Introduction
Have you ever wondered if your email has been compromised on the dark web? The dark web is a hidden part of the internet where illegal activities often take place, including the sale of personal information like email addresses. With cybercrime on the rise, it’s important to be proactive in protecting your personal data.
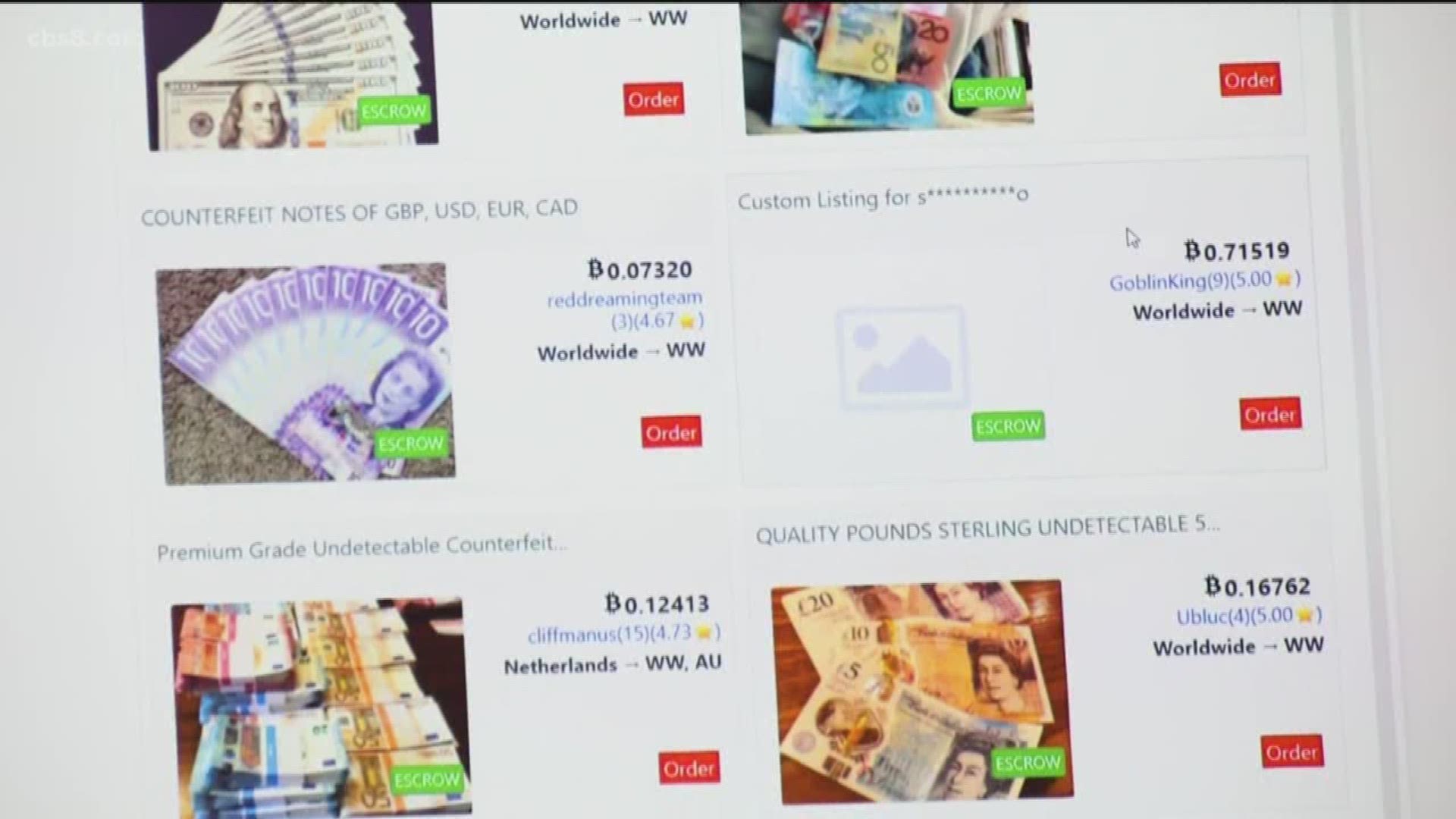
The dark web refers to websites and online platforms that are intentionally hidden and can only be accessed through specific software or authorization. Unlike the surface web that most of us are familiar with, the dark web is known for its anonymity and untraceability. This makes it an attractive hub for illegal activities such as drug trafficking, hacking, and the sale of stolen data.
So why should you be concerned about your email’s presence on the dark web? Your email address is a valuable piece of personal information. It can be used by cybercriminals for various malicious activities, including phishing scams, identity theft, and targeted attacks. If your email address is compromised and sold on the dark web, you may become a target for these cybercrimes, potentially leading to financial loss, reputational damage, or even legal issues.
Thankfully, there are methods available to help you check if your email is on the dark web. In this article, we will explore different approaches to determine if your email address has been compromised. By staying informed about your online presence, you can take necessary steps to protect yourself and safeguard your personal information.
What is the Dark Web?
The dark web is a part of the internet that is intentionally hidden and inaccessible through traditional search engines or web browsers. It is a network of encrypted websites that require specific software like Tor (The Onion Router) to access. This layer of anonymity allows users to browse and communicate with a higher level of privacy. Unlike the surface web, which is indexed by search engines and easily accessible, the dark web is intentionally hidden and primarily used for illegal activities.
One of the reasons the dark web is so attractive to criminals is its anonymity. Users can access websites on the dark web without revealing their true identities. This makes it difficult for law enforcement agencies to track down perpetrators involved in illegal activities such as drug trafficking, hacking, illegal trade, and cybercrime. The dark web provides a platform for these activities to take place without easy detection.
Another characteristic of the dark web is its structure of encrypted networks. Communication on the dark web is routed through multiple layers of encryption, making it difficult for anyone to trace the origin or destination of the communication. This encryption also ensures that data exchanged on the dark web remains secure and inaccessible to unauthorized parties.
It’s important to note that not everything on the dark web is illegal. While the dark web has gained a reputation for harboring illegal activities, it also provides a platform for individuals to exercise their freedom of speech and engage in activities that may be restricted or censored in their countries. Whistleblowers, journalists, and activists may utilize the dark web to share sensitive information or communicate without fear of surveillance or censorship.
However, the illegal activities on the dark web cannot be ignored. Criminals use the dark web to buy and sell stolen information, including personal data, credit card details, and login credentials. This makes it crucial for individuals to be aware of their online presence and take steps to protect their personal information from falling into the wrong hands.
Why Should You Be Concerned About Your Email’s Presence on the Dark Web?
Your email address is a gateway to your online presence, and it holds a significant amount of personal information. If your email address is compromised and ends up on the dark web, it can have serious repercussions. Here are a few reasons why you should be concerned about your email’s presence on the dark web:
1. Increased Risk of Cyberattacks: When your email is on the dark web, it becomes susceptible to various malicious activities. Cybercriminals can use your email address for phishing scams, where they send deceptive emails to trick you into disclosing sensitive information or installing malware. This can lead to financial loss, unauthorized access to your accounts, or identity theft.
2. Targeted Attacks: Once your email is compromised, cybercriminals may specifically target you for further attacks. They can use the stolen information to gather more details about you, your online presence, and your contacts. This information can be used to launch sophisticated attacks, such as spear-phishing, where hackers personalize their attacks to make them appear more legitimate and increase the chances of success.
3. Unauthorized Access to Accounts: If your email address and associated passwords are available on the dark web, hackers can attempt to access your accounts on various platforms, including social media, online banking, and e-commerce websites. With unauthorized access, they can steal sensitive information, make fraudulent transactions, or manipulate your online presence.
4. Reputation Damage: Your email may be linked to professional or business accounts, making it a valuable target for cybercriminals. If your email is compromised and used to send malicious or spam emails, it can damage your reputation and the trust of your contacts. This can have long-term consequences for your personal and professional relationships.
5. Legal Consequences: In some cases, having your email on the dark web can lead to legal problems. If your email is associated with illicit activities or is being used for illegal purposes, law enforcement agencies may investigate and hold you accountable for any unlawful actions. It is crucial to maintain control over your email and ensure it is not being misused on the dark web.
To mitigate these risks, it is vital to regularly check if your email is present on the dark web. By taking proactive measures to protect your email and personal information, you can reduce the chances of falling victim to cybercrime and safeguard your online identity.
Common Methods Used to Scan for Your Email on the Dark Web
As the dark web continues to pose a threat to online security, it’s important to understand the methods available to check if your email address has been compromised and is present on the dark web. Here are three common methods used to scan for your email on the dark web:
1. Using Online Tools to Check for Your Email on the Dark Web: There are several online tools available that allow you to check if your email address is present on the dark web. These tools work by searching through databases and websites known to deal in stolen data. You simply enter your email address, and the tool will scan the dark web to see if it appears in any compromised data sets. While these tools may not cover the entire dark web, they can provide a good starting point to assess the security of your email.
2. Utilizing Dark Web Monitoring Services: Dark web monitoring services are specialized services that continuously monitor the dark web for any mention of your email address or other personal information. These services use advanced algorithms and crawling techniques to search for stolen data that may include your email. If your email address is found, the service will notify you and provide recommendations on steps to take to mitigate the risk.
3. Employing Dark Web Intelligence Platforms: Dark web intelligence platforms are comprehensive solutions that offer advanced monitoring and analysis of the dark web. These platforms go beyond just scanning for individual email addresses and provide a broader perspective on cyber threats. They collect and analyze vast amounts of data from the dark web, including underground marketplaces, forums, and chat rooms. By utilizing these platforms, organizations can gain insights into emerging threats and proactively defend against potential attacks.
It’s important to note that while these methods can help identify if your email is present on the dark web, they cannot guarantee complete coverage. The dark web is vast and continuously evolving, making it challenging to track every instance of compromised data. Therefore, it’s essential to consider these methods as part of an overall cybersecurity strategy that includes strong passwords, regular monitoring of accounts, and staying informed about the latest threats.
By regularly monitoring for your email address on the dark web, you can take proactive measures to protect your personal information and reduce the risk of falling victim to cybercrime.
Method 1: Using Online Tools to Check for Your Email on the Dark Web
An effective approach to determine if your email address has been compromised and is present on the dark web is by utilizing online tools designed for this purpose. These tools offer a convenient and quick way to scan various databases and websites known to trade in stolen data. Here’s how you can use online tools to check for your email on the dark web:
1. Choose a Reliable Online Tool: Start by selecting a reputable online tool specifically designed to scan the dark web for compromised email addresses. There are several options available, each with their own features and efficiency. It’s important to choose a tool that is trustworthy and reliable, and that has positive reviews and a good track record of delivering accurate results.
2. Enter Your Email Address: Once you have selected a suitable online tool, enter your email address into the designated field or form provided. The tool will use this information to search through its database and the dark web for any instances in which your email address appears in compromised data sets.
3. Review the Results: After the scan is complete, the online tool will provide you with the results. These results may include information about whether your email address has been found on the dark web and where it was discovered. Some tools may also provide additional details, such as the type of compromise or the number of times your email address has appeared in compromised data. Take the time to carefully review the results and understand the severity of the situation, if applicable.
4. Take Necessary Actions: If your email address is found on the dark web, it is crucial to take immediate action to mitigate the risk. Change your passwords for all relevant accounts associated with the compromised email address. Monitor your accounts for any suspicious activity and enable additional security measures such as two-factor authentication. It may also be wise to inform your contacts about the situation so that they can be cautious of any suspicious emails originating from your compromised address.
5. Regularly Monitor for New Threats: Keep in mind that using online tools to check for your email on the dark web should be an ongoing practice. Cyber threats are constantly evolving, and new breaches occur regularly. Make it a habit to periodically scan for your email address using these tools to ensure that you are aware of any new compromises and can act promptly to protect your online security.
Using online tools to check for your email on the dark web is a proactive step in safeguarding your personal information. By staying informed about any compromises, you can take the necessary measures to protect yourself from potential cyber threats.
Method 2: Utilizing Dark Web Monitoring Services
To stay ahead of potential threats on the dark web, you can employ dark web monitoring services. These specialized services continuously scan the dark web for any mention of your email address or other personal information. By utilizing dark web monitoring services, you can receive timely alerts if your email address is identified on the dark web. Here’s how you can benefit from using dark web monitoring services:
1. Comprehensive Monitoring: Dark web monitoring services employ advanced algorithms and crawling techniques to scan the dark web for any mentions of your email address. They search through various forums, marketplaces, and chat rooms where stolen data is often traded. This comprehensive monitoring ensures that you are aware of any potential compromises before they can be used against you.
2. Real-Time Alerts: When a dark web monitoring service discovers your email address on the dark web, it sends you immediate alerts. These alerts can be in the form of emails, push notifications, or text messages, depending on your chosen notification preferences. Real-time alerts allow you to take prompt action to secure your compromised information and prevent further damage.
3. Enhanced Security Recommendations: Dark web monitoring services not only notify you of compromised data but also provide recommendations on the appropriate actions to take. They may suggest changing passwords, enabling two-factor authentication, or suggesting specific security measures based on the severity of the compromised information. These recommendations can help you strengthen your overall cybersecurity posture.
4. Continuous Monitoring: Dark web monitoring services offer continuous monitoring, ensuring that you are always informed about any new threats. As the dark web is constantly changing, new breaches and compromises occur regularly. By having ongoing monitoring in place, you can quickly respond to emerging threats and proactively protect your personal information.
5. Peace of Mind: Using dark web monitoring services provides peace of mind, knowing that your personal information is being actively monitored. It allows you to stay one step ahead of cybercriminals and take necessary actions to protect yourself. This proactive approach to security can help prevent potential financial loss, identity theft, or reputational damage.
It’s important to choose a reputable and reliable dark web monitoring service to ensure accurate and timely alerts. Additionally, in addition to relying solely on monitoring services, maintaining strong passwords, practicing good cybersecurity hygiene, and regularly updating your security measures are also essential for comprehensive protection.
By utilizing dark web monitoring services, you can stay informed about any compromises on the dark web and take immediate action to safeguard your personal information and online security.
Method 3: Employing Dark Web Intelligence Platforms
For a more comprehensive and advanced approach to monitoring the dark web, you can employ dark web intelligence platforms. These platforms provide in-depth monitoring and analysis of the dark web, allowing organizations to gain insights into emerging threats and proactively defend against potential attacks. Here’s how you can benefit from employing dark web intelligence platforms:
1. Extensive Dark Web Coverage: Dark web intelligence platforms have the capability to collect data from various sources on the dark web, such as underground marketplaces, forums, and chat rooms. This extensive coverage ensures that you have a broader perspective on cyber threats and can identify potential risks that are relevant to your organization.
2. Advanced Monitoring and Analysis: Dark web intelligence platforms use advanced algorithms and techniques to monitor and analyze the vast amount of data collected from the dark web. They can identify patterns, trends, and indicators of potential cyber threats. This proactive approach allows you to stay one step ahead of cybercriminals by detecting threats early and taking preventive measures.
3. Incident Response and Cyber Threat Intelligence: Dark web intelligence platforms provide incident response capabilities, enabling you to quickly respond to cyber threats. They offer real-time alerts, detailed reports, and actionable intelligence to guide your incident response efforts. This helps organizations mitigate risks, minimize the impact of data breaches, and protect sensitive information.
4. Deep Web Crawling: In addition to monitoring the dark web, dark web intelligence platforms also have the ability to crawl the deep web, which includes websites not indexed by traditional search engines. This allows for a more comprehensive understanding of potential threats that may not be readily visible on the surface web or be accessible through other monitoring methods.
5. Collaboration and Information Sharing: Dark web intelligence platforms often provide a platform for collaboration and information sharing within organizations. This enables security teams to work together, share insights, and exchange information about emerging threats. By leveraging collective knowledge and experiences, organizations can strengthen their defenses and respond effectively to cyber threats.
Employing dark web intelligence platforms should be seen as a strategic investment in your organization’s cybersecurity posture. It provides a proactive and holistic approach to monitoring the dark web, helping you identify and mitigate potential threats before they can impact your organization.
It’s important to choose a reputable and reliable dark web intelligence platform that aligns with your organization’s needs and security objectives. Regularly updating and fine-tuning the platform’s settings, as well as integrating the gathered intelligence into your overall security strategy, are also essential for maximizing the effectiveness of dark web intelligence platforms.
By employing dark web intelligence platforms, you can gain valuable insights, strengthen your cybersecurity defenses, and maintain a proactive stance against emerging cyber threats originating from the dark web.
Steps to Take If Your Email is Found on the Dark Web
Discovering that your email address has been found on the dark web can be concerning, but there are immediate actions you can take to mitigate the potential risks. Here are important steps to consider if your email is found on the dark web:
1. Change Your Passwords: Start by changing the password for the compromised email account. Ensure that the new password is strong, unique, and not used for any other accounts. Changing passwords regularly is a good practice to maintain strong security.
2. Enable Two-Factor Authentication (2FA): Enable two-factor authentication on your email account and any other online accounts associated with the compromised email address. 2FA adds an extra layer of security by requiring a verification code in addition to your password when logging in.
3. Monitor Account Activity: Be vigilant about monitoring your email account and other related accounts for any suspicious or unauthorized activities. Regularly check your inbox, sent folder, and trash folder for any unfamiliar or suspicious emails. Report and take action on any suspicious activity immediately.
4. Inform Your Contacts: Let your contacts know that your email address has been compromised. Inform them to be cautious about any emails they receive from your compromised address and advise them not to click on any suspicious links or download any attachments. Consider sending a warning email or message to prevent others from falling victim to potential phishing attempts.
5. Use Different Email Address for Sensitive Accounts: If possible, consider using a different email address for important and sensitive accounts, such as online banking or online shopping. This can help isolate the potential risks associated with the compromised email address.
6. Implement Additional Security Measures: Strengthen your overall security posture by implementing additional security measures. This may include using a reputable antivirus/antimalware software, keeping all your software and applications up to date, and regularly backing up your important data to minimize the impact of potential attacks.
7. Regularly Check for Updates: Regularly monitor for updates regarding the compromised email address. Repeat the process of scanning the dark web using online tools or employing dark web monitoring services to ensure that your email address has not appeared in any new compromised data sets.
8. Educate Yourself on Best Practices: Stay informed about cybersecurity best practices and educate yourself on how to protect your personal information online. Be cautious about clicking on suspicious links, be wary of phishing attempts, and practice good password hygiene to minimize the risk of future compromises.
Remember, prevention is key in maintaining your online security. By taking immediate action and implementing necessary security measures, you can minimize the potential risks associated with your compromised email address and protect yourself from further cyber threats.
Conclusion
Protecting your email address from being compromised on the dark web is crucial in today’s cyber landscape. The dark web poses significant risks, and your email address can be used for various malicious activities if it falls into the wrong hands. By being proactive and utilizing the methods discussed in this article, you can mitigate those risks and take control of your online security.
Checking for your email address on the dark web using online tools is a convenient and accessible option. These tools can provide you with immediate results and help you identify if your email address has been compromised. Additionally, utilizing dark web monitoring services offers continuous monitoring and real-time alerts, allowing you to quickly respond to any compromises and protect your personal information.
For a more comprehensive approach, employing dark web intelligence platforms allows for in-depth monitoring, analysis, and incident response capabilities. This can help organizations detect emerging threats and respond effectively to minimize potential damage.
If you discover that your email address is found on the dark web, taking immediate steps to change passwords, enable two-factor authentication, and inform your contacts is crucial. Regular monitoring, implementing additional security measures, and educating yourself on best practices can further strengthen your online security.
Remember, staying informed and proactive is key to safeguarding your personal information and protecting yourself from cyber threats. Regularly scanning for your email address on the dark web, implementing robust security measures, and keeping yourself educated on the latest cybersecurity trends are essential in this digital age.
By taking the necessary steps and being proactive in protecting your email address, you can significantly reduce the risk of falling victim to cybercrime and maintain control over your online security.