Introduction
Welcome to the guide on how to lock workstations after inactivity. In today’s digital world, where information security is paramount, it is crucial to implement measures that protect sensitive data and prevent unauthorized access. One effective way to enhance security is by automatically locking workstations when they remain inactive for a specified period of time.
When workstations are left unattended, they are vulnerable to prying eyes, whether it’s in an office setting or a public environment. Unauthorized access to workstations can result in compromised data, security breaches, and potential financial loss. By implementing workstation locking after inactivity, individuals and organizations can significantly reduce the risk of these security threats.
Locking workstations after a certain period of inactivity ensures that only authorized individuals have access to sensitive information. It acts as a safeguard, preventing unauthorized users from tampering with files, installing malicious software, or gaining administrative privileges. Additionally, automatic locking serves as a reminder for individuals to secure their workstations and maintain privacy, even when taking short breaks.
In this guide, we will explore various methods to implement workstation locking after inactivity. We will cover built-in Windows settings, third-party software, scripting or batch files, and the implementation of Group Policy settings. Each method offers unique advantages and can be tailored to meet the specific requirements of different environments and user preferences.
Whether you are an individual looking to secure your personal workstation or an IT professional responsible for securing a network of workstations, this guide will provide you with the necessary steps to implement effective workstation locking after inactivity.
Why Locking Workstations After Inactivity is Important
Locking workstations after a period of inactivity is an essential security practice that helps protect sensitive data and prevent unauthorized access. Let’s delve into the reasons why this practice is so important:
1. Prevent Unauthorized Access: When workstations are left unattended without being locked, anyone passing by can potentially gain access to confidential information. Locking a workstation after a period of inactivity ensures that only authorized individuals have access to the system, minimizing the risk of data breaches.
2. Protect Sensitive Data: Workstations often contain sensitive and confidential data, ranging from personal information to business-critical files. By locking the workstation, you prevent unauthorized users from accessing or tampering with this data, ensuring its confidentiality and integrity.
3. Mitigate Security Risks: Inactive unlocked workstations are vulnerable to numerous security risks. Malicious individuals may attempt to install malware, steal sensitive information, or exploit vulnerabilities in the system. Automatic workstation locking significantly reduces these risks by preventing unauthorized interactions.
4. Maintain Compliance: Many industries, such as healthcare and finance, have specific regulatory requirements for safeguarding sensitive data. Implementing workstation locking after inactivity helps organizations meet compliance standards and ensures data protection in accordance with industry regulations.
5. Protect User Privacy: Individual users also benefit from workstation locking, as it helps maintain their privacy. Even in personal settings, workstations may contain personal documents, emails, or financial information that should not be accessible to others. Automatically locking the workstation when idle adds an extra layer of privacy and peace of mind.
6. Promote Security Awareness: Reinforcing the habit of locking workstations after inactivity promotes a culture of security awareness within organizations. It serves as a reminder for individuals to take responsibility for protecting their systems and sensitive information, fostering a security-conscious environment.
By implementing workstation locking after inactivity, individuals and organizations can significantly enhance the security of their systems, protect sensitive data, and reduce the risk of unauthorized access and security breaches.
Methods to Lock Workstations After Inactivity
There are several methods that can be used to lock workstations automatically after a period of inactivity. Let’s explore the different options:
1. Using Built-In Windows Settings: Windows operating systems offer built-in features that allow users to configure workstation locking after a specified idle time. By accessing the Power & Sleep settings, users can set the time interval after which the workstation should lock automatically. This method is straightforward and does not require any additional software or technical expertise.
2. Using Third-Party Software: There are numerous third-party software applications available that specialize in workstation locking and security. These software solutions offer advanced features, such as customizable locking options, multi-factor authentication, and remote management capabilities. Examples of popular third-party software include ClearLock, Predator, and Eusing Maze Lock.
3. Using Scripts or Batch Files: For users with scripting knowledge, creating a script or batch file can be an effective way to automate the workstation locking process. Scripts can be written to monitor user activity and trigger the locking mechanism after a specified period of inactivity. This method allows for customization and flexibility but may require technical expertise to set up and maintain.
4. Implementing Group Policy Settings: In an enterprise environment, administrators can utilize Group Policy settings to enforce workstation locking after a specified idle time for all connected workstations. This method provides centralized control and allows for consistent security policies across the network. Administrators can define the lock timeout, complexity of the workstation unlock process, and other relevant security settings.
It’s important to consider the specific needs and requirements of your environment when choosing a method to lock workstations after inactivity. Factors such as the number of workstations, level of customization required, and available technical expertise should influence your decision.
By implementing one of these methods, you can ensure that workstations are automatically locked when left unattended, maximizing the security of your systems and protecting sensitive data from unauthorized access.
Using Built-In Windows Settings
Windows operating systems provide a convenient built-in feature that allows users to configure workstation locking after a specified period of inactivity. By utilizing the Power & Sleep settings, users can easily enable automatic workstation locking and define the idle time duration.
To configure workstation locking using built-in Windows settings, follow these steps:
Step 1: Open the Start menu and click on the “Settings” gear icon to access the Windows Settings.
Step 2: In the Windows Settings menu, select the “System” option.
Step 3: Within the System settings, choose “Power & Sleep” from the left-hand side navigation menu.
Step 4: In the Power & Sleep settings, scroll down to find the “Screen” section.
Step 5: Adjust the “Turn off display” and “Put the computer to sleep” settings according to your preferences. To enable workstation locking after inactivity, set the times for both options to the desired idle time duration. For example, if you want the workstation to lock after 10 minutes of inactivity, set both “Turn off display” and “Put the computer to sleep” to 10 minutes.
Step 6: Click on the “Additional power settings” link located under the “Related settings” section on the right-hand side.
Step 7: In the Power Options window, click on “Require a password on wakeup” from the left-hand side menu.
Step 8: Next, click on the “Change settings that are currently unavailable” link.
Step 9: Finally, check the box that says “Require a password (recommended)” and click on “Save changes.”
Once these settings are configured, your workstation will automatically lock after the specified idle time duration, and a password will be required to unlock it. This helps ensure the security of your workstation and sensitive data when the system is left unattended.
Using the built-in Windows settings to lock workstations after inactivity is a simple and effective method that does not require any additional software installation. However, keep in mind that this method relies on the user to adhere to the configured settings. It is important to educate users about the workstation locking feature and emphasize its importance in maintaining data security.
Using Third-Party Software
Another method to lock workstations after inactivity is by utilizing third-party software specifically designed for workstation locking and security. These software applications offer additional features and customization options beyond the built-in Windows settings, providing enhanced security and convenience.
Here are some popular third-party software options for locking workstations:
ClearLock: ClearLock is a lightweight and user-friendly software solution that allows users to lock their workstations with a single click. It provides a transparent lock screen that overlays the desktop, obscuring the content and requiring users to enter their password to unlock the workstation. ClearLock offers customizable options, such as defining the unlock sequence and duration of inactivity before locking.
Predator: Predator is a powerful security software that not only provides workstation locking after inactivity but also enables USB device protection. It utilizes a USB key as a physical key to unlock the workstation, enhancing security and preventing unauthorized access. Predator offers features like automatic locking, password customization, and remote control of multiple workstations.
Eusing Maze Lock: Eusing Maze Lock is a stylish and visually appealing software that locks the workstation using a pattern or maze. Users can draw a pattern on the screen to unlock the workstation, adding an extra layer of security. Eusing Maze Lock offers features like predefined lock patterns, customization options, and the ability to lock specific areas of the screen.
When choosing third-party software for locking workstations, consider factors such as ease of use, compatibility with your operating system, and available features. It is recommended to research and read reviews before deciding on a particular software solution.
Using third-party software for workstation locking provides additional security features and customization options for users. These software applications often have more advanced functionalities, such as multi-factor authentication, remote management, and integration with other security systems.
It is important to note that third-party software installations may require administrative privileges and potentially impact system performance. Therefore, it is advisable to consult with your organization’s IT department or follow the installation instructions provided by the software vendor to ensure compatibility and proper configuration.
By utilizing third-party software, you can enhance the security of your workstations and protect sensitive data from unauthorized access in a convenient and customizable manner.
Using Scripts or Batch Files
For users with scripting knowledge, creating a script or batch file can be a powerful method to automate the workstation locking process after a period of inactivity. With this method, you can customize the locking mechanism and tailor it to your specific requirements.
Here’s how you can use scripts or batch files to lock workstations after inactivity:
Step 1: Open a text editor, such as Notepad, to create a new script or batch file.
Step 2: Write the code for monitoring user activity and triggering the workstation lock. You can use programming languages like PowerShell or VBScript to achieve this. For example, in PowerShell, you can write a script that checks for keyboard or mouse activity and initiates the workstation locking process after a specified idle time.
Step 3: Customize the script or batch file based on your preferences. You can define the duration of inactivity before locking, the locking mechanism (such as requiring a password), and any additional actions you want to take when the workstation is locked, such as sending a notification or running a specific command.
Step 4: Save the script or batch file with a meaningful name and the appropriate file extension. For example, save a PowerShell script as “workstation-lock.ps1” or a batch file as “workstation-lock.bat”.
Step 5: Test the script or batch file to ensure it functions as intended. Run the script or batch file, and verify that it successfully locks the workstation after the specified idle time.
Step 6: Optionally, you can create a shortcut to the script or batch file and place it in a convenient location, such as the desktop or taskbar, for easy access.
Using scripts or batch files to lock workstations after inactivity offers flexibility and customization options. You have control over the idle time duration, the locking mechanism, and any additional actions you want to perform when the workstation is locked.
However, it’s important to note that this method requires scripting or coding knowledge and may be more suitable for technically inclined users or IT professionals. Additionally, maintaining and updating the script or batch file may require periodic adjustments to ensure compatibility with system updates or changes.
By utilizing scripts or batch files, you can automate the workstation locking process and enforce security measures that align with your specific needs and preferences.
Implementing Group Policy Settings
In an enterprise environment, administrators can utilize Group Policy settings to enforce workstation locking after a specified idle time for all connected workstations. Group Policy is a powerful tool that allows administrators to centrally manage and configure various settings on multiple computers within a Windows domain.
Here’s how you can implement Group Policy settings to lock workstations after inactivity:
Step 1: Open the Group Policy Management Console (GPMC) on a domain controller or a computer with administrative access to the Group Policy Management.
Step 2: In the GPMC, navigate to the Group Policy Object (GPO) that is linked to the organizational unit (OU) where your workstations are located.
Step 3: Right-click on the GPO, select “Edit,” and the Group Policy Management Editor window will open.
Step 4: Within the Group Policy Management Editor, navigate to “User Configuration” > “Policies” > “Administrative Templates” > “Control Panel” > “Personalization”.
Step 5: Locate the policy setting named “Screen saver timeout” and double-click on it.
Step 6: In the properties window, select the option “Enabled” and set the desired idle time duration before activating the screen saver and locking the workstation.
Step 7: Optionally, adjust other relevant settings such as screen saver options, password requirements, or any additional security policies you want to enforce.
Step 8: Click “Apply” and “OK” to save the changes.
Once the Group Policy settings are applied and propagated to the workstations, users will experience automatic locking of their workstations after the specified idle time duration. The screen saver will activate, and users will be prompted to enter their password to unlock the workstation.
Implementing Group Policy settings for workstation locking provides centralized control and ensures consistent security policies across the network. Administrators can define the lock timeout, complexity of the workstation unlock process, and other relevant security settings based on the organization’s requirements.
It’s important to note that implementing Group Policy settings requires administrative access and a Windows Active Directory domain environment. Additionally, Group Policy changes may take time to propagate to all workstations, so it’s essential to plan and communicate any policy updates effectively.
By utilizing Group Policy settings, administrators can enforce workstation locking after inactivity, maintain a secure computing environment, and protect sensitive data from unauthorized access in an efficient and centralized manner.
Tips for Effective Workstation Locking
Implementing workstation locking after inactivity is an important step in enhancing security and protecting sensitive data. However, to maximize the effectiveness of this security measure, consider the following tips:
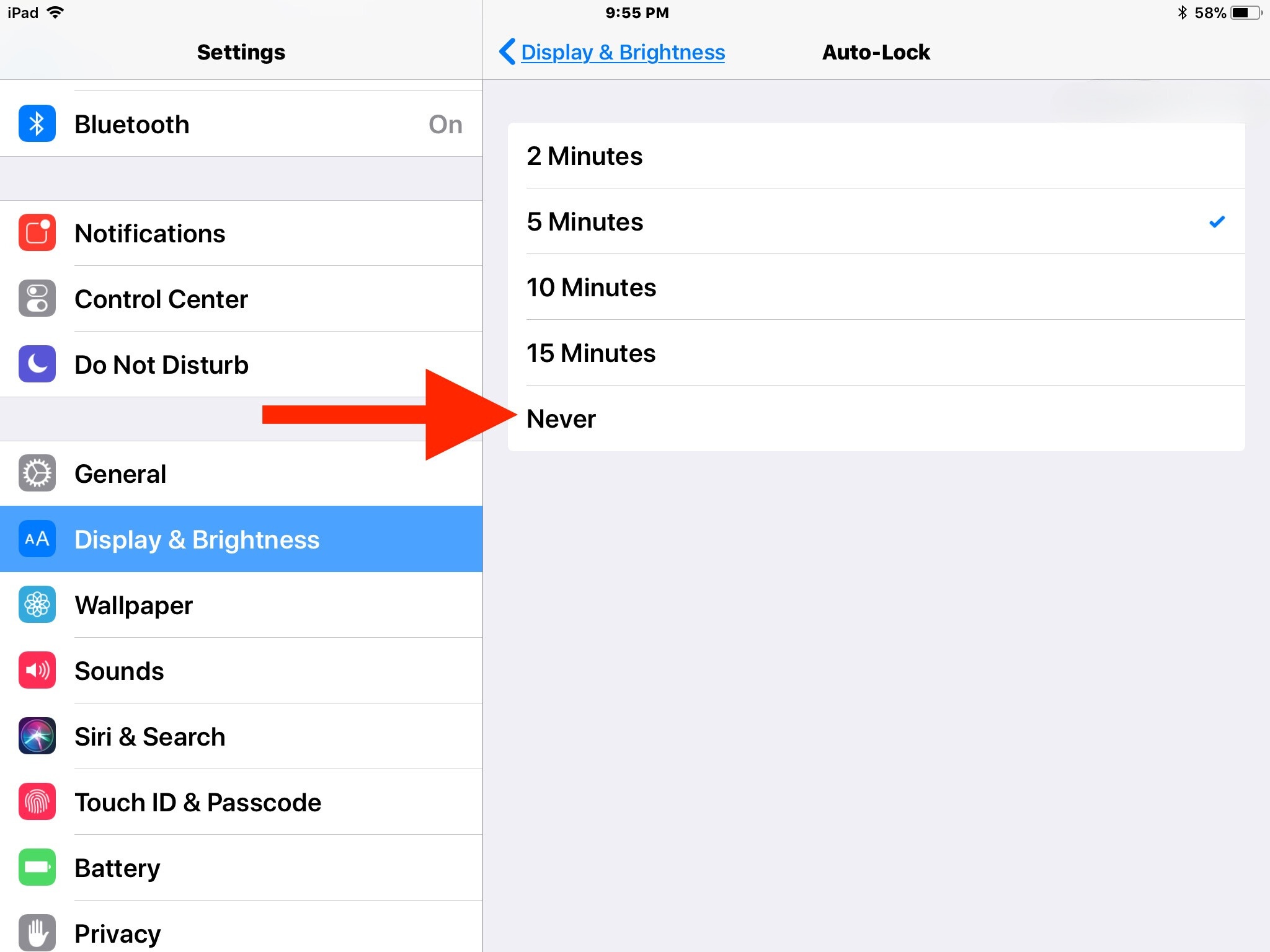
1. Set an Appropriate Idle Time: Determine the ideal idle time duration before your workstation locks automatically. It should strike a balance between security and user convenience. Too short of an idle time may be disruptive, while too long may increase the risk of unauthorized access.
2. Use Strong Passwords: Ensure that strong passwords are required on workstations to unlock them after they have been automatically locked. Encourage users to create unique passwords that are not easily guessable, and consider implementing multi-factor authentication for an added layer of security.
3. Educate Users: Awareness and education are key to the success of any security measure. Inform and train users about the importance of workstation locking, the risks of leaving workstations unattended, and the correct procedures to lock and unlock their workstations.
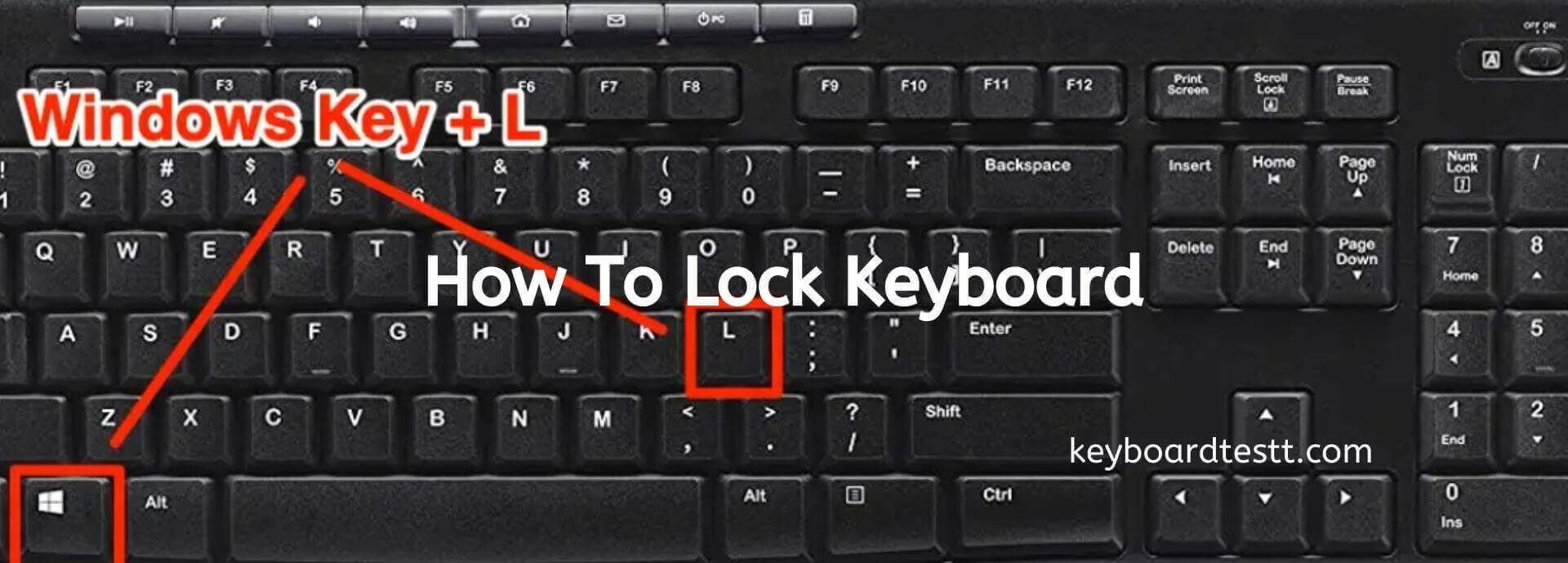
4. Lock Workstations Manually: Encourage users to manually lock their workstations whenever they step away, even if the automatic locking feature is enabled. This ensures that workstations remain locked, even if the idle time threshold has not been reached.
5. Secure Physical Access: Workstation locking is effective in preventing unauthorized digital access, but physical security is also crucial. Make sure workstations and equipment are in secure areas, and remind users to lock office doors or secure laptops when not in use.
6. Regularly Update Software: Keeping your operating system and security software up to date is essential for maintaining a secure computing environment. Install security patches and updates promptly to address any vulnerabilities that might lead to unauthorized access.
7. Implement Auditing and Monitoring: Regularly review logs and monitor workstation activity to detect any suspicious or unauthorized access attempts. Implement auditing tools to track login events, failed login attempts, and other security-related events.
8. Conduct Security Assessments: Periodically assess the effectiveness of your workstation locking measures through security audits and penetration tests. Identify any vulnerabilities or weaknesses in the system and take appropriate actions to mitigate risks.
9. Implement Security Policies: Develop and enforce comprehensive security policies that address workstation locking, data encryption, access controls, and other essential security measures. Regularly communicate these policies to employees and ensure compliance.
10. Regularly Train and Review: Provide ongoing security training to employees and conduct regular reviews of your workstation locking procedures. Stay up to date with new security trends and technologies, and adapt your strategies as needed.
By implementing these tips, you can enhance the effectiveness of workstation locking and strengthen the overall security posture of your organization. Remember that workstation locking is just one piece of the larger security puzzle, and a multi-layered approach is crucial for comprehensive security.
Conclusion
Workstation locking after inactivity is a critical security measure that helps protect sensitive data, prevent unauthorized access, and maintain privacy. By automatically locking workstations when they are left unattended, individuals and organizations can significantly reduce the risk of data breaches and security compromises.
In this guide, we explored various methods to achieve effective workstation locking. We discussed the use of built-in Windows settings, third-party software, scripts or batch files, and Group Policy settings. Each method offers its own advantages and can be tailored to meet specific needs and preferences.
Using built-in Windows settings provides a simple and convenient option for workstation locking, requiring no additional software. Third-party software offers advanced features and customization options, catering to specific security requirements. Scripts or batch files provide flexibility and customization for users with scripting knowledge. Group Policy settings, on the other hand, allow administrators to enforce consistent security policies across the network.
Regardless of the method chosen, it is important to adhere to security best practices and take additional measures to enhance overall security. Setting appropriate idle time durations, using strong passwords, educating users, securing physical access, regularly updating software, implementing auditing and monitoring, and enforcing security policies are all crucial to maintaining a secure computing environment.
By implementing effective workstation locking measures, individuals and organizations can safeguard sensitive data, mitigate security risks, maintain compliance with industry regulations, and promote a culture of security awareness.
Remember, security is a continuous effort, and it is imperative to stay proactive in adapting to emerging threats and implementing improved security measures. By prioritizing workstation locking and incorporating it as part of a comprehensive security strategy, individuals and organizations can better protect their systems, data, and privacy in today’s ever-evolving digital landscape.