Introduction
Welcome to the world of IP addresses! In today’s digital landscape, where everything revolves around the internet, understanding IP addresses is crucial. An IP (Internet Protocol) address is a unique numerical identifier that allows devices to communicate with each other on the internet.
But have you ever wondered what you can do with someone’s IP address? Can it reveal their location, personal information, or even be used to track them? In this article, we will delve into the possibilities and limitations of using an IP address for various purposes.
Before we dive into the exciting exploration, let’s develop a basic understanding of IP addresses. Each device connected to the internet, whether it’s a computer, smartphone, or tablet, is assigned an IP address. There are two types of IP addresses: IPv4 (Internet Protocol version 4) and IPv6 (Internet Protocol version 6). IPv4 addresses are represented by sets of four numbers separated by periods, while IPv6 addresses have a more complex alphanumeric format.
Now that we have a grasp on IP address fundamentals, let’s explore what can be done with someone’s IP address. From identifying the general location of the user to obtaining limited personal information, there are a few things you can do. However, it is important to note that using an IP address alone has its limitations, and personal information cannot be easily extracted without permission or legal justification.
So, if you’re curious about how IP addresses can be utilized and want to understand the implications, stick with us. In the following sections, we will address the various aspects of working with someone’s IP address and discuss the potential options available.
IP Address Basics
Before we delve into the functionalities of an IP address, it’s important to have a solid grasp of the basics. An IP address, which stands for Internet Protocol address, serves as a unique identifier for devices connected to a network. It enables communication and data exchange between devices, allowing them to send and receive information across the internet.
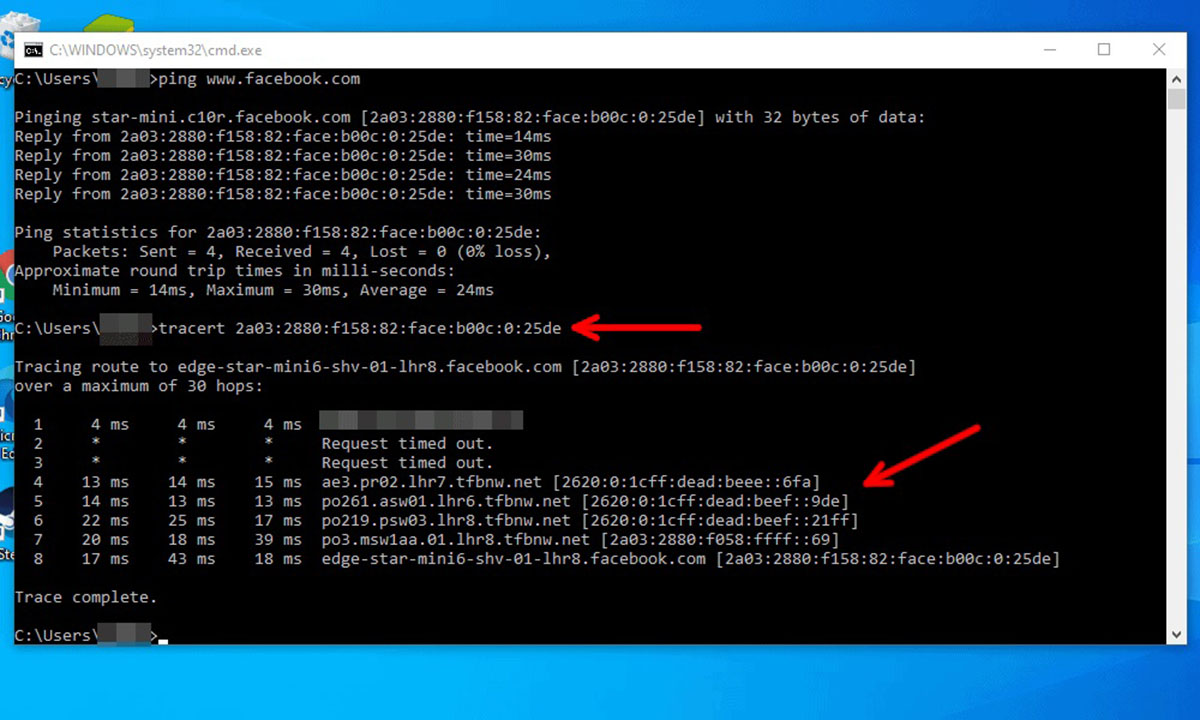
There are two main types of IP addresses: IPv4 and IPv6. IPv4 addresses are the most widely used and consist of four sets of numbers separated by periods (e.g., 192.168.0.1). These addresses have a limited range and are becoming scarce due to the rapid expansion of internet-connected devices. On the other hand, IPv6 addresses are designed to provide a much larger pool of unique identifiers. They feature an alphanumeric format and are separated by colons (e.g., 2001:0db8:85a3:0000:0000:8a2e:0370:7334).
IP addresses are vital for establishing connections in the digital world. When you visit a website, send an email, or stream a video, your device sends data packets containing your IP address to the destination server. This allows the server to route the data back to your device, ensuring a seamless communication process.
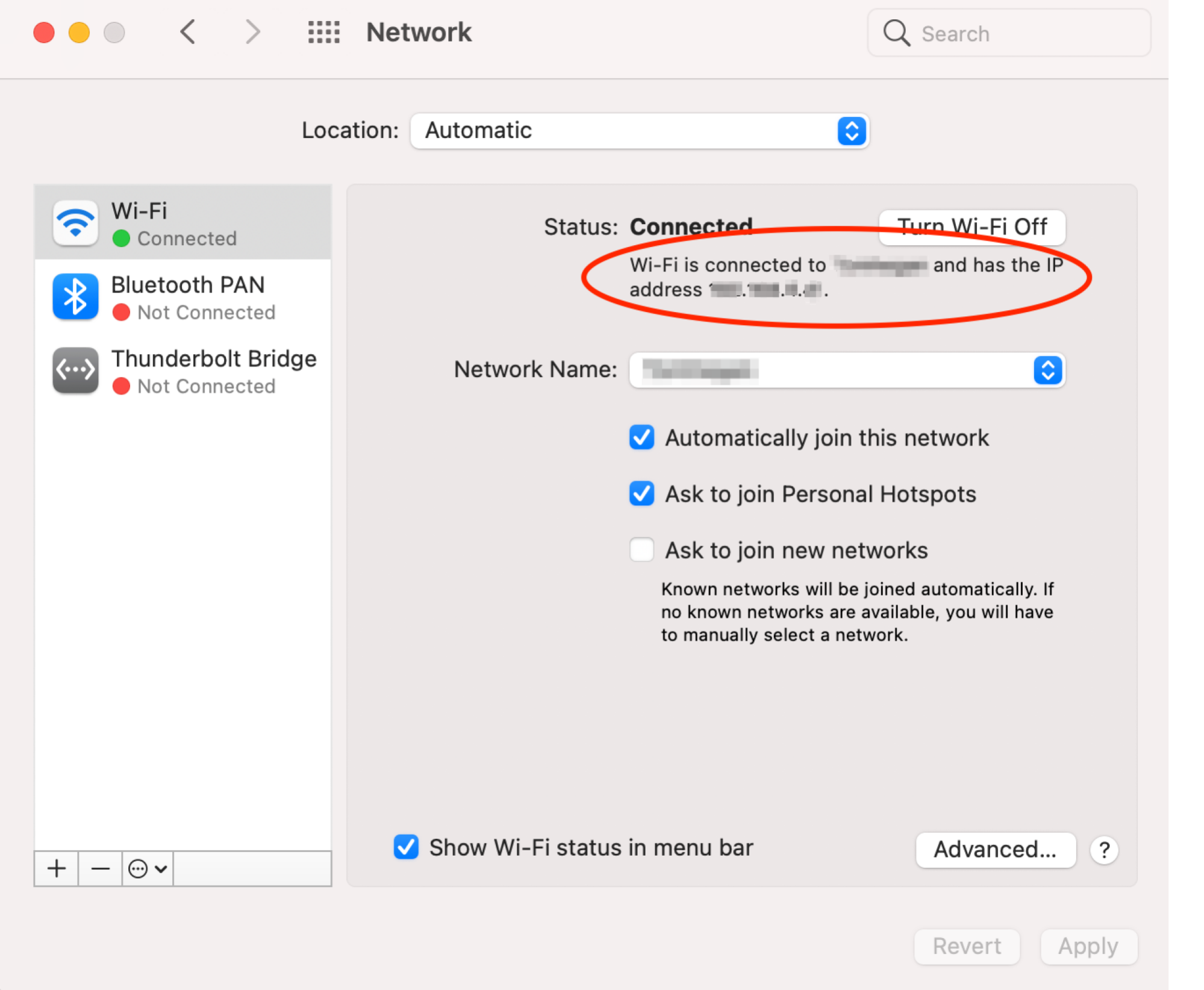
To locate your IP address, you can easily check your device’s network settings or use online IP lookup tools. In most cases, your IP address is assigned dynamically by your Internet Service Provider (ISP) each time you connect to the internet. However, there are instances where you may have a static IP address, which remains consistent every time you connect.
It’s important to understand that an IP address alone cannot reveal your exact physical location. It can provide a general idea of your geographical area, usually as narrow as your city or region, but not street-level accuracy. This limitation arises because IP addresses are associated with the registered location of the Internet Service Provider rather than the specific device or individual using it.
Now that we have established the basics of IP addresses, let’s move on to exploring how they can be used to identify location and gather limited user information.
Identifying Location
One of the common uses of an IP address is to identify the general location of the user. By analyzing the IP address, it is possible to determine the country, region, and sometimes even the city from where a device is connecting to the internet.
This information can be valuable in various scenarios. For example, it can help website owners deliver localized content, tailor advertisements based on location, or analyze traffic patterns specific to different regions. Additionally, businesses can use location data to understand their target audience better and make informed decisions when expanding their reach.
Several online tools and databases are available that can determine the geographical location associated with an IP address. These tools use a combination of IP geolocation databases, ISP data, and other relevant information to pinpoint the approximate location of the IP address.
However, it’s important to remember that IP-based geolocation is not always accurate or precise. When using IP address geolocation, there can be variations and discrepancies due to factors such as virtual private networks (VPNs), proxy servers, and mobile networks.
Proxy servers and VPNs can mask the true IP address and make it appear as if the user is connecting from a different location. This can result in misleading geolocation data. Similarly, mobile networks can present challenges in accurately locating devices due to IP address assignments that can change dynamically as users move between cell towers.
Furthermore, relying solely on IP geolocation to identify an individual’s exact physical address or specific details about their whereabouts is not feasible. IP addresses are associated with Internet Service Providers and network infrastructure, not with individuals or devices themselves.
It’s worth noting that IP geolocation should always be used responsibly and with respect for privacy. Collecting and using location data should adhere to applicable laws and regulations, including obtaining proper user consent.
In the next section, we will explore whether it is possible to obtain personal information based on an IP address and discuss the legal and ethical considerations involved.
Obtaining User Information
While an IP address can provide some insights into the geographical location of a user, obtaining personal information based solely on the IP address is much more challenging. In most cases, it is not possible to directly gather detailed and identifiable information about an individual using their IP address alone.
The reason for this limitation is that IP addresses are assigned to Internet Service Providers (ISPs) and not directly to individual users. Thus, only the ISP has access to the personal information associated with a specific IP address. Obtaining this information requires legal processes, such as subpoenas or court orders, which are typically reserved for law enforcement agencies or other authorized entities.
Additionally, privacy laws and regulations, such as the General Data Protection Regulation (GDPR) in the European Union, govern the collection, storage, and use of personal data. These laws prioritize an individual’s right to privacy and require explicit consent for the processing of personal information.
While it is not feasible to directly obtain personal information from an IP address, other methods can be used in combination to gather more data. For example, website analytics tools can track user behavior, such as click patterns and browsing habits, which can provide insights into user preferences and interests. These tools often rely on cookies and other tracking mechanisms rather than IP addresses alone.
Moreover, if a user voluntarily provides personal information on a website, such as filling out a form or creating an account, that information can be associated with their IP address. However, it is crucial for websites and businesses to follow data protection guidelines and ensure transparent disclosure of how the personal information will be used, stored, and shared.
In summary, while obtaining personal information directly from an IP address is challenging, it is always important to prioritize privacy and comply with applicable laws and regulations. User consent and transparency are key elements in any data collection process, and businesses should implement secure and ethical practices to protect user information.
Next, we will discuss the importance of reporting abuse related to IP addresses and internet-related misconduct.
Reporting Abuse
Reporting abuse is a crucial step in maintaining a safe and secure online environment. When it comes to IP addresses, reporting abuse refers to notifying the appropriate authorities or service providers about any malicious or harmful activities associated with a specific IP address.
Abuse can take various forms, including hacking attempts, spamming, phishing, cyberbullying, or any other illegal or unethical activities conducted over the internet. If you encounter such abuse or suspect that someone’s IP address is involved in malicious activities, it is important to take immediate action.
First and foremost, if you believe a crime has been committed, it is essential to contact your local law enforcement agency and provide them with all relevant information. They have the expertise and authority to investigate and address any criminal activity associated with an IP address.
Additionally, you can report abuse to the Internet Service Provider (ISP) responsible for the IP address in question. ISPs have provisions in place to deal with abuse complaints, and they can take appropriate actions against the offending users. Most ISPs have dedicated abuse departments or online forms where you can submit your complaint along with supporting evidence.
When reporting abuse, it is crucial to provide as much information as possible. This includes details such as the date and time of the incident, the specific nature of the abuse, any relevant IP addresses or URLs involved, and any evidence you have collected. The more specific and detailed your report, the better equipped authorities and ISPs will be to investigate and take action.
Remember, reporting abuse not only helps protect yourself and others from harm, but it also contributes to the overall security of the internet community. By reporting abusive activities related to IP addresses, you play an active role in creating a safer online environment for everyone.
Next, we will delve into the topic of protecting your own IP address and ensuring online privacy.
Protection and Privacy
Protecting your IP address and maintaining online privacy is essential to safeguarding your personal information and ensuring a secure digital presence. While it may not be possible to completely hide your IP address, there are steps you can take to enhance your online privacy:
1. Use Virtual Private Networks (VPNs): VPNs create a secure and encrypted connection between your device and the internet, masking your IP address and adding an extra layer of privacy. By connecting to a VPN server, you can route your internet traffic through a different IP address, making it more difficult for others to track your online activities.
2. Enable Firewall Protection: Activate the built-in firewall on your device or install a reputable firewall software. Firewalls help monitor and control incoming and outgoing internet traffic, protecting your device from unauthorized access and potential threats.
3. Regularly Update Software and Use Strong Passwords: Keeping your operating system, web browsers, and other software up to date is crucial for maintaining security. Additionally, using complex and unique passwords for your accounts can protect your personal information from unauthorized access.
4. Be Cautious with Public Wi-Fi: When using public Wi-Fi networks, exercise caution as they may not be secure. Avoid accessing sensitive information or making online transactions on public Wi-Fi, as your data can be intercepted by hackers.
5. Utilize Privacy Tools and Browser Extensions: Install reputable privacy-focused browser extensions that offer features like ad-blockers, anti-tracking, and HTTPS encryption. These tools can help enhance your browsing privacy and protect against intrusive tracking techniques.
It’s important to be aware that even with these precautions, there are still risks associated with online privacy. Websites and online services may collect and store your data, and government surveillance programs can also pose privacy concerns.
If maintaining privacy is a top priority for you, consider using privacy-focused search engines and email providers, as well as being cautious about the data you share online and the permissions you grant to apps and services.
By taking steps to protect your IP address and enhance your online privacy, you can have greater control over your personal information and mitigate the risks of unauthorized access and misuse.
In the next section, we will explore the concept of IP address blocking and its uses.
IP Address Blocking
IP address blocking is a technique used to restrict access to a website, server, or online service for specific IP addresses or ranges. It is employed as a security measure to prevent malicious activities, spamming, hacking attempts, or unwanted traffic from accessing a system or causing disruptions.
Blocking an IP address involves creating rules or configurations in network or server settings that deny incoming or outgoing connections from the specified IP addresses. This can be done at various levels, such as the server level, firewall level, or application level.
There are different scenarios where IP address blocking can be beneficial:
1. Blocking Malicious Users: If you notice suspicious activities or repeated login failures from a specific IP address, you can block that IP to prevent further unauthorized access attempts. This helps protect your systems and data from potential breaches.
2. Preventing DDoS Attacks: Distributed Denial of Service (DDoS) attacks involve overwhelming a server with a flood of traffic from multiple IP addresses simultaneously. By blocking the IP addresses responsible for initiating such attacks, you can mitigate the impact and ensure the stability of your online services.
3. Reducing Spam and Unwanted Traffic: If a website or server is constantly bombarded with spam messages or unwanted traffic from specific IP addresses, blocking those IPs can help reduce the nuisance and improve the overall user experience.
4. Restricting Access to Certain Regions: In some cases, website owners may wish to limit access to specific geographic regions or comply with regional restrictions or regulations. By blocking IP addresses associated with those regions, they can control who can access their content or services.
However, it’s important to exercise caution when implementing IP address blocking. Mistakes or misconfigurations can inadvertently block legitimate users or IP addresses, leading to unintended consequences. It’s recommended to review and analyze the data before deciding to block an IP address to ensure the action is justified and necessary.
Additionally, sophisticated users can employ techniques such as proxy servers or VPNs to bypass IP address blocking. Therefore, it’s crucial to combine IP blocking with other security measures, such as strong authentication mechanisms and regular security assessments, to maintain a robust defense against potential threats.
Next, we will discuss the concept of faking or spoofing an IP address and its implications.
Faking IP Address
Faking or spoofing an IP address refers to the act of manipulating the IP address field in network packets to make it appear as if the communication is originating from a different IP address than the actual source. This technique is often used for various purposes, including anonymity, bypassing restrictions, or carrying out malicious activities.
There are legitimate reasons why someone might want to fake their IP address. For example, journalists, activists, or individuals living under oppressive regimes may use methods like Virtual Private Networks (VPNs) or proxy servers to protect their identities and access information without being traced. By disguising their IP address, they can bypass censorship or surveillance.
However, it’s crucial to recognize that faking an IP address can also be employed for malicious intentions. Cybercriminals may use IP spoofing techniques to launch distributed denial of service (DDoS) attacks, disguise their identity while committing crimes, or gain unauthorized access to systems.
IP spoofing is an advanced technique that requires a certain level of expertise and control over network infrastructure. It often involves crafting network packets with manipulated IP headers, making it difficult to trace the origin of the communication accurately.
While the ability to fake an IP address presents challenges for network administrators and security professionals, several countermeasures can help mitigate the risks:
1. Network Monitoring: Constant monitoring of network traffic can help detect anomalies and patterns associated with IP spoofing attacks. Intrusion detection systems (IDS) and Intrusion Prevention Systems (IPS) can aid in detecting and preventing such malicious activities.
2. Filtering and Authentication: Implementing strict filtering rules at the network perimeter can help prevent spoofed packets from entering or leaving the network. Network administrators can also enforce the use of strong authentication mechanisms to authenticate users and devices, ensuring that only authorized entities can access the network.
3. Implementing Anti-Spoofing Measures: Network providers and ISPs can implement measures such as ingress and egress filtering, which verify the authenticity of packet headers and prevent unauthorized traffic from entering or leaving their networks.
4. Traffic Analysis: Analyzing network traffic patterns and identifying abnormal activity can help identify potential IP spoofing attempts. Behavior-based anomaly detection systems can detect unusual patterns and flag suspicious traffic for further investigation.
It’s important to note that while countermeasures can help minimize the risks associated with IP spoofing, complete prevention is challenging. Sophisticated attackers may find ways to bypass security measures, highlighting the importance of a multi-layered security approach and continuous monitoring to identify and respond to potential threats.
In the next section, we will summarize the key points discussed throughout this article.
Conclusion
In this article, we have explored the possibilities and limitations of working with someone’s IP address. We started by understanding the basics of IP addresses and how they serve as unique identifiers for devices connected to the internet. We then discussed how IP addresses can be used to identify the general location of a user, emphasizing that it has its limitations in terms of accuracy and privacy.
Furthermore, we examined the challenges of obtaining personal information solely based on an IP address, emphasizing the importance of respecting privacy laws and obtaining proper consent. We also highlighted the significance of reporting abuse associated with IP addresses to maintain a safe online environment and protect against malicious activities.
We then discussed the importance of protecting our own IP addresses and online privacy by utilizing tools such as VPNs, enabling firewalls, and regularly updating software. We explored the concept of IP address blocking as a security measure to prevent unauthorized access and the need for cautious implementation to avoid unintended consequences.
Lastly, we explored the concept of faking or spoofing IP addresses. While it can be used for legitimate reasons such as maintaining anonymity, we highlighted the potential risks and the need for network monitoring, filtering, and authentication measures to detect and prevent IP spoofing attacks.
Understanding and working with IP addresses requires a balance between utilizing their functionalities for legitimate purposes and respecting privacy and security. It is important to stay informed about the latest trends and best practices in managing IP addresses to ensure a safe and secure online experience for everyone.
By understanding the intricacies of IP addresses, we can navigate the digital landscape with confidence and make informed decisions regarding their use, protection, and privacy.