Introduction
With the rapid advancement of technology, the world is becoming increasingly interconnected. One such manifestation of this interconnectedness is the Internet of Things (IoT), a network of physical devices that are embedded with sensors, software, and connectivity to exchange data and interact with each other and their environment. From smart homes and wearable devices to industrial machinery and healthcare systems, IoT technology offers unprecedented convenience and efficiency in our daily lives.
However, as the number of IoT devices continues to escalate, so do the potential risks and vulnerabilities associated with them. IoT attacks have become a pressing concern in recent years, with cybercriminals targeting these devices for various malicious purposes. These attacks not only pose threats to individuals’ privacy and data security but can also have significant consequences on a larger scale, including disruptions to critical infrastructure and the economy.
In this article, we will explore what IoT attacks are, the types of attacks that can be carried out, the vulnerabilities commonly found in IoT devices, the consequences of IoT attacks, and how individuals and organizations can protect themselves against these threats.
What is IoT?
The Internet of Things (IoT) refers to the network of physical devices, vehicles, appliances, and other items that are embedded with sensors, software, and connectivity, allowing them to connect and exchange data with each other and with other systems over the internet. These devices are often equipped with unique identifiers that enable them to be recognized and controlled remotely.
The concept of IoT revolves around the idea of creating a digital ecosystem where devices can communicate, collaborate, and share information seamlessly. This interconnected network of devices has the potential to revolutionize various industries and improve the quality of life for individuals and communities.
IoT technology has found applications in diverse sectors, including smart homes, transportation systems, healthcare, agriculture, manufacturing, and more. Imagine being able to control your home’s thermostat, security cameras, and lights from your smartphone, or monitoring your heart rate and sleep patterns through a wearable device. These are just a few examples of the ways in which IoT is transforming daily life.
The foundational elements of IoT are the devices themselves, which range from simple sensors to complex machines. These devices collect and transmit data through various means such as Wi-Fi, Bluetooth, or cellular networks. The data generated by these devices can be analyzed to derive valuable insights and inform decision-making processes.
Furthermore, IoT systems often rely on cloud computing and large-scale data analytics to process and store the massive amount of data generated by the connected devices. This enables real-time monitoring, remote control, and advanced data analytics, making IoT solutions more powerful and efficient.
The potential benefits of IoT are vast. From improving operational efficiency and reducing costs in industries to enhancing healthcare outcomes and enabling sustainable living, the possibilities are endless. However, alongside these opportunities come significant challenges in terms of security, privacy, and interoperability, which must be adequately addressed to fully realize the potential of IoT.
What is an IoT Attack?
An IoT attack is a malicious attempt to compromise and exploit the vulnerabilities present in Internet of Things devices and networks. These attacks aim to gain unauthorized access, control, or disrupt the functionality of IoT devices for the attacker’s nefarious purposes.
Unlike traditional cyberattacks that target computers or servers, IoT attacks focus on exploiting the weaknesses of interconnected devices, which often have limited computing power, memory, and security measures. This makes them attractive targets for cybercriminals who can exploit these vulnerabilities to gain access to personal information, launch large-scale attacks, or even take control of critical systems and infrastructure.
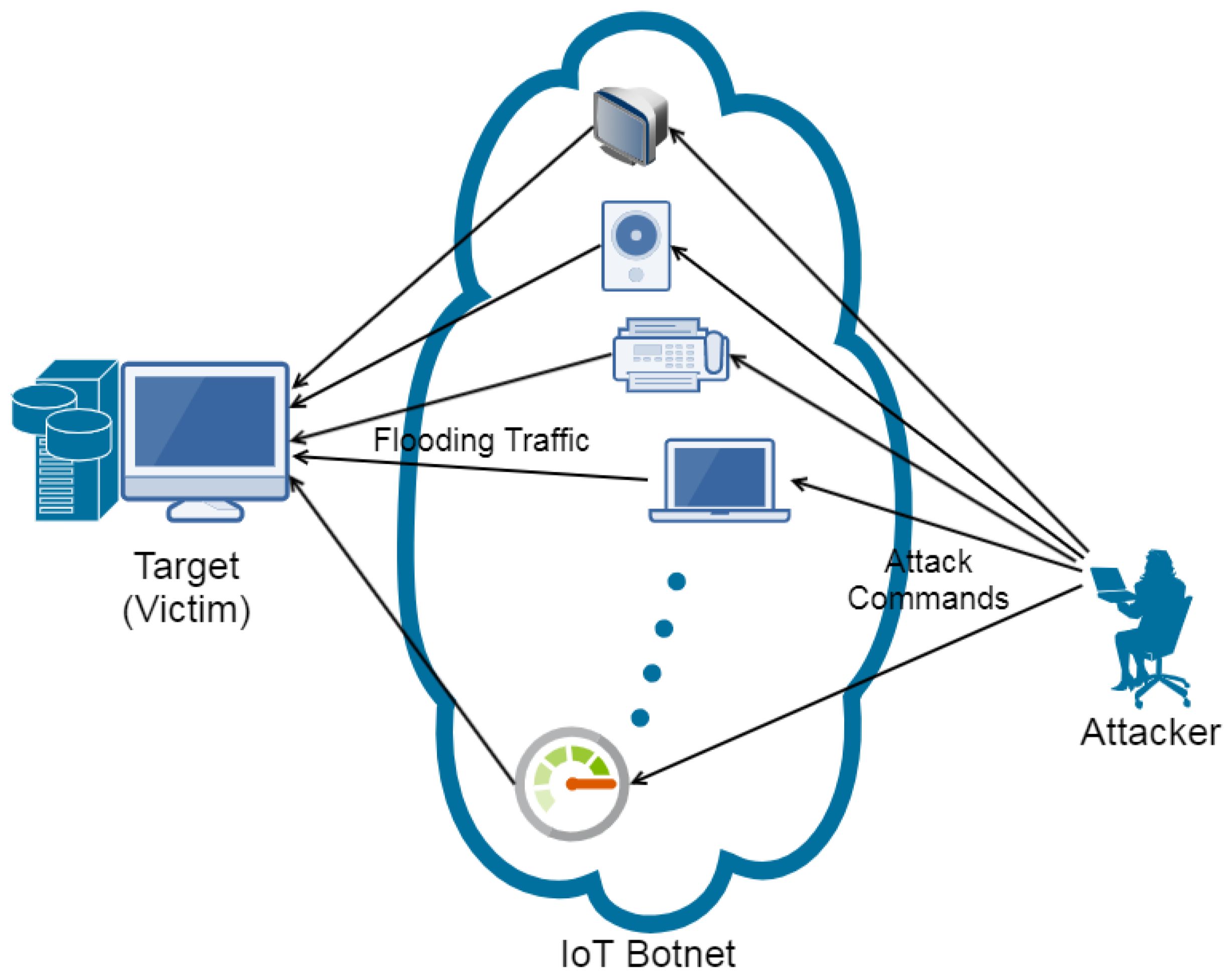
One common type of IoT attack is a botnet attack. In this scenario, the attacker compromises multiple IoT devices and forms a botnet, a network of infected devices controlled by a central command-and-control server. The attacker can then use this botnet to launch distributed denial-of-service (DDoS) attacks, overwhelming targeted services or networks with an overwhelming amount of traffic, effectively rendering them inaccessible.
Another form of IoT attack is device exploitation, where attackers exploit vulnerabilities within an individual IoT device to gain unauthorized access or control. This can include accessing sensitive user data, manipulating device functionality, or even remotely taking control of the device for malicious purposes.
IoT attacks can also involve intercepting and manipulating data traffic between IoT devices and their associated systems or services. By intercepting and altering data, attackers can sneak malicious commands or tamper with sensor readings, leading to potentially dangerous or disruptive outcomes.
It is important to note that IoT attacks can have serious consequences beyond the individual device or network being targeted. Compromised IoT devices can serve as gateways for attackers to infiltrate larger networks, including corporate systems or critical infrastructure, leading to widespread damage and disruption.
In summary, an IoT attack is a malicious act targeting the vulnerabilities of IoT devices and networks. These attacks exploit weaknesses in device security and can lead to unauthorized access, control, data manipulation, and disruptions with potentially severe consequences.
Types of IoT Attacks
The evolving landscape of IoT technology has given rise to various types of attacks, each with its own methods and objectives. Understanding these attack types is crucial for better protecting IoT devices and networks. Here are some common types of IoT attacks:
- Denial-of-Service (DoS) Attacks: These attacks aim to overload IoT devices or networks with a flood of traffic, making them unavailable to legitimate users. DoS attacks can be especially damaging in critical systems such as healthcare or industrial control systems.
- Distributed Denial-of-Service (DDoS) Attacks: In DDoS attacks, a network of compromised IoT devices, known as a botnet, is used to overwhelm targeted systems with a massive volume of traffic. This results in service disruptions and can have severe consequences for businesses or organizations.
- Eavesdropping: This attack involves intercepting and capturing data traffic between IoT devices or between devices and their associated systems. By eavesdropping, attackers can gain unauthorized access to sensitive information, compromising user privacy and security.
- Man-in-the-Middle (MitM) Attacks: In MitM attacks, attackers position themselves between IoT devices and the systems they communicate with, intercepting and manipulating data communication. This allows attackers to alter or inject malicious commands or steal sensitive information.
- Device Exploitation: This type of attack targets the vulnerabilities of individual IoT devices. Attackers exploit weaknesses in device security to gain unauthorized access or control. This can lead to data breaches, device malfunctions, or even physical harm in certain scenarios.
- Firmware Attacks: Firmware attacks involve tampering with the firmware of IoT devices. By compromising the firmware, attackers can install malicious code, manipulate device functionality, or gain persistent control over the device.
- Data Manipulation: Attackers may manipulate the data exchanged between IoT devices and their associated systems or services. By tampering with the data, attackers can deceive users or manipulate device behavior, leading to potentially dangerous or harmful outcomes.
- Physical Attacks: Physical attacks on IoT devices involve directly tampering with the hardware or physical components of the devices. This can include theft, destruction, or manipulation of IoT devices, compromising their functionality or rendering them useless.
These are just a few examples of the types of attacks that can be carried out against IoT devices and networks. It is crucial to have comprehensive security measures in place to mitigate the risks and protect against these various attack vectors.
Common Vulnerabilities in IoT Devices
While IoT devices offer numerous benefits and convenience, they also face a range of vulnerabilities that can be exploited by attackers. Understanding these vulnerabilities is essential for implementing effective security measures. Here are some common vulnerabilities found in IoT devices:
- Weak Authentication: Many IoT devices use default or weak passwords and lack proper authentication mechanisms. This makes it easier for attackers to gain unauthorized access to the devices or compromise their functionalities.
- Outdated Firmware: IoT devices may have outdated firmware that lacks necessary security patches and updates. This leaves them susceptible to known vulnerabilities and exploits that have been addressed in newer firmware versions.
- Lack of Encryption: Without proper encryption protocols, the data transmitted between IoT devices and their associated systems or services can be intercepted and exposed to potential attacks. Encryption is essential for protecting sensitive information from unauthorized access.
- Insecure Network Protocols: Some IoT devices rely on outdated or insecure network protocols, making them vulnerable to network-based attacks. It is crucial for devices to use secure communication protocols, such as Secure Shell (SSH) or Transport Layer Security (TLS), to protect against eavesdropping and data manipulation.
- Insufficient Secure Storage: Weak security measures in terms of storing data on IoT devices can expose sensitive information to unauthorized access or tampering. Proper encryption and secure storage practices must be implemented to protect data integrity.
- Lack of Regular Updates: IoT devices often lack automated update mechanisms, leaving them exposed to known vulnerabilities. Without regular firmware updates, devices remain at risk of exploitation by attackers who have knowledge of these vulnerabilities.
- Physical Security: Physical security of IoT devices is often neglected, making them susceptible to theft, tampering, or unauthorized physical access. Adequate physical security measures, such as tamper-proof enclosures or secure mounting, should be implemented.
- Third-Party Software: In many cases, IoT devices rely on third-party software components or libraries, which may have their own vulnerabilities. It is essential to assess the security of these components and ensure they are regularly updated and patched.
These vulnerabilities highlight the importance of implementing robust security measures at both the device and network levels. Regular updates, strong authentication, encryption, and secure storage practices are crucial to safeguarding IoT devices and protecting against potential attacks.
Consequences of IoT Attacks
IoT attacks can have severe consequences that extend beyond the individual device or network being targeted. Understanding the potential impact of these attacks underscores the importance of implementing strong security measures. Here are some consequences of IoT attacks:
- Privacy Breaches: IoT devices often collect and transmit sensitive personal data. A successful attack can compromise this data, leading to privacy breaches and exposing individuals to identity theft, financial fraud, or surveillance.
- Data Manipulation and Disruption: Attackers can manipulate the data transmitted by IoT devices, leading to misleading or false information. This can have significant consequences in critical systems such as healthcare, transportation, or industrial control, where decisions are made based on accurate data.
- Service Disruptions: IoT attacks, especially DDoS attacks, can overwhelm targeted systems or networks, causing significant disruptions. This can affect critical infrastructure, online services, or even public safety systems, leading to financial losses, service outages, or potentially endangering lives.
- Damage to Reputation: IoT attacks can harm the reputation of individuals, organizations, or manufacturers associated with compromised devices. The loss of trust from customers or stakeholders can have long-lasting consequences for businesses.
- Compromised Networks: IoT devices are often connected within larger networks, including corporate systems or critical infrastructure. If an IoT device is compromised, attackers can use it as a gateway to infiltrate and compromise the entire network, leading to further data breaches, service disruptions, or unauthorized access.
- Physical Harm or Safety Risks: In certain scenarios, IoT attacks can result in physical harm or safety risks. For example, compromising connected vehicles or medical devices can have life-threatening consequences for individuals relying on their proper functioning.
- Economic Impact: The financial impact of IoT attacks can be significant. This includes costs associated with remediation efforts, legal ramifications, loss of business, and potential fines or penalties for failing to protect customer data or critical systems.
- Cascading Effects: IoT attacks can have cascading effects and impact interconnected systems or services. For instance, an attack on a smart grid system can lead to power outages, affecting various sectors and services reliant on electricity.
These consequences highlight the multifaceted nature of IoT attacks and the importance of robust security measures to protect against them. By understanding the potential risks, individuals and organizations can take proactive steps to mitigate vulnerabilities and safeguard against the damaging effects of IoT attacks.
Examples of IoT Attacks
Over the years, there have been numerous notable examples of IoT attacks that have highlighted the potential risks and consequences associated with these interconnected devices. Here are a few prominent examples:
- Mirai Botnet: In 2016, the Mirai botnet attack compromised hundreds of thousands of IoT devices, including home routers, webcams, and digital video recorders (DVRs). The botnet was used to launch massive DDoS attacks, taking down major websites and services, including Twitter, Netflix, and Spotify.
- Stuxnet Worm: Although not exclusively an IoT attack, the Stuxnet worm serves as an important example of how IoT-like devices can be targeted. It targeted industrial control systems, specifically programmable logic controllers (PLCs) used in nuclear facilities in Iran in 2010. The worm caused physical damage to the centrifuges by manipulating their operational parameters, compromising the country’s nuclear program.
- Jeep Cherokee Hack: In 2015, researchers demonstrated how a vulnerability in a Jeep Cherokee’s infotainment system could be exploited remotely. The attackers were able to take control of critical vehicle functions, including the brakes and steering, making it a potential safety hazard for the driver and passengers.
- WannaCry Ransomware: Although not specific to IoT devices, the WannaCry ransomware attack in 2017 highlighted the potential risks faced by organizations with interconnected systems. It exploited vulnerabilities in Windows operating systems, infecting hundreds of thousands of computers worldwide, including those used in healthcare facilities. The attack disrupted critical services and demanded ransom payments in exchange for access to encrypted data.
- Baby Monitor Hacks: Several instances have been reported where baby monitors equipped with IoT capabilities were compromised. Attackers gained unauthorized access to the devices, allowing them to spy on and communicate with unsuspecting parents and their children, breaching their privacy and security.
- Smart Home Device Exploitation: As smart home devices gain popularity, vulnerabilities in these devices have been exploited. Attackers have manipulated smart thermostats, security cameras, and voice assistants to gain unauthorized access to personal information, spy on individuals, or even unlock doors remotely.
These examples demonstrate the diverse range of IoT attacks and their potential implications. They highlight the importance of proactive security measures, regular updates, and robust authentication mechanisms to mitigate the risks posed by IoT vulnerabilities.
How to Protect Against IoT Attacks
As the popularity and adoption of IoT devices continue to grow, it is crucial to take proactive steps to protect against potential IoT attacks. Here are some essential measures that can help enhance the security of IoT devices and networks:
- Change Default Passwords: Always change default passwords on IoT devices with strong, unique passwords. Avoid using common or easily guessable passwords to prevent unauthorized access.
- Regularly Update Firmware: Keep IoT devices up to date with the latest firmware and security patches. Regularly check for updates from device manufacturers to address known vulnerabilities.
- Enable Two-Factor Authentication (2FA): Enable 2FA whenever possible to add an extra layer of security. This requires an additional verification step, such as a one-time password (OTP), for accessing IoT devices.
- Secure Your Network: Segment your network to isolate IoT devices from critical systems. Use firewalls and network access controls to monitor and restrict incoming and outgoing traffic to IoT devices.
- Implement Encryption: Use encryption protocols, such as Transport Layer Security (TLS), for securing communication between IoT devices and their associated systems or services. This helps protect data from eavesdropping and tampering.
- Beware of Third-Party Software: Be cautious when using third-party software components or libraries. Ensure they are from reputable sources and regularly update them to address any known vulnerabilities.
- Monitor Device Behavior: Implement network monitoring and intrusion detection systems to detect any suspicious or anomalous activity. Regularly review device logs and monitor for unauthorized access attempts.
- Disable Unnecessary Features: Disable any unnecessary features or services on IoT devices that are not required. This reduces the attack surface and minimizes potential vulnerabilities.
- Implement Physical Security: Physically secure IoT devices to prevent unauthorized access or tampering. This includes properly installing and securing devices in tamper-proof enclosures and using unique device identifiers.
- Educate Users: Provide education and training to users on IoT security best practices. Encourage them to be vigilant, avoid clicking on suspicious links, and report any suspicious activity related to IoT devices.
By implementing these security measures, individuals and organizations can significantly reduce the risk of IoT attacks and better protect their devices, data, and networks. It is important to stay proactive, stay informed about emerging threats, and regularly reassess and update security measures in response to evolving IoT attack techniques.
Conclusion
The Internet of Things (IoT) has brought about a new era of connectivity and convenience, but it also introduces unique challenges and risks. IoT attacks pose significant threats to individuals, organizations, and even critical infrastructure. Understanding the nature of these attacks, the vulnerabilities in IoT devices, and their potential consequences is crucial for implementing effective security measures.
Throughout this article, we have explored the definition of IoT, the various types of IoT attacks, common vulnerabilities in IoT devices, the consequences of IoT attacks, and ways to protect against them. From denial-of-service attacks to data manipulation and physical harm risks, IoT attacks can have far-reaching implications. However, by following best practices such as changing default passwords, regularly updating firmware, enabling strong authentication, securing networks, and implementing encryption, we can mitigate the risks and enhance the security of our IoT devices and networks.
It is also important to stay informed about emerging threats and to continuously reassess and update security measures as new vulnerabilities and attack techniques emerge. Collaboration between device manufacturers, service providers, and users is key in addressing the evolving landscape of IoT security.
As the IoT ecosystem continues to expand and evolve, ensuring the security and privacy of connected devices will remain a critical challenge. By staying proactive, vigilant, and informed about the latest security practices, we can harness the power of IoT technology while keeping our data and networks protected from potential attacks.