Introduction
With the advancement of technology, the threat of computer viruses has become a constant concern for individuals and organizations alike. One type of virus that has gained prominence in recent years is the PHP file virus. These viruses target websites and web servers that rely on PHP (Hypertext Preprocessor) scripting language, which is widely used for web development.
A PHP file virus is a malicious program that infects PHP files, which are responsible for powering dynamic web pages. Once infected, these files can cause various types of damage, including data theft, website defacement, and even the spread of additional malware.
The primary objective of PHP file viruses is to exploit vulnerabilities in PHP files or the web server environment to gain unauthorized access, compromise sensitive data, or carry out other malicious activities. Due to the popularity and versatility of PHP, cybercriminals have found ways to take advantage of this scripting language to further their nefarious intentions.
In this article, we will explore the nature of PHP file viruses, how they spread, the common types of PHP file viruses, the signs of infection, the potential damage they can cause, and most importantly, how you can protect against them.
It is important to note that PHP file viruses can have severe implications for both individuals and businesses. Ignoring the threat or failing to take necessary precautions can lead to devastating consequences, including financial loss, reputation damage, and legal implications.
By understanding the inner workings of PHP file viruses and implementing appropriate security measures, you can safeguard your website and ensure its smooth operation.
What Is a PHP File Virus?
A PHP file virus is a type of malicious software that specifically targets PHP (Hypertext Preprocessor) files, which are commonly used in web development. These viruses are designed to infect PHP files and exploit vulnerabilities within the scripts or the web server environment. Once infected, the PHP files can execute harmful code, compromise data, and even spread the virus to other files or systems.
PHP file viruses are typically created by cybercriminals with the intention of gaining unauthorized access to websites, stealing sensitive information, or causing disruption. These viruses can be introduced to PHP files through various means, such as malicious downloads, compromised websites, or vulnerabilities in the web server software.
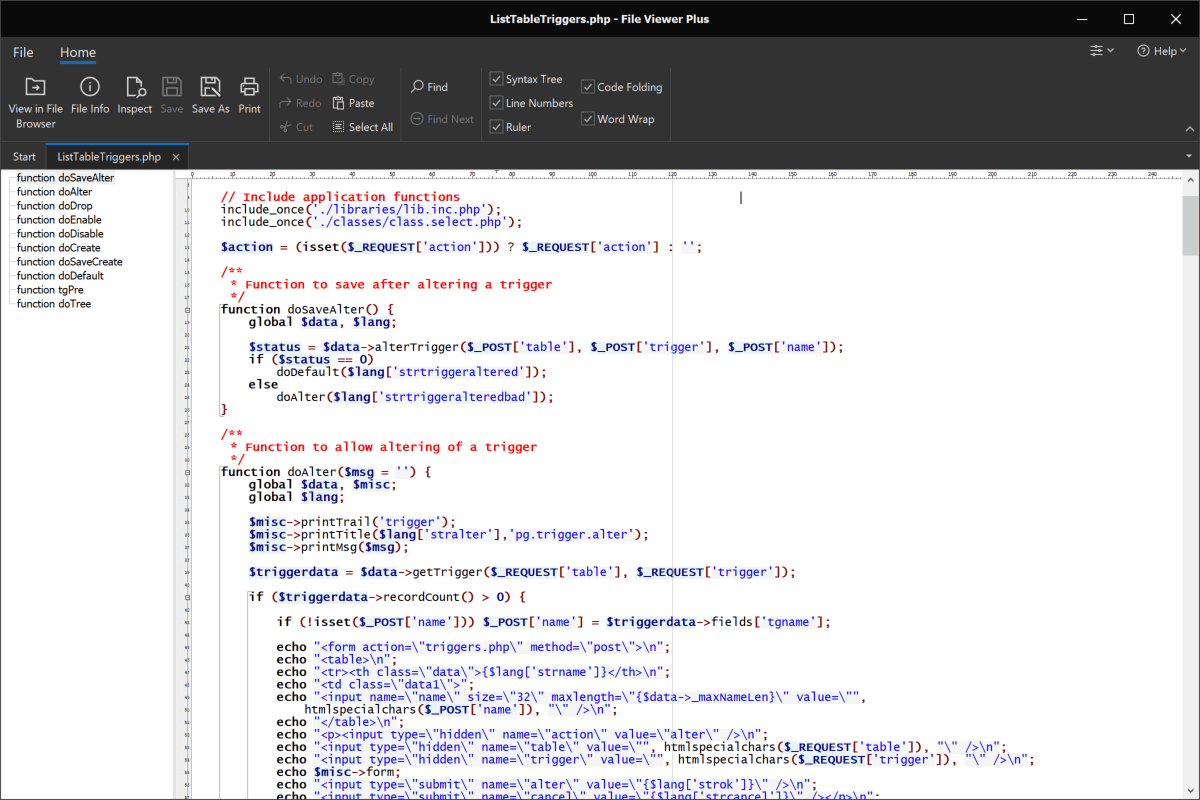
When a PHP file virus infects a PHP file, it can carry out a wide range of malicious activities. For example, it may modify the file’s code to redirect visitors to malicious websites, inject malicious scripts into web pages, or steal login credentials and other sensitive data. In some cases, PHP file viruses may also spread to other files and directories on the same server, further expanding their reach and impact.
It is worth noting that PHP file viruses are not limited to a single type or variant. Cybercriminals continuously develop new techniques and methods to create and distribute these viruses, making them a persistent threat to websites and web servers.
PHP file viruses can have devastating consequences for individuals and businesses. They can lead to website defacement, loss of customer trust, financial loss, and even legal ramifications. It is therefore crucial for website owners and administrators to understand the nature of PHP file viruses and implement proactive security measures to protect their valuable data and ensure the integrity of their websites.
In the following sections, we will delve deeper into how PHP file viruses spread, the common types of PHP file viruses, the signs of infection, the potential damage they can cause, and, most importantly, how you can protect against them.
How PHP File Viruses Spread
PHP file viruses can spread through various methods, taking advantage of vulnerabilities in websites, web servers, or the PHP scripting language itself. Understanding these spreading mechanisms is crucial to implementing effective preventive measures. Here are some of the common ways PHP file viruses spread:
1. Compromised websites: One of the primary ways PHP file viruses spread is by infecting legitimate websites. Cybercriminals exploit vulnerabilities in website security, such as outdated software, weak passwords, or insecure plugins, to gain unauthorized access to the website. Once inside, they inject malicious code into PHP files, which allows the virus to spread to visitors’ computers or other web servers.
2. Malicious downloads: Another method of spreading PHP file viruses is through downloads. Cybercriminals may trick users into downloading infected files, such as plugins, themes, or software updates. Once downloaded and executed, these files can infect PHP files on the user’s system, potentially spreading the virus further.
3. Exploiting vulnerabilities: PHP file viruses can also spread by targeting vulnerabilities in the PHP scripts or the web server software itself. Cybercriminals actively search for security loopholes or weaknesses that can be exploited to inject malicious code into PHP files or gain unauthorized access to the server. Once the virus gains a foothold, it can propagate to other files and directories.
4. Malicious email attachments: PHP file viruses can also be spread through malicious email attachments. Cybercriminals may send emails with infected PHP files disguised as legitimate attachments. When the recipient opens the attachment, the virus can infect PHP files on their system, potentially compromising the website if the affected files are uploaded to the server.
5. Drive-by downloads: Drive-by downloads occur when a user visits a compromised website without their knowledge or consent. The website contains hidden malicious scripts that exploit vulnerabilities in the user’s browser or plugins, allowing the virus to be downloaded and executed on their system. If the user has PHP files on their computer or connected to the same network, the virus can infect those files, enabling further spread.
To protect against the spread of PHP file viruses, it is essential to take proactive security measures. This includes keeping software and plugins up to date, using strong passwords, regularly scanning for malware, implementing a web application firewall, and staying vigilant against suspicious email attachments or downloads. By adopting these best practices, you can significantly reduce the risk of PHP file viruses infecting your website or web server.
Common Types of PHP File Viruses
PHP file viruses come in various forms and can utilize different techniques to infect websites and servers. Understanding the common types of PHP file viruses will help you identify and mitigate potential threats. Here are some of the most prevalent types:
1. Backdoor Viruses: Backdoor viruses are PHP file viruses that create a hidden entry point or “backdoor” in the infected PHP file. This allows the attacker to gain unauthorized access to the web server, bypassing any security measures in place. With the backdoor, the attacker can execute arbitrary code, upload additional malware, or steal sensitive data from the server.
2. Webshell Viruses: Webshell viruses are PHP file viruses that install a malicious script, often referred to as a webshell, on the infected PHP file. These webshells provide a remote administration interface, granting the attacker full control over the website or web server. Once installed, the attacker can carry out various malicious activities, such as uploading or deleting files, executing commands, or even defacing the website.
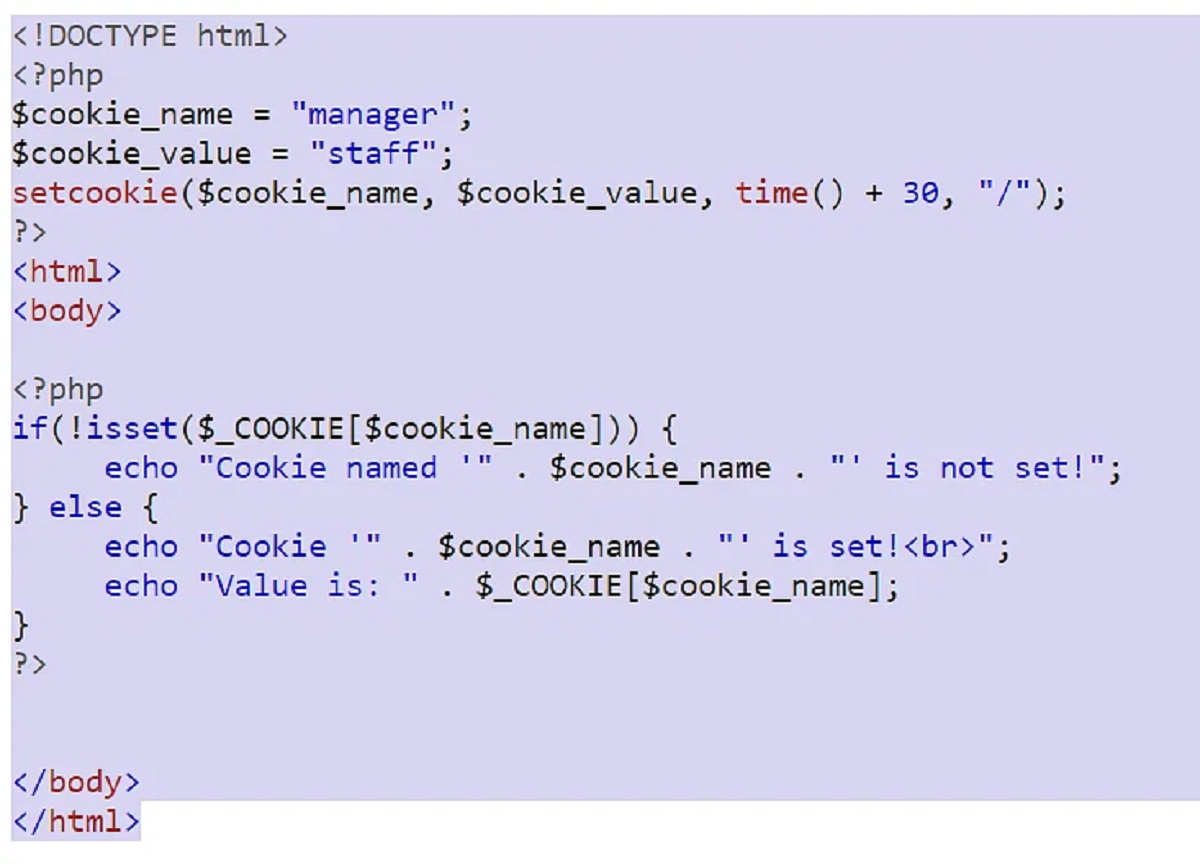
3. Phishing Viruses: Phishing viruses are designed to trick users into revealing sensitive information, such as login credentials or financial details. These PHP file viruses typically modify PHP files to create convincing login or contact forms that capture user input. The captured data is then sent to the attacker, who can use it for fraudulent purposes.
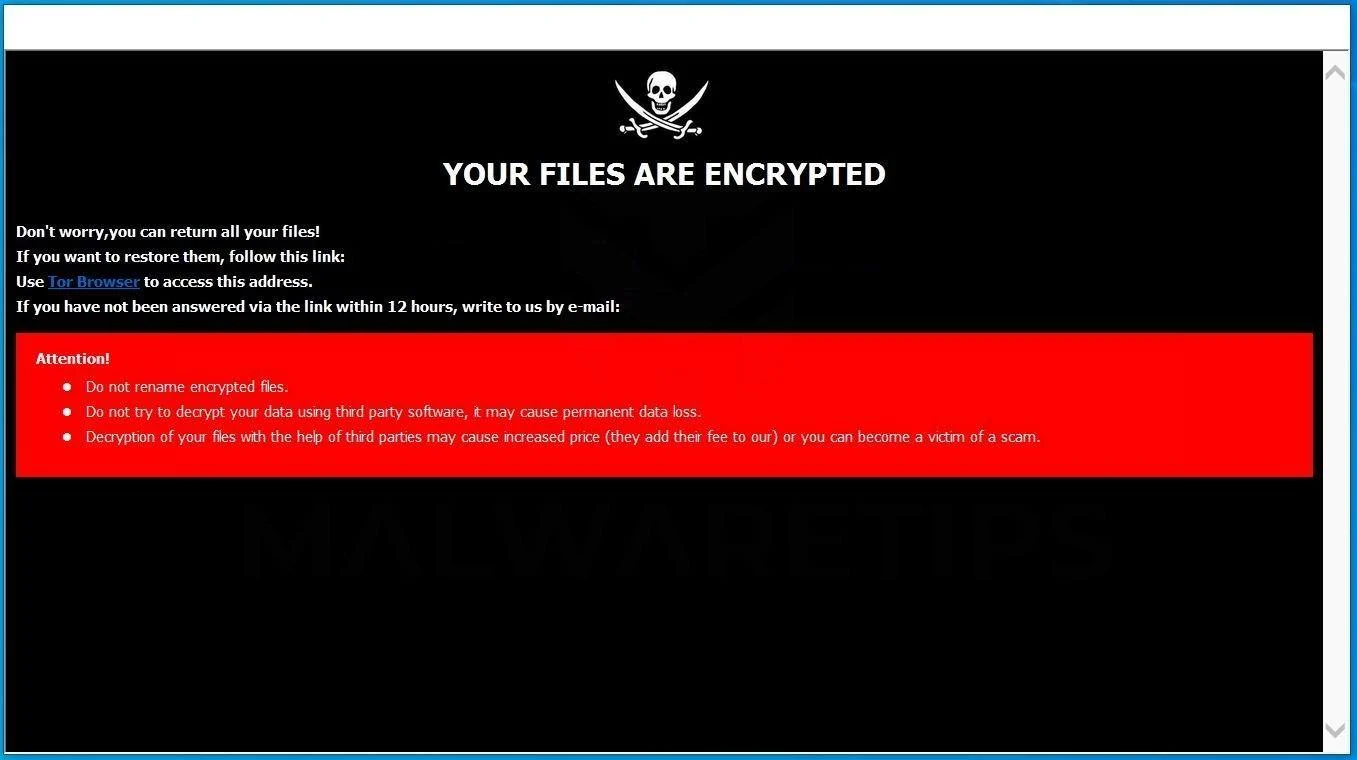
4. Malware Distribution Viruses: Malware distribution viruses focus on spreading additional malware to unsuspecting users. These PHP file viruses modify PHP files to inject code that redirects visitors to malicious websites or initiates unauthorized downloads. The downloaded malware can range from ransomware to spyware, which can wreak havoc on the infected system.
5. SEO Spam Viruses: SEO spam viruses aim to manipulate search engine rankings by injecting hidden links or spammy content into PHP files. These PHP file viruses typically target websites with high traffic volume. The injected links may redirect users to malicious websites or promote counterfeit products, negatively impacting the website’s reputation and search engine ranking.
6. File Inclusion Viruses: File inclusion viruses exploit vulnerabilities in PHP scripts that allow remote file inclusion. These PHP file viruses modify PHP files to include malicious code from external sources. The included code can then execute arbitrary commands, leading to data compromise, website defacement, or further spreading of the virus to other files.
Detecting and removing PHP file viruses require specialized tools and expertise. Implementing an up-to-date antivirus solution, conducting regular security scans, and monitoring website logs for suspicious activities can help identify and mitigate these threats. It’s important to note that preventive measures, such as keeping software and plugins updated, implementing strong access controls, and performing regular backups, can significantly reduce the risk of infection.
By staying informed about the common types of PHP file viruses, you can take proactive steps to protect your website and server from potential threats.
Signs of a PHP File Virus
Detecting a PHP file virus early is essential for preventing further damage to your website and server. Knowing the signs of a PHP file virus allows you to take immediate action and mitigate the impact. Here are some common indicators that your PHP files may be infected:
1. Unusual Website Behavior: If you notice unexpected changes in your website, such as strange redirects, defaced pages, or unauthorized content modifications, it could be a sign of a PHP file virus. These viruses often alter the code of PHP files, leading to abnormal website behavior.
2. Slow Website Performance: PHP file viruses can cause your website to slow down significantly. This is because the infected PHP files may contain additional code or processes that consume server resources, resulting in increased load times.
3. Increased Network Traffic: If you notice a sudden surge in network traffic or bandwidth usage without any reasonable explanation, it could indicate that your website or server is being used as part of a larger malicious operation. PHP file viruses may initiate unauthorized activities that require network resources.
4. Unexpected File Modifications: Check your PHP files for any unexpected modifications. Look for changes in file size, timestamps, or the presence of unfamiliar code or scripts. These alterations can be clear indicators of a PHP file virus.
5. Inclusion of Strange Files: PHP file viruses may introduce additional files or directories to your server that you did not create or authorize. These files may have random names or extensions and can serve as a gateway for further malware attacks.
6. Alerts from Website Security Tools: If you have website security tools or plugins installed, pay attention to any alerts or notifications regarding unusual activities or potential infections. These tools can often detect PHP file viruses and notify you of potential threats.
7. Anomalies in Website Analytics: Monitor your website analytics for any unusual patterns or anomalies. A sudden increase or decrease in traffic, changes in referral sources, or a spike in bounce rates could indicate the presence of a PHP file virus affecting your website’s performance.
If you suspect your website is infected with a PHP file virus, it is crucial to take immediate action. First, isolate the affected files by taking them offline or removing them from the server temporarily. Notify your web hosting provider and engage with cybersecurity professionals who can assist in identifying and removing the virus effectively.
Prevention is always better than cure when it comes to PHP file viruses. Regularly update your website’s software and plugins, use strong passwords, implement a web application firewall, and perform routine security scans to minimize the risk of infection. By staying vigilant and proactive, you can protect your website and server from the damaging effects of PHP file viruses.
Damage Caused by PHP File Viruses
PHP file viruses can inflict significant damage to websites, servers, and the individuals or organizations that rely on them. Understanding the potential consequences of these viruses is crucial for taking appropriate measures to prevent and mitigate their impact. Here are some of the damages that PHP file viruses can cause:
1. Data Theft: PHP file viruses can compromise sensitive data, including user credentials, personal information, or financial details. Cybercriminals can exploit this stolen data for identity theft, financial fraud, or other malicious activities. The theft of customer or client data can lead to reputational damage and legal implications.
2. Website Defacement: PHP file viruses can deface your website by replacing its original content with malicious or unauthorized content. This can result in a loss of credibility and trust, causing visitors to perceive your website as compromised or untrustworthy. It can also lead to negative impacts on your brand reputation.
3. Distributed Denial of Service (DDoS) Attacks: PHP file viruses can turn your website or server into a part of a botnet, allowing attackers to carry out DDoS attacks. These attacks overwhelm your server with an excessive amount of incoming traffic, causing service disruptions and rendering your website inaccessible to legitimate users.
4. Loss of Website Functionality: PHP file viruses can modify or delete critical files or code that are essential for your website to function properly. This can result in broken links, error messages, or complete website downtime. As a result, your website may lose its functionality and fail to serve its intended purpose.
5. Blacklisting by Search Engines: If your website is infected with a PHP file virus and is identified as a source of malware or spam, search engines may blacklist it. Being blacklisted means that your website will no longer appear in search results, severely impacting your online visibility and traffic.
6. Financial Loss: The damage caused by PHP file viruses can lead to financial losses. This can include the cost of repairing and recovering your website, conducting security audits, reputational damage recovery, and potential legal expenses resulting from data breaches or compliance violations.
7. Spread of Additional Malware: PHP file viruses can serve as entry points for other types of malware, such as ransomware, spyware, or adware. This can further compromise your website, infect user devices, and amplify the extent of the damage.
It is crucial to respond promptly to mitigate the effects of a PHP file virus. This involves isolating and removing infected files, strengthening website security, implementing regular backups, and seeking professional assistance to ensure a comprehensive recovery process.
Preventing these damages requires proactive security measures, such as keeping software up-to-date, following best practices for secure coding and web development, implementing robust access controls, and employing web application firewalls. By taking these steps, you can significantly reduce the risk of falling victim to the devastating consequences of PHP file viruses.
How to Protect Against PHP File Viruses
Protecting your website and server from PHP file viruses is crucial to safeguard your valuable data, preserve your online reputation, and ensure uninterrupted operation. By implementing effective security measures, you can significantly reduce the risk of falling victim to these malicious threats. Here are some proactive steps you can take to protect against PHP file viruses:
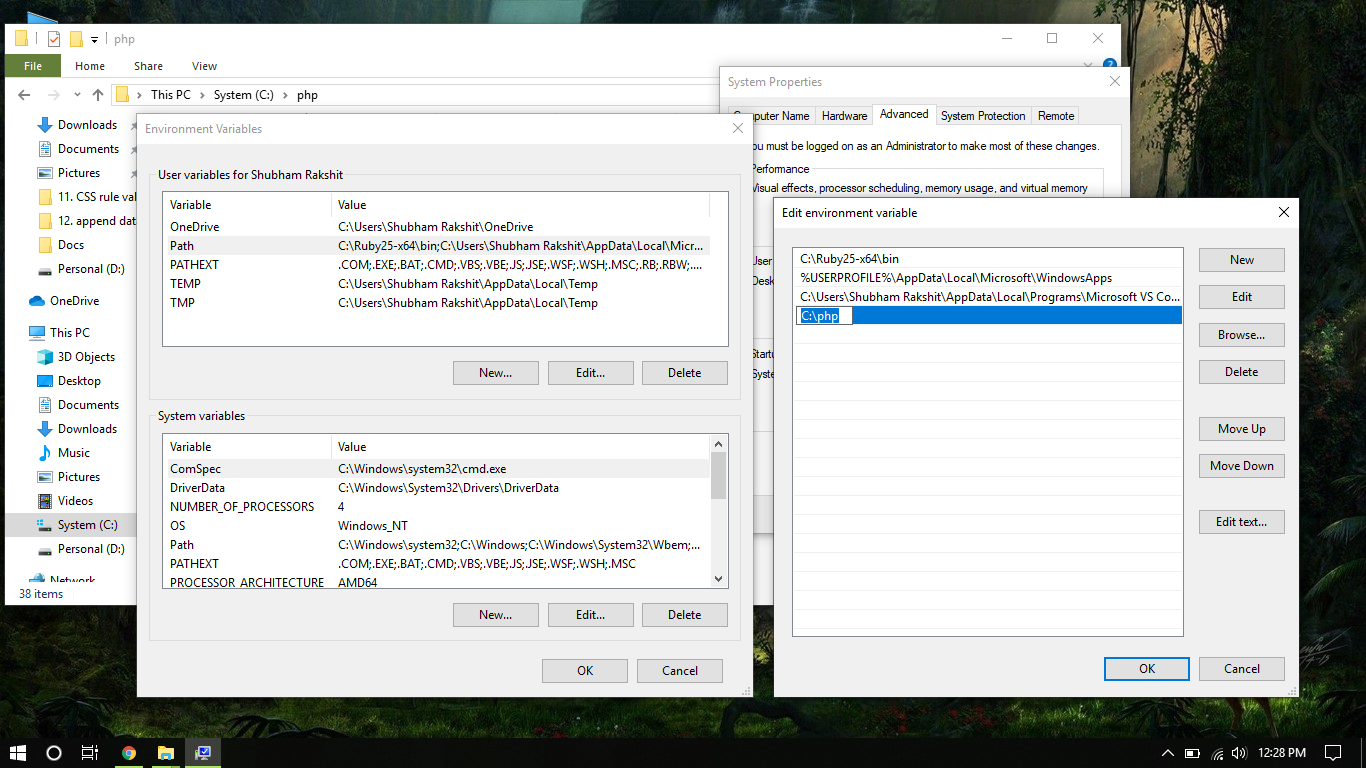
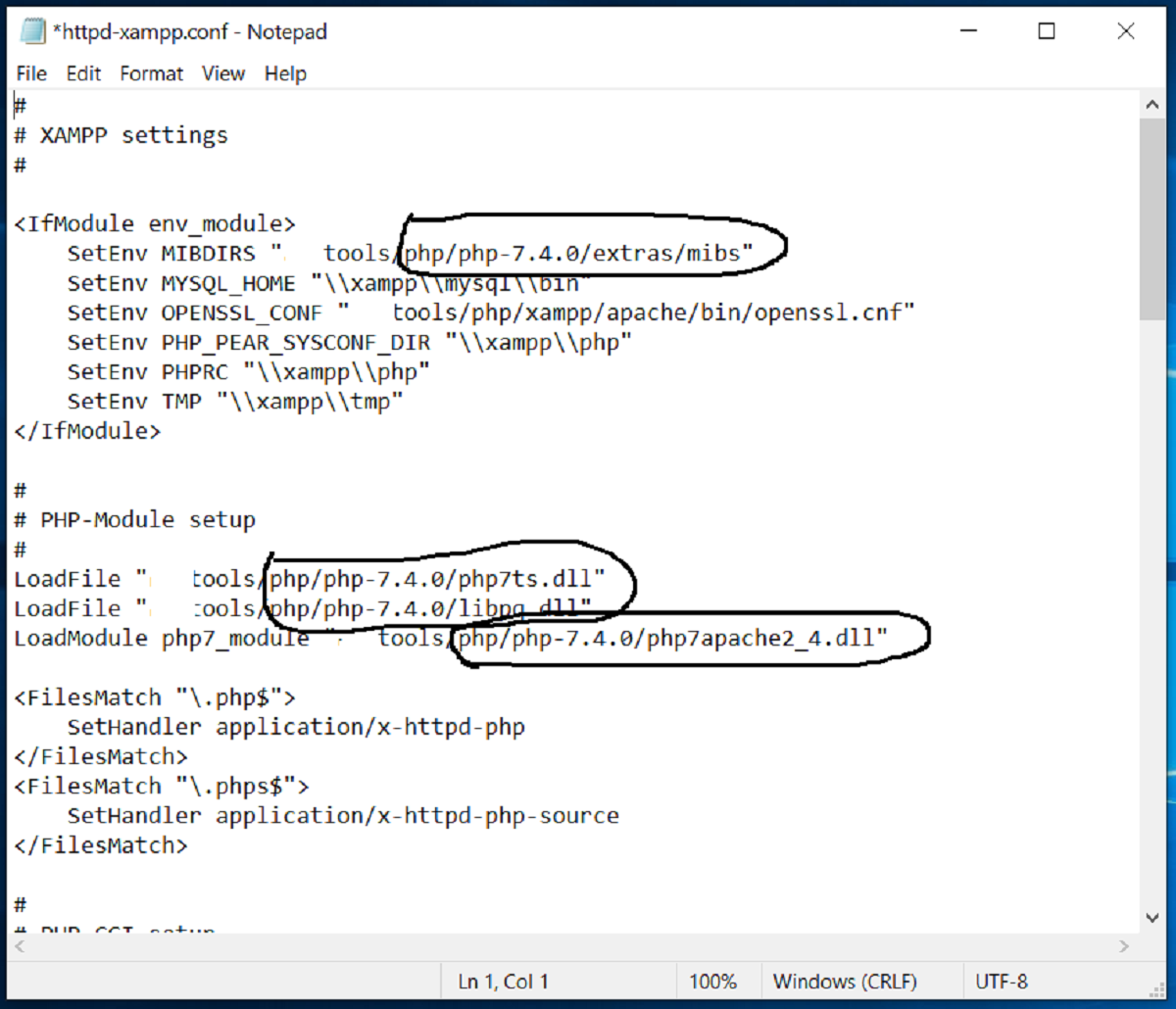
1. Keep Software and Plugins Up-to-Date: Regularly update your website’s content management system (CMS), PHP version, and installed plugins. Outdated software and plugins often contain vulnerabilities that can be exploited by PHP file viruses. By implementing updates and security patches, you close those security gaps.
2. Use Strong and Secure Passwords: Ensure that your website, server, and database passwords are strong and unique. Use a combination of uppercase and lowercase letters, numbers, and special characters. Avoid using common or easily guessable passwords, as they can be easily hacked.
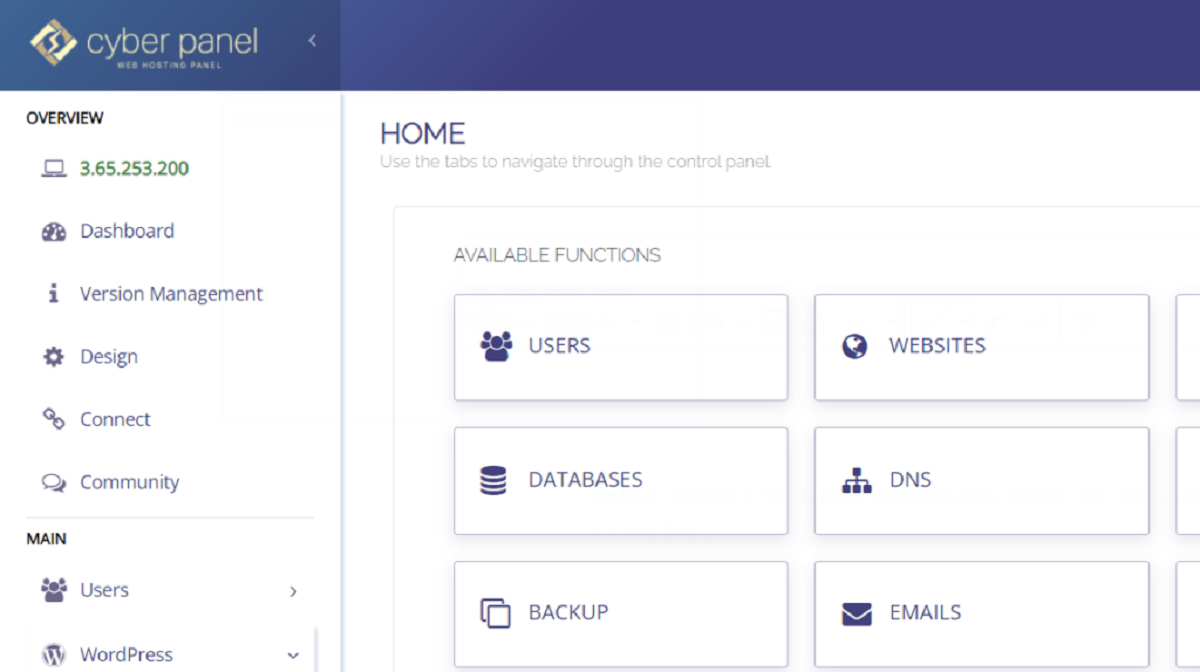
3. Implement a Web Application Firewall (WAF): Deploy a WAF to protect your website by filtering out malicious traffic and blocking known attack patterns. A WAF acts as an additional layer of protection, monitoring incoming requests and preventing potentially harmful PHP file viruses from reaching your server.
4. Perform Regular Security Audits: Conduct routine security audits of your website and server. This involves scanning for vulnerabilities, identifying compromised files, and addressing security weaknesses. Regular audits help you stay proactive in detecting and addressing PHP file viruses before they cause significant damage.
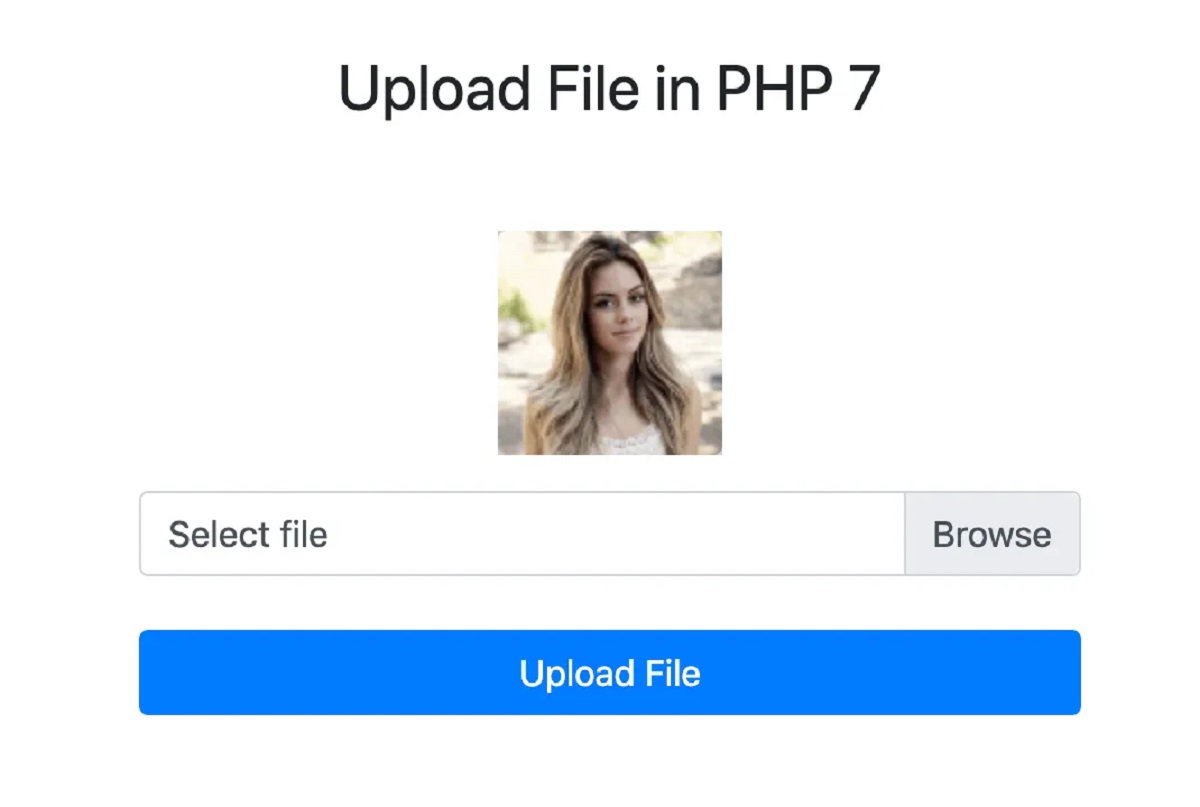
5. Use Secure File Uploads: Implement strong validation techniques for file uploads. Ensure that any files uploaded to your website are thoroughly scanned for malware using an antivirus solution. Restrict the types of files that can be uploaded and set proper permissions to prevent unauthorized access.
6. Practice Secure Coding: Follow secure coding practices when writing PHP scripts. Avoid using deprecated or insecure functions that can be exploited by attackers. Sanitize user inputs to prevent SQL injection and other code injection vulnerabilities.
7. Perform Regular Backups: Regularly back up your website files and databases. In the event of a PHP file virus infection, having backups ensures that you can easily restore your website to a clean and secure state without significant data loss.
8. Stay Vigilant Against Suspicious Activity: Monitor your website’s access logs and regularly review server logs for any suspicious activity or unauthorized access attempts. Pay attention to any alerts or notifications from your security software or hosting provider and promptly investigate and rectify any potential issues.
9. Educate Website Administrators and Users: Educate yourself and your website administrators about common phishing techniques, malware distribution methods, and social engineering tactics. Promote good security practices such as avoiding suspicious email attachments, practicing safe browsing habits, and staying informed about evolving threats.
10. Engage with Cybersecurity Professionals: Consider seeking assistance from cybersecurity professionals who specialize in website security. They can provide expert insights, conduct penetration testing, and implement robust security measures tailored to your specific needs.
By implementing these proactive measures, you can fortify your website and server against PHP file viruses. Remember, prevention is key when it comes to protecting your online assets and maintaining a secure online presence. Stay vigilant, keep your security measures up to date, and regularly review and enhance your security practices to stay one step ahead of potential threats.
Detecting and Removing PHP File Viruses
Swift detection and prompt removal of PHP file viruses are crucial to minimize the potential damage to your website and server. By implementing a proactive approach to security and utilizing effective tools and techniques, you can effectively detect and remove PHP file viruses. Here are the steps to follow:
1. Implement Regular Security Scans: Utilize reputable antivirus or security plugins to regularly scan your website’s files, directories, and databases. These scans can identify potentially infected PHP files by checking for known malicious patterns or suspicious code snippets.
2. Monitor File Modifications: Keep a watchful eye on your website’s PHP files for any unauthorized modifications. Check file sizes, timestamps, and compare the code to see if any unusual or unfamiliar changes have been made. Suspicious modifications should be thoroughly investigated.
3. Examine Access Logs: Review your web server access logs to identify any unauthorized access attempts or suspicious activities. Look for unusual IP addresses, repeated access to sensitive files, or any suspicious HTTP requests that might indicate a PHP file virus infection.
4. Engage with Website Security Service: Consider utilizing the services of a professional website security provider. These providers offer continuous monitoring, malware detection, and removal services. They have specialized tools and expertise to identify, quarantine, and remove PHP file viruses effectively.
5. Isolate and Remove Infected Files: Once a PHP file virus is detected, immediately isolate the infected files by taking them offline or moving them to a secure quarantine location. This prevents the virus from further spreading and causing additional harm. Delete or replace the infected files with clean backups.
6. Update and Patch Software: Ensure that your CMS, plugins, and server software are running on the latest versions. Regularly install security patches and updates provided by the software vendors. This helps to address known vulnerabilities that can be exploited by PHP file viruses.
7. Change Access Credentials: If you suspect a PHP file virus, change all passwords for your website, server, and database. This prevents any unauthorized access by the attacker even after the infected files have been removed.
8. Monitor Website Behavior: Continuously monitor your website’s performance, user experiences, and user feedback for any signs of persistent issues. Keep an eye out for unusual redirects, error messages, or reports of suspicious activities from site visitors.
9. Review Third-Party Code and Plugins: Evaluate all third-party code and plugins used in your website’s development. Only use trusted sources and regularly update them with the latest versions to ensure they are free from vulnerabilities that could be exploited by PHP file viruses.
10. Implement Web Application Firewall: Deploy a web application firewall (WAF) to protect your website from various types of attacks, including PHP file viruses. A WAF can detect and block malicious traffic, mitigating the risk of virus infection.
Remember, prevention and proactive measures are crucial to minimizing the risk of PHP file viruses. Regularly applying security patches, keeping backups, educating yourself and website administrators, and maintaining strong security practices can significantly reduce the likelihood of a PHP file virus infecting your website. If you’re unsure or lack the expertise, consider seeking assistance from cybersecurity professionals who can guide you in effectively detecting and removing PHP file viruses from your website and server.
Conclusion
PHP file viruses pose a significant threat to the security, integrity, and functionality of websites and servers. These malicious programs exploit vulnerabilities in PHP files and web server environments, often leading to severe consequences such as data theft, website defacement, financial loss, and reputational damage. However, by implementing proactive security measures, staying vigilant, and promptly responding to potential threats, you can protect your website and server from the damaging effects of PHP file viruses.
Understanding the nature of PHP file viruses, their spreading mechanisms, and common signs of infection is crucial in effectively safeguarding your online assets. Regularly updating software and plugins, practicing secure coding techniques, and implementing strong access controls are fundamental preventive measures. Monitoring website logs, conducting regular security audits, and utilizing security tools such as antivirus solutions and web application firewalls can help detect and mitigate PHP file viruses at an early stage.
In the event of a PHP file virus infection, swift action is essential. Isolating and removing infected files, changing access credentials, and seeking professional assistance from website security providers can aid in thorough virus removal and recovery without significant disruptions to your online presence.
Remember, protecting against PHP file viruses is an ongoing process. Staying informed about evolving threats, educating yourself and website administrators about best security practices, and regularly reviewing and enhancing your security measures are key to maintaining a secure and resilient online environment.
By prioritizing security, staying proactive, and adopting a comprehensive approach to website and server protection, you can minimize the risk of falling victim to PHP file viruses and ensure the continued safety and functionality of your online presence.