The increased reliance on cloud computing has created a greater need for cloud computing security. Do you remember the days of floppy disks? Technology has come a long way and cloud computing has revolutionized the way we work.
In addition, cloud computing has changed the way both businesses and users approach data storage and data transfer. However, improvements in technological development have increased the types of risks that come with innovation. Pesky viruses and malware are all too common to us everyday users and they have become more sophisticated over time. Sure, some of these threats have a low impact on our lives. But there are people with malicious intent that need to be safeguarded from.
Whether you are a user or a business, it is also prudent to have adequate cloud computing security in addition to practicing some of the best practices when it comes to cloud storage. In the event of a malicious attack or carelessness, cloud security can be the difference between damages or a close shave with danger. In this article, we will explore what is cloud computing as well as best practices for cloud computing security.
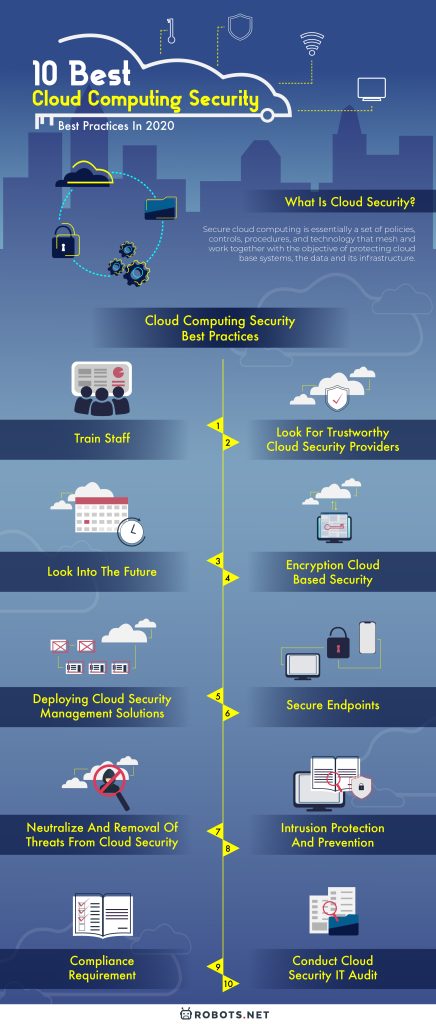
What Is Cloud Security?


To make things simple for the layman like us, secure cloud computing is essentially a set of policies, controls, procedures, and technology that mesh and work together with the objective of protecting cloud base systems, the data and its infrastructure.
Cloud-based security can be strategically centralized where the governing body protects both data and application. Moreover, could based security should have a recovery plan should anything go awry. Thus, when talking about cloud security or cloud network security, it is important to take note of what is written on the fine print of the cloud security provider.
Cloud Security For Business
Users of cloud base-computing such as individuals or businesses should make sure that the cloud computing process supports regulatory compliance and protects customer privacy. A breach in these two areas can have costly consequences for the parties involved. Cloud-based security might seem like a tedious task, but the benefits cloud computing can bring to the table have the potential to greatly improve productivity.
Besides the convenience of transferring and storing data and applications, cloud computing can set authentication rules for selected users and devices. With automated cloud computing and secure cloud computing, businesses can reduce their need for in-house IT support to configure security settings. These automation reduce micro-management and speed up the administrative process.
In this section, we will be delving into the top 10 best cloud computing best practices today. First, we will look at proactive things that we can do outside of technology. Secondly, IT solution best practices. Lastly, reactions to potential and active threats.
Top 10 Cloud Computing Security Best Practices
1. Train staff


The users are the front line against threats to secure cloud computing. These users are staff and stakeholders of the company that utilizes the cloud computing network to access different functions through different touchpoints. These users should be well trained in spotting dangerous elements such as malware masquerading as legitimate applications or files.
In addition, they should be made aware of the dangers of opening unsolicited emails and downloading their content. There are many ways hackers and malicious individuals can bypass cloud base security. Utilizing the users of the cloud network, they can sneak past safeguards. End-users should also be educated on the dangers of using unsecured dropboxes and uploading unauthorized files onto the cloud network.
2. Look for trustworthy cloud security providers
Unless you build your own cloud computing and cloud computing software, it is imperative to screen and select trustworthy providers of security cloud services. These providers of security cloud services should not only meet your needs but also the requirements of established standards.
In a digital age of transparency and lightning-fast connections, privacy has become a serious concern. A breach in data such as a leak of customer personal information to hackers can result in costly lawsuits and compensations. Therefore, it is paramount that cloud cybersecurity providers are up to the task and understand the regulations surrounding cloud network security. These providers of security cloud services should provide documentation and reports on the process and status of the cloud network’s security. In addition, they should have accountability and transparency in their security cloud services operations.
It would be best if these providers of security cloud services meet established industry standards. He should also hold certifications such as 7011 or ISO 27001. Thus, cloud security starts at the very bottom with the entities providing cloud-based security.
3. Look into the future
The internet is a rapidly growing place with new innovations being made. These innovations have led to the creation of more complicated and capable cloud cybersecurity threats. In response, security cloud computing evolved to ward off these potential threats.
This then becomes a revolving security arms race where stronger cybersecurity defenses force cybersecurity threats to evolve to meet the resistance. With the rapidly evolving risk, cloud computing security must look into the future and prepare for potential threats that the cloud network security might face. As such, cloud security should be regularly updated. This goes for both the software and the polices involved. The software needs to be able to fend off the threat while policy updates keep the process compliance with the latest industry standards.
As we have mentioned, cloud computing security is a set of policies, controls, procedures, and technology working together to safeguard the network. Therefore, an update on all aspects of cloud security is needed. In addition, the improvement should be accomplished with limited downtime to reduce inefficiencies and frustration for all parties involved.
4. Encryption cloud-based security


For cloud computing to be secure, the data should be encrypted as it enters the cloud storage device. Moreover, in creating a secure cloud computing system, users should be able to send encrypted data to and from the network. It protects the confidentiality of data being transmitted. Also, it limits the level of access each user has within the cloud computing network.
This security process requires both the sender and receiver to have a secret encryption key. As encryption can become a complicated process, it is advantageous to find a cloud computing security solution that makes it easy for end-users to both encrypt and decrypt data.
5. Deploying cloud security management solutions
A tactical cloud computing security best practice would be to implement identity and access management solutions to the cloud computing network. This process involves stopping threats from the user’s endpoint as its purpose is to screen the entities accessing the cloud computing network from a designated access point. There are two types of threats that this cloud computing security best practice targets.
Firstly, it seeks to mitigate the threat from unauthorized access. Secondly, it serves as a safeguard against the hijacking of accounts. An individual could accidentally or intentionally allow unauthorized individuals to access the data stored on the cloud network. Thus, identity management will help reduce the chance of a security leak through better user recognition. In addition, it is a secure cloud computing best practice to also include access management because each user’s access privilege should match their level of trust.
Incorporating Cloud Infrastructure Entitlement Management (CIEM) into your security strategy is a critical step in addressing and managing permissions and entitlements, ensuring robust cloud computing security practices. Furthermore, using CSPM (Cloud Security Posture Management) is essential for maintaining security and compliance in cloud environments, fitting seamlessly with the top cloud computing security practices mentioned.
6. Secure endpoints
Securing endpoints is a good practice for cloud computing security as it provides intrusion protection and access control. Endpoint security and cloud computing security used to be separated disciplines. However, changes in consumer behavior have led companies to adopt more open, affordable and accessible IT solutions for cloud computing. By integrating cloud computing security with the endpoints, companies are able to meet the round the clock demands of its customer base.
This endpoint access is a form of decentralized access to data and applications from any time in the world. Decentralized access has brought greater convenience to users and made companies more competitive. But this is a double-ended sword as decentralization can result in a loss of control. As such, cloud security around these endpoints must be ramped up to meet potential threats coming from endpoint devices. Besides the usual secure cloud computing protocols such as firewalls and anti-malware, cloud computing strategies should be revisited to ensure that cloud computing security protection is adequate.
7. Neutralize and removal of threats from cloud security


One of the best cloud computing best practices is improving the speed of neutralization and removal of cyber threats. Cloud cybersecurity threats have become increasingly advanced. They are able to disguise themselves as innocently appearing resumes, invoices, and other common documents.
These weaponized documents can wreak havoc on the cloud network. Therefore, it is a best practice to remove the threats associated with shared folders and auto sync-ing through screening files entering the network. As the best defense is to avoid being attacked in the first place, it is prudent to actively avoid malware, ransomware, and data theft attack.
Thus, it is in the company’s best interest to have an enhanced layer of cloud computing security that is able to inspect and sanitize the treat reactively.
8. Intrusion protection and prevention
An intrusion protection and prevention system examines the files moving through the network to identify and prevent vulnerabilities that can be exploited. An intruder usually finds a way into the cloud computing network through input from an endpoint. The aim of such an intrusion is to interrupt the network and gain control of applications.
The result of such threat can cause the disabling of applications or the theft of data and network permissions. Understandably, this situation will result in loses for the parties involved. With such a cloud computing security in place, a passive system scans traffic through the network and provides feedback on threats.
Thus, intrusion protection and prevention system is part of best practices. It can detect and respond to threats that happen in near real-time.
9. Compliance Requirement


It is essential to implement cloud cybersecurity that meets the regulations of both the industry and governments. As stakeholders are becoming increasingly connected in a rapidly globalized world. While compliance might seem intuitive, the process is made complex. This is because data and applications move from a controlled environment to endpoints in different countries, jurisdiction and regulations.
Therefore, choosing a security cloud services provider that proactively address cloud cybersecurity compliance issues. It can save a company a lot of time and trouble later on. Some of the best practices for cloud cybersecurity compliance are compliance assessments, security assessments, gap assessments, third party risk management, and cloud computing security consulting.
10. Conduct cloud security IT audits
The final best practice for cloud security on this list is cloud computing security IT audits. These cloud computing security audits are performed to determine if the network and its maintainers meet the legal expectations of customer data protection and the company’s standards for facing cloud cybersecurity threats. These audits should be transparent, cover the relevant scope and consider locational jurisdictions.