Introduction
When it comes to computer security, one of the most crucial elements is password protection. In Windows operating systems, passwords play a vital role in safeguarding user accounts and sensitive data. However, have you ever wondered where passwords are stored in Windows?
Understanding where passwords are stored can help you gain insights into their security and potential vulnerabilities. In this article, we will explore various locations where passwords are stored in Windows, shedding light on different scenarios and devices.
From local user account passwords to cached domain passwords, let’s delve into the intricate world of Windows password storage.
Before we dive into specific password storage locations, it’s essential to note that passwords in Windows are usually encrypted or hashed. Encryption ensures that passwords are stored in a secure manner, making it difficult for unauthorized individuals to access them. Hashing, on the other hand, transforms passwords into unique sets of characters, making it virtually impossible to reverse-engineer the original password.
Now, let’s explore the various locations where passwords are stored in Windows, uncovering the secrets behind your account and system security.
Local User Account Passwords
Local user account passwords in Windows are stored in the Security Account Manager (SAM) database, which is a part of the Windows Registry. The SAM database is an encrypted file that contains user account information, including usernames and password hashes.
When a user creates a local user account or updates the password for an existing account, the password hash is stored in the SAM database. It’s important to note that the actual password is never stored in clear text; instead, it is transformed into a cryptographic hash using a one-way function.
The SAM database is located in the %SystemRoot%\system32\config directory, and it is protected from unauthorized access by Windows. However, malicious actors with administrative privileges or physical access to the system may attempt to extract the password hashes from the SAM database.
To further enhance security, Windows uses a process called “salting” to prevent rainbow table attacks. A salt is a random value that is added to the password before hashing, making it more difficult to crack the password using precomputed tables of hashes.
In order to retrieve the actual password from the SAM database, an attacker would need to employ various password cracking techniques, such as brute-force attacks or dictionary attacks, to attempt to match the hashed password with possible plaintext passwords.
Windows also provides mechanisms for administrators to reset or change local user account passwords, both through the graphical user interface (GUI) and command-line tools. These changes are reflected in the SAM database, where the new password hash replaces the old one.
It’s important to regularly update and strengthen passwords for local user accounts in order to maintain the security and integrity of your Windows system.
Cached Domain Passwords
In Windows, when a user logs into a domain-joined computer, the domain controller is responsible for authenticating the user’s credentials. However, to provide users with uninterrupted access to their accounts, Windows caches domain credentials locally.
Cached domain passwords are stored in the Security Account Manager (SAM) database, similar to local user account passwords. When a user logs in, Windows stores a copy of their hashed domain password in the SAM database on the local system.
This cache allows users to log in to their domain account even if the domain controller is not available. It is especially useful for mobile users who frequently work offline or experience network connectivity issues.
The cached domain passwords are stored in the Credential Manager, which is a utility in Windows that manages and stores various types of credentials, including passwords for remote resources.
The Credential Manager encrypts the cached domain passwords to ensure their security. By default, only the user who cached the passwords or an administrator can access them. This provides an additional layer of protection against unauthorized access to cached domain passwords.
It’s important to note that the number of cached domain passwords that can be stored on a system is limited. By default, Windows stores the most recent ten logon credentials. If more than ten users have logged in to the system, the oldest credentials will be replaced with the new ones.
Although cached domain passwords provide convenience for users, they also present a potential security risk. If an attacker gains physical access to a computer with cached domain credentials, they can extract the password hashes from the SAM database and attempt to crack them offline.
Therefore, it is crucial to have strong passwords, implement other security measures such as screen lock or hibernate, and ensure that physical access to the computer is restricted to trusted individuals.
Active Directory Domain Passwords
In a Windows Active Directory domain environment, user account passwords are managed and stored on the domain controller. The domain controller is responsible for authenticating users and maintaining the security of their passwords.
When a user creates or changes their password, the password is submitted to the domain controller, where it is hashed and stored in the Active Directory database. The password is never stored in clear text, ensuring that even administrators cannot view the actual password.
The hashing algorithm used in Active Directory is based on the Secure Hash Algorithm (SHA), which transforms the password into a fixed-length hash value. The hash value is unique to the password and cannot be reversed to retrieve the original password.
Active Directory also employs additional security measures, such as salting and stretching, to further protect password hashes. Salting involves adding a random value to the password before hashing, making it more resistant to precomputed table attacks. Stretching involves repeatedly hashing the password, which increases the time required for brute-force attacks.
When a user logs into a domain-joined computer, the entered password is sent to the domain controller for verification. The domain controller retrieves the stored password hash for that user account and compares it with the hash of the entered password. If they match, the user is granted access.
Active Directory provides domain administrators with tools to manage and monitor domain passwords. This includes options to enforce password complexity requirements, determine password expiration policies, and implement account lockout thresholds.
To enhance password security in an Active Directory environment, it is recommended to enforce strong password policies, educate users about the importance of unique and secure passwords, and consider implementing multi-factor authentication (MFA) for added protection.
Remember, the security of Active Directory passwords is crucial in maintaining the overall security posture of an organization’s network.
Windows Subsystem for Linux (WSL) Passwords
The Windows Subsystem for Linux (WSL) allows users to run a Linux environment directly on their Windows operating system. With WSL, users can access Linux utilities, applications, and command-line tools without the need for a separate Linux installation.
When it comes to passwords, WSL behaves differently from traditional Windows user accounts. In WSL, the user’s password is managed by the Linux subsystem, rather than the Windows authentication system.
When a user sets up their WSL environment, they are prompted to create a username and password specific to their Linux distribution. This username and password combination is used to authenticate the user within the WSL environment.
The password for the Linux user account in WSL is stored in an encrypted form within the Linux distribution. The specific location and method of encryption can vary depending on the chosen Linux distribution.
It’s important to note that the WSL password is separate from the Windows user account password. Changing the password for the Windows user account does not automatically update the password for the WSL Linux user account.
Resetting or changing the WSL password is done through the Linux distribution itself. The process may vary depending on the Linux distribution, but generally involves using the passwd command to update the password for the Linux user account.
Since the WSL environment operates as a subsystem within Windows, it is important to maintain strong and secure passwords for the Linux user account. This helps prevent unauthorized access and protects the integrity of the Linux environment and any data or applications within it.
It’s worth noting that the WSL environment is designed for development and testing purposes, and may not have the same level of security as a dedicated Linux installation. Therefore, it’s advisable to exercise caution and avoid using WSL for sensitive activities or storing sensitive data.
Overall, understanding how passwords are managed in WSL can help users maintain the security of their Linux environment and ensure a smooth and secure experience within the Windows operating system.
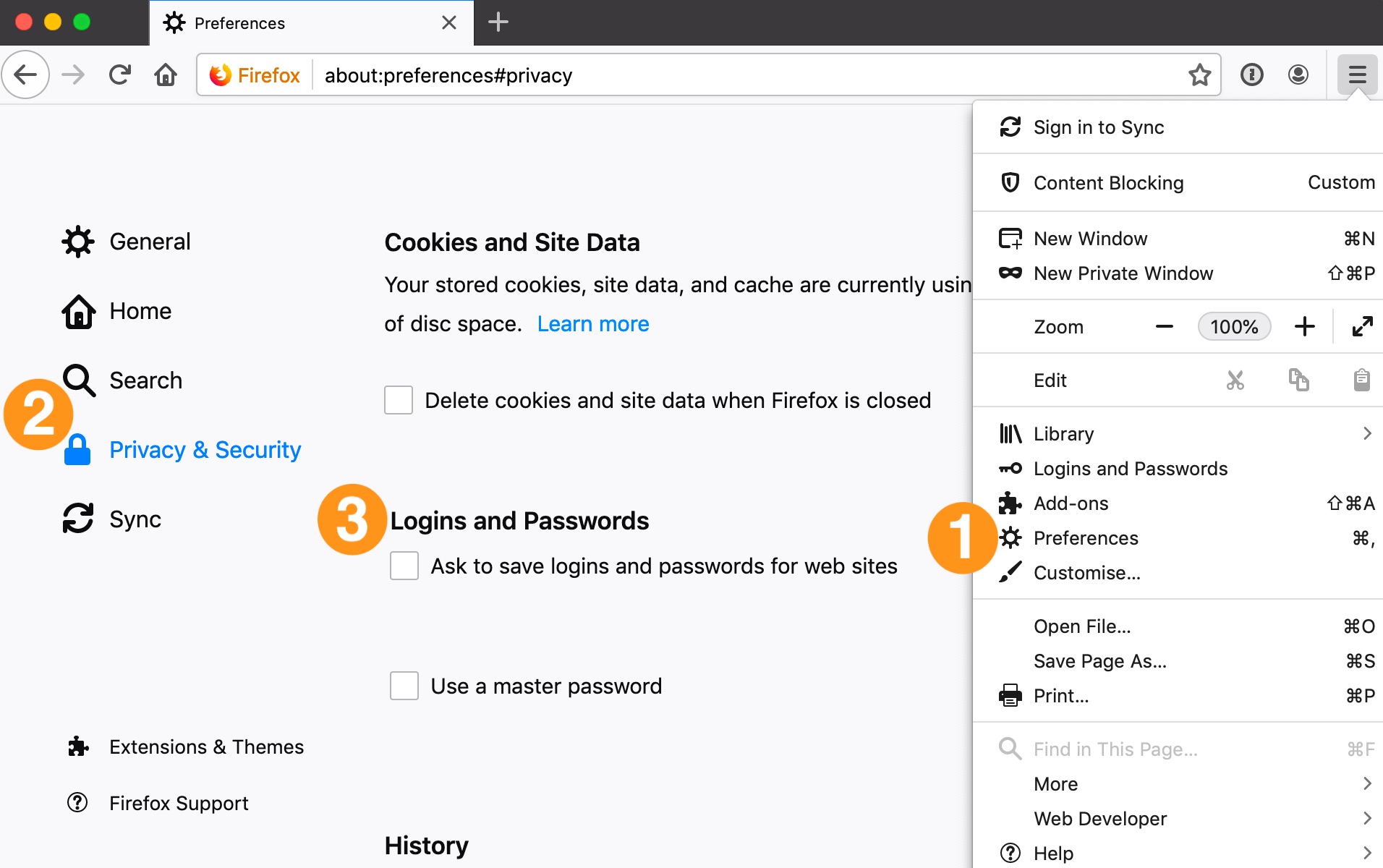
Credential Manager
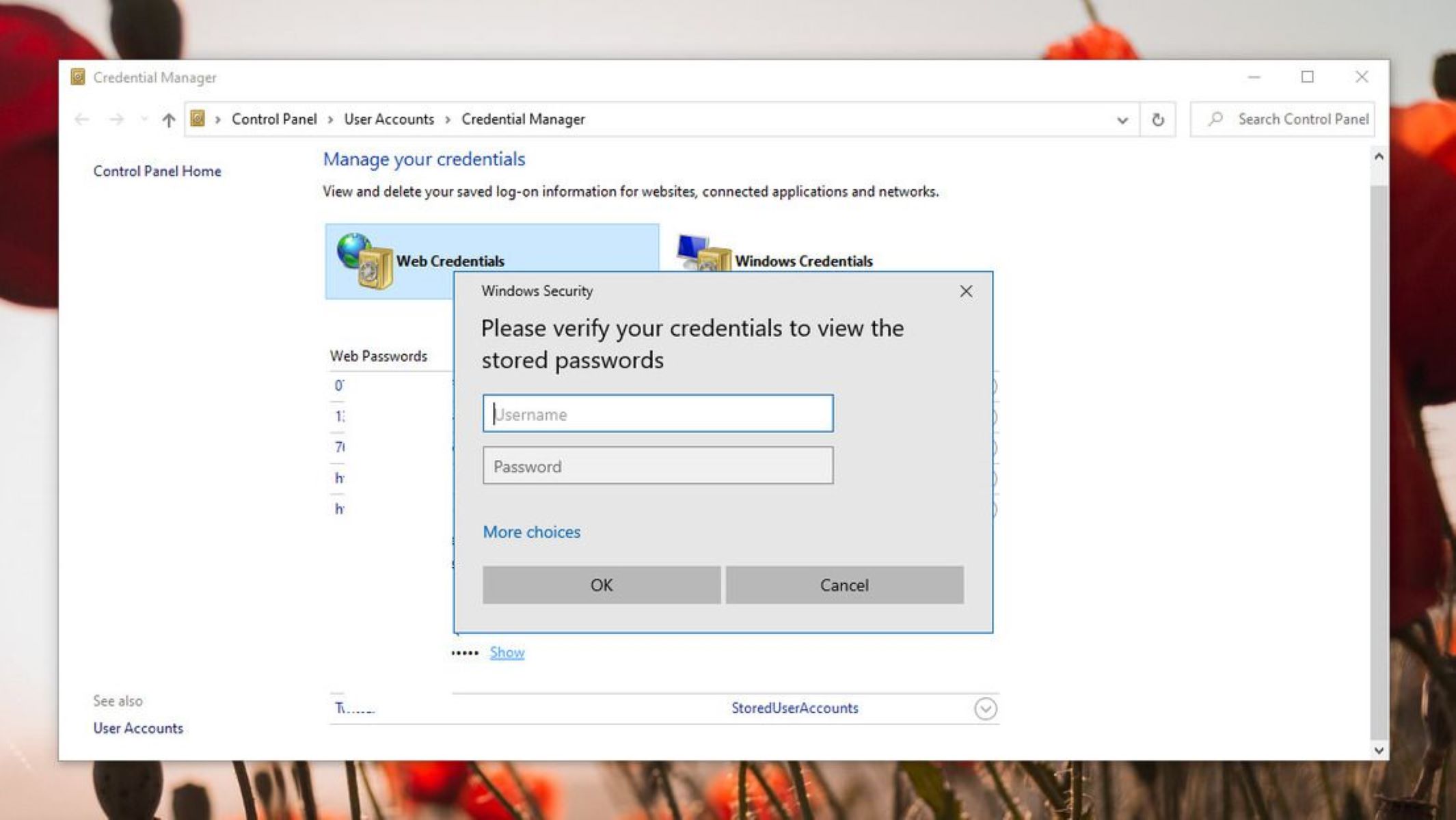
The Credential Manager is a built-in utility in Windows that allows users to securely store and manage various types of credentials, including usernames, passwords, and certificates. It serves as a centralized repository for storing credentials for different applications, networks, and websites.
The Credential Manager can be accessed through the Control Panel or by searching for “Credential Manager” in the Start menu. It provides a user-friendly interface for managing credentials and simplifies the login process for applications and websites.
When you save a username and password for a specific application or website, Windows encrypts and stores the credentials in the Credential Manager. This ensures that the passwords are protected and not easily accessible to unauthorized users.
In addition to application and website passwords, the Credential Manager also stores other types of credentials, such as network credentials and virtual private network (VPN) credentials. This allows for seamless authentication when connecting to resources on a network or accessing a remote server.
The Credential Manager provides options for editing, deleting, and backing up stored credentials. It also allows for the creation of new credentials manually, in case you need to store credentials for an application or website that does not prompt you to save them.
It’s important to note that while the Credential Manager offers convenience by automatically filling in usernames and passwords for stored credentials, it’s crucial to use strong and unique passwords for each application or website. This helps to prevent unauthorized access to multiple accounts if one credential is compromised.
Additionally, it’s recommended to regularly review and remove any unnecessary or outdated credentials from the Credential Manager to maintain security. This minimizes the risk of exposing sensitive information in case of a security breach.
The Credential Manager plays a vital role in simplifying the authentication process for various applications and resources in Windows. By using this utility to store and manage credentials, users can benefit from enhanced convenience while maintaining strong security practices.
Internet Explorer and Microsoft Edge Passwords
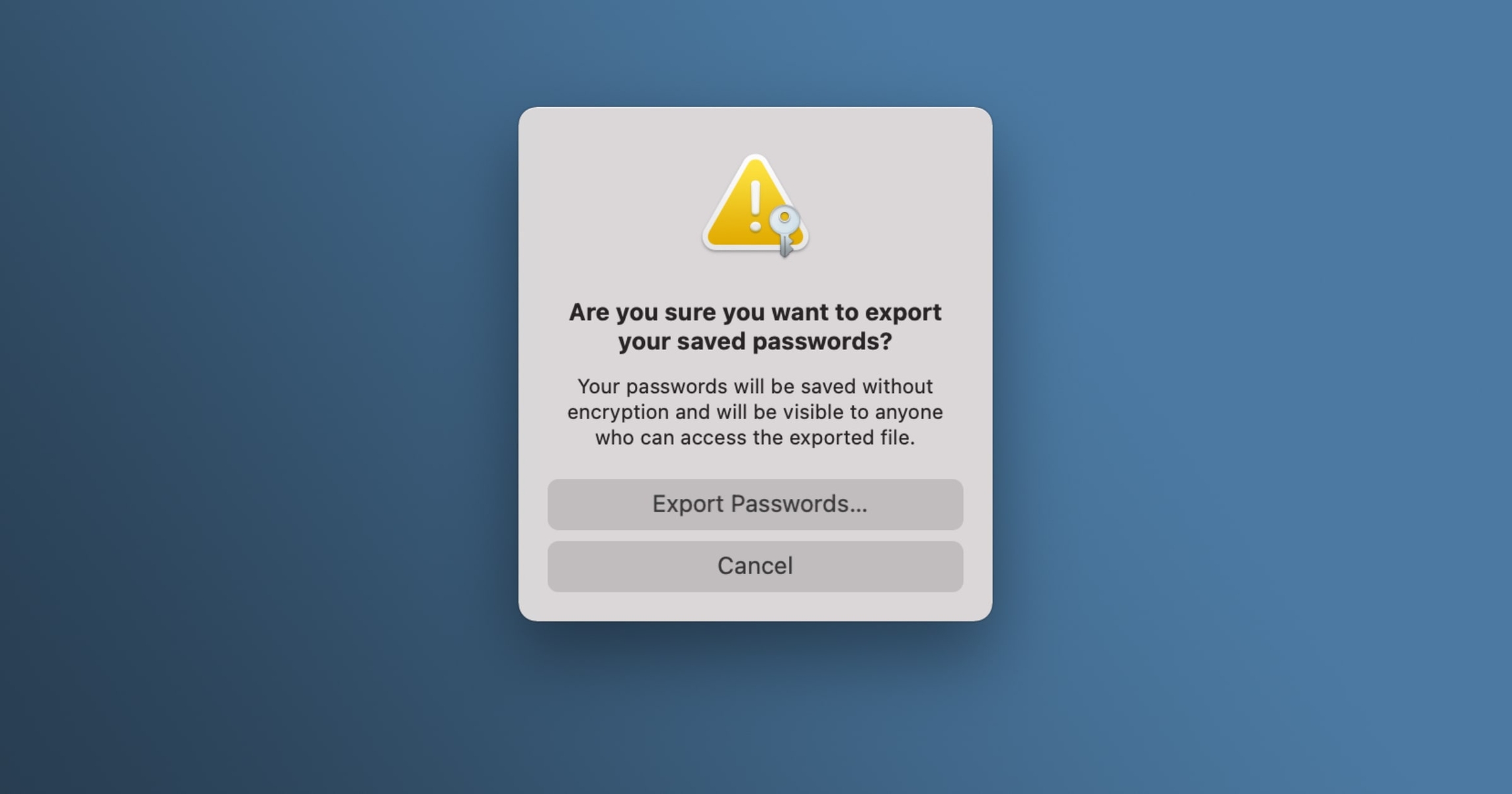
Internet Explorer was the default web browser in Windows for many years, and it has been succeeded by Microsoft Edge as the default browser in recent versions of Windows. Both browsers offer the ability to save and manage passwords for websites that users frequently visit.
When a user chooses to save a password for a website in Internet Explorer or Microsoft Edge, the browser securely stores the credentials in its password manager. The saved passwords are encrypted and stored within the Windows Credential Manager, which we discussed earlier.
To access the saved passwords in Internet Explorer, users can go to the “Internet Options” menu, select the “Content” tab, and click on the “Settings” button in the “AutoComplete” section. From there, they can choose the “Manage Passwords” option to view, edit, or remove saved passwords.
In Microsoft Edge, users can access the saved passwords through the browser’s settings. By opening the “Settings and More” menu (represented by three dots in the top-right corner), selecting “Settings,” and navigating to the “Passwords” section, users can view and manage their saved passwords.
It’s worth noting that both Internet Explorer and Microsoft Edge offer the option to protect saved passwords with a master password. This adds an additional layer of security and prevents unauthorized access to the password manager.
However, it’s crucial to be aware that the security of saved passwords in these browsers ultimately depends on the security measures implemented by the user. It’s recommended to use strong, unique passwords for each website, enable two-factor authentication when available, and regularly review and update passwords for increased security.
Furthermore, if an unauthorized user gains access to the Windows user account or compromises the system, they may be able to access the saved passwords in Internet Explorer or Microsoft Edge. Therefore, it’s essential to secure your Windows user account with a strong password and keep your system updated with the latest security patches and updates.
By understanding how passwords are managed in Internet Explorer and Microsoft Edge, users can make informed decisions on whether to save passwords and take necessary precautions to protect their credentials when using these browsers.
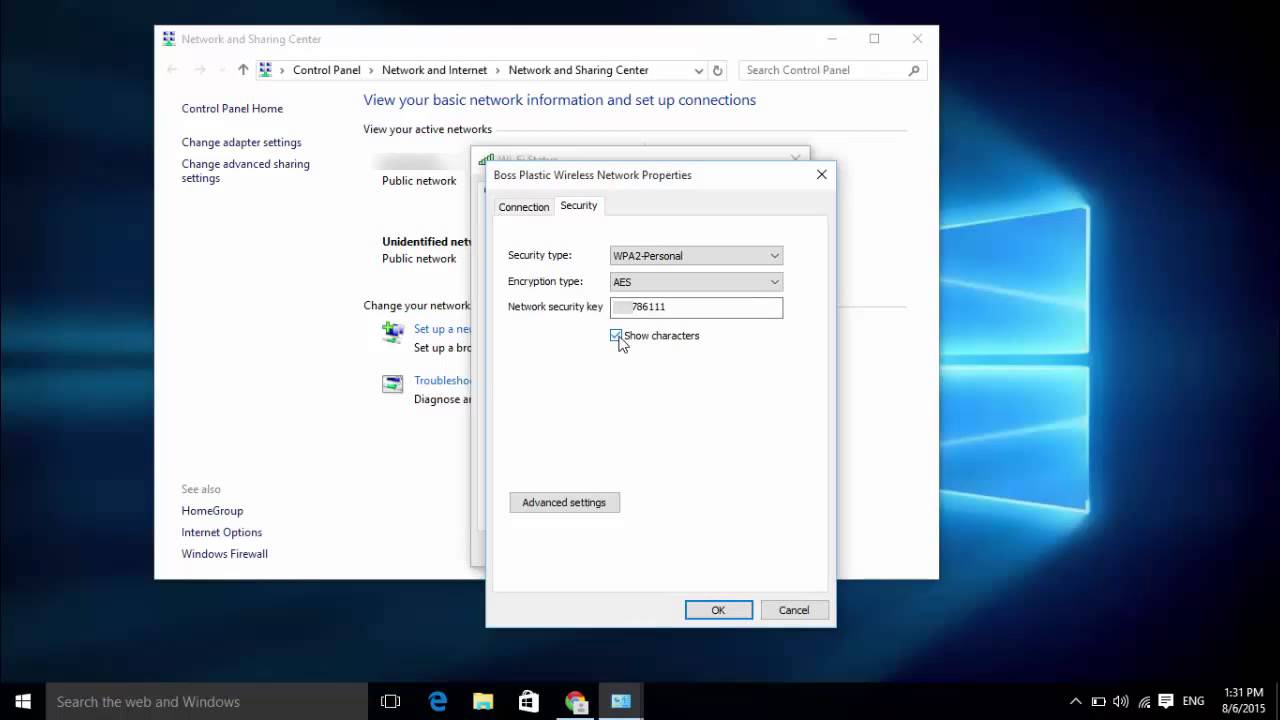
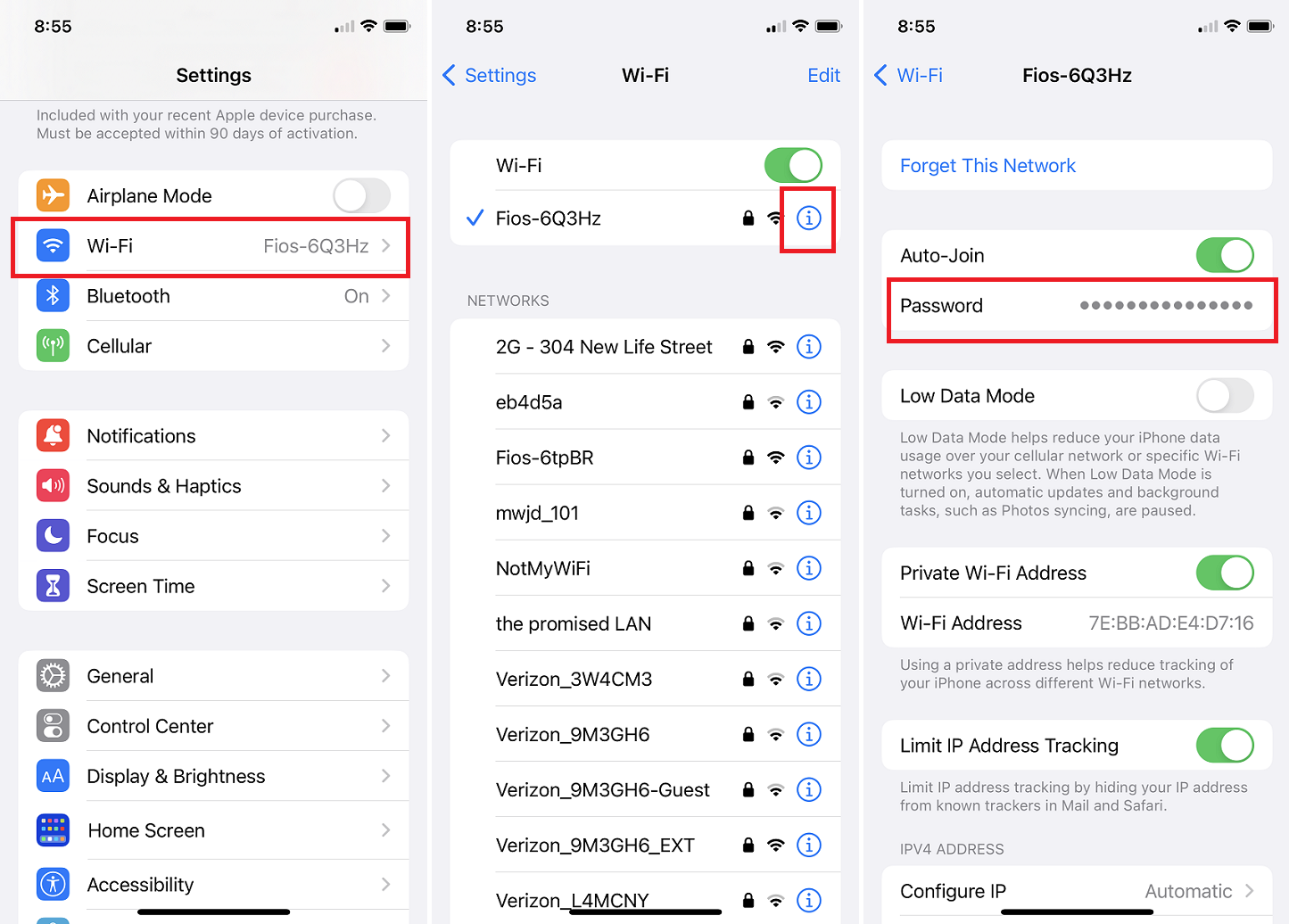
Wi-Fi Network Passwords
Wi-Fi network passwords are an essential part of securing wireless connections and preventing unauthorized access to your network. In Windows, when you connect to a Wi-Fi network, the network’s password is securely stored on your computer to allow for automatic and seamless connections in the future.
Windows uses the Wireless Network Key, also known as the Wi-Fi password, to encrypt and decrypt data transmitted over the wireless network. It ensures that only authorized devices with the correct password can access the network and exchange information.
When you connect to a new Wi-Fi network, Windows prompts you to enter the network’s password. Once validated, the password is saved in the Windows operating system.
You can view and manage saved Wi-Fi network passwords in Windows by going to the Network and Sharing Center. From there, you can navigate to the “Manage Wireless Networks” section, select the desired network, and choose the “Properties” option. In the Properties window, you can view the network’s password or modify it if needed.
It’s important to note that the saved Wi-Fi network passwords are stored within the Windows operating system, specifically in the Windows Credential Manager. The Windows Credential Manager stores various types of credentials, including Wi-Fi network passwords, in an encrypted format to ensure their security.
While the Wi-Fi network passwords are encrypted and stored securely, it’s crucial to protect your Windows user account with a strong password. An unauthorized user who gains access to your Windows account may be able to view and extract the network passwords from the Credential Manager.
To further enhance the security of your Wi-Fi network, it is recommended to use a strong and unique password for your network, enable encryption protocols such as WPA2 or WPA3, and regularly update the Wi-Fi network password.
If you need to share your Wi-Fi network password with others, it’s advisable to do so in a secure and private manner. Avoid sharing it over insecure communication channels, such as public messaging platforms or social media.
By understanding how Wi-Fi network passwords are stored and managed in Windows, you can ensure the security of your wireless connections and protect your network from unauthorized access.
Remote Desktop Passwords
Remote Desktop is a feature in Windows that allows users to connect to and control a remote computer over a network connection. To establish a remote desktop session, users must provide the appropriate credentials, including a username and password.
When accessing a remote computer using Remote Desktop, the password is sent securely over the network and verified by the remote computer’s operating system. Windows uses strong encryption protocols to protect the password during transmission, ensuring that it cannot be intercepted or easily deciphered by unauthorized individuals.
Once authenticated, the remote desktop session is established, and the user gains control over the remote computer as if they were physically present. It’s important to note that the actual password is not stored on the local computer used to initiate the remote desktop session; it is only used for authentication purposes during the connection process.
On the remote computer, the password is stored in the local security database, known as the Security Account Manager (SAM) database, along with other user account information. The password is stored in an encrypted form using hash algorithms to protect it from unauthorized access.
When the user logs out or disconnects from the remote desktop session, the password is no longer accessible on the local computer. Instead, it remains securely stored on the remote computer’s SAM database and can only be accessed through proper authentication.
To enhance the security of remote desktop connections, it is important to use strong and unique passwords for user accounts on both the local and remote computers. Regularly updating the passwords and implementing other security measures, such as two-factor authentication, can further enhance the security of remote desktop sessions.
It’s also crucial to ensure that the remote desktop feature is properly configured to protect against unauthorized access. This includes using strong network-level authentication protocols, such as Network Level Authentication (NLA), to establish secure connections.
By understanding how remote desktop passwords are utilized and stored, users can maintain the security of their remote connections and protect sensitive information on both the local and remote computers.
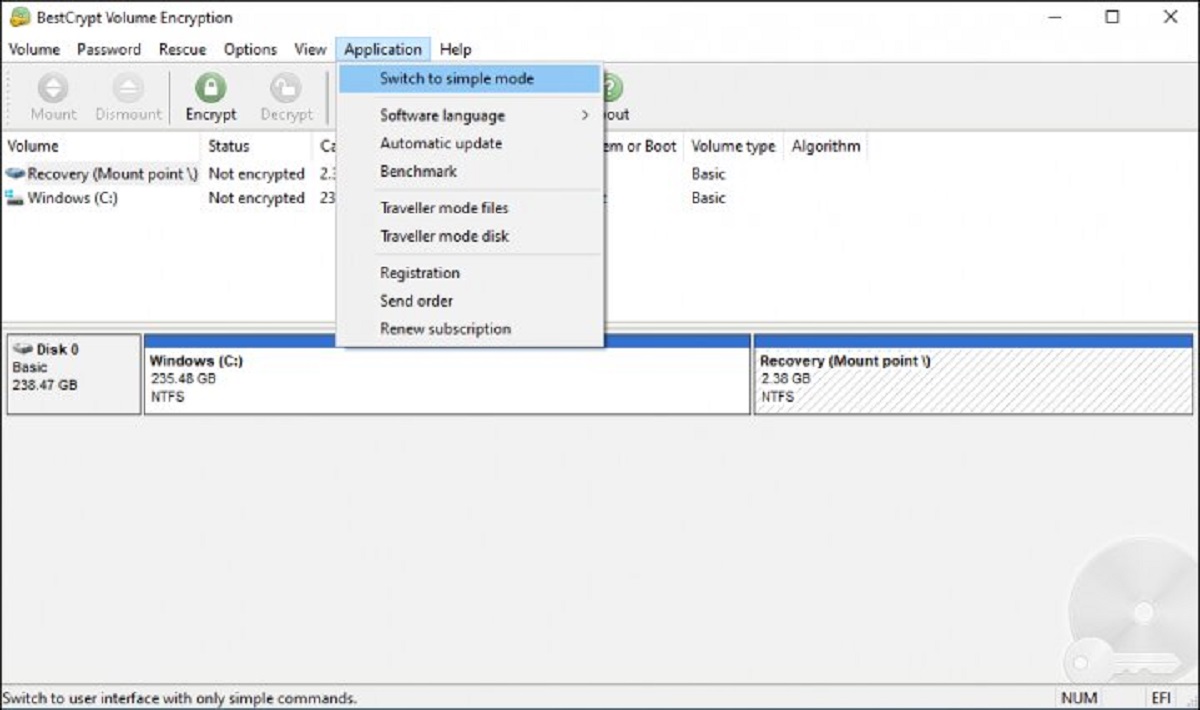
BitLocker Recovery Key Passwords
BitLocker is a disk encryption feature in Windows that provides enhanced security for data stored on drives. When BitLocker is enabled, it encrypts the entire drive, making the data inaccessible without the correct authentication. In case of a forgotten password or other issues, BitLocker provides a recovery key that allows users to regain access to the encrypted drive.
The BitLocker recovery key serves as a backup method to unlock the encrypted drive in situations where the password or other authentication methods cannot be used. It is essential to store the recovery key in a secure location separate from the encrypted drive to prevent unauthorized access to the data.
By default, BitLocker offers several ways to store the recovery key, including saving it to a file, printing it, or syncing it to a Microsoft account. Users can choose the method that best suits their needs and ensures the recovery key’s security.
The recovery key itself is a unique alphanumeric code that consists of 48 or 256 bits, depending on the BitLocker encryption option chosen. It is randomly generated and stored in the BitLocker metadata of the encrypted drive.
When the user forgets their BitLocker password or encounters any issues, they can use the recovery key to access the encrypted drive. Windows prompts the user to enter the recovery key during the BitLocker recovery process to authenticate their ownership of the drive.
It’s crucial to note that the BitLocker recovery key is a critical piece of information for accessing encrypted data. Losing the recovery key can result in permanent data loss, as there is no built-in method to recover data without it.
Windows provides a way to view and copy the recovery key through an interactive prompt when BitLocker is enabled. Users can also access it by going to the BitLocker settings in the Control Panel or using the Manage-bde command-line tool.
Given the sensitivity of the BitLocker recovery key, it is advisable to store it in a secure, offline location such as a safe, encrypted drive, or a password manager with strong security measures in place. It’s important to ensure that only authorized individuals can access the recovery key to prevent any compromise of the encrypted data.
By understanding the significance of the BitLocker recovery key and adopting secure practices for its storage and management, users can ensure that their encrypted data remains protected while having a backup plan in case of emergencies.
Conclusion
In the world of Windows, password management plays a critical role in maintaining the security of user accounts, data, and systems. We have explored various locations where passwords are stored in Windows and learned about the security measures in place to protect them.
From the local user account passwords stored in the SAM database to the cached domain passwords in the Credential Manager, understanding where and how passwords are stored helps us appreciate the importance of strong and unique passwords.
We’ve also explored how passwords are managed in specific contexts, such as the Windows Subsystem for Linux (WSL), where Linux user account passwords are stored within the Linux environment.
The Credential Manager serves as a centralized repository for various types of credentials, including application passwords and network credentials, while Internet Explorer and Microsoft Edge provide password management features to simplify the login process for websites.
Additionally, we’ve learned about the secure storage of Wi-Fi network passwords on Windows and the critical role the BitLocker recovery key plays in unlocking encrypted drives.
By adopting best practices, such as regularly updating passwords, using strong and unique passwords, and enabling additional security features like multi-factor authentication, users can enhance the security of their accounts and data.
As technology advances and threats evolve, it’s essential to stay vigilant and up-to-date with the latest security practices. Regularly reviewing and removing unnecessary or outdated credentials, adjusting password policies, and educating users about password security can help ensure the continued protection of sensitive information.
By recognizing the value of password security and taking the necessary steps to strengthen it, individuals and organizations can maintain a robust security posture in the Windows environment.