Introduction
In today's hyper-connected world, the ability to access the internet on the go has become a necessity for many. Mobile hotspots, also known as portable Wi-Fi routers, provide a convenient way to stay connected while traveling, working remotely, or simply seeking an alternative to public Wi-Fi networks. However, with this convenience comes the responsibility to ensure the security of your mobile hotspot.
As the reliance on mobile hotspots continues to grow, so does the importance of understanding the potential security risks and implementing best practices to safeguard sensitive information. Whether you're using a dedicated mobile hotspot device or leveraging your smartphone's tethering capabilities, it's crucial to be aware of the security implications and take proactive measures to mitigate potential threats.
In this article, we will delve into the realm of mobile hotspot security, offering valuable insights and practical tips to help you secure your connection and protect your data. By understanding the nuances of mobile hotspot security and adopting best practices, you can enjoy the benefits of wireless connectivity without compromising your privacy or falling victim to cyber threats.
Throughout the following sections, we will explore the fundamental aspects of mobile hotspot security, providing actionable guidance to fortify your connection and minimize the risk of unauthorized access or data breaches. From encryption and password management to network monitoring and software updates, we will equip you with the knowledge and tools necessary to enhance the security posture of your mobile hotspot.
As we navigate the intricacies of mobile hotspot security, it's essential to approach this topic with a proactive mindset, recognizing that safeguarding your digital footprint is an ongoing endeavor. By embracing a proactive approach to mobile hotspot security, you can harness the full potential of wireless connectivity while mitigating the inherent risks associated with transmitting data over public or shared networks.
Join us on this journey as we unravel the complexities of mobile hotspot security, empowering you to navigate the digital landscape with confidence and peace of mind. Let's embark on this exploration of best practices and actionable tips to elevate the security of your mobile hotspot and ensure a seamless and protected online experience.
Understanding Mobile Hotspot Security
Mobile hotspot security encompasses the measures and protocols designed to protect the integrity and privacy of data transmitted through a mobile hotspot connection. A mobile hotspot functions as a gateway, enabling devices to connect to the internet by leveraging a cellular network or other means of wireless connectivity. While providing the convenience of on-the-go internet access, mobile hotspots also introduce security considerations that necessitate careful attention and proactive management.
One of the primary aspects of mobile hotspot security revolves around encryption. Encryption plays a pivotal role in safeguarding data as it travels between connected devices and the hotspot itself. By encrypting the transmitted data, sensitive information such as login credentials, financial details, and personal communication is rendered indecipherable to unauthorized entities. This is achieved through the implementation of robust encryption protocols, such as WPA2 or WPA3, which serve as a barrier against eavesdropping and unauthorized access.
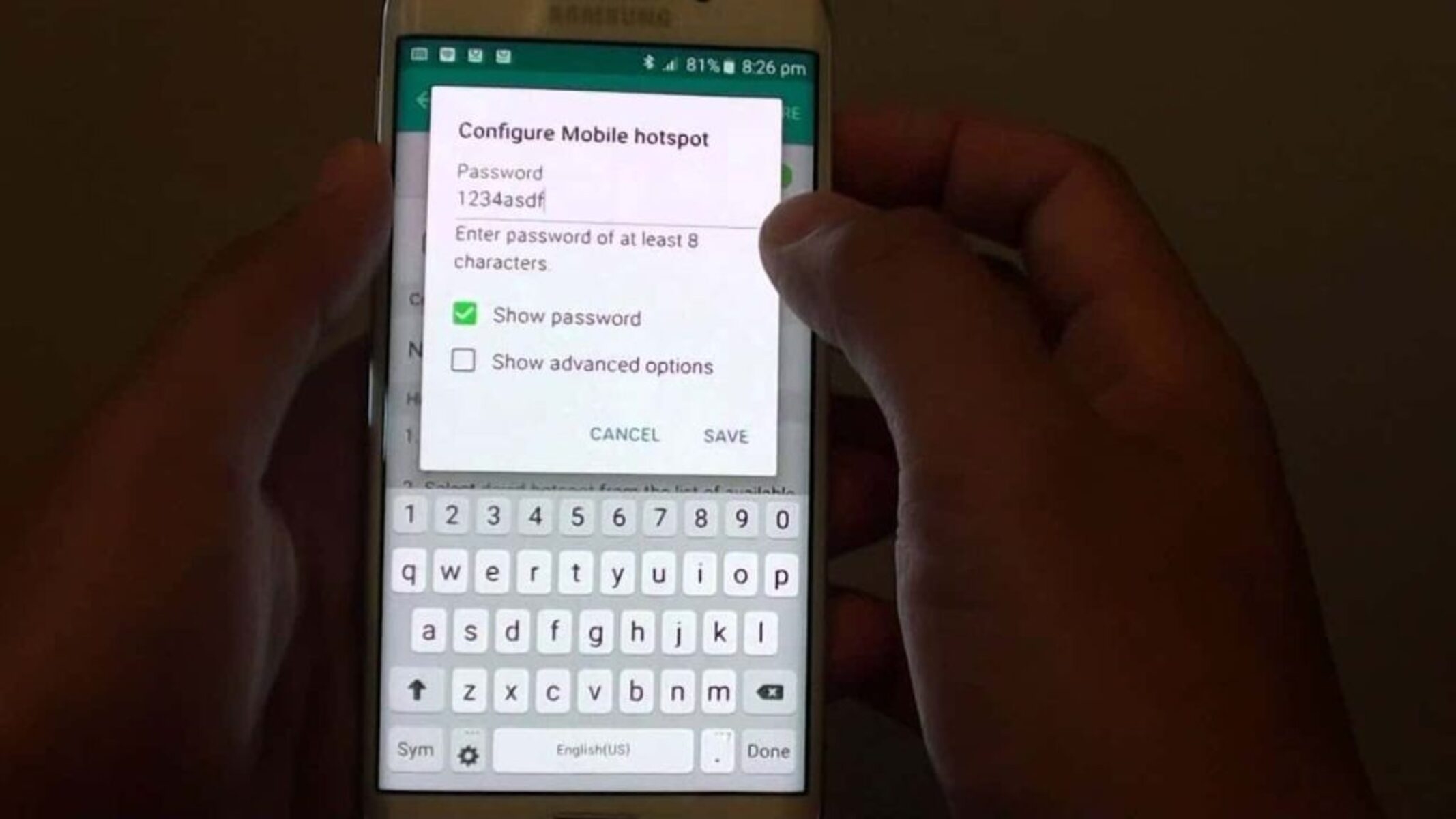
Another critical element in mobile hotspot security is the management of access credentials. The password used to access the mobile hotspot serves as a crucial line of defense against unauthorized intrusion. It is imperative to set a strong, unique password that combines alphanumeric characters and symbols to bolster its resilience against brute force attacks. Additionally, regularly updating the hotspot's password and avoiding the use of default or easily guessable passphrases are integral components of effective access credential management.
Furthermore, the inherent vulnerability of public Wi-Fi networks underscores the importance of understanding the distinction between secure and unsecured hotspots. When utilizing public Wi-Fi to create a mobile hotspot, it is essential to discern the potential risks associated with unsecured connections. Unsecured hotspots lack encryption and authentication mechanisms, making them susceptible to interception and unauthorized access. Conversely, secure mobile hotspots implement encryption and authentication protocols to fortify the confidentiality and integrity of transmitted data.
Moreover, the proactive monitoring of connected devices and network traffic is instrumental in identifying and mitigating potential security threats. By monitoring the devices connected to the hotspot and scrutinizing network activity, anomalous behavior indicative of unauthorized access or malicious activity can be promptly detected and addressed. Additionally, staying abreast of software updates for the mobile hotspot device or tethering-enabled smartphone is crucial for addressing security vulnerabilities and fortifying the overall security posture.
In essence, understanding mobile hotspot security entails a comprehensive grasp of encryption, access credential management, network security, and the nuances of secure and unsecured connections. By cultivating a deep understanding of these fundamental aspects, individuals can navigate the realm of mobile hotspot security with confidence, proactively mitigating potential threats and safeguarding their digital interactions. This foundational knowledge serves as a cornerstone for implementing robust security measures and fostering a secure and resilient mobile hotspot environment.
Tips for Securing Your Mobile Hotspot
Securing your mobile hotspot is paramount to safeguarding your sensitive data and maintaining a protected online experience. By implementing the following tips, you can fortify the security of your mobile hotspot and minimize the risk of unauthorized access and data breaches:
-
Enable Strong Encryption: Ensure that your mobile hotspot is configured to utilize robust encryption protocols, such as WPA2 or WPA3. Encryption serves as a critical defense mechanism, rendering transmitted data indecipherable to unauthorized entities and thwarting potential eavesdropping attempts.
-
Set a Strong Password: Establish a strong, unique password for your mobile hotspot to prevent unauthorized access. Combine alphanumeric characters, symbols, and a sufficient length to bolster the resilience of the password against brute force attacks. Regularly updating the password and refraining from using easily guessable phrases are essential practices for effective access credential management.
-
Disable SSID Broadcasting: Conceal the SSID (Service Set Identifier) of your mobile hotspot to enhance its security. By disabling SSID broadcasting, you can mitigate the visibility of your hotspot network, making it less susceptible to unauthorized detection and connection attempts.
-
Implement MAC Address Filtering: Utilize MAC (Media Access Control) address filtering to specify which devices are permitted to connect to your mobile hotspot. By configuring MAC address filtering, you can restrict network access to authorized devices, thereby mitigating the risk of unauthorized intrusion.
-
Regularly Update Firmware and Software: Stay vigilant about firmware and software updates for your mobile hotspot device or tethering-enabled smartphone. Keeping the device's software up to date is crucial for addressing security vulnerabilities and ensuring the implementation of the latest security enhancements.
-
Monitor Connected Devices: Proactively monitor the devices connected to your mobile hotspot to detect any unauthorized access or suspicious activity. Regularly review the list of connected devices and promptly investigate any unfamiliar or unauthorized entries to maintain the integrity of your network.
-
Exercise Caution on Public Networks: When creating a mobile hotspot using public Wi-Fi networks, exercise caution and prioritize the use of secure, encrypted connections. Avoid utilizing unsecured public Wi-Fi hotspots for creating a mobile hotspot, as they pose heightened security risks due to the absence of encryption and authentication measures.
By incorporating these tips into your mobile hotspot security practices, you can establish a resilient and secure environment for wireless connectivity. These proactive measures empower you to mitigate potential security threats, fortify your digital interactions, and uphold the confidentiality and integrity of your transmitted data.
Best Practices for Using a Mobile Hotspot
When leveraging a mobile hotspot for wireless connectivity, adopting best practices is essential to optimize security and ensure a seamless online experience. By adhering to the following best practices, individuals can maximize the utility of their mobile hotspot while fortifying the integrity and privacy of their data.
1. Select a Secure Location for the Hotspot Device
Position the mobile hotspot device in a secure and inconspicuous location to minimize the risk of physical tampering or unauthorized access. By safeguarding the physical integrity of the device, you can mitigate the potential for unauthorized manipulation or interference.
2. Establish Clear Usage Policies and Guidelines
Communicate clear usage policies and guidelines to individuals granted access to the mobile hotspot. Emphasize the importance of responsible and secure usage, outlining best practices for safeguarding sensitive data and adhering to security protocols.
3. Leverage VPN (Virtual Private Network) Technology
Utilize a reputable VPN service to establish a secure and encrypted connection when accessing the internet through the mobile hotspot. VPN technology enhances privacy and security by encrypting data traffic, thereby mitigating the risk of interception and unauthorized access.
4. Regularly Review Data Usage and Network Activity
Periodically review data usage and network activity associated with the mobile hotspot to identify any anomalies or irregularities. Monitoring data consumption and network traffic enables the detection of potential security breaches or unauthorized usage.
5. Educate Users on Cybersecurity Awareness
Educate users on cybersecurity awareness and best practices for identifying and mitigating potential threats. By fostering a culture of cybersecurity awareness, individuals can contribute to the collective effort of maintaining a secure and resilient mobile hotspot environment.
6. Implement Multi-Factor Authentication (MFA)
Where applicable, implement multi-factor authentication (MFA) for accessing the mobile hotspot or associated administrative interfaces. MFA adds an additional layer of security by requiring multiple forms of verification, such as a password and a one-time code sent to a registered device.
7. Securely Store and Transport the Hotspot Device
When transporting the mobile hotspot device, ensure it is securely stored to prevent physical damage or unauthorized access. Utilize protective cases or secure enclosures to safeguard the device during transit and minimize the risk of tampering.
8. Regularly Conduct Security Audits and Assessments
Periodically conduct security audits and assessments of the mobile hotspot environment to identify and address potential vulnerabilities. By proactively evaluating the security posture, individuals can fortify the resilience of the mobile hotspot and preemptively mitigate security risks.
By embracing these best practices, individuals can maximize the security and functionality of their mobile hotspot, fostering a protected and efficient wireless connectivity experience. These proactive measures empower users to navigate the digital landscape with confidence, safeguarding their data and interactions while leveraging the convenience of mobile hotspot technology.
Conclusion
In the realm of mobile hotspot security, vigilance and proactive measures are paramount to safeguarding sensitive data and maintaining a secure online environment. By understanding the fundamental principles of encryption, access credential management, and network security, individuals can fortify the integrity of their mobile hotspot connections and mitigate potential security risks. The adoption of best practices, such as enabling strong encryption, implementing access control measures, and staying abreast of software updates, serves as a cornerstone for enhancing the security posture of mobile hotspots.
As individuals navigate the digital landscape, the utilization of mobile hotspots for wireless connectivity underscores the necessity of prioritizing security and privacy. The convergence of encryption, secure password management, and network monitoring empowers users to fortify their mobile hotspot environments, minimizing the risk of unauthorized access and data breaches. By exercising caution on public networks and leveraging VPN technology, individuals can further bolster the confidentiality and integrity of their transmitted data, mitigating the inherent risks associated with unsecured connections.
Furthermore, the dissemination of cybersecurity awareness and the establishment of clear usage policies contribute to fostering a culture of responsible and secure usage of mobile hotspots. Educating users on best practices and the implications of mobile hotspot security cultivates a collective commitment to maintaining a resilient and protected wireless connectivity environment. Additionally, the implementation of multi-factor authentication, regular security audits, and the secure storage and transportation of mobile hotspot devices serve as proactive measures to fortify the overall security posture.
In conclusion, the proactive management of mobile hotspot security is indispensable in preserving the privacy and integrity of transmitted data. By embracing encryption, access control, and best practices, individuals can harness the full potential of mobile hotspots while mitigating potential security threats. The seamless integration of security measures and proactive vigilance empowers users to navigate the digital landscape with confidence, ensuring a secure and protected online experience while leveraging the convenience of wireless connectivity through mobile hotspots.
By adopting a proactive approach to mobile hotspot security, individuals can elevate the resilience of their digital interactions and uphold the confidentiality of their data, reinforcing the foundation of secure wireless connectivity in an increasingly interconnected world.