Introduction
When it comes to the internet, there is a mysterious side known as the Dark Web. This hidden part of the web is not indexed by search engines and offers a level of anonymity that attracts many curious individuals. However, it’s important to note that the Dark Web is not entirely legal or safe, as it harbors various illegal activities and potentially dangerous individuals.
Despite its less than savory reputation, there are legitimate reasons why someone may want to navigate the Dark Web. For journalists, researchers, or anyone seeking to understand the underbelly of the internet, accessing the Dark Web may be necessary. However, it is crucial to approach this exploration with caution and take steps to ensure your safety and privacy.
In this article, we will explore the Dark Web and discuss the importance of staying safe in this digital realm. We will delve into various steps you can take to navigate the Dark Web while protecting your identity, personal information, and financial security. By following these precautions, you can venture into the Dark Web with confidence and minimize the risks associated with it.
Before we dive into the safety measures, let’s first gain a better understanding of what the Dark Web actually is and why it requires extra caution.
Understanding the Dark Web
The Dark Web, also known as the Darknet, is a portion of the internet that is intentionally hidden and inaccessible through traditional search engines. While the surface web is easily accessible to anyone with an internet connection, the Dark Web requires specific software, configurations, and authorization to access.
One common misconception is that the Dark Web and the Deep Web are the same. The Deep Web refers to all the content on the internet that is not indexed by search engines, including private databases, emails, and other restricted areas. The Dark Web, on the other hand, specifically refers to the hidden websites that intentionally conceal their IP addresses and cannot be accessed through regular browsers.
The Dark Web operates on a network called Tor (The Onion Router), which anonymizes online activity by directing internet traffic through a volunteer network of servers. This ensures that users’ identities and locations remain hidden. Tor achieves this by encrypting and bouncing internet connections through multiple servers, making it difficult to trace the original source of a request or the location of a website.
While the Dark Web is often associated with illegal activities such as drug trafficking, weapons trade, and hacking services, it does also host legitimate and useful content. For example, whistleblowers and journalists use the Dark Web to communicate securely and anonymously, protecting themselves and their sources from surveillance and retaliation.
It’s important to note that accessing the Dark Web comes with significant risks. The anonymity it offers can attract cybercriminals, scammers, and other malicious individuals. Therefore, it is crucial to approach the Dark Web with caution and take necessary safety precautions to protect your identity and personal information.
Now that we have a better understanding of what the Dark Web is and the potential risks involved, let’s explore the importance of staying safe when venturing into this hidden digital landscape.
The Importance of Staying Safe on the Dark Web
When it comes to browsing the Dark Web, safety should be your top priority. The very nature of the Dark Web, with its hidden and anonymous nature, makes it a breeding ground for cybercrime, scams, and illicit activities. Therefore, taking precautions to protect your identity, personal information, and financial security is of utmost importance.
One key reason to prioritize safety on the Dark Web is to avoid legal repercussions. While not all activity on the Dark Web is illegal, there is a significant amount of illegal content, including drugs, weapons, stolen data, and more. Engaging in or even stumbling upon such content can lead to serious legal consequences. By staying safe and being diligent about the sites you visit and the activities you engage in, you can minimize the risk of falling into legal trouble.
Another important reason to prioritize safety is to protect your personal information. On the Dark Web, your identity and personal details can be at risk if you’re not careful. Cybercriminals may attempt to steal your information, such as your financial details or login credentials, to carry out identity theft or fraud. By implementing proper security measures and following safe browsing practices, you can greatly reduce the likelihood of becoming a victim of such attacks.
Additionally, staying safe on the Dark Web helps protect your financial security. Criminals often use the Dark Web to sell stolen payment information, credit card numbers, and other financial data. By ensuring that your transactions are secure and verifying the reputation and credibility of the websites you visit, you can minimize the risk of falling victim to financial scams or unauthorized transactions.
Lastly, prioritizing safety on the Dark Web is essential for maintaining your overall online well-being. The Dark Web is an intricate network filled with potential threats, ranging from malware-infected websites to phishing attempts. By staying vigilant, using secure communication channels, and avoiding suspicious downloads or files, you can safeguard your devices and data from harmful attacks.
Now that we understand the importance of staying safe on the Dark Web, let’s explore the practical steps you can take to browse this hidden realm while minimizing the associated risks.
Steps to Browse Dark Web Safely
Navigating the Dark Web can be a daunting task, but with the right precautions, you can browse safely and protect your personal information. By following these steps, you can minimize the risks associated with exploring the Dark Web:
- Install a Secure Operating System: Consider using a secure operating system like Tails or Whonix, which are designed specifically for privacy and security. These operating systems route your internet traffic through Tor automatically, enhancing your anonymity.
- Set up a Virtual Private Network (VPN): Use a reputable VPN service to encrypt your internet connection and hide your IP address. This adds an additional layer of security and ensures that your online activities are not easily traceable.
- Use Tor Browser for Anonymity: Download and use the Tor Browser to access the Dark Web. This browser is specifically designed to route your internet traffic through the Tor network, providing enhanced anonymity and privacy.
- Access Dark Web Marketplaces Safely: If you plan to explore Dark Web marketplaces, be cautious and research reputable and trusted sources before making any transactions. Verify the reputation of sellers and always rely on escrow services to protect your funds.
- Protect Your Identity and Personal Information: Avoid using your real name or providing personal details when creating accounts or engaging in any online activities on the Dark Web. Use pseudonyms, separate email accounts, and be mindful of the information you share.
- Ensure Safe Communication: When communicating on the Dark Web, use secure messaging tools with end-to-end encryption, such as Signal or Wickr. Avoid sharing sensitive information or engaging in suspicious conversations.
- Ensure Secure Payments: If making purchases or engaging in financial transactions on the Dark Web, use cryptocurrencies like Bitcoin. This provides an additional layer of privacy and minimizes the risk of exposing your financial information.
- Check Website Reputation and Credentials: Before accessing a Dark Web website, try to find reviews and recommendations from trusted sources. Look for forums or communities where users discuss the reputation and credibility of different websites.
- Avoid Scams and Fraudulent Activities: Be vigilant and skeptical of offers that seem too good to be true. Avoid engaging in illegal activities, falling for phishing attempts, or participating in schemes that promise unrealistic returns.
- Be Cautious with Downloads and Files: Download files with caution and always use reputable sources. Be wary of executable files, as they can contain malware or other malicious content that may compromise your security.
- Regularly Update Security Measures: It’s essential to keep your operating system, antivirus software, and other security tools up to date. Regular updates patch vulnerabilities and protect you against emerging threats.
By following these steps, you can navigate the Dark Web with greater confidence and reduce the risks associated with exploring this hidden part of the internet.
Installing a Secure Operating System
One of the key steps to browse the Dark Web safely is to install a secure operating system. By utilizing a dedicated operating system focused on privacy and security, you can enhance your anonymity and protect your online activities. Here are some essential considerations when installing a secure operating system:
1. Tails: Tails is a popular secure operating system that prioritizes privacy and anonymity. It is designed to run from a USB stick or DVD and routes all internet traffic through the Tor network. Tails includes built-in encryption and ensures that no trace of your activities is left behind.
2. Whonix: Whonix is another secure operating system that focuses on anonymity. It utilizes a combination of Tor and virtual machines to keep your identity hidden from the prying eyes. With Whonix, your internet traffic is isolated and encrypted, providing an extra layer of security.
3. Qubes OS: Qubes OS takes a different approach by integrating virtualization technology to isolate various tasks and applications. Each task runs in a separate virtual machine, enhancing security and protecting against potential threats. Qubes OS offers compartmentalization and is suitable for users who prioritize strong security measures.
4. Considerations: When installing a secure operating system, it’s essential to carefully follow the installation instructions provided by the respective operating system. Make sure to validate the authenticity of the operating system image you are downloading, as there are potential risks associated with tampered or compromised versions. Verify the checksums and signatures provided by the developers to ensure that the operating system is legitimate and hasn’t been tampered with.
5. Keep the Operating System Updated: Once you have installed a secure operating system, it’s crucial to keep it updated regularly. Updates often include security patches that address vulnerabilities and help protect your system from emerging threats. Enable automatic updates whenever possible to ensure you are running the latest version of the operating system.
By installing a secure operating system like Tails, Whonix, or Qubes OS, you can establish a solid foundation for browsing the Dark Web with enhanced privacy and security. These operating systems are specifically designed to prioritize anonymity, protecting your identity and online activities from potential risks.
Setting up a Virtual Private Network (VPN)
Using a Virtual Private Network (VPN) is an important step in ensuring your safety and privacy when browsing the Dark Web. A VPN encrypts your internet traffic and hides your IP address, making it difficult for anyone to trace your online activities. Here’s what you need to know about setting up a VPN for Dark Web browsing:
1. Choose a Reputable VPN Provider: Start by selecting a reputable VPN provider that prioritizes user privacy and security. Look for one that has a no-logs policy, which means they don’t store any information about your online activities. Take the time to research and read reviews to find a reliable VPN service.
2. Install the VPN Software: After selecting a VPN provider, download and install their VPN software on your device. Most VPN providers have dedicated software for various operating systems, including Windows, Mac, iOS, and Android. Install the software following the provider’s instructions.
3. Configure the VPN: Once the software is installed, open it and configure the settings to your preferences. You may have options to select a server location, enable additional security features, or customize your connection settings. It’s advisable to choose a server location that is in a different country to further increase your anonymity.
4. Connect to the VPN Server: With the software configured, you can now connect to the VPN server. Most VPN software provides a simple interface where you can choose a server and click on the “Connect” button to establish a secure connection. Once connected, all of your internet traffic will be encrypted and routed through the VPN server.
5. Test the VPN Connection: It’s important to test your VPN connection to ensure that it’s working as expected. Visit websites like whatismyipaddress.com or iplocation.net to verify that your IP address reflects the location of the VPN server you’re connected to. Additionally, make sure that your internet speed is still sufficient for browsing the Dark Web.
6. Use the VPN while Browsing the Dark Web: Once you have successfully connected to the VPN server, you can open your Tor Browser or any other Dark Web browsers, knowing that your connection is encrypted and your real IP address is hidden. This adds an extra layer of security and privacy to your Dark Web browsing activities.
7. Regularly Update the VPN Software: Like any other software, VPN applications release updates that include security enhancements and bug fixes. Make sure to update your VPN software regularly to ensure you have the latest security features and protection against emerging threats.
By setting up a VPN, you create a secure tunnel for your internet connection, protecting your identity and online activities while browsing the Dark Web. It adds an extra layer of privacy and helps ensure that your digital footprints remain hidden from prying eyes.
Using Tor Browser for Anonymity
When it comes to browsing the Dark Web, the Tor Browser is an essential tool for achieving anonymity and protecting your online privacy. The Tor network routes your internet traffic through a series of volunteer-operated servers, encrypting your data and making it difficult for anyone to trace your online activities. Here’s what you need to know about using Tor Browser for anonymity:
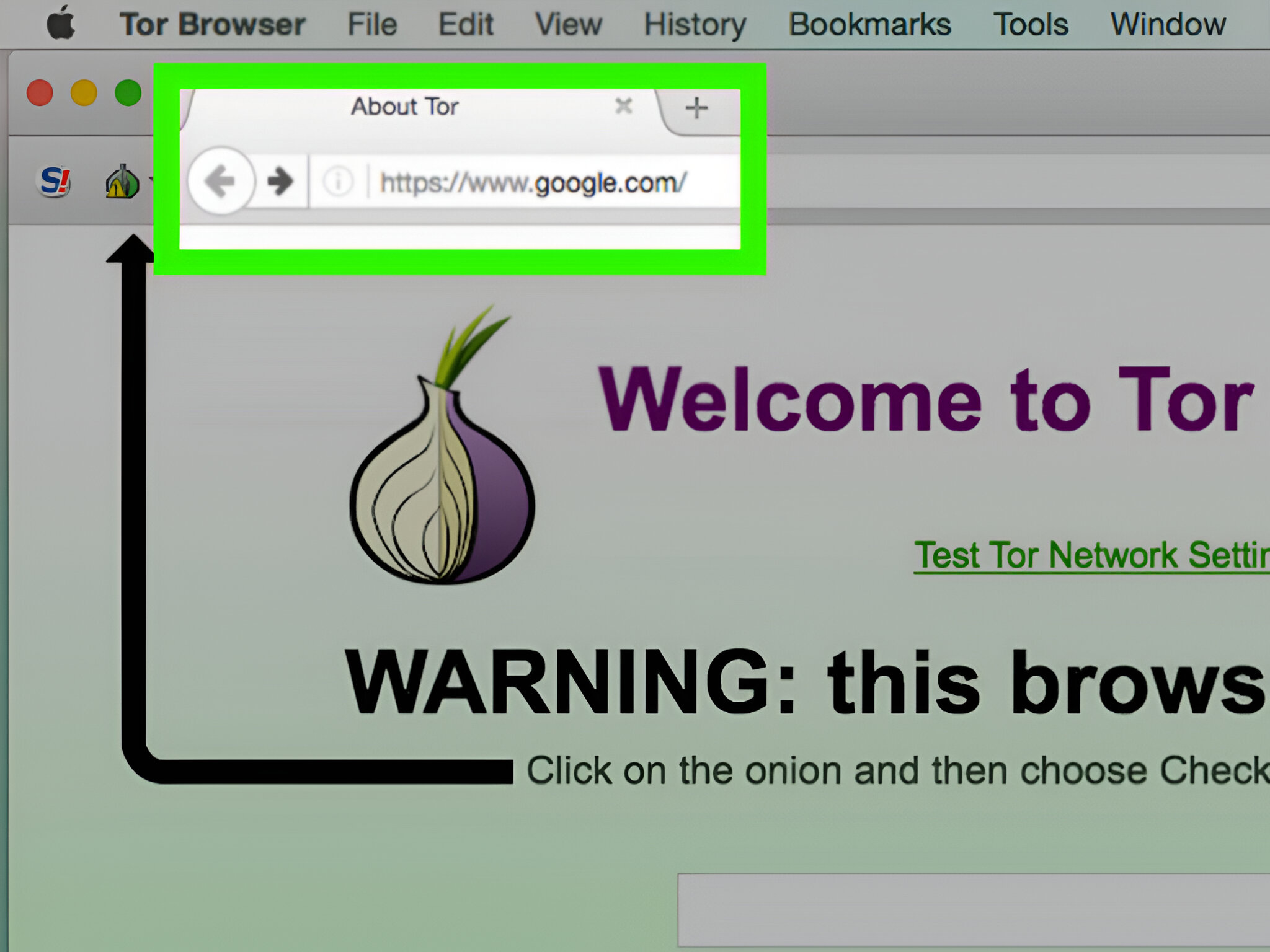
1. Download and Install Tor Browser: Start by downloading the Tor Browser from the official Tor Project website. The Tor Browser is available for Windows, Mac, Linux, and Android. After downloading, follow the installation instructions provided to set up the browser on your device.
2. Understand How Tor Works: Tor works by bouncing your internet traffic through a network of relays, which are volunteer-operated systems. Your connection is encrypted at each stage, making it difficult to track your activities. This anonymization process helps protect your identity and maintain your privacy while browsing the Dark Web.
3. Launch Tor Browser: Once installed, launch the Tor Browser. It might take a little longer to start compared to other browsers since it needs to establish a secure connection through the Tor network.
4. Adjust Tor Browser Settings: Tor Browser is designed to prioritize privacy and security. However, you can further enhance your anonymity by adjusting the browser’s settings. For example, you can disable certain scripts and plugins that may compromise your privacy. Carefully consider each setting and their potential impact on your browsing experience.
5. Understand the Limitations: While Tor Browser provides anonymity, it’s important to understand its limitations. It does not grant complete invincibility, and certain activities or vulnerabilities can still compromise your online privacy. Therefore, it’s crucial to exercise caution and follow safe browsing practices while using Tor.
6. Stick to Official Tor Hidden Services: When browsing the Dark Web with Tor Browser, it’s recommended to stick to official Tor Hidden Services. These are websites with the “.onion” domain that can only be accessed through the Tor network. This reduces the risk of encountering malicious websites or scams that may compromise your safety.
7. Avoid Using Personal Information: To maintain anonymity on the Dark Web, refrain from using your real name or providing personal information on any websites or platforms. Instead, opt for pseudonyms or aliases to protect your identity.
8. Regularly Update Tor Browser: Like any software, Tor Browser releases updates to address security vulnerabilities and provide enhanced privacy features. Make sure to keep your Tor Browser up to date by regularly checking for updates and installing them promptly.
By using Tor Browser, you can browse the Dark Web with a higher level of anonymity. Keep in mind that while Tor Browser enhances privacy, it’s crucial to combine it with other security measures, such as a VPN, to further protect your online activities.
Accessing Dark Web Marketplaces Safely
Accessing dark web marketplaces can be risky, as they often involve illegal activities and potential security threats. However, if you decide to explore these marketplaces, there are steps you can take to do so safely and minimize the associated risks. Here are some guidelines for accessing dark web marketplaces securely:
1. Research Reputable Sources: Before engaging with any dark web marketplace, conduct thorough research to identify trusted and reputable sources. Look for recommendations and reviews from reliable forums or communities that discuss the credibility and reputation of different marketplaces. This information can help you make informed choices and reduce the risk of falling victim to scams.
2. Verify Vendor Trustworthiness: Within dark web marketplaces, vendors offer various products and services. It’s important to verify the trustworthiness of vendors before making any purchases. Look for vendors with positive feedback, high ratings, and a history of successful transactions. This increases the likelihood of dealing with reliable sellers.
3. Use Escrow Services: Most reputable dark web marketplaces offer escrow services, where a third party temporarily holds the funds until both parties are satisfied with the transaction. This helps protect against fraud and ensures that your funds are not released until you receive the product or service as agreed upon.
4. Use Cryptocurrencies: Dark web marketplaces often rely on cryptocurrencies like Bitcoin for transactions. Consider using cryptocurrency to make purchases, as it provides an extra layer of security and privacy. Bitcoin transactions are difficult to trace back to individuals, reducing the risk of exposing your financial information.
5. Protect Your Personal Information: When interacting within dark web marketplaces, limit the amount of personal information you provide. Avoid giving out sensitive details that could be used to compromise your identity. Use pseudonyms or anonymous usernames, and be cautious about sharing any personally identifiable information.
6. Avoid Clicking Suspicious Links: Be wary of clicking on any suspicious links within dark web marketplaces. Cybercriminals may attempt to trick users into visiting malicious websites or phishing pages. Stick to reputable vendors and avoid any links that seem suspicious or lead to unfamiliar destinations.
7. Secure Communication: If you need to communicate with vendors or other users within dark web marketplaces, use secure communication channels. Encrypted messaging apps like Signal, Wickr, or PGP encryption methods can help ensure your messages remain private and protected from surveillance.
8. Stay Informed and Vigilant: The dark web landscape is constantly evolving, and new security threats emerge regularly. Stay informed about the latest security practices, trends, and potential risks associated with dark web marketplaces. Regularly update your knowledge and be vigilant while browsing and engaging in transactions.
By following these guidelines, you can access dark web marketplaces with greater caution and reduce the risk of encountering scams or compromising your security. Remember that engaging in illegal activities within these marketplaces is strongly discouraged and can lead to severe consequences.
Protecting Your Identity and Personal Information
When browsing and engaging on the Dark Web, protecting your identity and personal information is crucial to maintaining your privacy and security. With the right precautions, you can minimize the risk of your information falling into the wrong hands. Here are some essential steps to protect your identity and personal information:
1. Use Pseudonyms: Avoid using your real name or identifiable information when creating accounts or profiles on the Dark Web. Instead, use pseudonyms or alternate usernames to maintain anonymity and protect your identity.
2. Separate Email Accounts: Create separate email accounts to use exclusively for Dark Web activities. This helps prevent the potential linkage of your Dark Web activities to your personal or professional email accounts.
3. Employ Strong Passwords: Use strong, unique passwords for all your accounts on the Dark Web. A strong password should include a combination of upper and lowercase letters, numbers, and special characters. Avoid using easily guessable passwords or reusing them across multiple accounts.
4. Enable Two-Factor Authentication (2FA): Whenever possible, enable two-factor authentication for your Dark Web accounts. This adds an extra layer of security by requiring a second verification step, such as a unique code sent to your smartphone, in addition to your password.
5. Limit Personal Information Sharing: Be cautious about sharing personal information on the Dark Web. Avoid providing unnecessary details that could potentially compromise your identity or security. Never share your social security number, home address, or financial information unless absolutely necessary and only with trusted sources.
6. Encrypt Your Communications: Use encrypted communication channels and messaging apps when communicating on the Dark Web. End-to-end encryption tools like Signal, Wickr, or PGP encryption can help ensure that your messages remain private and protected from eavesdropping.
7. Regularly Clear Cookies and Cache: Clear your cookies, cache, and browsing history regularly. This helps minimize the footprint of your online activities and reduces the chance of tracking or linking your Dark Web browsing to other activities on the surface web.
8. Avoid Uploading Personal Photos or Documents: Steer clear of uploading personal photos, documents, or any other content that could potentially reveal your identity or location. Be mindful of the photos you share and make sure they do not contain any identifiable information.
9. Regularly Monitor Your Accounts: Regularly review your Dark Web accounts for any suspicious activity. Be on the lookout for unauthorized access or changes to your account details. If you suspect any compromise, take immediate action to secure your account and change your passwords.
10. Consider Using Anonymity Tools: In addition to following these steps, consider using anonymity tools like VPNs and the Tor network to further protect your identity and online activities on the Dark Web. These tools can add an extra layer of encryption and help mask your IP address.
By following these best practices, you can fortify your identity and personal information against potential threats on the Dark Web. Remember, being cautious and proactive is key to maintaining your privacy and staying secure in this hidden digital realm.
Safe Communication on the Dark Web
Safe and secure communication is crucial when navigating the Dark Web. As this hidden part of the internet can be rife with surveillance and potential risks, taking steps to protect your privacy and ensure secure communication is essential. Here are some guidelines to follow for safe communication on the Dark Web:
1. Use Encrypted Messaging Apps: Utilize encrypted messaging apps such as Signal, Wickr, or Telegram’s Secret Chat feature, which provide end-to-end encryption. These apps ensure that only you and the intended recipient can read the messages, protecting your conversations from eavesdropping.
2. Implement PGP Encryption: Consider using Pretty Good Privacy (PGP) encryption to secure your messages and emails on the Dark Web. PGP encryption provides an added layer of security by encrypting your messages using both a public key to encrypt and a private key to decrypt. This ensures that only the intended recipient can decipher the message.
3. Verify Encryption Keys: Before exchanging sensitive information or engaging in encrypted communication, thoroughly verify the encryption keys of the person or entity you are corresponding with. This ensures that you are communicating with the correct recipient and not an impersonator seeking to intercept your messages.
4. Minimize Personal Details: When communicating on the Dark Web, avoid providing unnecessary personal details. Keep your conversations focused and strictly related to the purpose at hand to minimize the risk of unintentionally revealing identifying information.
5. Use Different Usernames and Pseudonyms: It is best practice to use different usernames or pseudonyms on different platforms or accounts within the Dark Web. This further adds to your anonymity and makes it more difficult to link your activities across multiple platforms.
6. Practice OpSec: OpSec, short for Operational Security, involves taking steps to protect your identity and activities online. This includes making sure your online presence doesn’t leak information that can be used to identify you. Avoid sharing unnecessary personal information and be cautious about any digital footprints you create on the Dark Web.
7. Be Cautious of Metadata: While you may take precautions to secure your encrypted communications, be aware that metadata can reveal information about your activities. Metadata includes details such as the time and date of communication, the size of the message, and the sender and recipient. Mitigate this risk by being mindful of the amount of metadata you generate and take steps to anonymize or obfuscate it.
8. Avoid Sending Sensitive Files: In general, it is best to avoid sending sensitive files or documents through Dark Web communication channels unless absolutely necessary. File transfers can carry additional risks, including the potential for malware or compromised downloads. If required, use trusted file encryption tools and verify the integrity of files before sending them.
9. Regularly Update Security Tools: Keep your security tools, including your encrypted messaging apps and PGP encryption software, up to date. Regular updates ensure that you have the latest security patches and protection against emerging threats.
10. Trust Your Instincts: Trust your instincts and be wary of any communication that seems suspicious or too good to be true. If something feels off or raises red flags, it’s advisable to err on the side of caution and discontinue the conversation.
By following these guidelines, you can enhance your privacy and security while engaging in communication on the Dark Web. Remember that maintaining safe communication practices is crucial for protecting your identity and ensuring confidential conversations stay private.
Ensuring Secure Payments on the Dark Web
When engaging in transactions on the Dark Web, ensuring secure payments is paramount. The anonymous nature of the Dark Web can present risks, but by following proper protocols, you can minimize the chance of fraud and protect your financial security. Here are important steps to take for secure payments on the Dark Web:
1. Use Cryptocurrencies: Cryptocurrencies like Bitcoin (BTC), Monero (XMR), or Litecoin (LTC) are commonly used for transactions on the Dark Web due to their inherent privacy features. Consider using cryptocurrency for payments, as it adds an extra layer of anonymity and reduces the risk of exposing your financial information.
2. Understand the Seller’s Payment Policy: Before making a purchase, carefully review the seller’s payment policy. Understand their preferred payment methods and any specific instructions they provide. Following their guidelines ensures a smooth transaction and reduces the risk of misunderstandings or scams.
3. Use Escrow Services: Whenever possible, use escrow services offered by reputable dark web marketplaces. Escrow services act as intermediaries, temporarily holding the funds until both parties agree that the transaction has been completed satisfactorily. This helps protect against fraudulent sellers and ensures that you receive the products or services as expected before payment is released.
4. Verify Seller Reputation and Reviews: Before making a payment, research the reputation and reviews of the seller. Look for feedback from fellow buyers on dark web forums or marketplaces to gauge the seller’s reliability and trustworthiness. Be skeptical of sellers with limited or negative reviews, as they may be more likely to engage in fraudulent activities.
5. Use Secure Communication Channels: When discussing payment details, use encrypted communication channels to protect your sensitive information. Encrypted messaging apps like Signal or Wickr can safeguard your conversations from eavesdropping or interception.
6. Confirm Seller’s Identity: Take steps to confirm the seller’s identity before making a payment. Request additional verification or proof of ownership, such as photos or specific information related to the product or service. This helps ensure that you are dealing with the genuine seller and not an impersonator.
7. Avoid Sharing Unnecessary Information: During the payment process, provide only the necessary information to complete the transaction. Avoid sharing additional personal or financial information that could potentially be used for identity theft or fraud.
8. Keep Records and Documentation: Maintain records of all payment details, receipts, and communication related to the transaction. These records serve as evidence in case of any disputes or issues that may arise. Organizing and saving these documents can help protect your interests and assist in resolving potential conflicts.
9. Regularly Monitor Your Financial Accounts: Keep a close eye on your financial accounts after making a payment on the Dark Web. Regularly monitor your bank statements, credit card activity, or cryptocurrency wallets for any suspicious transactions. If you notice any unauthorized or suspicious activity, report it immediately to your financial institution.
10. Use Reputable Dark Web Marketplaces: It’s generally safer to make payments through reputable dark web marketplaces rather than directly with individual sellers. Established marketplaces often have systems in place to protect buyers and enforce certain security measures to minimize the risk of fraudulent transactions.
By following these steps, you can enhance the security of your payments on the Dark Web and reduce the risk of falling victim to scams or fraudulent activities. Remember to exercise caution and perform due diligence when engaging in transactions to protect your financial information and ensure a secure payment process.
Checking Website Reputation and Credentials
When exploring the Dark Web, it’s crucial to be diligent in checking the reputation and credentials of websites you visit. The hidden nature of the Dark Web means there’s a higher risk of encountering fraudulent or malicious websites that can compromise your safety and security. Here are some steps to follow when checking website reputation and credentials:
1. Research Trusted Sources: Seek out reliable forums or communities where users share experiences and discuss the reputation of Dark Web websites. These sources can provide valuable insights into the authenticity of websites and the credibility of their operators.
2. Look for Reviews and Recommendations: Search for reviews and recommendations from trustworthy sources that specialize in reviewing Dark Web websites. These platforms may assess parameters like usability, security of transactions, and user experiences, helping you make informed decisions about which websites to trust.
3. Verify Onion Links: Websites on the Dark Web use “.onion” domain addresses. To ensure the link you’re visiting is legitimate, use reputable onion link directories or search engines. Avoid clicking on links shared randomly or from untrusted sources, as they may lead to scams or phishing attempts.
4. Consider Website Trustworthiness Indicators: Look for trustworthiness indicators such as HTTPS encryption, security badges, or trust seals on Dark Web websites. While these indicators are not foolproof, they can give you some confidence in the website’s security measures.
5. Assess Website Content and Design: Examine the content and design of the website. Poor grammar, spelling errors, or unprofessional design may indicate that the website is not trustworthy. Legitimate websites typically invest time and effort into presenting themselves professionally.
6. Check for Established Reputation: Prefer websites with an established reputation in the Dark Web community. Websites that have been around for a longer time and have a history of positive user feedback are generally more reliable than newly established sites.
7. Verify Secure Payment Methods: Dark Web marketplaces typically offer secure payment methods such as encryption, escrow services, or cryptocurrency transactions. Ensure that the website you’re visiting supports secure payment options to protect your financial information.
8. Scrutinize Admin and User Activity: Assess the activity and engagement levels of the website’s administrators and users. Active participation and prompt responses to users’ queries or issues can indicate a more legitimate website, whereas low activity or delayed responses may raise concerns.
9. Use Online Reputation Tools: Utilize online reputation tools and services that provide insights into the reputation and credibility of websites. These tools may analyze factors such as domain age, website popularity, user reviews, and ratings to evaluate the trustworthiness of Dark Web sites.
10. Trust Your Intuition: Ultimately, trust your instincts when assessing website reputation and credentials. If something feels off or too good to be true, it’s better to err on the side of caution and avoid engaging with the website altogether.
By adopting these practices, you can minimize the chances of encountering fraudulent or malicious websites on the Dark Web. Remember that maintaining a cautious mindset and being proactive in researching and validating website reputations will help safeguard your online experience.
Avoiding Scams and Fraudulent Activities
When navigating the Dark Web, it is essential to be vigilant and cautious, as scams and fraudulent activities are prevalent. Criminals often use the anonymity and lack of regulation on the Dark Web to deceive and exploit unsuspecting individuals. Protect yourself from scams and fraudulent activities by following these guidelines:
1. Research and Verify: Before engaging in any transaction or activity on the Dark Web, thoroughly research and verify the legitimacy of the website, vendor, or service provider. Look for reviews, ratings, and feedback from trusted sources to ensure the credibility and trustworthiness of the entity.
2. Trust Reputable Platforms: Stick to reputable platforms and marketplaces with a proven track record of protecting their users. Established platforms often have robust security measures and mechanisms in place to minimize the risk of scams and fraudulent activities.
3. Be Wary of Unrealistic Offers: Exercise caution when encountering offers that seem too good to be true. Scammers may entice users with unbelievable discounts or promises of high returns. Remember that if something seems too good to be true, it probably is.
4. Avoid Providing Excessive Personal Information: Be cautious of websites or individuals that request unnecessary personal information beyond what is required for the transaction or desired service. Minimize the details you share to reduce the risk of identity theft or fraud.
5. Use Secure Payment Methods: Whenever possible, use secure payment methods such as escrow services or trusted cryptocurrencies. Escrow services provide a layer of protection by withholding funds until both parties are satisfied with the transaction. Cryptocurrency transactions add another level of privacy and reduce the risk of exposing your financial information.
6. Be Skeptical of Phishing Attempts: Be on the lookout for phishing attempts posing as legitimate websites or services. Scammers may send deceptive links or emails, attempting to trick users into revealing sensitive information. Verify the authenticity of links and avoid clicking on suspicious or unsolicited messages.
7. Beware of Social Engineering Tactics: Scammers may use social engineering techniques to manipulate and deceive individuals. Be cautious of unsolicited requests for personal information or attempts to build trust too quickly. Verify the identity and intentions of individuals or entities before providing any sensitive details.
8. Trust User Reviews and Feedback: User reviews and feedback can provide valuable insights into the reputation and trustworthiness of sellers, marketplaces, or websites. Consider the experiences and opinions of others when assessing the legitimacy of a dark web entity.
9. Regularly Update Security Measures: Keep your security measures, including antivirus software, VPNs, and operating systems, up to date. Regular updates provide the latest protection against emerging threats and vulnerabilities that scammers may exploit.
10. Trust Your Gut Feeling: Trust your instincts and rely on your intuition. If something feels off or raises suspicions, it’s best to refrain from proceeding with the transaction or interaction. Err on the side of caution to protect yourself from potential scams or fraudulent activities.
By following these practices and remaining vigilant, you can significantly lower the risk of falling victim to scams and fraudulent activities on the Dark Web. Staying informed, exercising caution, and thinking critically are essential for maintaining your safety and security in this digital realm.
Being Cautious with Downloads and Files
When navigating the Dark Web, one must exercise caution when it comes to downloading files. Malware, viruses, and malicious content are prevalent, posing significant risks to your device’s security and personal information. To protect yourself, follow these guidelines for being cautious with downloads and files:
1. Verify the Source: Only download files from trusted sources or reputable websites on the Dark Web. Stick to platforms or individuals with positive user reviews and established reputations. Avoid downloading files from random or unverified sources that could potentially contain malware or other security threats.
2. Scan Files with Antivirus Software: Before opening or executing downloaded files, scan them with reliable antivirus software. This helps detect and remove any potential malware or viruses that may be present in the file.
3. Be Wary of Executable Files: Exercise caution when downloading executable files (such as .exe or .bat) from the Dark Web. These types of files can carry malicious payloads and pose a significant risk to your device’s security. Consider avoiding executable files unless they are from a trusted source and necessary for your specific needs.
4. Use Sandboxing: Consider using a sandboxing tool or virtual machine to run downloaded files in an isolated environment. Sandboxing helps prevent potential malware or viruses from affecting your actual operating system by containing them within a separate virtual environment.
5. Avoid Suspicious File Types: Be cautious when downloading files with suspicious or uncommon file extensions. Files with extensions that are not commonly associated with the types of content you expect may indicate disguised malware or malicious content.
6. Evaluate File Size: Be wary of files with unusually small sizes that claim to deliver highly sought-after or large content. Such files may be fake or could lead to potentially harmful websites or downloads.
7. Use Encrypted or Password-Protected Archives: When downloading files stored in archives, prefer those that are encrypted or password-protected. This increases the security of the files and helps ensure that only authorized individuals can access their content.
8. Check File Reputation: Use online reputation tools or antivirus scanners specific to detecting malicious files to check the reputation of the downloaded file. These tools can flag files with potentially harmful content based on their known patterns or behaviors.
9. Regularly Update File Security Software: Keep your file security software, such as antivirus and anti-malware tools, up to date. Regular updates ensure that you have the latest protection against emerging threats and vulnerabilities.
10. Trust Your Instinct: When in doubt, trust your instinct. If a download or file seems suspicious, questionable, or too good to be true, it’s better to err on the side of caution and refrain from proceeding with the download.
By following these precautions and maintaining a cautious approach to downloads and files, you can minimize the risks associated with malware and other security threats on the Dark Web. Prioritizing the security of your device and personal information is crucial in maintaining a safe online experience.
Regularly Updating Security Measures
Regularly updating your security measures is essential for maintaining a secure and protected online experience, especially when navigating the Dark Web. New threats and vulnerabilities constantly emerge, and staying proactive with security updates ensures you are prepared. Here are key reasons why regular updates are crucial and how to implement them effectively:
1. Patching Security Vulnerabilities: Software updates often include security patches that address vulnerabilities or weaknesses discovered by developers or identified by the cybersecurity community. Applying these updates promptly helps keep your operating system and applications secure, reducing the risk of exploitation by hackers or malware.
2. Strengthening Protection Against Emerging Threats: Regular updates ensure you have the latest defense mechanisms against emerging threats. Cybercriminals are continuously evolving their tactics, so staying up to date with security updates allows you to benefit from the latest security enhancements and protection.
3. Enhancing Privacy Features: Updates to security software and applications often include improvements to privacy features. Privacy is especially important when navigating the Dark Web, where anonymity and confidentiality are paramount. Regularly updating security measures helps ensure your data and online activities remain private and protected.
4. Fixing Software Bugs and Stability Issues: Updates also address software bugs and stability issues that may compromise the performance or functionality of your system. Fixing these issues improves your overall online experience, ensuring smooth operation and minimizing the likelihood of crashes or other disruptions.
5. Utilizing the Latest Security Tools: Regular updates ensure that you have access to the latest security tools and features available. By taking advantage of these tools, such as antivirus software, firewalls, or virtual private networks (VPNs), you strengthen your defenses against various threats encountered on the Dark Web.
6. Keeping Protection Up to Date: As cyber threats evolve rapidly, relying on outdated security measures can leave you vulnerable to new attack methods. Regularly updating security measures allows you to adapt to the ever-changing threat landscape, keeping your protection up to date and effective.
7. Automating Updates: Enable automatic updates whenever possible to ensure that your operating system, applications, antivirus software, and other security tools receive the latest patches and upgrades promptly. Automating updates eliminates the risk of overlooking critical security updates and simplifies the update process.
8. Prioritizing Critical Updates: For systems or tools that do not support automatic updates, develop a habit of regularly checking for updates and prioritizing critical security patches. Pay close attention to vulnerabilities that have a higher risk of exploitation and update those systems promptly to mitigate potential threats.
9. Educating Yourself on Latest Security Practices: Stay informed about the latest security practices through reputable sources, such as cybersecurity blogs or news outlets. Educating yourself on emerging threats, best practices, and recommended security measures helps you make informed decisions and adjust your security measures accordingly.
10. Regularly Assessing and Adjusting Security Measures: Regularly assess your security measures and adjust them as needed. Conduct periodic reviews of your antivirus software, firewall settings, and other security tools to ensure they are operating optimally and providing the level of protection required.
By prioritizing regular security updates and staying proactive with security measures, you strengthen your defenses against evolving threats encountered while navigating the Dark Web. Keep your digital presence safe by adopting a proactive approach to maintain up-to-date security measures.
Conclusion
Exploring the Dark Web can be an intriguing and enlightening experience, but it is crucial to prioritize safety and security. By following the steps and guidelines outlined in this article, you can browse the Dark Web with confidence while minimizing the risks associated with this hidden part of the internet.
Understanding the Dark Web and its potential dangers is the first step in ensuring your safety. By recognizing the significance of staying safe on the Dark Web, you can make informed decisions about the risks you are willing to take and take necessary precautions to protect your identity, personal information, and financial security.
Installing a secure operating system, setting up a VPN, and using the Tor Browser are vital steps in maintaining anonymity and protecting your online activities. Accessing Dark Web marketplaces safely involves verifying reputations, using escrow services, and protecting your personal information during transactions.
Safe communication on the Dark Web requires encrypted messaging apps, verifying encryption keys, and minimizing personal details. Ensuring secure payments through cryptocurrencies, reputable platforms, and secure payment methods is crucial for protecting your financial security.
Checking website reputation and credentials, avoiding scams and fraudulent activities, being cautious with downloads and files, and regularly updating security measures are all essential practices to strengthen your safeguards on the Dark Web.
Overall, navigating the Dark Web without compromising your safety requires a combination of knowledge, caution, and proactive measures. Stay informed about emerging threats, keep your security measures up to date, and trust your instincts to navigate this hidden digital realm effectively.
Remember, the Dark Web poses inherent risks, and engaging in illegal activities or taking unnecessary risks is strongly discouraged. Prioritize your safety, remain vigilant, and use the tips shared in this article to minimize the potential risks associated with exploring the Dark Web.
Now that you are equipped with the knowledge and understanding of how to browse the Dark Web safely, you can venture into this mysterious realm with confidence while maintaining your privacy, security, and peace of mind.