Legacy devices that lack necessary security features may compromise the overall security of the network, allowing attackers to gain access to other connected devices.
Addressing these risks and vulnerabilities requires a multi-faceted approach that encompasses both technological and operational measures. The next section will explore the security challenges in IoT and discuss potential solutions to mitigate these risks.
Security Challenges in IoT
The widespread adoption of Internet of Things (IoT) devices has introduced various security challenges that need to be overcome to ensure the safety and integrity of IoT ecosystems. These challenges stem from the unique characteristics of IoT, such as the vast number of devices, diverse communication protocols, and limited resources in individual devices.
One of the primary challenges in IoT security is the sheer scale of interconnected devices. With billions of IoT devices in use, managing and securing them becomes a complex task. Each device represents a potential entry point for attackers, and ensuring the security of every device in the ecosystem is a challenging feat.
Another challenge is the diversity of communication protocols used in IoT. Devices may use different protocols, such as Wi-Fi, Bluetooth, Zigbee, or cellular networks, each with its own set of security considerations. Coordinating and securing the communication between different devices and protocols requires careful planning and implementation of robust security measures.
The limited resources of IoT devices also pose significant challenges. Many IoT devices have limited computing power, storage capacity, and battery life. Implementing strong security measures on such devices without compromising their functionality or usability is a delicate balance. Device manufacturers must consider resource-efficient security solutions to ensure the protection of these devices.
The lifecycle management of IoT devices is another security challenge. IoT devices are often deployed for long periods, and some may have limited capabilities for software updates or firmware patches. This leaves them vulnerable to known vulnerabilities that could be exploited by attackers. Ensuring regular updates and patches to address security flaws throughout the lifecycle of these devices is critical.
The lack of standardization and regulatory frameworks in IoT also presents a challenge. With various manufacturers producing different devices and protocols, achieving consistent security standards becomes difficult. Establishing industry-wide guidelines and regulations can help ensure minimum security requirements and enhance interoperability among devices.
Furthermore, the complexity of IoT environments, with multiple layers of interaction and data exchange, increases the potential attack surface. The interconnectedness between devices, networks, and cloud platforms creates opportunities for attackers to exploit vulnerabilities at different points in the ecosystem. Comprehensive security measures must be implemented at each layer to protect the entire IoT ecosystem.
Addressing these challenges requires a collaborative effort between manufacturers, service providers, policymakers, and consumers. The next section will delve into potential solutions and best practices for securing IoT devices and mitigating the risks associated with them.
Cyber Security Solutions for IoT
The unique challenges posed by the Internet of Things (IoT) require robust cybersecurity solutions to ensure the safety and integrity of IoT devices and the data they handle. Implementing effective security measures in IoT ecosystems is crucial in mitigating risks and protecting against potential threats. Here are some cyber security solutions specifically tailored for IoT:
1. Secure Authentication and Access Control: Implementing strong authentication mechanisms, such as multi-factor authentication or biometrics, helps ensure that only authorized individuals or devices can access IoT devices and networks. Access control policies should be enforced to restrict and manage access privileges effectively.
2. Encryption and Data Privacy: Encrypting data at rest and in transit helps protect sensitive information from being intercepted or tampered with. Additionally, data privacy regulations should be adhered to, ensuring that user data is handled and stored securely.
3. Regular Software Updates: Manufacturers should provide regular software updates and patches to address security vulnerabilities in IoT devices. Users should be encouraged to install updates promptly to ensure their devices are protected.
4. Network Segmentation: Segmenting IoT devices into separate networks or VLANs helps contain potential compromises and limits the lateral movement of attackers. It prevents unauthorized access to critical resources or other devices connected to the same network.
5. Intrusion Detection and Monitoring: Implementing intrusion detection systems (IDS) and monitoring solutions enables real-time detection of suspicious activities and potential security breaches. These solutions can alert administrators when anomalies are detected, allowing for immediate response and remediation.
6. Threat Intelligence and Vulnerability Management: Continuous monitoring and assessment of potential threats and vulnerabilities are crucial in staying ahead of emerging risks. Utilizing threat intelligence feeds and conducting regular vulnerability assessments helps identify and mitigate security weaknesses.
7. Secure Firmware and Supply Chain Management: Implementing secure development practices ensures that IoT devices have trustworthy firmware. Additionally, monitoring the supply chain to identify any tampering or malicious modifications during device manufacturing and distribution is essential.
8. User Education and Awareness: Educating users about IoT security best practices, such as creating strong passwords, avoiding public Wi-Fi networks, and being cautious of suspicious emails or links, helps prevent common security pitfalls and strengthens the overall security posture.
9. Collaboration and Standardization: Encouraging collaboration and standardization among manufacturers, policymakers, and industry stakeholders promotes consistent security practices, interoperability, and the establishment of security frameworks.
By implementing these cyber security solutions, individuals and organizations can enhance the security of IoT devices and reduce the risks associated with their deployment and usage. However, it’s important to note that security is an ongoing process, and continual monitoring, updates, and adaptation are necessary to stay ahead of evolving threats in the ever-expanding IoT landscape.
Best Practices for Securing IoT Devices
Securing Internet of Things (IoT) devices is crucial to mitigate risks and ensure the integrity of connected ecosystems. Implementing best practices for IoT security can help individuals and organizations protect their devices, data, and networks. Here are some recommended best practices for securing IoT devices:
1. Change Default Credentials: The first step in securing IoT devices is to change the default credentials (username and password) immediately after installation. Many devices come with generic or well-known default credentials, making them an easy target for attackers.
2. Keep Firmware Updated: Manufacturers often release firmware updates to address security vulnerabilities. Regularly check for updates and install them promptly to ensure that your devices have the latest security patches.
3. Disable Unnecessary Features: Disable any features or services on your IoT devices that are not essential for their intended purpose. Each enabled feature increases the potential attack surface, so limit functionality to minimize security risks.
4. Implement Network Segmentation: Separate IoT devices into their own network segment to isolate them from other connected devices. This helps contain potential compromises and limits the extent of any successful attack.
5. Enable Network Encryption: Make sure the communication between your IoT devices and your network is encrypted. Ensure that strong encryption protocols such as WPA2 or WPA3 are being used to secure wireless connections.
6. Utilize Secure Protocols: Use secure communication protocols such as HTTPS, MQTT with TLS, or SSH for device management and data transmission. These protocols provide encryption and authentication, protecting against eavesdropping and unauthorized access.
7. Conduct Regular Vulnerability Scans: Regularly scan your IoT devices and network for vulnerabilities using professional vulnerability scanning tools. This helps identify any weaknesses or security gaps that need immediate attention.
8. Disable Universal Plug and Play (UPnP): Disable UPnP on your IoT devices and routers. UPnP can expose vulnerable devices to attacks by allowing automatic port forwarding, which could be exploited by attackers.
9. Assess Third-Party Security: When using third-party IoT applications or services, evaluate their security practices and reputation. Ensure that they have implemented proper security measures to protect your data and devices.
10. Regularly Monitor and Audit: Monitor your IoT devices and network for any suspicious activities or unusual behavior. Enable logging and auditing features to keep track of device activities, allowing for quick detection of potential security incidents.
11. Stay Informed: Keep yourself updated on the latest security threats, vulnerabilities, and best practices. Regularly check reputable sources for security advisories and patches related to your IoT devices.
12. Educate Users: Promote IoT security awareness among all users, whether it’s individuals in a home environment or employees in an organization. Educate them about the potential risks and the importance of following security practices when using IoT devices.
By following these best practices, individuals and organizations can enhance the security of their IoT devices and reduce the likelihood of falling victim to attacks. Remember, IoT security should be an ongoing effort, with regular updates, monitoring, and adaptation to combat emerging threats in the ever-evolving cybersecurity landscape.