An international operation led by law enforcement agencies from the United States, the European Union, and Japan has successfully seized the dark web portal used by the infamous RagnarLocker ransomware group. The coordinated action resulted in the closure of the group’s website and marks a significant blow to their operations.
Key Takeaway
An international law enforcement operation has successfully taken down the dark web portal used by the RagnarLocker ransomware group, dealing a significant blow to their operations. While the full extent of the operation remains unknown, the closure of the group’s website is a major milestone in the fight against ransomware.
International Collaboration
Law enforcement agencies from multiple countries collaborated in the operation, although the full details and scale remain undisclosed. It is still unknown whether the infrastructure of the gang was also seized, if any arrests were made, or if any funds were recovered. However, spokespersons from Europol and the Italian State Police have confirmed their involvement in the ongoing action against the RagnarLocker group. Europol plans to make an official announcement on Friday, once all the necessary actions have been finalized.
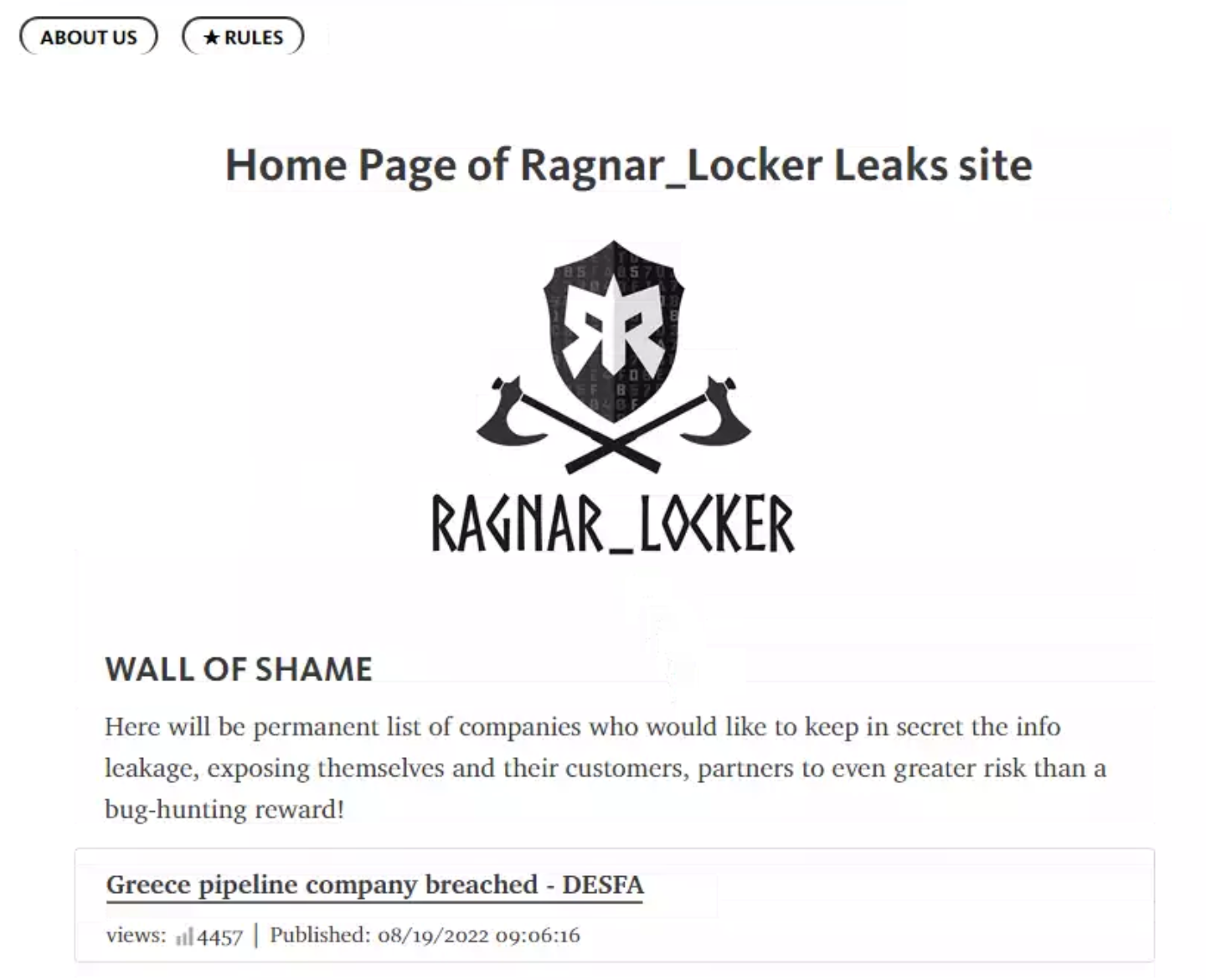
A Notorious Ransomware Group
The RagnarLocker gang is not only the name of a ransomware strain but also the criminal group responsible for developing and operating it. Although some security experts have linked the gang to Russia, their exact origins and affiliations have yet to be confirmed. Since 2020, the group has been observed targeting organizations, particularly in critical infrastructure sectors.
Past Attacks and FBI Warning
Last year, the FBI identified at least 52 U.S. entities across various critical infrastructure sectors that had fallen victim to the RagnarLocker ransomware. Sectors affected included manufacturing, energy, and government. The FBI issued an alert containing indicators of compromise associated with the gang, such as Bitcoin addresses used for ransom demands and email addresses used by the gang’s operators.
Ongoing Threat and Recent Attacks
Despite law enforcement efforts, the RagnarLocker gang has remained active, with documented attacks as recent as this month. The group claimed responsibility for an attack on Israel’s Mayanei Hayeshua hospital in September, where they threatened to leak over a terabyte of data allegedly stolen during the incident.