Introduction
Welcome to the fascinating world of P2P ports! In today’s technologically advanced era, where the Internet plays a significant role in our daily lives, it’s important to understand the basic concepts behind Peer-to-Peer (P2P) communication. Whether you’re a seasoned tech enthusiast or just starting to explore the intricacies of networking, this article will provide you with a comprehensive overview of P2P ports and their significance.
Before delving into the intricacies of P2P ports, let’s briefly examine the term “P2P” itself. P2P, or Peer-to-Peer, refers to a decentralized network architecture where individual devices, known as peers, can directly communicate with each other without the need for a central server. This form of communication differs from the traditional client-server model, where a central server acts as a mediator between devices.
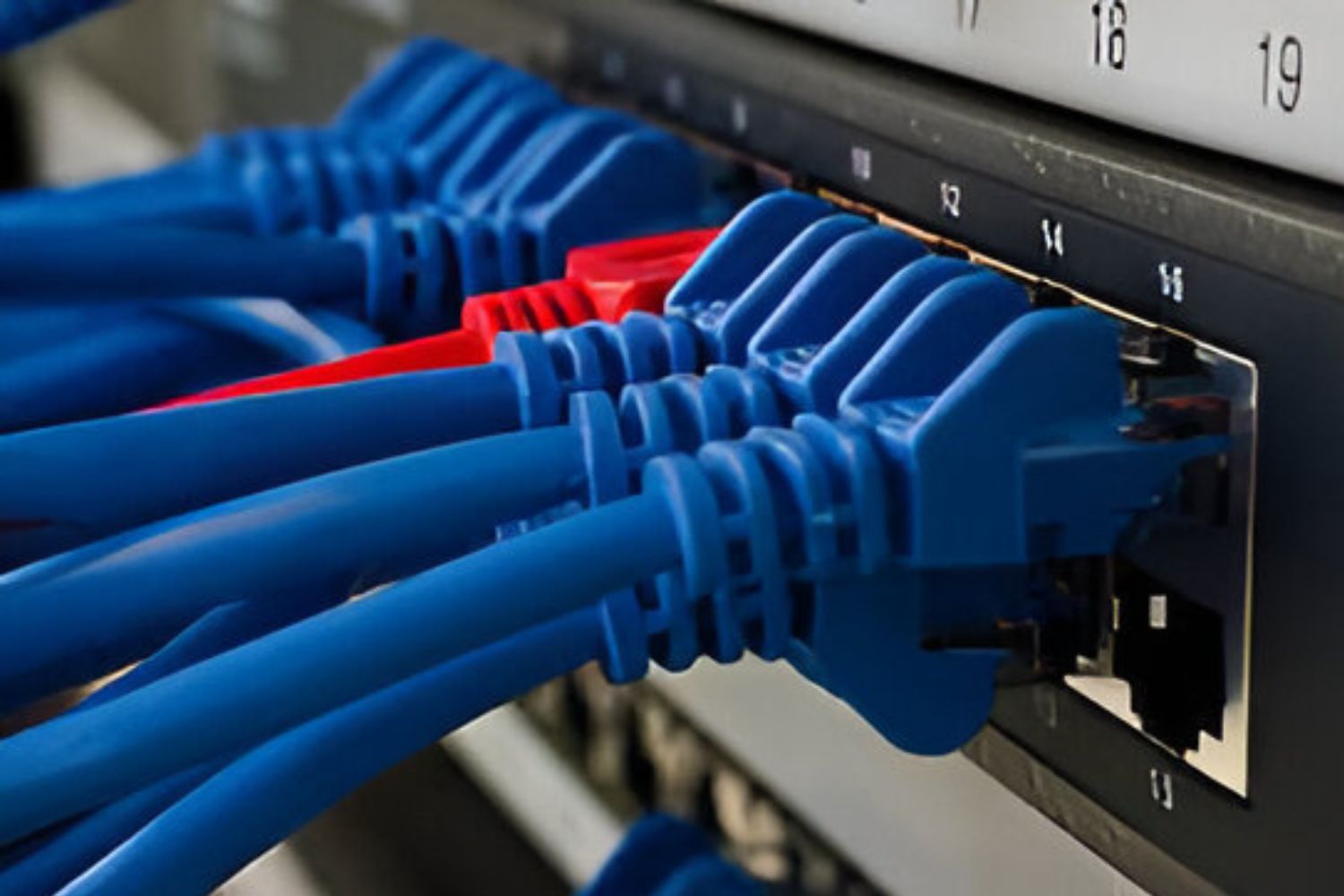
A P2P port, also known as a Peer-to-Peer port or simply a port, is an endpoint mechanism used to identify and distinguish different types of network traffic on a device. It acts as a gateway, allowing data to flow in and out of a device. Think of a P2P port as a virtual doorway that enables communication between peers in a P2P network.
Without P2P ports, devices would not be able to establish direct connections with each other. These ports serve as a vital component in P2P applications, enabling the exchange of data, files, and other resources between connected devices. Additionally, P2P ports facilitate the efficient distribution of workloads and resources among peers, leading to improved network performance and scalability.
Throughout this article, we will delve deeper into the workings and significance of P2P ports. We will explore how they function, common uses of P2P ports, the concept of P2P port numbers, and the steps involved in opening or closing P2P ports. Furthermore, we will discuss important security considerations when dealing with P2P ports to ensure a safe and protected networking environment.
So, let’s embark on this exciting journey into the world of P2P ports, where we’ll uncover the key elements that make P2P communication possible and learn how to harness their power to optimize our networking experiences.
What is a P2P Port?
A P2P port, or Peer-to-Peer port, is a crucial element in peer-to-peer networking that facilitates direct communication between devices. It serves as a virtual gateway through which data can flow in and out of a device, enabling peers to establish connections and exchange information.
When two devices in a P2P network want to communicate, they rely on P2P ports to establish a direct connection. Each device in the network is assigned a specific P2P port number, allowing incoming and outgoing data packets to be directed to the intended device.
Imagine a P2P port as a designated entrance or exit point for data packets within a device. Just as a physical doorway allows individuals to enter or leave a room, a P2P port enables data to enter or exit a device, ensuring seamless communication between peers.
These ports are essential for P2P applications, which rely on direct device-to-device communication to function effectively. By circumventing the need for a central server, P2P applications can distribute workloads and resources more efficiently, leading to improved scalability and network performance.
Furthermore, P2P ports play a crucial role in enabling file sharing, streaming, voice and video calling, and other collaborative activities in P2P networks. Each P2P application typically requires specific ports to be open or forwarded to allow incoming connections from other peers.
It’s important to note that P2P ports are not limited to a specific range or set of numbers. Instead, they utilize the same port numbers as other types of network traffic, such as web browsing or email. This is because P2P ports do not represent a distinct and separate kind of port, but rather they are associated with the communication protocols used by P2P applications.
In summary, a P2P port acts as a gateway that facilitates direct communication between devices in a P2P network. It allows data packets to enter or exit a device, enabling peers to exchange information, collaborate, and share resources. Understanding the role and significance of P2P ports is crucial for optimizing P2P networking experiences and harnessing the power of peer-to-peer communication.
How Does a P2P Port Work?
Understanding how a P2P port works is key to comprehending the intricate communication processes that take place within a peer-to-peer network. P2P ports operate based on a combination of protocols, addressing schemes, and network configurations.
When a device initiates a connection with another device in a P2P network, it must utilize a specific P2P port number associated with the desired communication protocol. For example, a file-sharing application might use port 6881 for BitTorrent protocol connections.
Once the P2P port number is known, the device attempts to establish a direct connection with the targeted peer. This involves initiating a handshake process, where the devices exchange control information to establish a secure and reliable connection.
If the connection is successful, data packets can then flow between the devices through the established P2P port. The devices can exchange files, messages, or any other type of information required for the intended communication.
It is important to note that P2P ports can be either TCP (Transmission Control Protocol) or UDP (User Datagram Protocol) ports. TCP ports provide reliable, ordered, and error-checked delivery of data packets, making them suitable for applications such as file sharing or video streaming that require accuracy and flow control.
On the other hand, UDP ports offer a faster transmission rate but do not guarantee the reliability or order of data packets. This makes them suitable for applications such as real-time voice or video communication, where a slight delay in data is preferable over the potential disruption caused by retransmissions.
In some cases, P2P applications may require incoming connections to be established through Network Address Translation (NAT) devices, such as routers or firewalls. These devices translate the device’s private IP address to a public IP address, allowing external peers to establish connections.
However, NAT devices can pose challenges for P2P connectivity due to their inherent security features, which limit incoming connections. P2P applications often employ techniques such as port forwarding or UPnP (Universal Plug and Play) to bypass NAT restrictions and establish direct connections between peers.
In summary, P2P ports work by utilizing specific port numbers associated with communication protocols. Devices in a P2P network establish direct connections through these ports, facilitated by protocols such as TCP or UDP. P2P ports enable the exchange of data packets, allowing peers to share files, collaborate, and engage in various forms of communication. Overcoming NAT restrictions and implementing port forwarding techniques are essential for achieving optimal P2P connectivity.
Common Uses of P2P Ports
P2P ports play a vital role in enabling a wide range of applications and services in peer-to-peer networks. From file sharing to real-time communication, P2P ports facilitate seamless connectivity and data exchange between devices. Let’s explore some of the common uses of P2P ports in more detail:
- File Sharing: One of the primary uses of P2P ports is for file sharing applications. These ports allow peers to exchange files directly without relying on a central server. Popular P2P file sharing protocols, such as BitTorrent, utilize specific P2P port numbers to establish connections and enable efficient distribution of files among peers.
- Streaming Services: P2P ports also enable streaming services that rely on peer-to-peer networks. With the help of P2P ports, peers can share parts of the streaming content with each other, reducing the load on centralized servers and improving streaming efficiency. This allows for faster and more reliable media streaming experiences.
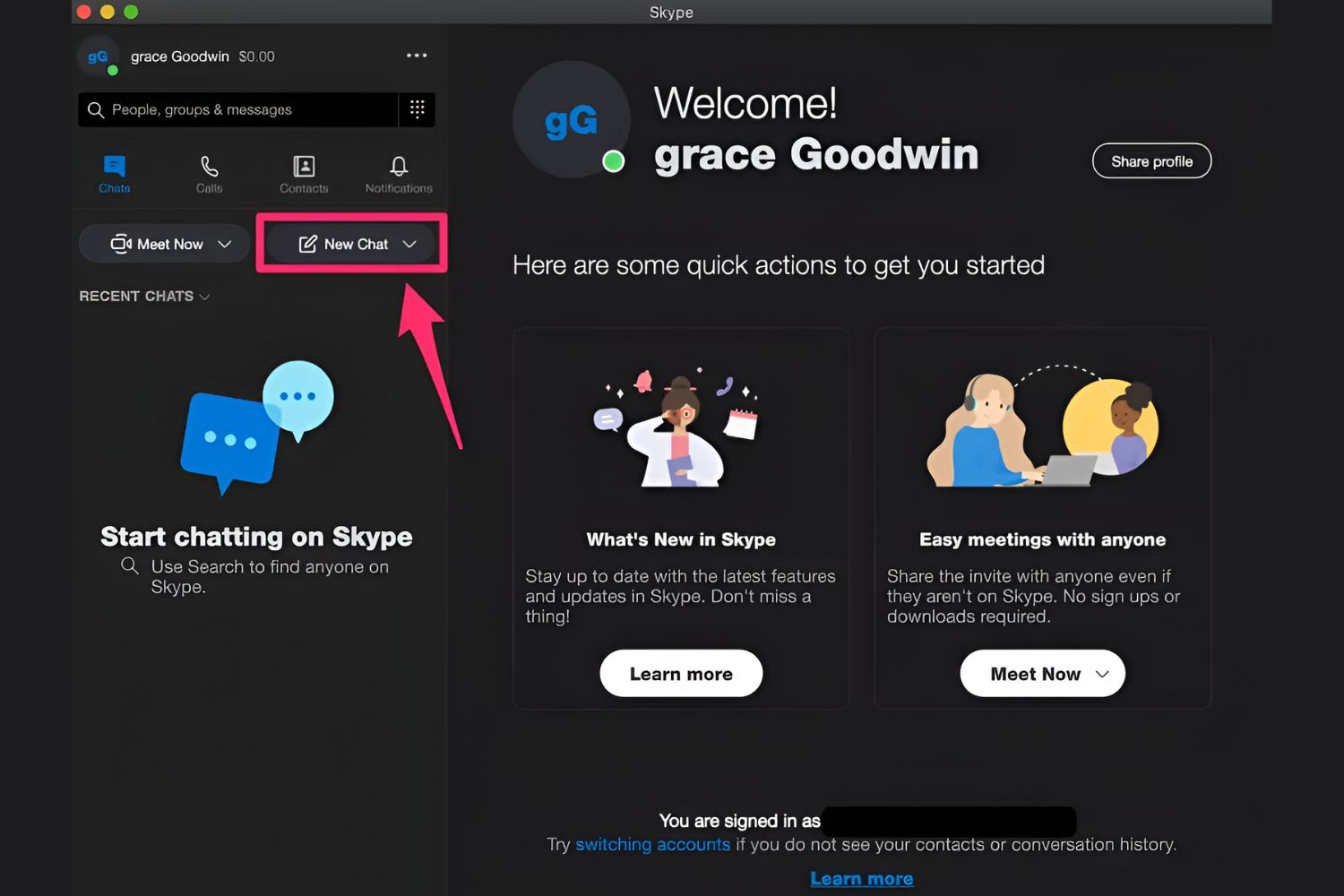
- Voice and Video Communication: P2P ports are crucial for real-time voice and video communication applications. Peer-to-peer communication enables direct connections between devices, facilitating clear and uninterrupted communication. By utilizing P2P ports, these applications can establish reliable and low-latency connections, enhancing the quality of voice and video calls.
- Collaborative Applications: P2P ports are instrumental in enabling collaboration among peers in real-time applications. Whether it’s co-editing documents, sharing project updates, or whiteboarding sessions, P2P ports allow for efficient and secure data exchange between connected devices. This enhances productivity and fosters seamless teamwork regardless of geographical locations.
- Multiplayer Gaming: P2P ports are widely used in multiplayer gaming applications. They enable direct communication between game clients, allowing players to engage in real-time gaming experiences. By utilizing P2P ports, multiplayer games can optimize network performance and minimize latency, enhancing the overall gaming experience.
These are just a few examples of the common uses of P2P ports. However, the versatility and flexibility of P2P port usage extend far beyond these applications. P2P ports open up a world of possibilities for decentralized, peer-to-peer communication, enabling various services and applications to function efficiently and seamlessly.
Understanding P2P Port Numbers
P2P port numbers are a crucial component of peer-to-peer communication as they facilitate the identification and differentiation of network traffic within a P2P network. Each P2P application or protocol typically uses specific port numbers to establish connections and facilitate data exchange.
Port numbers are 16-bit unsigned integers, meaning they range from 0 to 65535. They are divided into three ranges: well-known ports (0-1023), registered ports (1024-49151), and dynamic or private ports (49152-65535).
While well-known ports are reserved for standard protocols such as HTTP (port 80) or FTP (port 21), P2P applications usually utilize higher-numbered ports within the registered or dynamic port ranges.
It’s important to note that P2P port numbers are not universal and can vary depending on the specific P2P application or protocol being used. For example, BitTorrent commonly uses ports in the range of 6881-6889, while the eDonkey protocol uses port 4662.
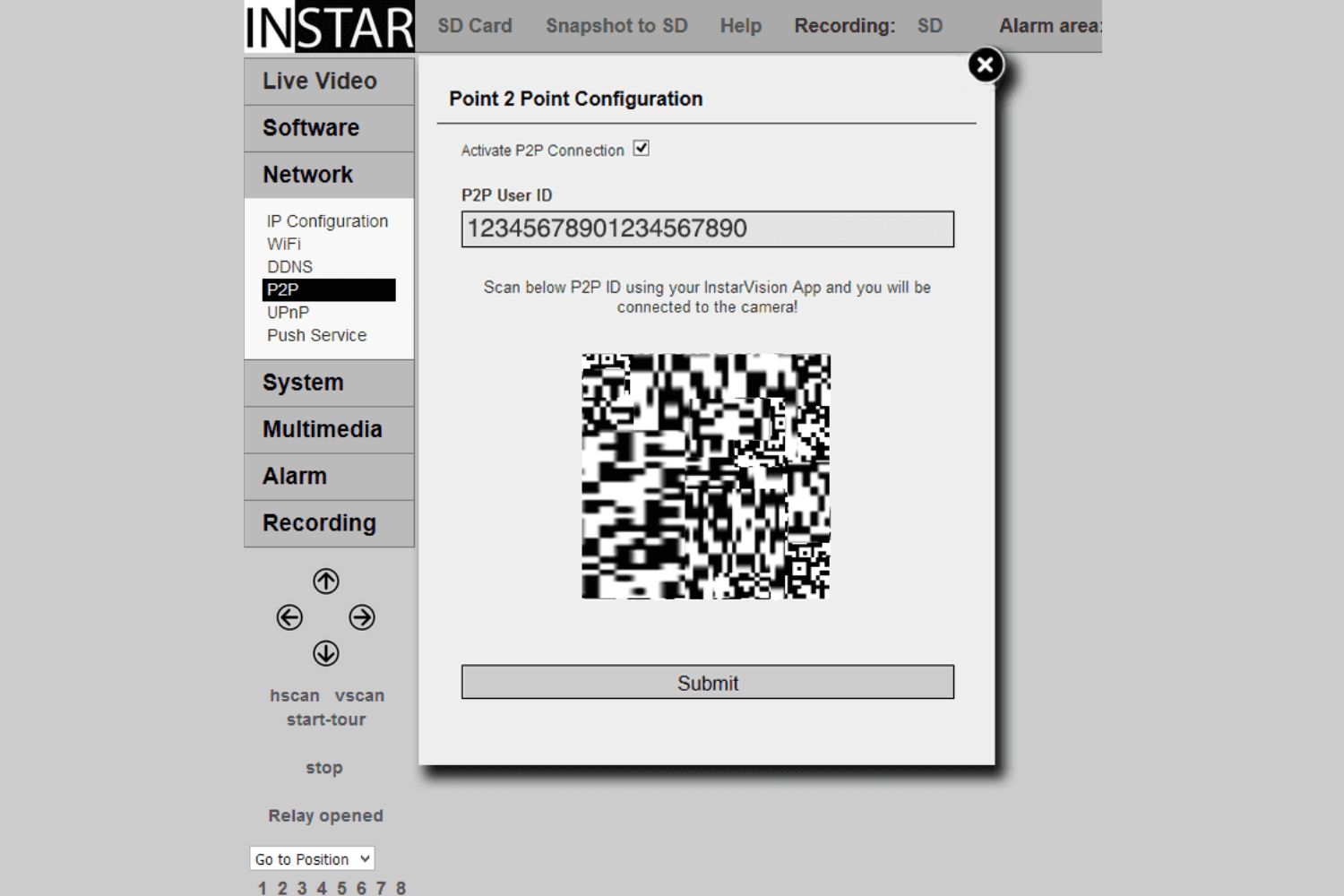
When a device in a P2P network initiates a connection, it specifies both the IP address and the port number of the intended peer. This information allows the devices to establish a direct connection through the respective P2P ports.
Having distinct port numbers for each P2P application or protocol enables devices to handle different types of network traffic concurrently. For instance, a device can simultaneously host a file-sharing application using one port number and engage in voice communication through another port number.
In scenarios where multiple devices within a network host the same P2P application, each device must use a unique port number. This allows for the proper routing of data packets to the correct device. It’s important to configure port forwarding or UPnP settings on routers or firewalls to ensure that incoming connections on specific P2P port numbers reach the correct device in such cases.
Understanding P2P port numbers is essential for effective P2P networking. It allows users to identify the ports used by specific applications or protocols, configure network settings accordingly, and optimize connectivity and data exchange within a peer-to-peer network.
How to Open or Close P2P Ports
Opening or closing P2P ports is an important task to ensure seamless connectivity and efficient data exchange within a peer-to-peer network. The process involves configuring network settings, such as port forwarding or firewall rules, to allow or restrict incoming connections on specific P2P port numbers. Here are some steps to open or close P2P ports:
- Identify the P2P Port Number: First, determine the specific P2P port number that needs to be opened or closed. This information is typically provided by the P2P application or protocol documentation.
- Access the Router Configuration: Enter the router’s IP address into a web browser to access the router configuration interface. The IP address is often printed on the router itself or can be found in the instruction manual.
- Locate the Port Forwarding or Virtual Server Settings: Look for the port forwarding or virtual server settings in the router’s configuration interface. This location may vary depending on the router model, but it is typically found under the “Advanced,” “Security,” or “Firewall” sections.
- Add a New Port Forwarding Rule: To open a P2P port, create a new port forwarding rule by specifying the P2P port number, the local IP address of the device running the P2P application, and select the appropriate protocol (TCP or UDP). Save or apply the changes to activate the new rule.
- Configure Firewall Settings: If there is a firewall enabled on the device running the P2P application, ensure that it allows incoming traffic on the specified P2P port. Add an exception or rule to allow the specific port number, keeping in mind any security considerations.
- Test the P2P Port: Verify that the P2P port is now open by using online port checker tools. These tools scan the specified port number to check its accessibility from the internet. If the port is open, it should show as “Open” or “Accessible.”
- Closing P2P Ports: To close a P2P port, simply remove or disable the port forwarding rule associated with the specific port number in the router’s configuration interface. Additionally, ensure that the firewall settings on the device running the P2P application do not allow incoming connections on the closed port.
It’s important to note that the exact steps for opening or closing P2P ports may vary depending on the router model and the specific P2P application or protocol being used. It’s advisable to consult the router’s documentation or seek technical support if needed.
By successfully opening or closing P2P ports, users can optimize their peer-to-peer networking experience, ensuring effective communication, faster data exchange, and improved connectivity among peers.
Security Considerations for P2P Ports
While P2P ports are essential for enabling seamless connectivity and data exchange within a peer-to-peer network, it’s important to consider certain security aspects to protect your network and devices. Here are some key security considerations to keep in mind when dealing with P2P ports:
- Firewall Configuration: Properly configuring your firewall is crucial to prevent unauthorized access through open P2P ports. Ensure that only necessary P2P ports are open and limit access to trusted IP addresses or networks.
- Regularly Update P2P Applications: To mitigate potential security vulnerabilities, keep your P2P applications up to date. Software updates often include security patches and bug fixes, providing better protection against potential threats.
- Choose Strong Passwords: Use strong, unique passwords for your P2P applications and router admin interface. Weak passwords can make it easier for attackers to gain unauthorized access to your devices or network.
- Beware of Malicious P2P Networks: Be cautious when joining or downloading from unfamiliar or untrusted P2P networks. Malicious files or applications shared through these networks can expose your devices to security risks, such as malware or viruses.
- Monitor Network Traffic: Regularly monitor your network traffic for any suspicious activity. Unusual network behavior or excessive traffic on P2P ports could indicate a potential security breach or the presence of malicious actors.
- Enable Encryption: Whenever possible, enable encryption for your P2P connections. Encryption adds an extra layer of security, ensuring that data exchanged between peers remains confidential and protected from eavesdropping.
- Disable Universal Plug and Play (UPnP) if Not Needed: UPnP allows devices to automatically configure network settings, but it can also be exploited by attackers. If not required, disable UPnP to reduce the risk of potential vulnerabilities in your network.
- Regularly Backup Data: Create regular backups of your important data stored on devices connected to your peer-to-peer network. In the event of a security incident or system failure, having backups ensures you can restore your data and minimize potential losses.
- Educate Yourself and Users: Stay informed about the latest security best practices and educate users on the potential risks associated with P2P networks. Encourage them to be vigilant and report any suspicious activity to maintain a secure networking environment.
By considering these security aspects and implementing appropriate measures, you can mitigate potential risks and protect your devices and network while leveraging the benefits of peer-to-peer communication through P2P ports.
Conclusion
In conclusion, P2P ports are vital components of peer-to-peer networking that enable direct communication and data exchange between devices. Understanding the workings of P2P ports is essential for optimizing connectivity and harnessing the power of peer-to-peer communication.
Throughout this article, we have explored various aspects of P2P ports, including their definition, functionality, common uses, port numbers, and security considerations.
We have learned that P2P ports act as gateways for data to flow in and out of devices, facilitating direct communication between peers in a P2P network. These ports enable file sharing, streaming services, voice and video communication, collaborative applications, and multiplayer gaming, among other applications.
P2P port numbers are used to identify and differentiate network traffic within a P2P network. Each P2P application or protocol typically utilizes specific port numbers for establishing connections and facilitating efficient data exchange.
When working with P2P ports, it is crucial to consider security aspects such as firewall configuration, software updates, strong passwords, cautiousness with unknown P2P networks, network traffic monitoring, encryption, and regular backups.
By following these security considerations and understanding how to open or close P2P ports, users can enhance their network security and protect their devices from potential threats.
In conclusion, P2P ports empower peer-to-peer networking, enabling seamless communication, efficient data exchange, and collaborative experiences. By leveraging the power of P2P ports, users can optimize their networking capabilities and embrace the innovative possibilities of decentralized communication.