Introduction
IP Spoofing, also known as IP Address Spoofing, is a technique used in computer networking to manipulate the source IP address in a packet’s header. This method allows the sender to disguise their true identity and make it appear as if the data is originating from a different IP address. IP Spoofing can be employed for various purposes, both harmful and legitimate, such as bypassing restrictions, launching malicious attacks, or ensuring anonymity.
IP Spoofing involves modifying the source IP address of a packet, which is a fundamental component of Internet communication. Normally, this address is used to identify the source of the data and establish network connections. However, by altering the IP address, the true origin can be concealed, making it difficult to trace back the actual sender.
This technique can be used for both positive and negative intentions. On the positive side, IP Spoofing can be utilized by researchers and developers for testing network security, evaluating firewalls, and analyzing network behavior. However, on the negative side, it can be exploited by attackers to perform DDoS (Distributed Denial of Service) attacks, IP address hijacking, identity theft, and other malicious activities.
It is crucial to be aware of the risks and legal implications associated with IP Spoofing. While it can be a powerful tool for certain purposes, its misuse can result in severe consequences, including legal penalties.
In the following sections, we will explore the concept of IP Spoofing in more detail, discuss the associated risks and legal implications, and provide an overview of the steps and tools involved in IP Spoofing. We will also address the ethical considerations surrounding this practice.
What is IP Spoofing?
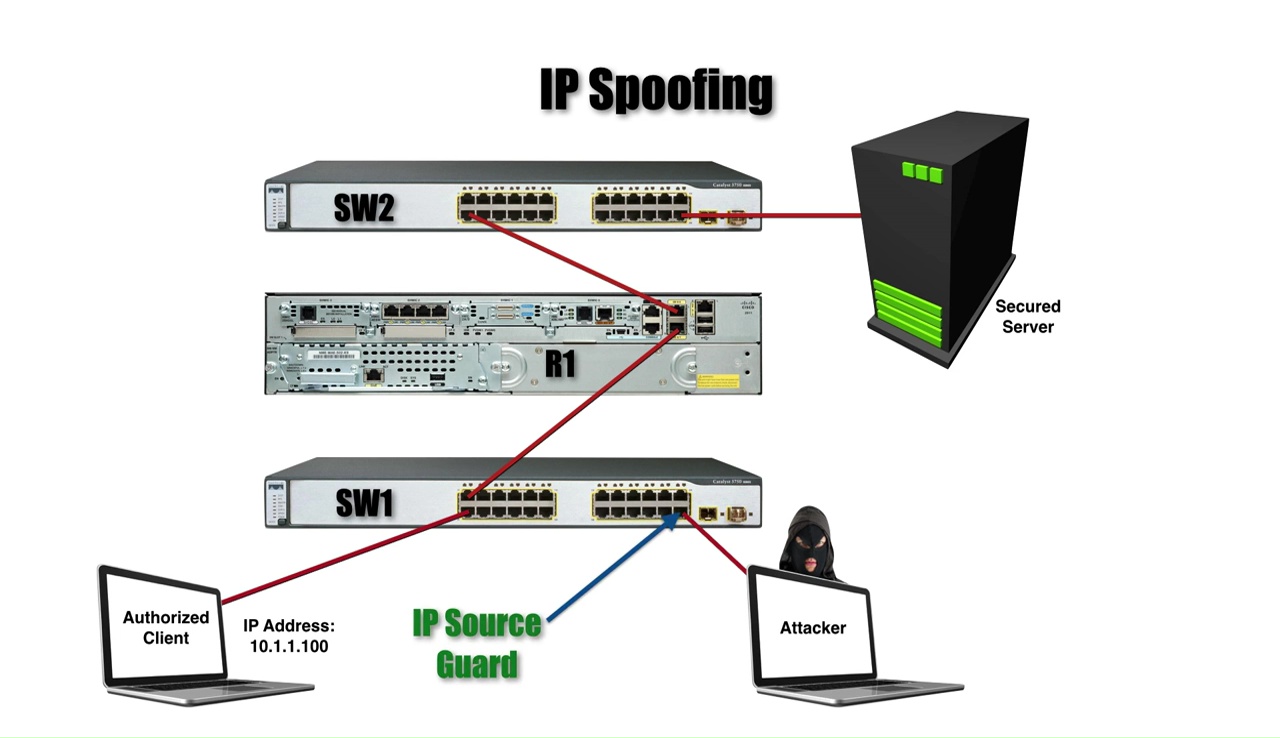
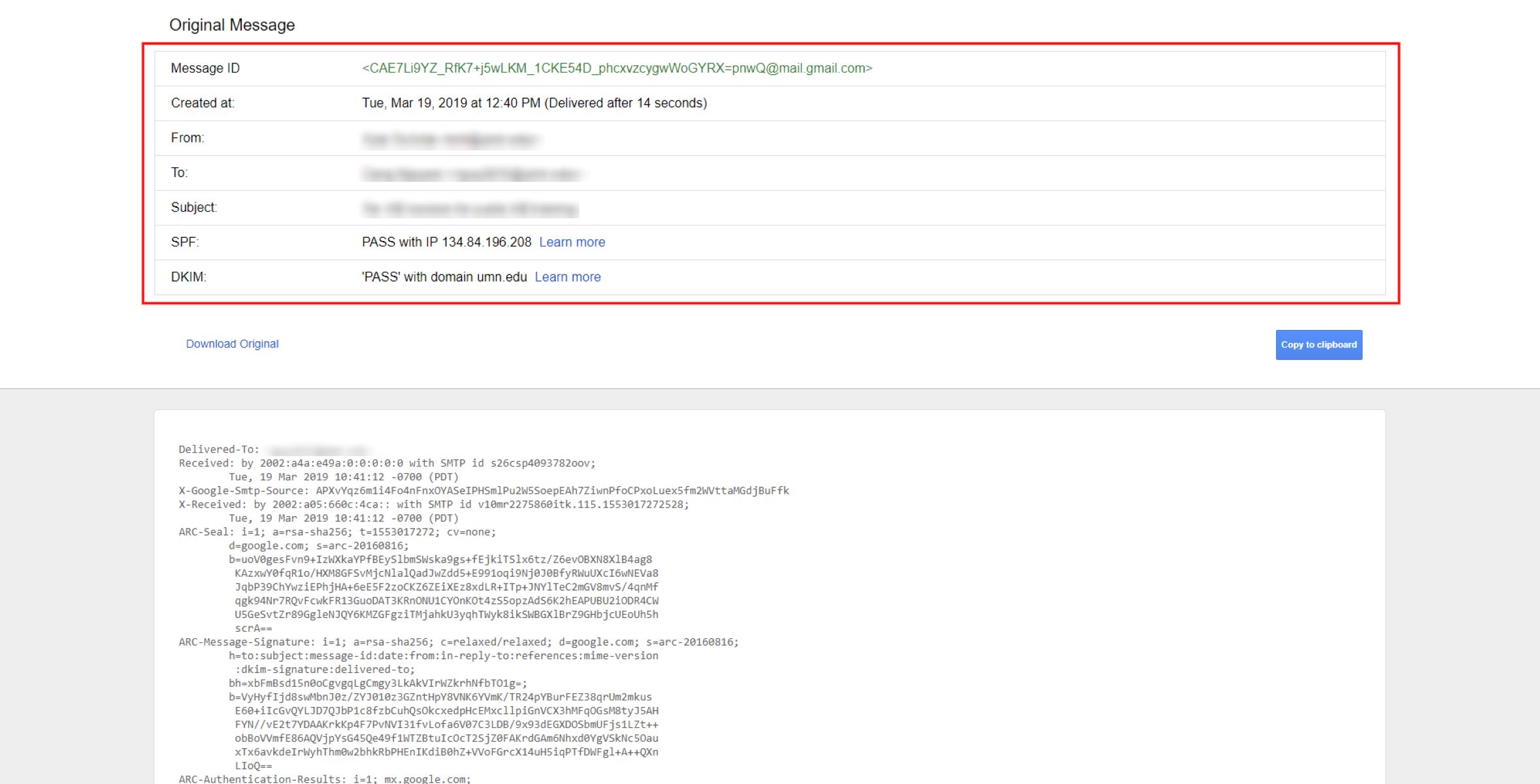
IP Spoofing refers to the act of altering the source IP address in a packet’s header to deceive the recipient or bypass certain security measures. When data is sent over the internet, it is divided into packets, and each packet contains a header that includes information such as the source and destination IP addresses. By manipulating the source IP address, an attacker can make it appear as if the data is originating from a different IP address altogether.
The main purpose of IP Spoofing is to conceal the identity of the sender and deceive the recipient or intermediary devices along the network path. This technique can be employed for various reasons, ranging from legitimate uses to malicious activities.
In legitimate scenarios, IP Spoofing can be utilized for network testing and troubleshooting. For example, network administrators may simulate different IP addresses to assess the security measures and response of their own network. They can also use IP Spoofing to emulate different network conditions and evaluate the effectiveness of their network infrastructure.
However, IP Spoofing is most commonly associated with malicious activities. Attackers can use IP Spoofing to launch various attacks, such as Denial of Service (DoS) or Distributed Denial of Service (DDoS) attacks. By altering the source IP address, attackers can make it difficult for the victims or network operators to trace back the origin of the attack, thus complicating the mitigation process.
Furthermore, IP Spoofing can be employed for other nefarious purposes, including IP address hijacking, where an attacker assumes the IP address of a legitimate user or device, enabling them to intercept or modify the victim’s communication. This can lead to unauthorized access to sensitive information or even identity theft.
It is essential to note that IP Spoofing alone does not guarantee successful penetration or unauthorized access to a network. Additional measures, such as exploiting vulnerabilities or employing sophisticated techniques, may be required to accomplish malicious objectives.
Understanding the concept of IP Spoofing is paramount for both network administrators and individuals alike. By being aware of the possibilities and risks associated with IP Spoofing, individuals can take appropriate precautions to protect their networks and ensure the security of their data and communications.
Risks and Legal Implications of IP Spoofing
While IP Spoofing can be employed for legitimate purposes, it carries significant risks and legal implications when used maliciously. Understanding these risks is vital to prevent abuse and mitigate potential damage.
One of the primary risks associated with IP Spoofing is the potential for launching DoS or DDoS attacks. By spoofing IP addresses, attackers can overwhelm target systems with a flood of requests, rendering them unable to handle legitimate traffic. This can result in severe downtime, financial loss, and reputational damage for individuals or organizations. Moreover, attackers can distribute the attack traffic across multiple IP addresses, making it challenging to identify and mitigate the sources of the attack.
IP Spoofing also opens doors for IP address hijacking, where an attacker assumes the identity of a legitimate user or device. This can lead to unauthorized access to sensitive information, data interception, and the potential for identity theft. Individuals or organizations may suffer severe consequences if their IP addresses are misused in such activities.
From a legal standpoint, engaging in IP Spoofing without proper authorization is often considered illegal in many jurisdictions. Misusing IP Spoofing techniques to launch attacks, cause disruptions, or engage in identity theft can result in legal penalties. Violators may face criminal charges, significant fines, and potential imprisonment.
Furthermore, organizations that fail to implement adequate security measures to prevent IP Spoofing can also face legal consequences. As custodians of user data and network integrity, organizations are responsible for safeguarding their networks from malicious activities such as IP Spoofing. Negligence in implementing security controls may expose them to legal liabilities, regulatory sanctions, and damage to their reputation.
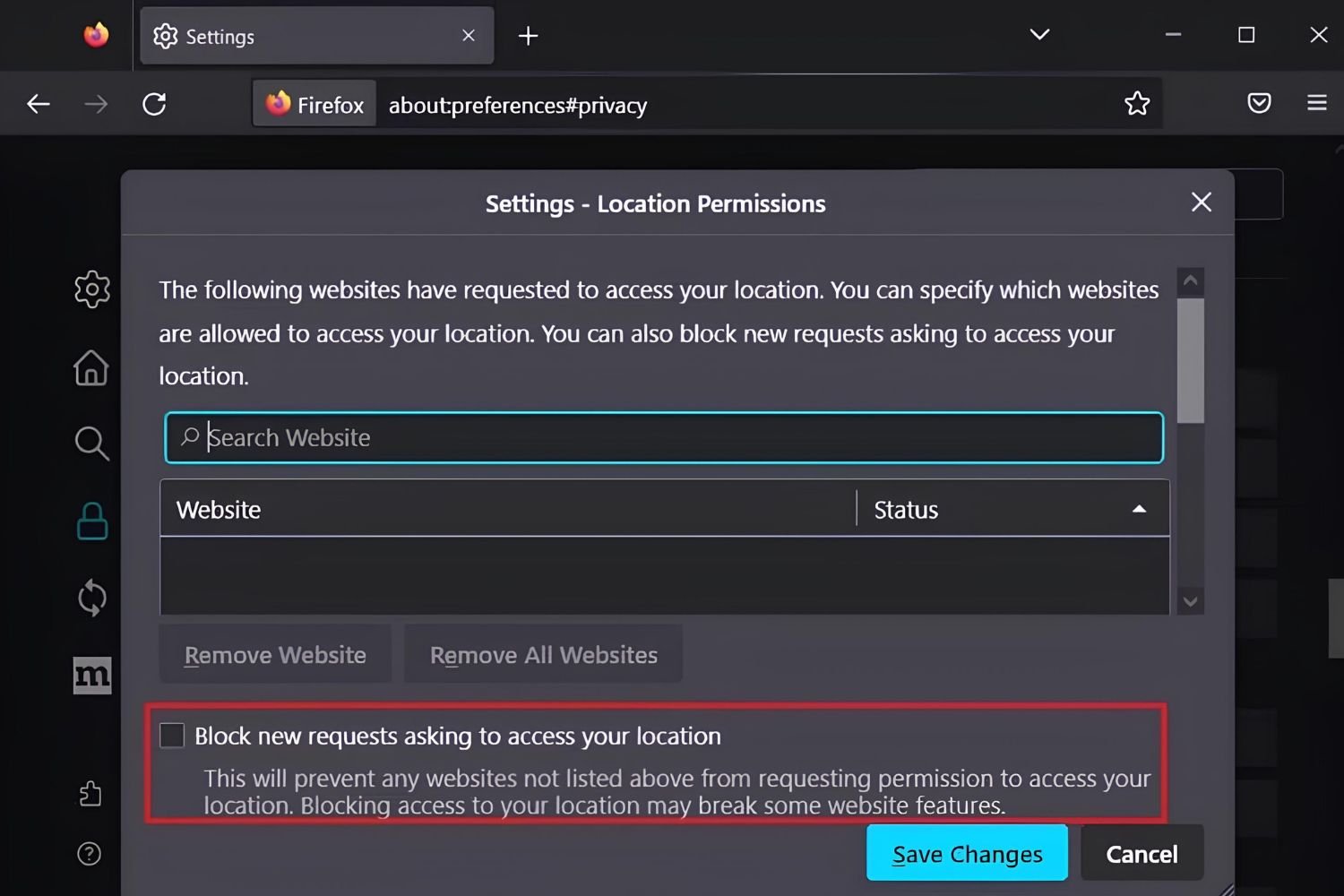
To combat the risks associated with IP Spoofing, network administrators and individuals should implement various security measures. These measures include firewall configurations, intrusion detection systems, and implementing secure network protocols such as Secure Shell (SSH) or Virtual Private Networks (VPNs).
It is crucial to educate individuals about the risks and consequences of IP Spoofing. By raising awareness and promoting responsible usage, the harmful impact of IP Spoofing can be minimized, and individuals can make informed decisions regarding their actions and network security.
Steps to IP Spoofing
IP Spoofing involves several steps to successfully alter the source IP address and deceive the recipient or intermediary devices. It is important to understand these steps to fully comprehend the process and its implications.
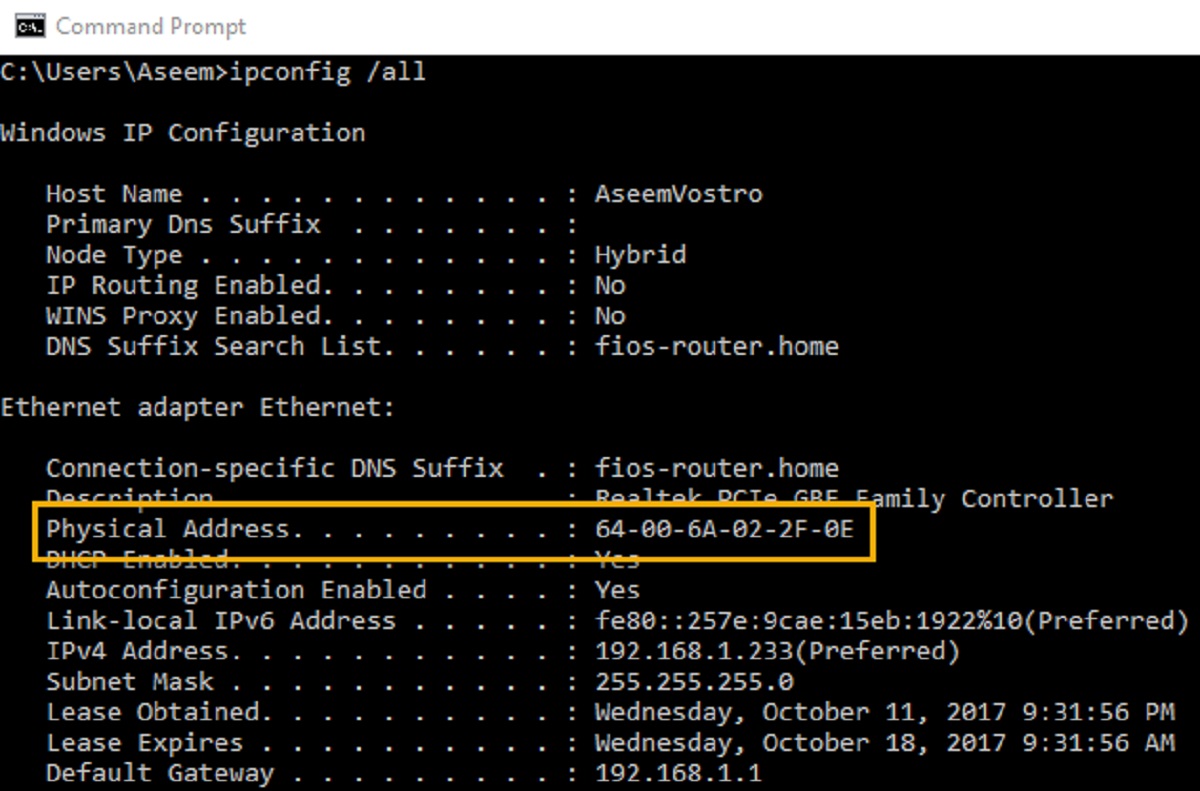
- Identify the target: The first step in IP Spoofing is to identify the target whose IP address you want to spoof. This can be a specific device, a network, or even an individual.
- Choose the spoofed IP address: Select an IP address to use as the spoofed source IP. This IP address should ideally be from a trusted network or one that wouldn’t raise suspicion.
- Disable or bypass filtering: To perform IP Spoofing successfully, you may need to disable or bypass any filtering mechanisms or firewall rules that would otherwise block or detect spoofed IP addresses.
- Create and modify packets: Craft or modify the packets you intend to send. This involves altering the source IP address within the packet’s header to the chosen spoofed IP address.
- Send the spoofed packets: Transmit the spoofed packets with the modified source IP address. This can be done using various network tools or programming languages capable of manipulating packet headers.
- Avoid detection: It is essential to take additional steps to avoid detection during the IP Spoofing process. This may include randomizing the timing of packet transmission, utilizing different IP addresses for each packet, or using techniques such as IP fragmentation to further obfuscate the source.
- Monitor and analyze: Monitor the network traffic and analyze the response of the target or any intermediary devices. This can help determine the effectiveness of the IP Spoofing technique and identify potential vulnerabilities that may need to be addressed.
It is important to note that IP Spoofing can have severe legal and ethical implications if used for malicious purposes. As such, it is essential to understand and respect the ethical considerations surrounding this technique. Engaging in unauthorized IP Spoofing activities can result in severe consequences, including legal penalties and damage to one’s reputation.
While IP Spoofing can be a valuable tool for network testing and security evaluation, it is crucial to approach it responsibly and within the bounds of the law and ethical guidelines. By doing so, individuals can protect themselves and others while harnessing the benefits of this technique for legitimate purposes.
Tools for IP Spoofing
IP Spoofing requires specialized tools and software that can manipulate packet headers and modify the source IP address. These tools are often utilized by researchers, network administrators, and individuals interested in testing network security or analyzing network behavior. While these tools can be used for legitimate purposes, it is important to note that their misuse for malicious activities is both unethical and illegal.
Here are a few of the popular tools used for IP Spoofing:
- Scapy: Scapy is a powerful Python-based tool that allows for packet manipulation, including spoofing IP addresses. It provides a flexible framework for crafting and sending customized packets to the network.
- Hping3: Hping3 is a versatile command-line tool that supports various network protocols and can be used for IP Spoofing. It offers the ability to create and send custom packets with altered source IP addresses.
- Cain & Abel: Cain & Abel is a comprehensive network security tool that offers IP Spoofing capabilities, among many other features. It can be used for network password cracking, ARP spoofing, and other security-related tasks.
- Wireshark: Wireshark is a popular network protocol analyzer that can be utilized to capture and analyze network traffic. While it is not primarily designed for IP Spoofing, it can assist in monitoring and identifying potential IP Spoofing attempts.
- Ettercap: Ettercap is a powerful network sniffer and interceptor that supports various Man-in-the-Middle (MITM) attacks, including IP Spoofing. It allows for the modification of packets and can intercept communication between devices on a network.
It is worth highlighting that the use of IP Spoofing tools should strictly adhere to legal and ethical guidelines. These tools should only be utilized for legitimate purposes, such as network testing, security assessments, or authorized penetration testing. Any unauthorized or malicious use of these tools can result in severe consequences, including legal action and reputational damage.
Additionally, when using IP Spoofing tools, it is important to obtain proper authorization and follow any applicable laws and regulations. Obtaining permission from the network owner or system administrator is crucial to ensure that the activities performed with IP Spoofing tools are within the boundaries of legal and ethical frameworks.
Overall, it is essential to approach the use of IP Spoofing tools responsibly, maintaining a strong commitment to ethical behavior and respecting the rights and privacy of others. By doing so, individuals can leverage these tools for positive purposes while minimizing the potential for misuse or harm.
Ethical Considerations of IP Spoofing
The practice of IP Spoofing raises important ethical considerations that must be carefully evaluated. While IP Spoofing can be used for legitimate purposes, ensuring ethical behavior is essential to prevent harm and maintain trust within the digital ecosystem.
One of the primary ethical concerns surrounding IP Spoofing is the potential for misuse and harm. While it can be employed for network testing, security evaluations, or authorized research, the same techniques can be utilized for launching malicious attacks and engaging in illegal activities. It is crucial to differentiate between responsible, authorized usage and malicious intent.
Respect for privacy and consent is another crucial ethical consideration. Engaging in IP Spoofing without proper authorization can infringe upon the privacy and security of individuals or organizations. Obtaining consent from the network owner or system administrator is essential to ensure that the activities performed with IP Spoofing are lawful and adhere to ethical standards.
Transparency and accountability are vital values that need to be upheld when considering IP Spoofing. If IP Spoofing activities are performed for legitimate purposes, it is crucial to communicate openly about the actions taken and the potential implications. This helps to establish trust and ensures that individuals or organizations understand the intentions and potential impact of the IP Spoofing activities.
Another ethical consideration relates to the responsible disclosure of vulnerabilities identified through IP Spoofing. If security flaws or vulnerabilities are discovered during the testing process, it is important to follow ethical guidelines and responsible disclosure practices. This involves notifying the relevant parties, such as network administrators or software vendors, and allowing them the opportunity to address and resolve the vulnerabilities before they can be exploited maliciously.
Furthermore, network neutrality and fair use principles need to be respected in the context of IP Spoofing. Engaging in activities that discriminate against certain users or restrict access to information based on manipulated IP addresses is against the principles of a free and open internet. IP Spoofing should not be exploited to manipulate network traffic for unfair advantage or to limit access to resources.
Ultimately, ethical behavior and responsible usage of IP Spoofing are essential to maintain the trust and integrity of computer networks and the broader internet ecosystem. It is important to ensure that IP Spoofing activities align with legal frameworks, ethical guidelines, and the principles of honesty, transparency, privacy, and fairness in order to prevent harm and promote a secure and inclusive digital environment.
Conclusion
IP Spoofing is a technique that can be used for both legitimate and malicious purposes. By altering the source IP address in a packet’s header, the true origin of data can be concealed, allowing for various applications, such as security testing, network troubleshooting, or even launching malicious attacks.
However, it is crucial to understand the risks and legal implications associated with IP Spoofing. Misuse of this technique can lead to severe consequences, including legal penalties, reputational damage, and harm to individuals or organizations. Engaging in IP Spoofing activities without proper authorization and adherence to ethical guidelines can infringe upon privacy, compromise security, and disrupt network infrastructure.
To ensure responsible usage of IP Spoofing, it is important to obtain proper authorization, communicate openly about intentions and potential impact, and adhere to legal frameworks and ethical standards. Engaging in legitimate activities, such as network testing or security assessments, can help improve network resilience and safeguard against potential vulnerabilities.
Additionally, it is important to promote awareness and education regarding IP Spoofing and its ethical considerations. By raising awareness, individuals can make informed decisions, respect privacy and consent, and contribute to a more secure and trustworthy digital ecosystem.
In conclusion, IP Spoofing is a powerful tool that should be used responsibly and ethically. It is essential to balance the potential benefits of this technique with the necessary precautions and considerations to prevent misuse and harm. By upholding ethical behavior, accountability, and transparency, individuals and organizations can promote a secure and reliable network environment while respecting the rights and privacy of others.