Introduction
PHP, which stands for Hypertext Preprocessor, is a widely used programming language for web development. It is known for its versatility and flexibility, making it a popular choice among developers. However, with great power comes great responsibility, and PHP is not immune to security vulnerabilities.
One of the most common security risks associated with PHP is known as PHP injection. It is a type of web application vulnerability that allows an attacker to manipulate or exploit the PHP code running on a web server. This can lead to various malicious activities, such as unauthorized access, data theft, or executing arbitrary code.
Understanding PHP injection is crucial for web developers and website owners to ensure the security and integrity of their applications. By familiarizing themselves with the nature of PHP injection and implementing preventive measures, they can effectively protect their websites and users from potential attacks.
In this article, we will delve into the world of PHP injection, exploring its mechanics, common types, real-world examples, and how to detect and prevent it. By the end of this article, you will have a comprehensive understanding of PHP injection and be equipped with the knowledge to fortify your PHP applications against it.
What is PHP Injection?
PHP injection, also known as code injection or remote code execution, refers to a vulnerability in PHP applications that allows an attacker to insert malicious code into the server-side PHP scripts. This unauthorized code can cause a variety of issues ranging from data theft to complete system compromise.
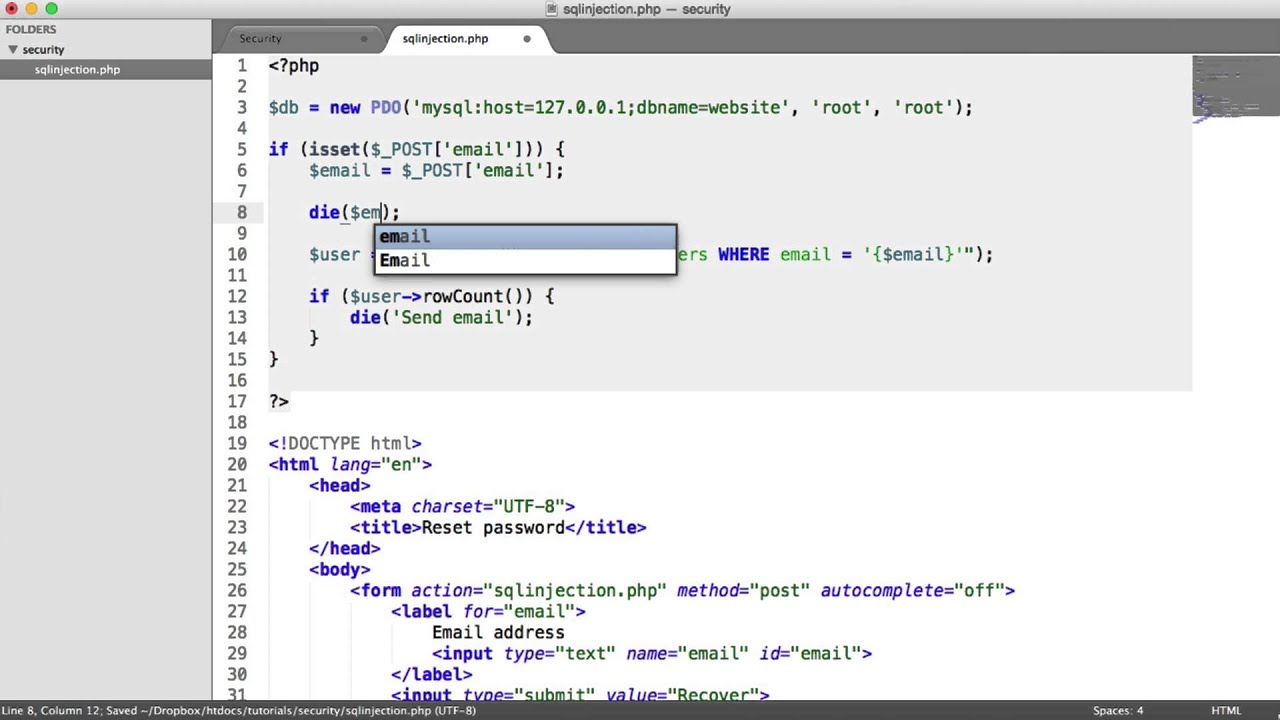
The basis of PHP injection lies in the fact that PHP is an interpreted language, meaning that the server executes the PHP code to generate dynamic web content. However, if the application does not properly validate and sanitize user input, attackers can manipulate that input to inject their own PHP code.
When an attacker succeeds in injecting malicious PHP code, it becomes part of the server-side script and is executed by the server along with the legitimate code. This can lead to a wide range of possible consequences, including:
- Gaining unauthorized access to sensitive information, such as databases or user accounts
- Modifying or deleting data stored on the server
- Executing arbitrary commands on the server
- Defacing the website by altering its content
- Installing backdoors or malware for persistent access
PHP injection can occur through various vectors, including user input fields, query parameters, cookies, and HTTP headers. Attackers often exploit vulnerabilities in the application code or take advantage of insufficient input validation and sanitization measures. It is important to note that both poorly secured custom code and outdated third-party libraries can be potential entry points for PHP injection attacks.
To mitigate the risk of PHP injection, developers need to adopt secure coding practices, including input validation, input sanitization, and the use of parameterized queries or prepared statements to prevent unintended code execution.
How does PHP Injection work?
PHP injection is often achieved by exploiting vulnerabilities in web applications that fail to properly sanitize and validate user input. Attackers take advantage of these vulnerabilities to inject malicious PHP code into the server-side scripts, which are then executed by the server.
Here’s a step-by-step breakdown of how PHP injection works:
- Identifying the vulnerable target: Attackers identify web applications running on a server that are vulnerable to PHP injection. They may use automated tools or conduct manual analysis to find potential targets.
- Understanding the application: Attackers analyze the web application to understand how user input is handled and processed by the PHP scripts. This involves identifying the points in the code where user input is used without proper validation or sanitization.
- Constructing the injection payload: Attackers create a payload consisting of malicious PHP code that they want to inject into the vulnerable point of the application. This code can include commands for data retrieval, database manipulation, or even remote system control through the server.
- Injecting the payload: Attackers submit the specially crafted input to the application, exploiting the vulnerability to inject the malicious PHP code. This can be done through input fields, query parameters, or other user-controllable elements in the application.
- Executing the injected code: Once the server receives the injected payload, it treats it as legitimate PHP code and executes it alongside the original code. This allows the attacker’s code to interact with the server’s environment and potentially carry out unauthorized actions.
Successful PHP injection attacks can have severe consequences, such as compromising privacy, stealing sensitive data, or taking control of the affected server. To prevent PHP injection, developers must implement strong input validation and sanitization techniques, as well as utilize secure coding practices to ensure the integrity of their applications.
Common Types of PHP Injection
PHP injection can take on various forms depending on the specific vulnerability being exploited. Here are some common types of PHP injection:
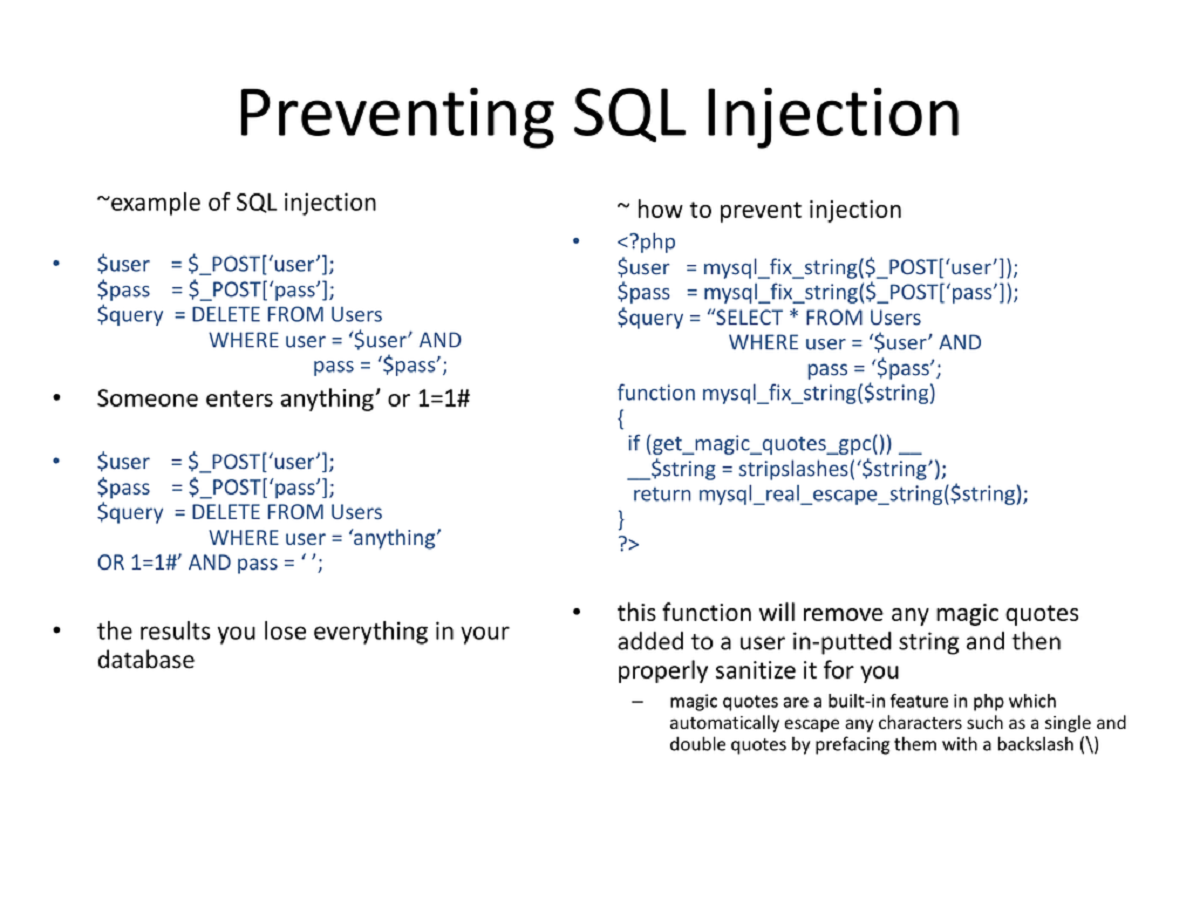
- SQL Injection: SQL injection is a type of PHP injection where attackers manipulate user input to modify or retrieve data from databases. By injecting malicious SQL queries, attackers can bypass authentication, extract sensitive information, or modify database records.
- OS Command Injection: OS command injection occurs when user input is passed directly into an operating system command without proper validation. Attackers can execute arbitrary commands on the server, potentially giving them full control over the system.
- File Include Injection: File include injection happens when attackers manipulate user input to include or execute arbitrary files on the server. This can lead to unauthorized code execution, information disclosure, or remote system compromise.
- Code Injection: Code injection involves injecting malicious PHP code into the server-side scripts, allowing attackers to execute arbitrary code on the server. This can lead to unauthorized access, data manipulation, or even complete server compromise.
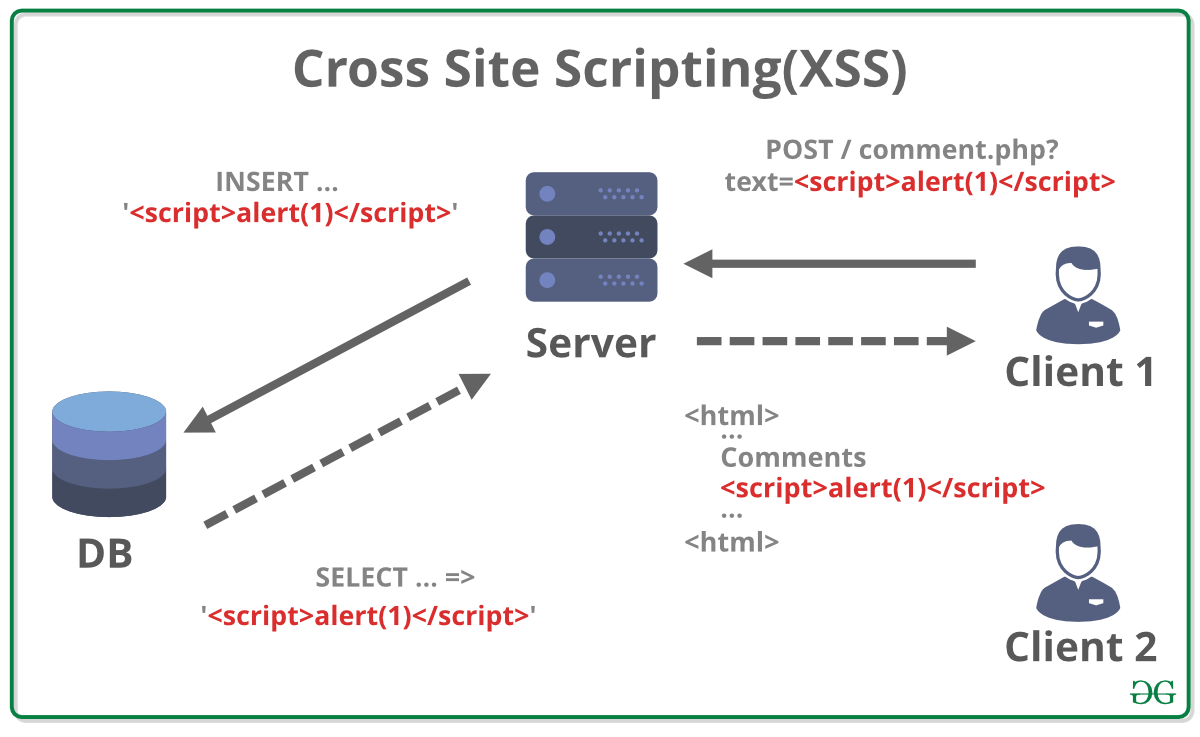
- XSS (Cross-Site Scripting): Although not directly a PHP injection, XSS attacks involve injecting malicious client-side scripts to exploit vulnerable PHP web applications. Attackers can steal user session cookies, deface websites, or redirect users to malicious sites.
- LDAP (Lightweight Directory Access Protocol) Injection: LDAP injection occurs when attackers manipulate user input to construct LDAP queries that are used for user authentication and directory access. By exploiting this vulnerability, attackers can bypass authentication or extract sensitive information from the LDAP directory.
It’s essential for developers and website owners to be aware of these common types of PHP injection vulnerabilities and take appropriate measures to prevent them. This includes implementing proper input validation and sanitization techniques, using parameterized queries, and keeping libraries and frameworks up to date.
Examples of PHP Injection Attacks
To understand the real-world impact of PHP injection, let’s explore some notable examples of PHP injection attacks:
- SQL Injection in User Login: In a web application’s login functionality, attackers can exploit SQL injection to bypass authentication and gain unauthorized access to user accounts. By injecting malicious SQL queries into the login form, they can manipulate the authentication process or extract sensitive information such as passwords.
- File Include Injection in File Upload: Many web applications allow users to upload files. In cases where the application does not properly validate and sanitize the file names or paths, attackers can inject malicious files that, when included or executed by the server, may lead to remote code execution or unauthorized access to the server’s file system.
- OS Command Injection in Form Input: Attackers can exploit OS command injection vulnerabilities when user input is directly passed into system commands. For example, in a web application’s search functionality, if the input is not properly validated or sanitized, an attacker could inject system commands within the search query to execute arbitrary commands on the server.
- XSS via PHP Injection: PHP injection attacks can facilitate cross-site scripting (XSS) vulnerabilities. For instance, if an application blindly echoes user input without proper HTML encoding, an attacker could inject malicious JavaScript code. When unsuspecting users visit the affected page, the injected code would execute in their browsers, potentially leading to session hijacking or defacement of the website.
- Code Injection via Unvalidated Form Input: When user input is directly included or evaluated as PHP code without proper validation, it can lead to code injection attacks. For example, if an application uses the PHP
eval()function on user-supplied data, an attacker could inject their own PHP code within the input, enabling arbitrary code execution on the server. - LDAP Injection in User Search: In systems implementing LDAP for user authentication or directory access, attackers may exploit LDAP injection vulnerabilities. By manipulating input fields like username or search queries, an attacker can inject LDAP commands to bypass authentication or retrieve sensitive information from the directory.
These examples highlight the variety of PHP injection attacks that can have severe repercussions for the security of web applications. By understanding these attack vectors, developers can implement the necessary measures to mitigate the risk of PHP injection vulnerabilities.
How to Detect and Prevent PHP Injection
Preventing PHP injection requires a proactive approach towards web application security. Here are some important steps to detect and prevent PHP injection vulnerabilities:
1. Input Validation: Implement robust input validation techniques to ensure that user input adheres to expected patterns and formats. Use whitelist validation where possible, allowing only specific characters or patterns in input fields, and rejecting anything that doesn’t meet the criteria.
2. Input Sanitization: Apply proper input sanitization methods to remove or escape potentially harmful characters from user input. For example, use functions like htmlspecialchars() to encode special characters in HTML entities and prevent cross-site scripting (XSS) attacks.
3. Use Prepared Statements or Parameterized Queries: Instead of directly embedding user input into SQL queries, use prepared statements or parameterized queries. These techniques separate the query structure from the user-provided values, preventing SQL injection attacks by automatically escaping special characters.
4. Avoid Dynamic Code Evaluation: Minimize or eliminate the use of functions like eval() or create_function() that execute code dynamically based on user input. Dynamic code evaluation greatly increases the risk of code injection vulnerabilities.
5. Keep Software Dependencies Up to Date: Regularly update and patch your PHP framework, libraries, and CMS (Content Management System) to benefit from the latest security fixes. Outdated software can have known vulnerabilities that attackers can exploit.
6. Implement Input Length and Type Checks: Validate the length and type of user input to ensure it matches the expected format. For example, validate email addresses using regular expressions and limit the maximum length of input fields to prevent buffer overflow or other potential vulnerabilities.
7. Use Web Application Firewalls (WAFs): Consider implementing a web application firewall that can detect and block common PHP injection attacks. WAFs analyze incoming web requests and apply security rules to filter out potentially malicious traffic.
8. Security Audits and Penetration Testing: Periodically conduct security audits and penetration tests on your PHP applications to identify and address any vulnerabilities. Engage security professionals to assess the security posture of your systems and provide recommendations for improving security.
9. Secure Coding Practices: Train your developers in secure coding practices, emphasizing the importance of input validation, parameterized queries, and secure coding practices. Promote an awareness of PHP injection vulnerabilities and provide guidelines for secure coding throughout the development process.
By following these best practices, developers and website owners can significantly reduce the risk of PHP injection vulnerabilities and enhance the overall security of their web applications.
Conclusion
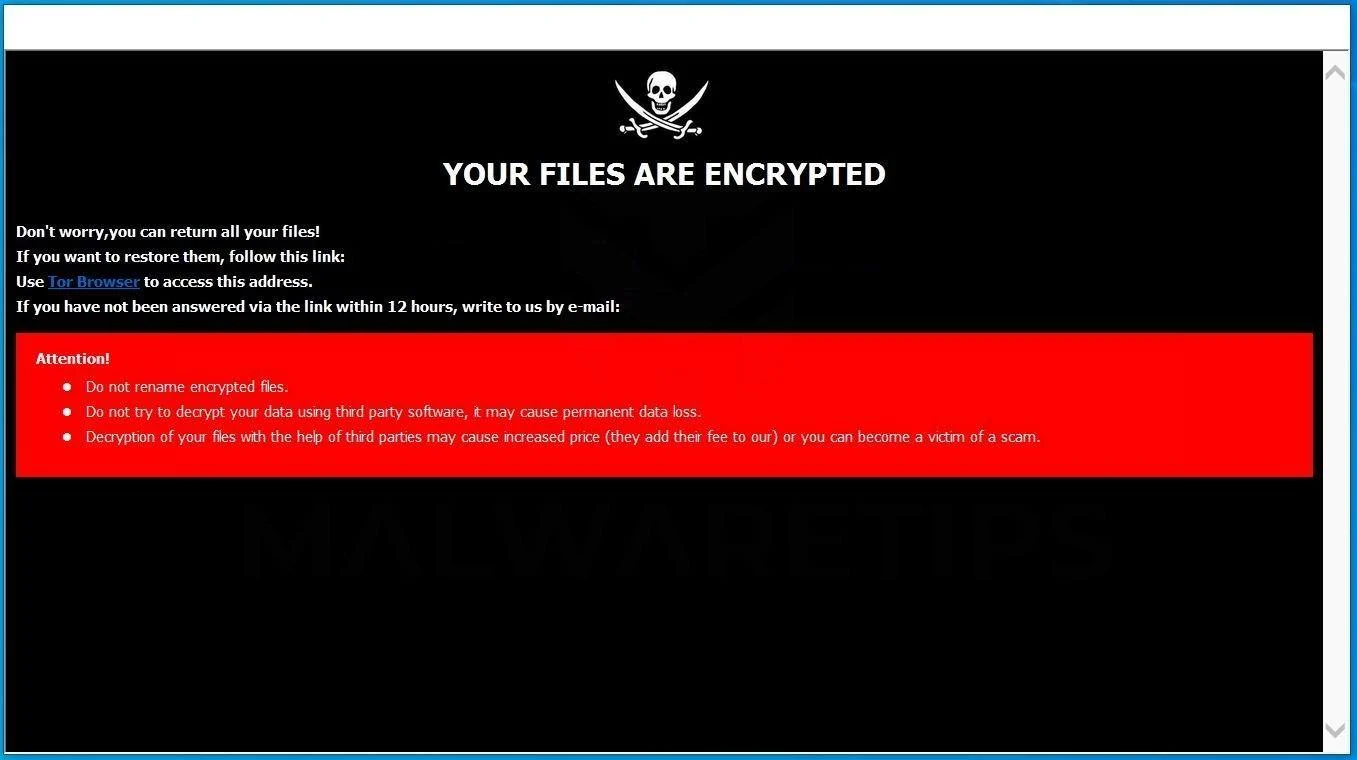
PHP injection poses a significant risk to the security of web applications. Failing to adequately protect against PHP injection can lead to unauthorized access, data breaches, and other malicious activities.
In this article, we explored the nature of PHP injection, how it works, common types of PHP injection, real-world examples of attacks, and methods to detect and prevent vulnerabilities.
It is crucial for developers and website owners to prioritize security measures and adopt best practices to mitigate the risk of PHP injection. This includes implementing input validation and sanitization, using parameterized queries, avoiding dynamic code evaluation, and keeping software dependencies up to date. Regular security audits, penetration testing, and educating developers about secure coding practices are essential components of a comprehensive approach to PHP injection prevention.
By taking proactive steps and staying vigilant, developers can protect their PHP applications from the risks associated with PHP injection and ensure the confidentiality, integrity, and availability of their websites and user data.