Introduction
Near Field Communication, commonly known as NFC, is a technology that enables devices to communicate wirelessly over short distances. It allows for the seamless exchange of information and data between two compatible devices simply by bringing them close together. NFC has gained popularity in recent years due to its convenience and versatility, and it is now used in a wide range of applications, from mobile payments to smart home automation.
NFC relies on radio frequency identification (RFID) technology, which makes it possible for devices to establish a connection by simply tapping or bringing them close together. This technology has revolutionized the way we interact with devices and has introduced new possibilities for businesses and consumers alike.
With NFC, users can easily perform tasks such as making payments, transferring files, accessing secure areas, and even controlling household appliances with a simple tap or wave of their devices. It offers a seamless and secure way to connect and exchange information, making it a highly convenient technology for everyday use.
In this article, we will explore how NFC tags work and the various components involved in their operation. We will also delve into the supported devices and technologies, as well as the common uses and benefits of NFC tags. Additionally, we will discuss security considerations and limitations associated with this technology.
So, grab your device and get ready to dive into the fascinating world of NFC and its tags.
What is NFC?
Near Field Communication, commonly referred to as NFC, is a wireless communication technology that allows for the exchange of data between electronic devices within a short range. It enables seamless and secure interactions between devices simply by bringing them close together, typically within a few centimeters.
NFC operates on the same principle as radio frequency identification (RFID), where electromagnetic fields are used to transfer data. However, unlike RFID, which is primarily used for identification and tracking, NFC is designed for more complex interactions between devices.
One of the key features of NFC is its compatibility with a wide range of devices. Most smartphones and tablets are equipped with NFC capabilities, making it accessible to a large user base. Additionally, many modern credit and debit cards also utilize NFC technology for contactless payments.
NFC is a two-way communication technology, meaning information can be exchanged between devices in both directions. This allows for various applications, such as mobile payments, ticketing, access control, data transfer, and more. NFC tags are often used to store and transmit specific information to other devices, making them versatile tools for a variety of use cases.
Furthermore, NFC operates at a frequency of 13.56 MHz, which offers a balance between data transfer speed and range. While the range is limited to a few centimeters, this limitation ensures a higher level of security and prevents unauthorized access to sensitive information.
Overall, NFC technology has revolutionized the way devices communicate and interact with one another. Its convenience, security, and compatibility have made it a popular choice for various applications, ranging from mobile payments and ticketing to home automation and access control systems.
In the next section, we will explore in detail how NFC tags work and the integral components that make them functional.
How do NFC tags work?
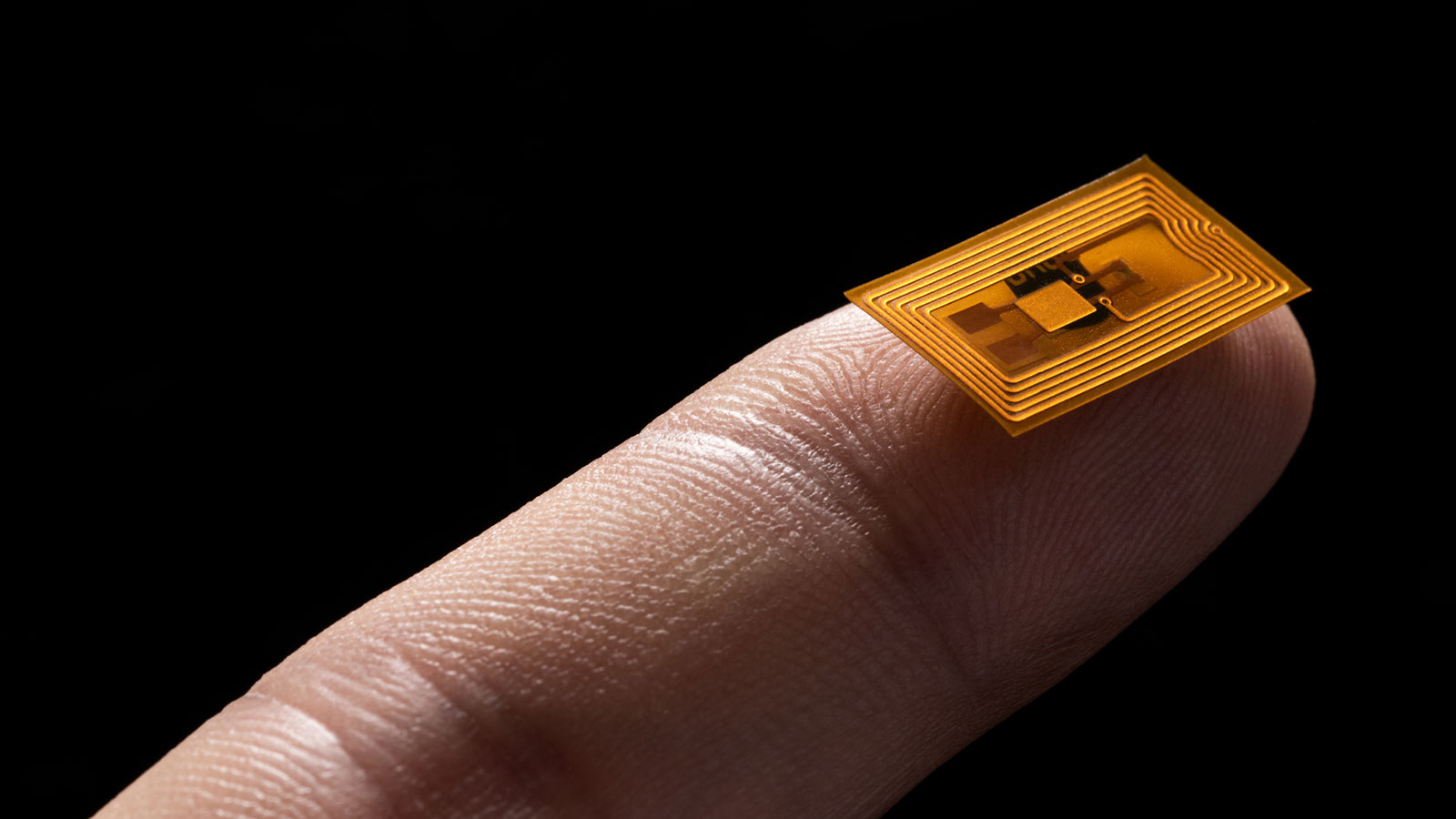
NFC tags are small, passive electronic devices that are embedded with a tiny microchip and an antenna. These tags are capable of storing and transmitting information when activated by an NFC-enabled device.
When an NFC-enabled device, such as a smartphone, comes into close proximity to an NFC tag, electromagnetic induction is used to establish a connection between the two. This allows for the transfer of data and information between the device and the tag.
The communication between the NFC-enabled device and the NFC tag occurs through a process called electromagnetic coupling. The NFC tag is powered by the radio frequency signals emitted by the device, eliminating the need for an external power source.
Once the connection is established, the NFC-enabled device can read the information stored on the NFC tag, or it can write new information onto the tag. This process is known as reading and writing. The NFC tag can store a variety of data, including URLs, text, contact information, and more.
There are different types of NFC tags with varying storage capacities and capabilities. The most common type is the NFC Forum Type 2 tag, which has a storage capacity of up to 48 bytes and is widely used for general purposes, such as marketing campaigns and smart posters.
Another important aspect of NFC tags is the presence of different security features. Some NFC tags support encryption, allowing for secure communication between the device and the tag. This is especially important when dealing with sensitive information, such as financial data or personal credentials.
In addition to reading and writing, NFC tags can also trigger specific actions on the NFC-enabled device they are paired with. For example, tapping an NFC tag embedded in a smart speaker can automatically play a specific music playlist or adjust the lighting in a smart home system.
Overall, NFC tags provide a seamless and convenient way to transmit and receive information between devices. Their versatility and ease of use make them valuable tools in various applications, from marketing and advertising to home automation and access control.
In the following sections, we will explore the components of an NFC tag in more detail and discuss the supported devices and technologies.
The components of an NFC tag
NFC tags are composed of several key components that work together to facilitate communication with NFC-enabled devices. Understanding these components is essential to grasp how NFC tags function and their capabilities.
1. Microchip: The microchip is the brain of the NFC tag. It stores and processes data, allowing the tag to perform various functions. The microchip determines the storage capacity and capabilities of the NFC tag.
2. Antenna: The antenna is responsible for transmitting and receiving radio frequency signals between the NFC tag and the NFC-enabled device. It captures the electromagnetic waves emitted by the device and converts them into electrical signals that the microchip can understand.
3. Memory: The memory of an NFC tag is where the data is stored. Different types of NFC tags offer varying amounts of memory, typically ranging from a few bytes to several kilobytes. The memory can store information such as URLs, text, contact details, or commands to be executed by the NFC-enabled device.
4. Protocol: NFC tags operate based on specific protocols or standards defined by the NFC Forum. The protocols ensure compatibility between NFC-enabled devices and NFC tags, allowing for seamless communication. The most common protocol for NFC tags is the NFC Data Exchange Format (NDEF).
5. Security Features: Some NFC tags are equipped with security features to protect data and ensure secure communication. These features may include encryption, password protection, or the ability to lock the tag after a certain number of accesses. Security is especially important when dealing with sensitive information, such as financial data or personal credentials.
6. Form Factor: NFC tags are available in various form factors, including stickers, cards, key fobs, and even embedded within objects. The form factor determines where and how the NFC tag can be deployed. Stickers, for example, can be attached to surfaces, while cards can be used for access control or as contactless payment cards.
By combining these components, NFC tags can be customized for different use cases and applications. Whether it’s for marketing campaigns, access control, or smart home automation, the components of an NFC tag enable seamless and efficient communication between devices.
The next section will dive into the reading and writing process with NFC tags, shedding light on how devices interact with these tags to exchange data.
Reading and writing with NFC tags
One of the key functionalities of NFC tags is the ability to read and write data between an NFC-enabled device and the tag. This process allows for the exchange of information, customization, and interaction with the NFC tag.
When an NFC-enabled device comes into close proximity with an NFC tag, it can read the data stored on the tag. This data can include various types of information such as URLs, text, contact details, or commands. By simply tapping or bringing the device close to the tag, the NFC technology initiates the communication between the two devices.
To read the data from an NFC tag, the NFC-enabled device emits radio frequency signals that power the tag. The tag then responds by transmitting the stored data back to the device. The device interprets the received data and performs the relevant action based on the information retrieved from the NFC tag.
Writing to an NFC tag is another crucial functionality. With the appropriate permissions and access, an NFC-enabled device can write new data onto an NFC tag. This allows for customization and personalization of the tag’s content. For example, a marketing campaign can utilize NFC tags to distribute customized content or promotional offers to customers.
The process of writing data to an NFC tag involves sending instructions from the NFC-enabled device to the tag. The device specifies the type of data to write, such as a URL or contact information, and the tag stores this new information in its memory. The written data can then be read by other NFC-enabled devices in the future.
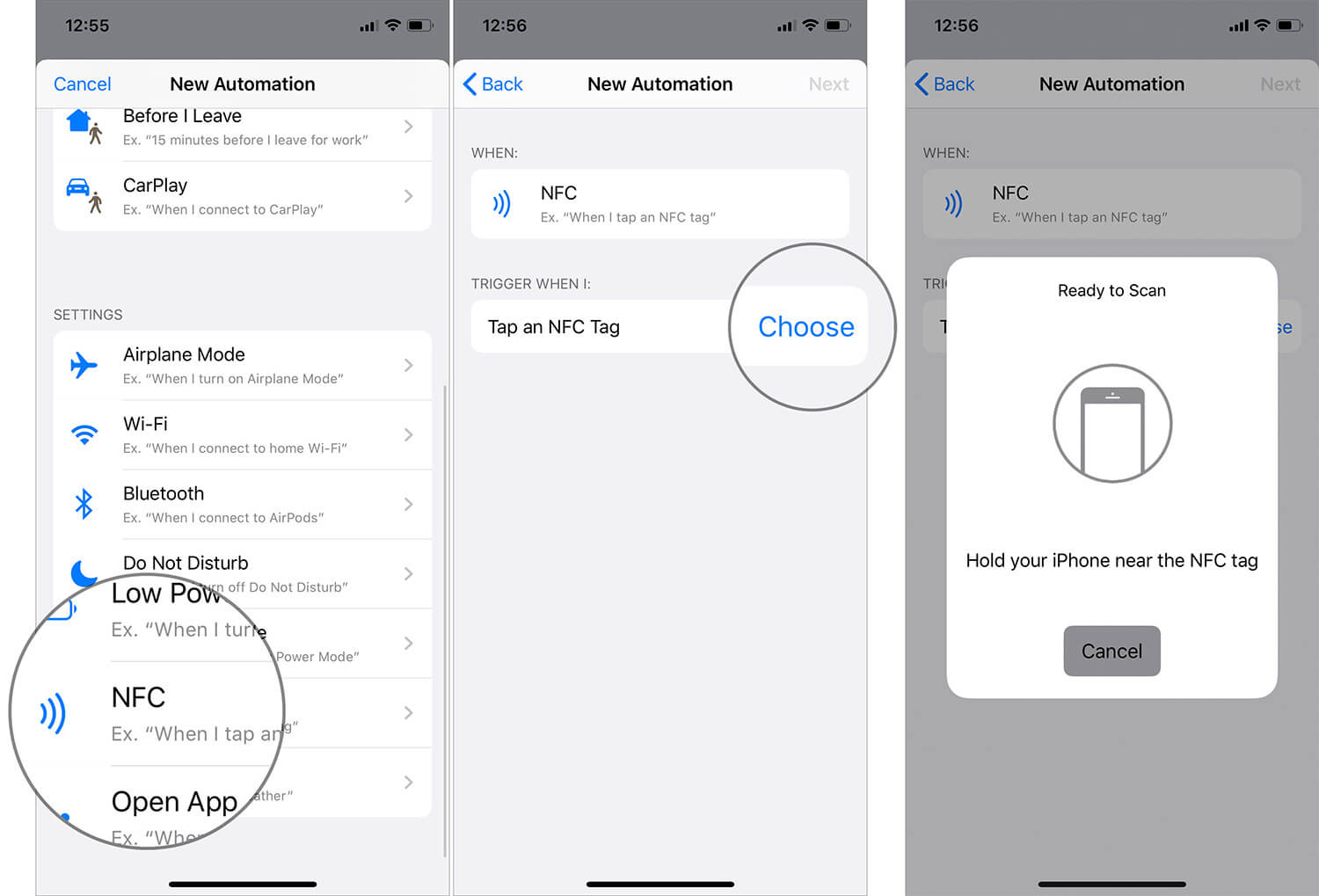
Another useful feature of NFC tags is the ability to trigger specific actions on the NFC-enabled device when tapped or interacted with. This is accomplished by programming the NFC tag to execute a command or launch an application. For example, tapping an NFC tag attached to a car dashboard can automatically launch the navigation app on the user’s smartphone.
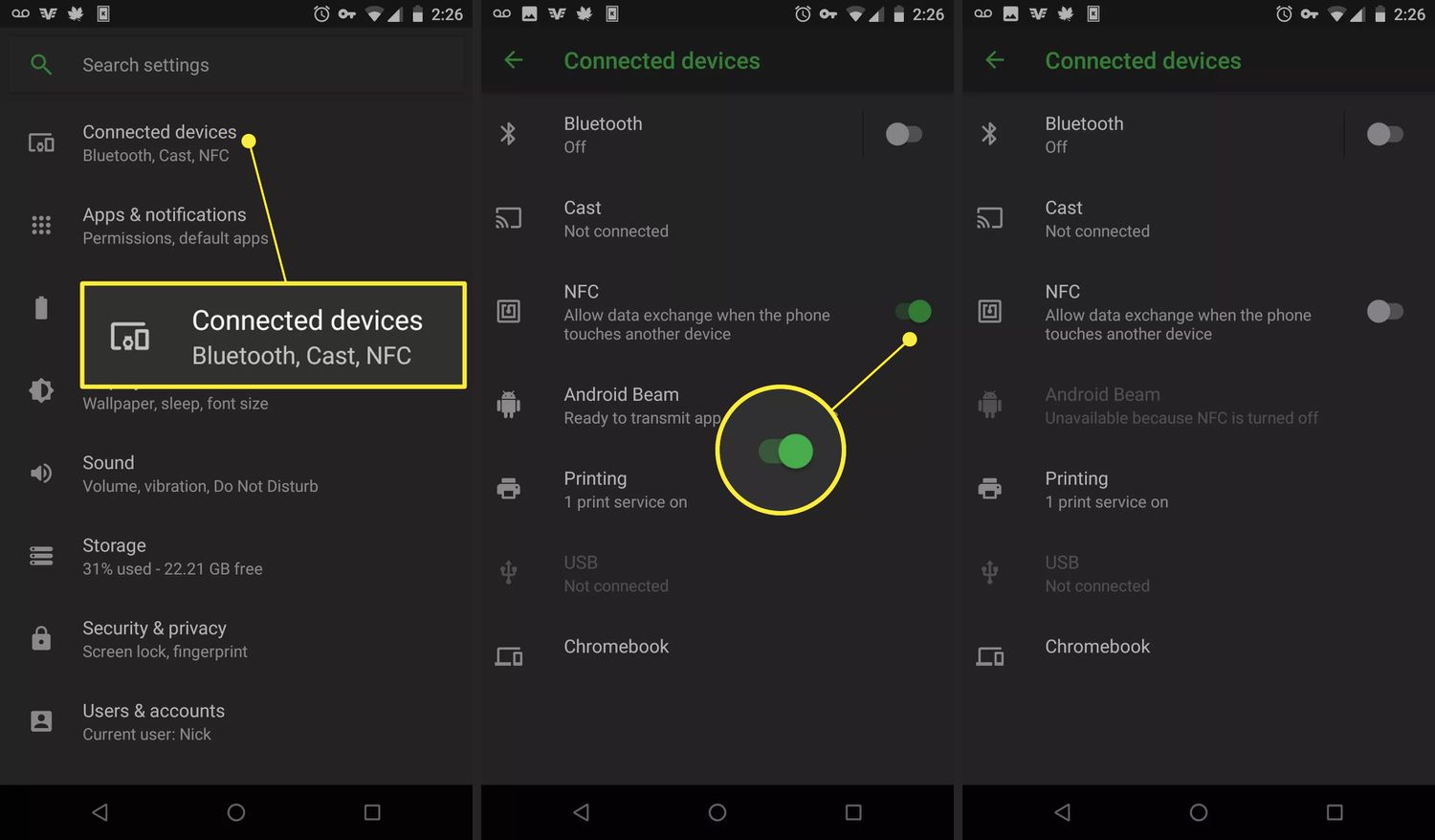
It is important to note that not all NFC-enabled devices support writing to NFC tags. Some devices may only support reading, limiting their interaction with the tags. Additionally, the compatibility of NFC tags with different devices and applications may vary depending on factors such as tag type and protocols supported.
In the next section, we will explore the supported devices and technologies that are compatible with NFC tags, further expanding the possibilities and applications of NFC technology.
Supported devices and technologies
NFC technology has gained widespread adoption and is supported by a wide range of devices and technologies. Understanding the compatibility of NFC tags with different devices is essential for leveraging the full potential of this technology.
1. Smartphones and Tablets: Most modern smartphones and tablets are equipped with NFC capabilities. This includes popular brands such as Apple, Samsung, Google, and many others. NFC-enabled devices allow users to interact with NFC tags for tasks such as mobile payments, transferring files, accessing digital content, and more.
2. Payment Cards: Contactless payment cards often utilize NFC technology to enable secure and convenient transactions. These NFC-enabled cards can be used to make payments by simply tapping or waving them near compatible payment terminals.
3. Wearables: NFC is also supported by various wearable devices, such as smartwatches and fitness trackers. These devices can interact with NFC tags for tasks like accessing information, making payments, or controlling connected devices.
4. Access Control Systems: NFC tags are commonly used in access control systems for secure entry to buildings, rooms, or parking areas. NFC-enabled cards or key fobs can be easily read by NFC readers, granting authorized individuals access to restricted areas.
5. IoT Devices: The Internet of Things (IoT) ecosystem is expanding rapidly, and many IoT devices now support NFC technology. This includes smart home devices, health monitoring devices, and various other IoT-enabled products. NFC tags can be used to configure or control these devices seamlessly.
6. Contactless Ticketing: NFC is widely used in contactless ticketing systems for transportation, events, and concerts. Users can simply tap their NFC-enabled devices or NFC cards to access tickets or validate their fares, eliminating the need for physical tickets.
7. Other Technologies: NFC can also work in conjunction with other technologies such as Bluetooth and Wi-Fi. For example, NFC can be used for quick and secure pairing of devices via Bluetooth, establishing a stable wireless connection for enhanced functionality.
Furthermore, NFC technology utilizes standards and protocols defined by the NFC Forum, ensuring compatibility and interoperability between devices and applications. The NFC Data Exchange Format (NDEF) is the most commonly used protocol for storing and exchanging data on NFC tags.
It’s worth noting that the availability and capabilities of NFC may vary depending on the specific device model or region. While NFC has gained widespread acceptance, it is important to check device specifications and ensure compatibility before relying on NFC functionality.
In the next section, we will explore some common use cases of NFC tags, highlighting their practical applications in various industries and domains.
Common uses of NFC tags
NFC tags have become increasingly popular due to their versatility and ease of use. They are widely utilized in various industries and domains, offering practical solutions to everyday challenges. Let’s explore some common use cases of NFC tags:
1. Mobile Payments: NFC tags play a crucial role in enabling contactless payments. With a simple tap of an NFC-enabled device or card, users can make secure transactions without the need for physical cash or traditional payment methods.
2. Marketing and Advertising: NFC tags are frequently used in marketing campaigns and advertising to enhance customer engagement. By incorporating NFC tags into promotional materials, businesses can deliver personalized content, discounts, or product information directly to customers’ devices.
3. Access Control and Security: NFC tags are extensively utilized in access control systems to grant authorized individuals entry to restricted areas. NFC-enabled cards or key fobs are easily read by NFC readers, ensuring secure and efficient access control.
4. Asset Tracking: NFC tags are valuable tools for tracking and managing assets. By affixing NFC tags to equipment or inventory, businesses can easily monitor their location, track maintenance schedules, or update information in real-time.
5. Smart Home Automation: NFC tags are essential for controlling and automating smart home devices. A simple tap on an NFC tag can adjust lighting, activate security systems, or configure special settings, providing a convenient and seamless smart home experience.
6. Event Ticketing: NFC tags revolutionize the ticketing industry by allowing contactless entry to events and venues. By tapping NFC-enabled devices or cards to NFC readers, attendees can swiftly access events without the hassle of physical tickets.
7. Information Sharing: NFC tags make information sharing effortless. By encoding contact details, social media profiles, or website URLs onto an NFC tag, users can easily share their information with others by simply tapping their devices.
8. Authentication and Verification: NFC tags are employed in various authentication applications, including user verification, employee identification, or digital signatures. The secure communication capabilities of NFC technology provide an extra layer of authentication and verification.
These examples represent just a fraction of the potential use cases for NFC tags. The versatility and convenience of NFC technology make it an invaluable tool in a wide range of industries, from retail and hospitality to healthcare and logistics.
Next, we will discuss the benefits and limitations of NFC tags, helping you weigh the advantages and considerations of utilizing this technology.
Benefits and limitations of NFC tags
NFC tags offer a range of benefits that have contributed to their widespread adoption. However, it is important to consider their limitations as well. Let’s explore the advantages and considerations associated with NFC tags:
Benefits of NFC tags:
1. Convenience: NFC tags provide a convenient way to exchange information and perform tasks with a simple tap or wave of an NFC-enabled device. This eliminates the need for physical contact or complex setup procedures.
2. Compatibility: NFC technology is supported by a wide range of devices, including smartphones, tablets, wearables, and contactless payment cards. This compatibility allows for seamless interaction and widespread adoption.
3. Versatility: NFC tags can be programmed to perform various actions, such as opening URLs, launching applications, or adjusting settings. This versatility makes NFC tags suitable for a wide range of applications and use cases.
4. Security: NFC tags offer secure communication between devices, ensuring the confidentiality of data exchanged. Some NFC tags support encryption and password protection, enhancing the security of sensitive information.
5. Integration with IoT: NFC tags seamlessly integrate with the Internet of Things (IoT) ecosystem, allowing users to control and interact with IoT devices effortlessly. This integration enhances the automation and customization capabilities of IoT systems.
Limitations of NFC tags:
1. Limited Range: NFC tags have a short reading range, typically within a few centimeters. This limitation restricts the distance at which the tag can be read, requiring close proximity between the tag and the NFC-enabled device.
2. Limited Storage Capacity: NFC tags have limited storage capacity, typically ranging from a few bytes to several kilobytes. This may restrict the amount of data that can be stored on the tag, depending on the specific use case.
3. Device Compatibility: While NFC technology is widely supported, some devices may not have NFC capabilities or may have limitations in terms of reading and writing to NFC tags. Compatibility should be verified before relying on NFC functionality.
4. Power Dependency: NFC tags rely on the power generated by the NFC-enabled device for operation. This means that the tag is passive and requires an external power source, such as a smartphone, to function.
5. Environmental Interference: NFC technology can be affected by environmental factors, such as metal objects or electromagnetic interference. These factors may hinder the performance of NFC tags in certain situations or environments.
Understanding the benefits and limitations of NFC tags is crucial for making informed decisions when implementing NFC-based solutions. While NFC tags offer numerous advantages in terms of convenience, compatibility, and security, it is important to consider the limitations and ensure they align with the specific requirements of the use case.
In the next section, we will discuss the security considerations associated with NFC tags, highlighting the importance of implementing appropriate security measures to safeguard the data exchanged.
Security considerations with NFC tags
While NFC technology offers convenience and ease of use, it is important to address the security considerations associated with NFC tags. Implementing appropriate security measures is essential to protect the data exchanged between NFC-enabled devices and NFC tags. Let’s explore some key security considerations:
1. Data Encryption: To enhance security, NFC tags can support data encryption, ensuring that any sensitive information stored on the tag is protected. Encryption prevents unauthorized access to the data and provides an additional layer of security during communication.
2. Password Protection: Some NFC tags allow for password protection to safeguard access to the stored data. This helps prevent unauthorized individuals from reading or modifying the information contained within the tag.
3. Authentication Mechanisms: NFC tags can be equipped with authentication mechanisms to verify the identity of the device attempting to read or write data. This ensures that only authorized devices can interact with the tag, minimizing the risk of tampering or unauthorized access.
4. Limited Access Control: NFC tags can be programmed to restrict access to certain actions or functionalities. This limits the capabilities of unauthorized devices and enhances the control over the interactions with the tag.
5. Secure Communication Channels: Secure communication protocols, such as Secure Element or Host Card Emulation, can be employed to ensure the integrity and confidentiality of the exchanged data. These protocols establish secure channels between the NFC-enabled device and the tag, preventing eavesdropping or interception of sensitive information.
6. Physical Protection: Physical tampering with NFC tags can be a potential security risk. Measures such as embedding NFC tags within tamper-evident packages or using specialized secure NFC tags with physical anti-tampering features can mitigate these risks.
7. Vulnerability Management: Regular updates and patches should be applied to NFC-enabled devices and their firmware to address any security vulnerabilities that may arise. Keeping both the devices and the NFC tag technology up-to-date is crucial in maintaining a secure environment.
8. User Awareness and Education: Educating users about secure NFC interactions, such as being cautious when interacting with unknown NFC tags or not sharing sensitive information with untrusted sources, is essential to prevent social engineering attacks.
Implementing a combination of these security measures ensures the protection of data and minimizes the risk of unauthorized access or tampering. Organizations and individuals should evaluate their specific use cases and apply the appropriate security practices accordingly.
In the next section, we will conclude the article by summarizing the key points discussed and highlighting the significance of NFC tags in today’s technological landscape.
Conclusion
NFC tags have revolutionized the way devices communicate and interact with one another. With their convenience, compatibility, and security features, NFC tags have found widespread applications across various industries and domains.
NFC technology allows for seamless and secure communication between NFC-enabled devices and tags through electromagnetic coupling. This enables tasks such as mobile payments, information sharing, access control, and smart home automation with a simple tap or wave of a device.
NFC tags are equipped with microchips, antennas, and memory, enabling them to store and transmit data to NFC-enabled devices. The ability to read and write data on these tags opens up endless possibilities for customization and interaction.
Supported by a wide range of devices, including smartphones, tablets, wearables, and contactless payment cards, NFC tags have become an integral part of our daily lives. They are used in marketing campaigns, access control systems, event ticketing, IoT integration, and various other applications.
While NFC tags offer numerous benefits, it is important to consider their limitations. These include the limited range, storage capacity, and reliance on external power sources.
Addressing security considerations is crucial when utilizing NFC tags. Implementing encryption, password protection, authentication mechanisms, and secure communication channels helps safeguard the data exchanged between devices and tags.
In conclusion, NFC tags provide a seamless and convenient way to exchange information and perform tasks with NFC-enabled devices. Their versatility, compatibility, and security features make them valuable tools in multiple industries and use cases.
As technology continues to evolve, NFC tags will continue to play an important role in enabling efficient and secure interactions between devices. It is an exciting technology that will likely see further advancements and increased adoption in the future.