Introduction
Welcome to the world of P2P ID, a revolutionary concept in identity verification that is transforming how we establish and authenticate our digital identities. In today’s interconnected and digitized world, where personal data is increasingly vulnerable to cyber threats, the need for secure and reliable identity verification mechanisms has never been more critical. P2P ID, also known as Peer-to-Peer ID, is emerging as a promising solution to this pressing issue.
P2P ID is a decentralized identity verification system that allows individuals to take control of their own identities without relying on traditional centralized authorities such as governments or financial institutions. It leverages the power of blockchain technology, cryptography, and peer consensus to create a transparent, tamper-proof, and user-centric identity verification process.
With P2P ID, individuals can securely share their personal information and prove their identity to counterparties in online transactions, without compromising their privacy or relying on third-party intermediaries. By eliminating the need for centralized authorities, P2P ID offers a more efficient, cost-effective, and inclusive alternative for identity verification, addressing some of the key challenges faced by current systems.
In this article, we will delve deeper into the concept of P2P ID, exploring its definition, history, functionality, benefits, challenges, and real-world applications. By the end, you will have a comprehensive understanding of how P2P ID is revolutionizing identity verification and the potential it holds for a more secure and user-centric digital future.
Definition of P2P ID
P2P ID, also known as Peer-to-Peer ID, refers to a decentralized identity verification system that enables individuals to have control over their digital identities without relying on centralized authorities. It is built on the principles of blockchain technology, cryptography, and peer consensus, creating a transparent and tamper-proof process for verifying and sharing personal information securely.
Unlike traditional identity verification systems that rely on central authorities like governments or financial institutions, P2P ID empowers individuals to manage their own identities. It allows users to create and store their identity information in a secure and encrypted manner, eliminating the need for intermediaries and reducing the risk of data breaches or identity theft.
At its core, P2P ID utilizes blockchain technology to create a distributed ledger that records and verifies identity-related transactions. Each user in the network has their own unique digital identity represented in the form of a cryptographic key. These keys are used to verify the authenticity and integrity of identity-related transactions, ensuring that only authorized parties can access and verify the information.
To establish trust and consensus in the P2P ID system, participants in the network validate and confirm each other’s identities. This decentralized approach allows for greater transparency and minimizes the risk of fraud or manipulation. Additionally, the use of strong cryptographic algorithms ensures that personal information remains encrypted and secure.
P2P ID is designed to be an inclusive and interoperable system, enabling individuals to seamlessly share their verified identities across different platforms and services. This cross-platform compatibility makes it easier for users to establish trust and conduct secure transactions in various online settings.
Overall, P2P ID represents a paradigm shift in how we approach identity verification. By decentralizing the process and giving individuals greater control over their personal data, P2P ID offers a more secure, efficient, and user-centric solution for managing digital identities in the digital age.
History of P2P ID
The concept of P2P ID traces its roots back to the emergence of blockchain technology and the desire for a more secure and decentralized approach to identity verification. The concept gained traction in the early 2010s when the potential of blockchain for secure identity management started to be explored.
One of the key milestones in the history of P2P ID is the creation of Bitcoin, the first and most well-known cryptocurrency, in 2009. Bitcoin introduced the concept of a decentralized peer-to-peer network, where transactions are recorded on a public blockchain ledger, providing transparency and security without relying on a central authority.
Building on the principles of blockchain technology, developers recognized the potential for using this technology for identity verification. In 2014, the W3C Consortium, a leading organization that sets web standards, established the W3C Credentials Community Group. This group aimed to explore the possibilities of using blockchain and decentralized technologies for identity management.
In 2016, Sovrin Foundation was established with the goal of creating a global self-sovereign identity (SSI) network. This network would enable individuals to have control over their own identity information and securely share it as needed. The Sovrin Foundation’s work has been instrumental in advancing the development of P2P ID and shaping the broader vision of self-sovereign identity management.
As the concept of P2P ID gained traction, numerous startups and organizations began developing their own implementations and protocols. Some notable projects include uPort, Evernym, and DID (Decentralized Identifiers) by W3C. These initiatives focused on creating decentralized systems that leverage blockchain technology, cryptography, and peer consensus to enable secure and user-centric identity verification.
With the increasing concerns around privacy and data breaches, governments and regulatory bodies also started exploring the potential of P2P ID. Estonia, known for its digital innovation, introduced the concept of e-Residency in 2014, allowing non-residents to obtain a digital identity and access various government services remotely.
The history of P2P ID is still relatively short, but its potential impact is significant. As more individuals and organizations recognize the advantages of decentralized identity verification, the development and adoption of P2P ID systems continue to progress, ushering in a new era of secure and user-centric identity management in the digital age.
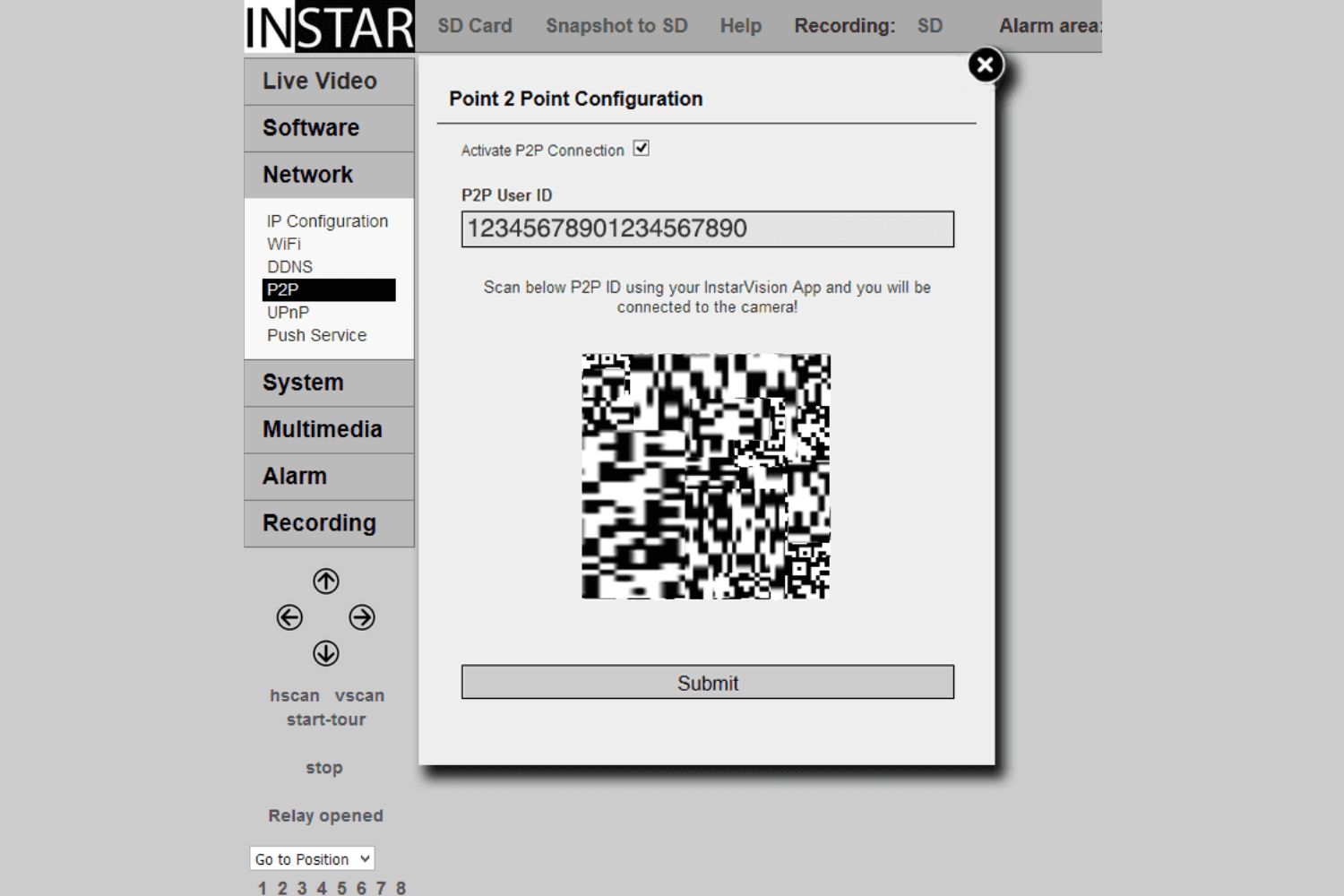
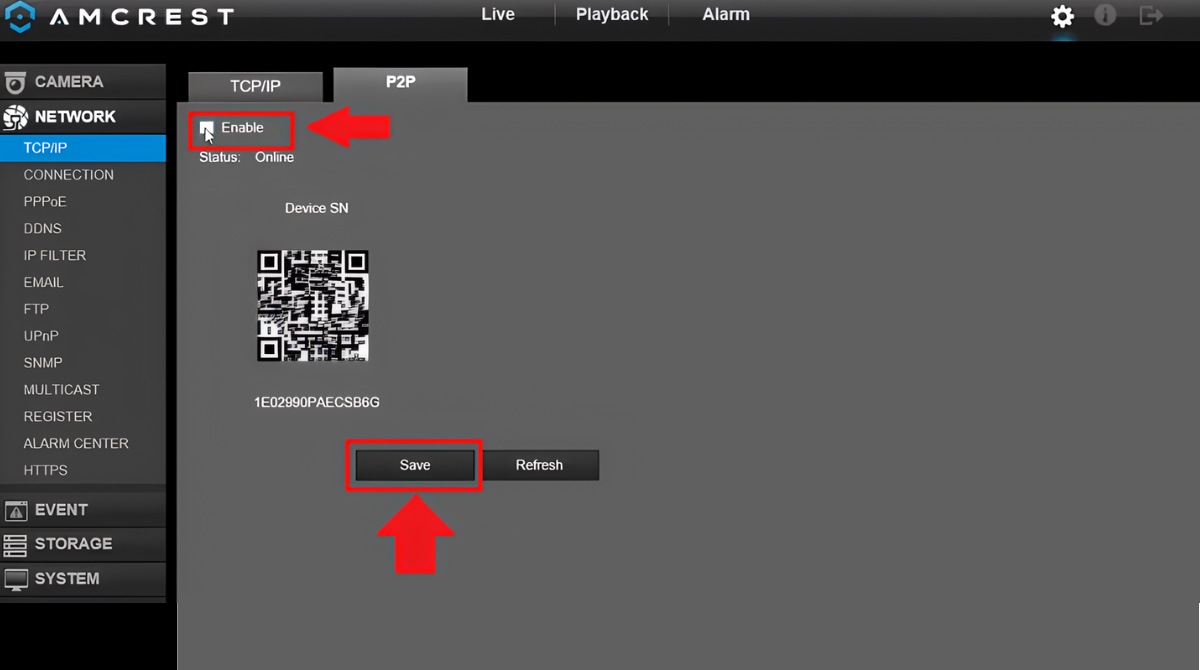
How P2P ID Works
P2P ID operates through a decentralized network, utilizing blockchain technology, cryptography, and peer consensus to verify and manage digital identities. Let’s explore the key components and steps involved in how P2P ID works:
- Identity Creation: To participate in the P2P ID network, individuals create their unique digital identities. These identities are represented by cryptographic keys derived from complex algorithms. The keys serve as a secure and private way to authenticate and verify users’ identities.
- Decentralized Network: P2P ID operates on a network of distributed nodes, where each participant maintains a copy of the blockchain ledger. This decentralization ensures that there is no single point of failure or control, enhancing security and resilience.
- Transaction Validation: When a user wants to verify their identity or share specific information, a transaction is initiated on the P2P ID network. The transaction includes the necessary details and cryptographic signatures to ensure integrity and authenticity.
- Consensus Mechanism: The P2P ID network relies on a consensus mechanism, such as proof-of-work or proof-of-stake, to validate and agree upon the authenticity of transactions. This consensus process involves network participants collectively verifying and confirming the transaction, adding it to the blockchain ledger.
- Data Encryption: Personal information shared within the P2P ID network is encrypted using robust cryptographic algorithms. This encryption ensures that the data remains secure and confidential.
- Self-Sovereign Identity: P2P ID enables individuals to maintain control over their digital identities, hence the term “self-sovereign identity”. Users have the authority to grant and revoke access to their identity information, putting them in charge of managing their personal data.
- Interoperability: P2P ID aims for interoperability, allowing users to seamlessly share their verified identities across different platforms and services. This cross-platform compatibility facilitates trust and enables secure transactions in various online environments.
By leveraging the power of blockchain, cryptography, and peer consensus, P2P ID provides a secure and efficient method for individuals to establish and manage their digital identities. With its decentralized nature, P2P ID offers a more inclusive and user-centric approach to identity verification in the digital age.
Benefits of Using P2P ID
P2P ID, a decentralized identity verification system, offers several significant benefits compared to traditional centralized approaches. Let’s explore the advantages of using P2P ID:
- Enhanced Security: P2P ID leverages robust encryption and blockchain technology to ensure the security and integrity of digital identities. With no central authority to target, the risk of data breaches and identity theft is greatly reduced.
- User Control and Privacy: P2P ID puts users in control of their digital identities, enabling them to manage and share their personal information as they see fit. Individuals can maintain their privacy by only disclosing necessary details for specific transactions, minimizing the risk of identity fraud.
- Elimination of Third-Party Intermediaries: By removing the need for centralized authorities, P2P ID eliminates reliance on third-party intermediaries for identity verification. This streamlines the process, reduces costs, and ensures faster and more efficient transactions.
- Inclusive Access: P2P ID promotes inclusivity by enabling individuals to access and participate in digital services without traditional identity credentials. It allows marginalized populations, such as the unbanked or refugees, to establish their digital identities and access vital services.
- Interoperability: P2P ID aims for cross-platform compatibility, allowing individuals to seamlessly share their verified identities across different platforms and services. This interoperability enhances trust and facilitates secure transactions across diverse online environments.
- Reduced Identity Fraud: P2P ID’s decentralized and tamper-proof nature makes it significantly more difficult for fraudsters to manipulate identities or impersonate others. The use of cryptographic algorithms and consensus mechanisms adds an extra layer of protection against identity fraud.
- Efficiency and Cost Savings: By eliminating the need for manual identity verification processes and relying on centralized authorities, P2P ID offers efficiency gains and cost savings. Organizations can reduce administrative overheads and benefit from faster, more streamlined transactions.
- Transparency and Auditability: The use of blockchain technology in P2P ID provides transparency and auditability. Every transaction and change to identity information is recorded on the blockchain, creating an immutable and auditable history of identity-related activities.
Overall, P2P ID offers a user-centric, secure, and efficient solution for identity verification. By empowering individuals with control over their digital identities, P2P ID addresses key challenges associated with centralized identity systems, enhancing security, privacy, and inclusivity in the digital landscape.
Challenges and Limitations of P2P ID
While P2P ID brings numerous benefits and has the potential to revolutionize identity verification, there are also some challenges and limitations associated with its implementation. Let’s explore these factors:
- Adoption and Integration: The widespread adoption of P2P ID requires collaboration between various stakeholders, such as governments, organizations, and individuals. Integrating P2P ID into existing systems and processes may present technical and logistical challenges.
- Standardization and Interoperability: Ensuring the compatibility and interoperability of different P2P ID systems and protocols is crucial. The development of standardized frameworks and protocols is necessary to ensure seamless data exchange and communication across platforms.
- Regulatory Frameworks: The legal and regulatory environment surrounding P2P ID needs to be established to address concerns such as privacy, data protection, and compliance with identity verification requirements. Developing appropriate frameworks that strike a balance between privacy and security is essential.
- Identity Recovery: In a P2P ID system, there is an increased responsibility on individuals to protect their private keys and ensure the security of their digital identities. However, if someone loses their key or becomes a victim of hacking, the process of identity recovery may be challenging and require additional support.
- Scalability: As the number of P2P ID users grows, scalability becomes a concern. It is crucial to ensure that the network can handle a large number of transactions and maintain performance without sacrificing security or decentralization.
- Disruption and Resistance: The adoption of P2P ID may face resistance from existing centralized identity verification systems, which may have vested interests. Overcoming inertia and promoting the benefits of P2P ID to stakeholders may be a significant challenge.
While these challenges and limitations exist, they are not insurmountable. With continued research, collaboration, and refinement, many of these obstacles can be addressed to ensure the successful implementation of P2P ID systems that offer a secure, user-centric, and inclusive approach to identity verification.
Examples of P2P ID in Use
P2P ID is gaining traction, and various organizations and initiatives are incorporating this innovative identity verification concept into their platforms. Let’s explore some real-world examples of P2P ID in use:
- Estonian e-Residency: Estonia’s e-Residency program utilizes P2P ID to enable non-residents to establish a digital identity and access government services remotely. It allows individuals to digitally sign documents, start businesses, and securely access online services from anywhere in the world.
- Sovrin Foundation: The Sovrin Foundation is working towards creating a global self-sovereign identity (SSI) network based on P2P ID principles. The foundation aims to empower individuals with control over their digital identities and facilitate secure and privacy-enhancing digital interactions.
- uPort: uPort is a blockchain-based identity management platform that leverages P2P ID to enable users to create and manage their digital identities. It allows individuals to control their personal data and selectively share identity information with trusted parties. uPort has been used in various applications, including digital voting systems and self-sovereign identity solutions.
- Evernym: Evernym is a leading provider of self-sovereign identity solutions that utilize P2P ID. Their platform allows individuals to create and manage their digital identities, enabling secure and trusted interactions in various domains such as healthcare, financial services, and government sectors.
- Decentralized Identifiers (DID): Decentralized Identifiers, developed by the W3C Consortium, is a set of specifications that standardizes the representation and resolution of decentralized identities. DID allows individuals to have control over their digital identities and securely manage their personal data across different platforms and services.
These examples demonstrate the potential and versatility of P2P ID in transforming how we establish, authenticate, and manage digital identities. As more organizations and initiatives embrace P2P ID principles, we can expect to see a broader adoption of this innovative approach to identity verification in various sectors and industries.
Conclusion
P2P ID, a decentralized identity verification system, is reshaping the way we establish and manage our digital identities. By leveraging blockchain technology, cryptography, and peer consensus, P2P ID offers a secure, user-centric, and efficient solution that addresses the limitations of traditional centralized systems. It puts individuals in control of their own identities, enhances privacy, reduces the risk of identity fraud, and promotes inclusivity.
With P2P ID, individuals can securely share their verified identities across different platforms and services, eliminating the need for third-party intermediaries and streamlining transactions. The compatibility and interoperability of P2P ID systems allow for seamless data exchange and communication, creating a more connected and trusted digital environment.
While there are challenges and limitations to overcome, such as standardization, regulatory frameworks, and scalability, the potential of P2P ID cannot be ignored. Governments, organizations, and individuals are recognizing the benefits of decentralized identity systems, leading to the development and adoption of various P2P ID solutions.
As P2P ID continues to evolve, it has the potential to revolutionize identity verification in numerous industries, including finance, healthcare, government, and more. The secure, user-centric nature of P2P ID can enhance the trustworthiness and efficiency of online transactions, empower individuals with control over their personal data, and provide greater privacy protection.
In conclusion, P2P ID represents a paradigm shift in identity verification, offering a more secure, inclusive, and user-centric approach in the digital age. With ongoing research, collaboration, and refinement, P2P ID has the potential to transform how we establish and authenticate our digital identities, fostering a more transparent, secure, and interconnected digital future.