Introduction
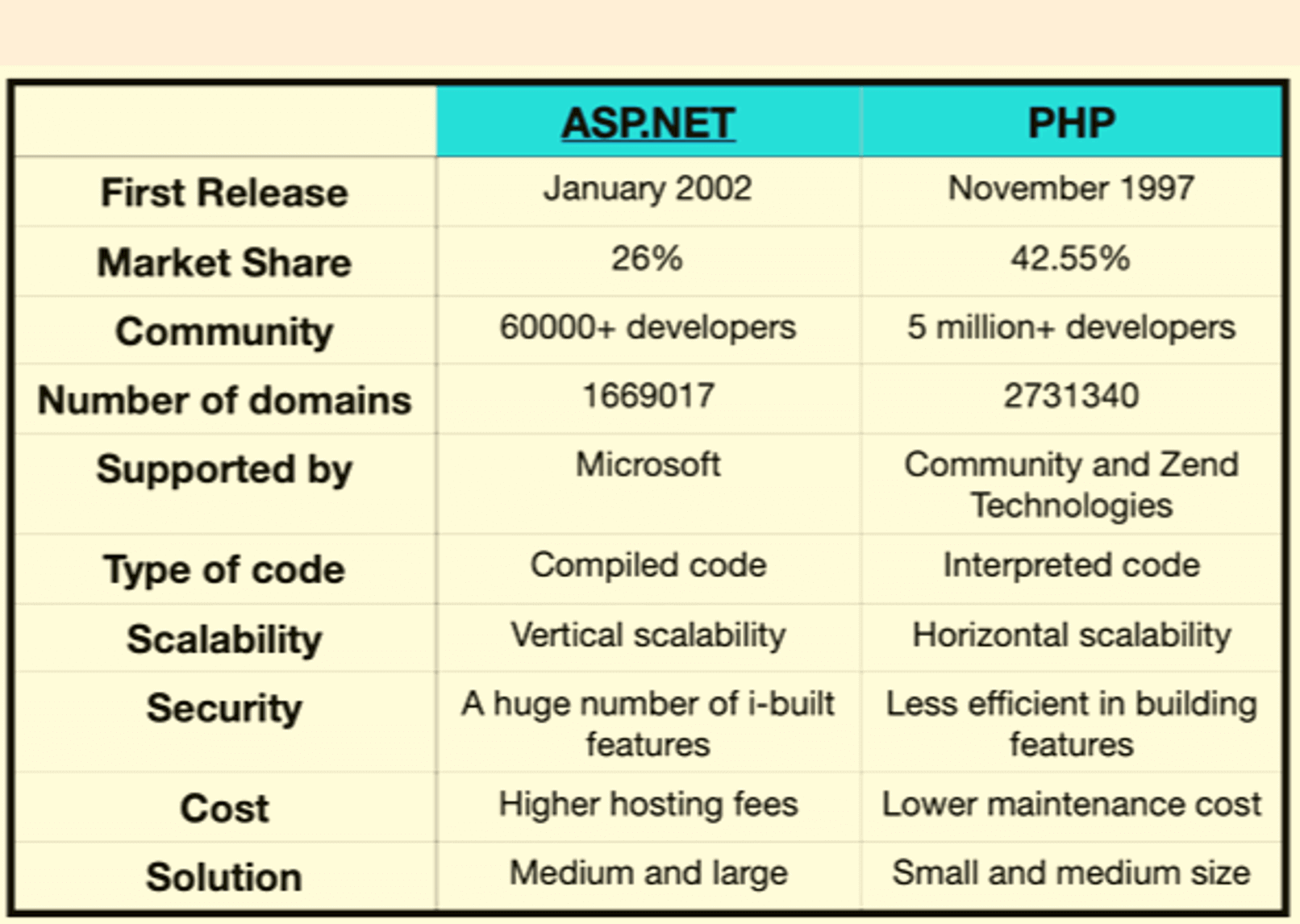
PHP is one of the most widely-used programming languages for building dynamic websites and web applications. However, its popularity also makes it a prime target for cyber attacks. Without proper security measures in place, PHP applications can be vulnerable to various threats, including hacking attempts, data breaches, and injection attacks.
To ensure the security of your PHP code and protect your website and users from potential harm, it is essential to follow best practices and implement robust security measures. In this article, we will explore a range of strategies and techniques to secure PHP applications.
From keeping your PHP installation up to date and applying secure coding practices to validating user input, implementing secure session handling, and protecting against common web vulnerabilities like cross-site scripting (XSS) and cross-site request forgery (CSRF), we will cover various aspects of PHP security. We will discuss the importance of using HTTPS for secure communication and protecting sensitive information, as well as how to handle file uploads, secure database connections, and prevent SQL injection attacks.
By following these security measures, you can significantly minimize the risk of potential attacks and ensure the integrity, confidentiality, and availability of your PHP applications. Let’s dive into the details of each strategy and learn how to secure PHP effectively.
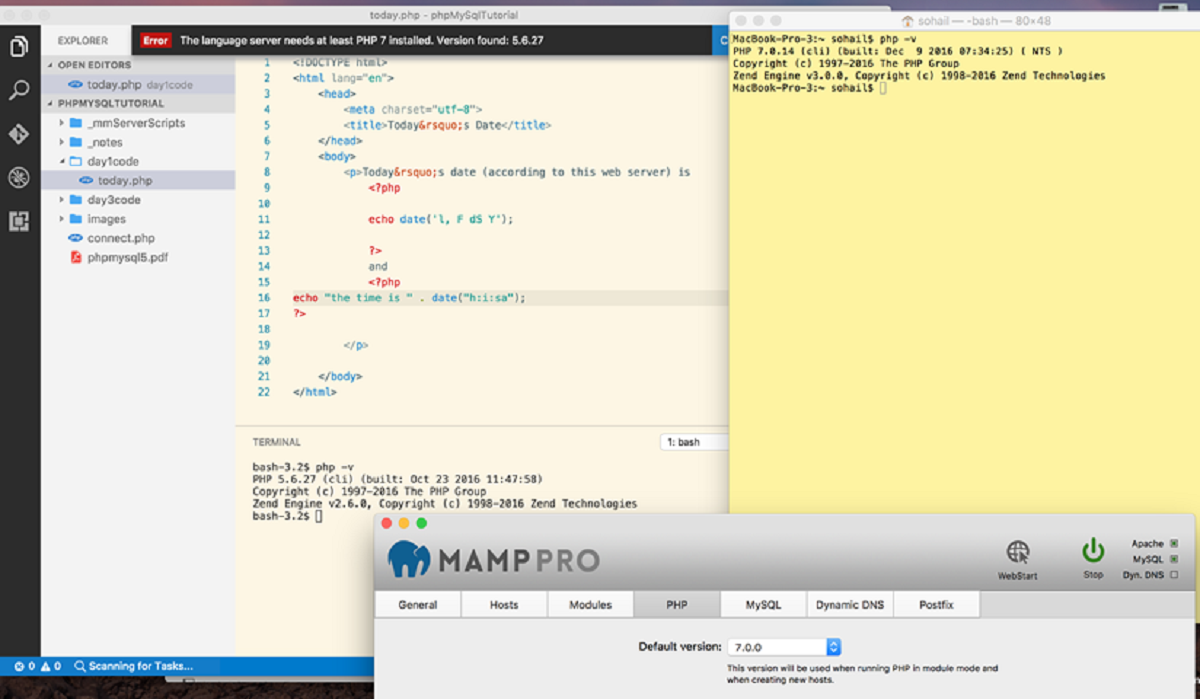
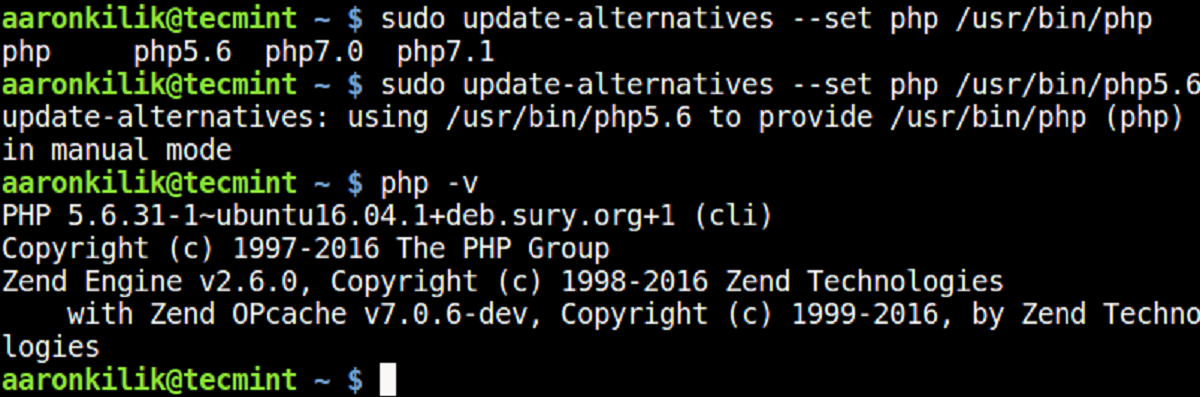
Use the Latest Version of PHP
Using the latest version of PHP is essential for ensuring the security of your applications. PHP developers regularly release new versions that include important security patches and bug fixes. These updates address known vulnerabilities and provide improved security features. By staying up to date with the latest PHP version, you can protect your application from potential exploits and vulnerabilities.
When a new version of PHP is released, it is important to upgrade your applications promptly. This involves testing your code with the new version to ensure compatibility and resolving any issues that may arise. Additionally, make sure to regularly update any third-party libraries or frameworks you use, as they may also release updates to address security vulnerabilities.
Using outdated versions of PHP can leave your application vulnerable to attacks, as attackers may exploit known vulnerabilities that have been patched in newer versions. Major releases of PHP, such as PHP 7, often come with significant security improvements and performance enhancements, making them a recommended choice for securing your applications.
Keep in mind that using the latest PHP version is just one aspect of maintaining a secure environment. It is important to combine this with other security practices, such as secure coding, input validation, and secure configuration, to provide comprehensive protection for your PHP applications.
Keep the PHP Installation Up to Date
Maintaining an up-to-date PHP installation is crucial for ensuring the security of your applications. Just as with any software, PHP releases regular updates that include security patches, bug fixes, and performance improvements. By keeping your PHP installation up to date, you can protect your application from known vulnerabilities and exploit attempts.
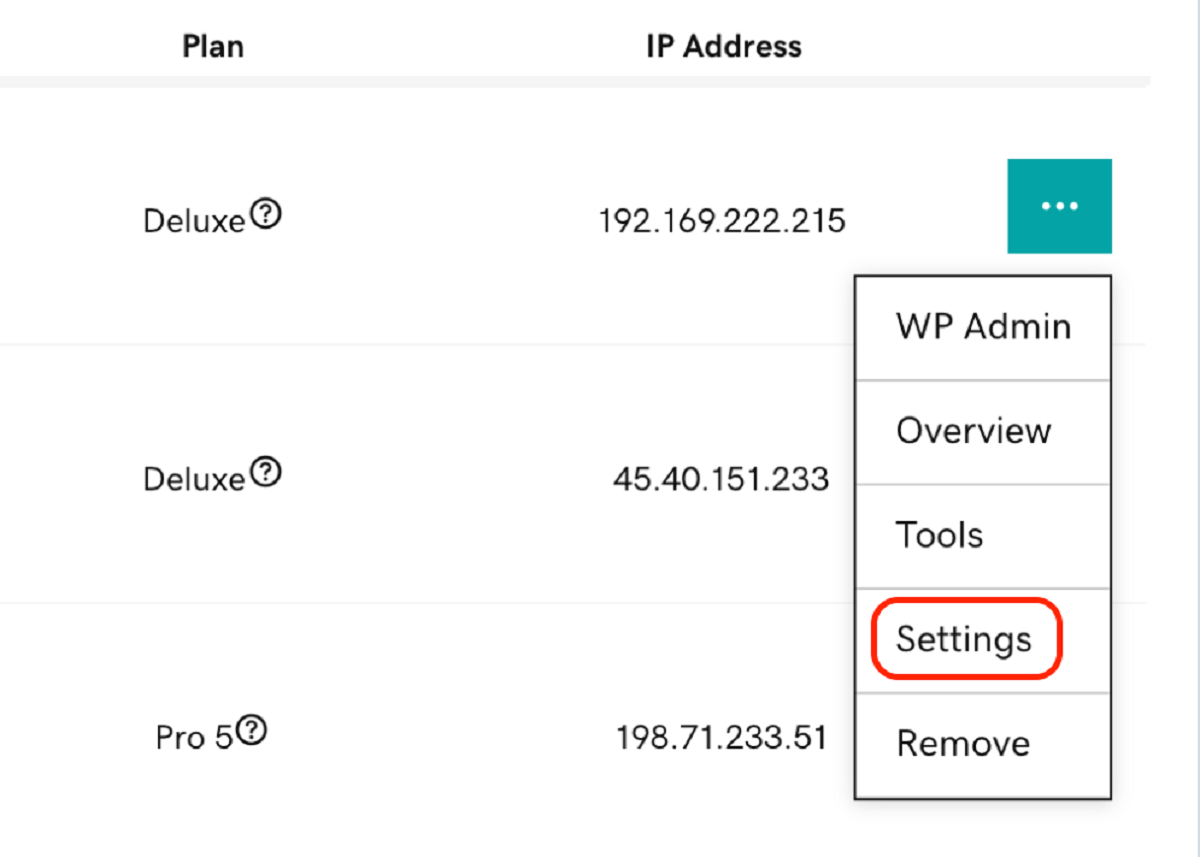
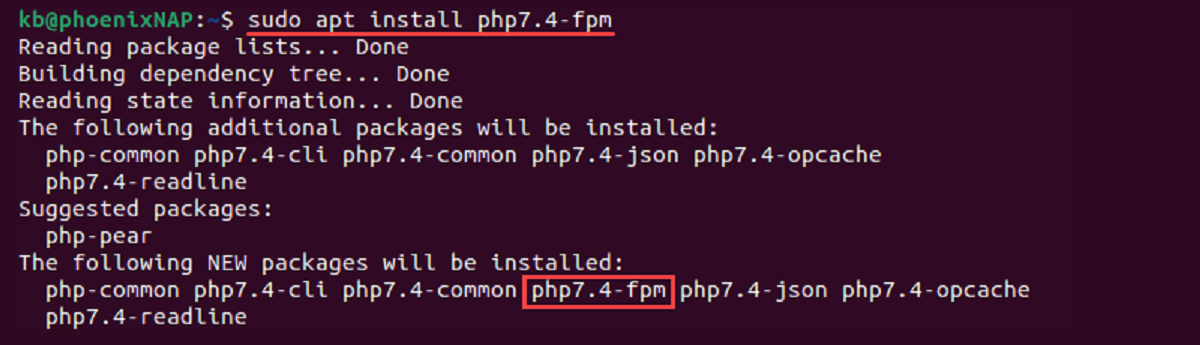
When a new version or patch is released, it is important to promptly update your PHP installation. Most hosting providers offer control panels or management tools that allow you to easily update PHP with a few clicks. Alternatively, if you manage your own server, you can refer to the official PHP documentation or your server’s documentation for guidance on how to update PHP to the latest version.
In addition to updating PHP itself, it is important to regularly update the associated PHP extensions and libraries. Many vulnerabilities are found in these components, and updating them to the latest versions can help mitigate potential security risks. Keep track of the extensions and libraries your application relies on and check for updates regularly.
By keeping your PHP installation and related components up to date, you ensure that security vulnerabilities are addressed promptly and reduce the risk of your application being compromised. However, it’s worth noting that updating PHP alone is not enough to guarantee complete security. It should be complemented with other security measures, such as secure coding practices, input validation, and secure server configurations, to create a robust defense against potential threats.
Use Secure Coding Practices
Adhering to secure coding practices is essential for developing PHP applications that are resilient to security threats. By following these practices, you can reduce the likelihood of introducing vulnerabilities and improve the overall security posture of your codebase.
One fundamental aspect of secure coding is to validate and sanitize user input. Always validate and sanitize user-supplied data before using it in your application to prevent common vulnerabilities like cross-site scripting (XSS) and SQL injection attacks. PHP provides various functions and libraries for input validation and sanitization, such as filter_var() and prepared statements, which should be used consistently throughout your code.
Another important practice is to use parameterized queries or prepared statements when interacting with the database. This helps protect against SQL injection attacks by ensuring that user-supplied data is treated as data and not as executable code.
Additionally, avoid using deprecated functions or features that may have known security vulnerabilities. Regularly review your codebase to identify and replace any deprecated functions or insecure coding practices.
It is also recommended to enable error reporting during development and testing but disable it in production environments. Displaying detailed error messages to users could reveal sensitive information or potential vulnerabilities.
Furthermore, implement proper access control and authentication mechanisms to ensure that only authorized users can access sensitive parts of your application. Apply the principle of least privilege, granting users only the privileges necessary for them to carry out their intended tasks.
Lastly, always validate and sanitize data before outputting it to the browser to prevent cross-site scripting (XSS) attacks. Utilize HTML encoding or output escaping functions, such as htmlspecialchars(), to ensure that user-generated content is properly sanitized before displaying it.
By applying these secure coding practices, you can significantly enhance the security of your PHP applications and reduce the risk of vulnerabilities that can be exploited by attackers.
Validate and Sanitize User Input
Validating and sanitizing user input is a crucial step in securing PHP applications. User input can often be manipulated or maliciously crafted to exploit vulnerabilities in the code. By properly validating and sanitizing user input, you can prevent common attacks such as Cross-Site Scripting (XSS) and SQL injection.
When receiving user input, it is essential to validate it to ensure it meets the expected format and restrictions. This includes validating the data type, length, and any specific criteria relevant to the input field. PHP provides various built-in functions and filters, such as filter_var() and regular expressions, to assist in input validation.
Sanitizing user input involves removing or encoding any potentially malicious characters or code that could be used to execute attacks. Depending on the context, different sanitization techniques may be required. For instance, when dealing with user-generated content that will be displayed as HTML, the htmlspecialchars() function can be used to encode special characters and prevent XSS attacks.
When handling user input that will be used in database queries, it is crucial to use prepared statements or parameterized queries. This prevents SQL injection attacks by ensuring that user-supplied data is treated as data and not executable code.
Aside from validating and sanitizing user input at the server-side, it is also necessary to consider client-side validation using JavaScript or HTML5 input validation attributes. While client-side validation provides immediate feedback to users, server-side validation is essential to prevent bypassing of client-side checks and ensure the integrity of the data.
By implementing robust input validation and sanitization practices, you can significantly reduce the risk of security vulnerabilities in PHP applications. Remember to validate all user input, sanitize data before using it, and use proper techniques to prevent attacks like XSS and SQL injection. These measures, combined with other security strategies, help ensure the overall security and reliability of your PHP application.
Enable Error Reporting and Logging
Enabling error reporting and logging is an essential step in maintaining the security and stability of your PHP applications. Error reporting helps you identify and address any issues or vulnerabilities in your code, while logging allows you to track and analyze system behavior for debugging and security purposes.
By enabling error reporting, you ensure that PHP displays any runtime errors and warnings, providing valuable information about potential vulnerabilities or coding mistakes. This helps you identify and fix issues early on, preventing them from being exploited by attackers. In your development and staging environments, it is recommended to set the error_reporting directive in your PHP configuration file to report all errors, warnings, and notices.
However, in a production environment, it is advisable to disable error reporting for the end-user. Instead, you should log errors to a secure and separate location. This allows you to gather crucial information about errors, including the timestamp, error message, and the file and line number where the error occurred.
Logging is important not only for identifying errors but also for detecting security incidents and suspicious activities. By analyzing logs, you can gain valuable insights into potential attacks and take appropriate measures to mitigate them. Make sure your logs include relevant information such as user actions, login attempts, and critical system events.
It is crucial to secure log files and ensure they are not accessible to unauthorized users. Store logs in a separate directory with restricted permissions and consider encrypting sensitive log information, such as user credentials or personally identifiable information (PII).
Additionally, consider implementing a log analysis and monitoring system to automate the process of reviewing and analyzing logs. This can help you detect patterns or anomalies that may indicate malicious activity or potential security breaches. There are various tools available for log analysis, such as Elasticsearch, Logstash, and Kibana (ELK stack).
Enabling error reporting and logging in your PHP applications allows you to proactively identify and address coding errors, vulnerabilities, and potential security incidents. By monitoring and analyzing logs, you can maintain the integrity and security of your application while simultaneously gaining valuable insights into its behavior.
Protect Sensitive Information
Protecting sensitive information is of utmost importance in PHP applications to prevent unauthorized access and data breaches. Sensitive information can include user credentials, payment details, personal information, or any other data that, if compromised, could lead to significant harm.
One crucial step in protecting sensitive information is to avoid storing it in plain text. Passwords, for example, should never be stored in their original form. Instead, use secure hashing algorithms like bcrypt or Argon2 to hash user passwords before storing them in the database. When a user logs in, the entered password can be hashed again and compared to the stored hashed password for authentication.
Another important aspect is the secure handling of session data. Session hijacking or session fixation attacks can occur if session IDs are not properly protected. Use secure session handling techniques, such as regenerating session IDs after each successful login and storing them securely (e.g., in encrypted cookies or server-side storage). Also, consider using session timeouts and mechanisms to detect and prevent session hijacking.
When transmitting sensitive information over a network, it is crucial to use secure communication protocols such as HTTPS. HTTPS encrypts the data exchanged between the webserver and the client, ensuring that it remains confidential and protected from eavesdropping or tampering. Obtain and install an SSL/TLS certificate for your domain to enable HTTPS on your website.
In addition, be cautious about the information that you expose in error messages. Avoid displaying sensitive details, such as database connection credentials or stack traces, in error messages. Instead, provide generic error messages to users while logging the detailed error information for administrative purposes.
Furthermore, ensure that sensitive data is appropriately handled in your code. Avoid unnecessary logging of sensitive information and strictly control access to systems or files that store or process sensitive data.
Regularly test the security of your application to identify vulnerabilities. Conduct penetration testing and security audits to uncover potential weaknesses in your application’s defense mechanisms. Use tools like OWASP ZAP or Burp Suite to perform security scans and vulnerability assessments.
By taking proper measures to protect sensitive information, you can mitigate the risk of data breaches and unauthorized access. Implementing secure storage and transmission strategies, secure session handling, and practicing good coding practices will help safeguard your PHP application and the sensitive information it processes.
Implement Secure Session Handling
Secure session handling is crucial for protecting user sessions and preventing unauthorized access to sensitive information in PHP applications. A session is a way to store user-specific data across multiple HTTP requests, allowing the application to maintain stateful interactions with users.
One of the first steps in secure session handling is ensuring that session IDs are securely generated. Use a cryptographically secure random number generator to generate session IDs that are long and unpredictable. PHP provides the function session_regenerate_id() to generate a new session ID and invalidate the old one. It is recommended to regenerate the session ID after a user logs in or changes their privilege level to prevent session fixation attacks.
It is essential to store session data securely, either server-side or using secure encrypted cookies. Server-side storage ensures that session data remains on the server and is not accessible to clients. Avoid storing sensitive data in session variables whenever possible. Instead, store a reference or identifier that can be used securely to retrieve the required data from the server.
Implement measures to prevent session hijacking or session replay attacks. One approach is to use mechanisms that bind session data to client characteristics, such as the client’s IP address or user-agent. However, be aware that this method may not be foolproof, as clients can change IP addresses, and user-agents can be modified.
Another crucial consideration is setting proper session timeouts. Sessions should expire after a certain period of inactivity to reduce the risk of unauthorized access if a user forgets to log out. Set a reasonable timeout period, depending on the requirements of your application, to balance security and user experience.
In addition to session timeouts, implement mechanisms to detect and prevent session hijacking. One such approach is tracking session activity and comparing it with the user’s behavior. If activity patterns deviate significantly, consider terminating or re-authenticating the session to prevent unauthorized access.
Regularly monitor session logs and review session-related activities for suspicious or anomalous behavior. Analyzing session logs can help identify potential security incidents and allow for timely response and mitigation.
Finally, be aware of session-related vulnerabilities, such as session fixation and session sidejacking attacks. Stay informed about the latest security best practices and keep your PHP application updated with the latest security patches and fixes.
By implementing secure session handling techniques, you can protect user sessions from unauthorized access and maintain the integrity and confidentiality of the data stored within them. Secure session handling is a critical component of overall application security and should be given due attention in PHP development.
Handle File Uploads Securely
Handling file uploads securely is essential in PHP applications to prevent potential security vulnerabilities and protect against malicious attacks. File uploads can pose a significant risk if not properly validated and processed.
First and foremost, thoroughly validate all uploaded files to ensure they meet the specified criteria. Perform checks on the file size, file type, and file name to prevent the upload of malicious files or files that may cause issues within your system. Utilize PHP functions like $_FILES[‘file’][‘size’] and mime_content_type() to validate file size and file type, respectively.
Implement proper file extension checking to prevent the upload of potentially dangerous file types. Restrict uploads to specific file extensions that your application expects and deny any suspicious or potentially harmful file types. This can be achieved by maintaining a whitelist of allowed file extensions and comparing the uploaded file against it.
Consider using a secure temporary storage location for uploaded files before further processing or validation. This helps prevent direct access to uploaded files and allows you to perform additional security checks before moving the files to their permanent storage location.
Scan uploaded files for malware or malicious code using antivirus or malware scanning tools. These tools can identify potentially harmful files and prevent them from being processed or stored on your server. Additionally, keep your antivirus software up to date to ensure it can detect the latest threats.
Avoid storing uploaded files in a publicly accessible directory, as this can allow unauthorized access or execution of the files. Instead, store uploaded files in a separate folder outside of the web root directory and use appropriate file permissions to restrict access to them.
When displaying or serving uploaded files to users, ensure that proper content-disposition headers are set to prevent browser execution of potentially malicious files. This helps protect against attacks such as remote code execution.
Regularly monitor and review the file upload functionality in your application for any potential vulnerabilities or security risks. Stay up to date with the latest security advisories and patches related to file upload vulnerabilities, and promptly apply any necessary fixes.
By implementing these secure file upload practices, you can significantly reduce the risk of malicious file uploads and protect your PHP application and server from potential security threats. Handling file uploads securely is an imperative aspect of overall application security and should be given careful consideration.
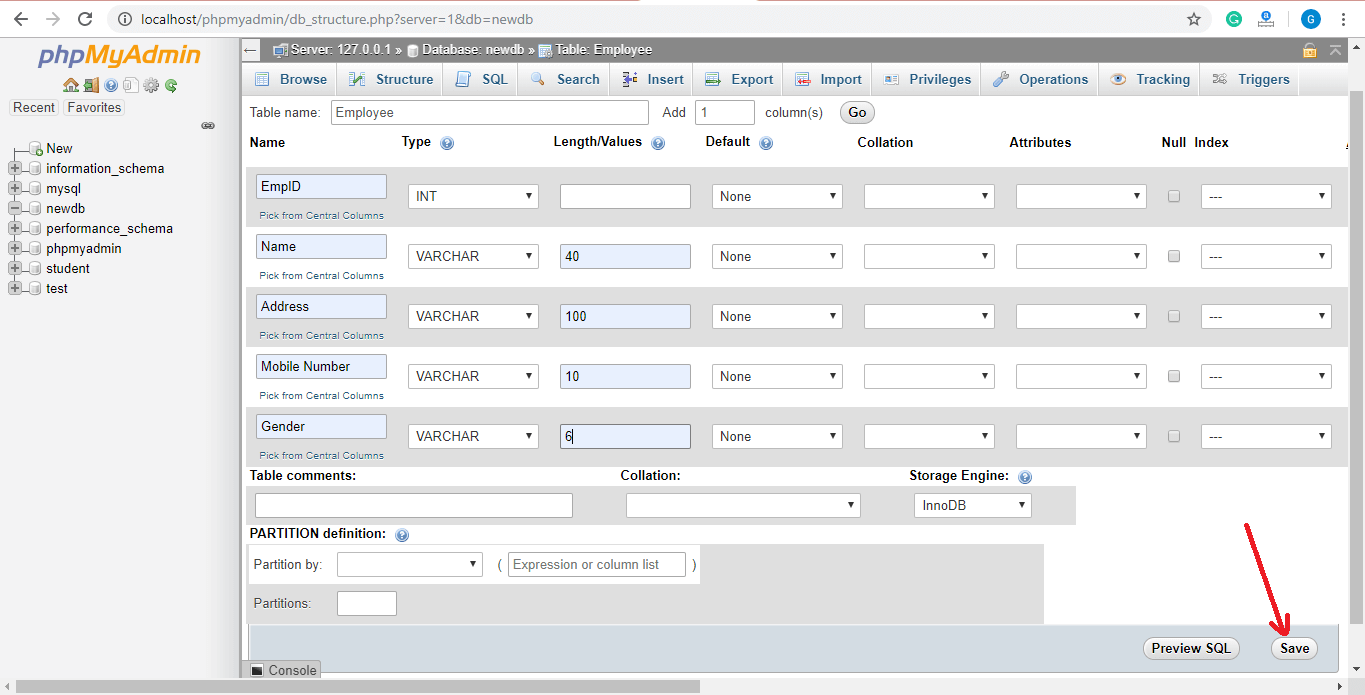
Secure Database Connections
Securing database connections is crucial for protecting sensitive data stored in a PHP application. It ensures that data is transmitted securely and access to the database is restricted to authorized users only.
One fundamental step in securing database connections is to use a secure and encrypted protocol such as SSL/TLS. Encrypting the communication between your PHP application and the database server prevents eavesdropping and unauthorized access to sensitive data transmitted over the network.
Ensure that your database server is configured to accept only secure connections and that SSL/TLS certificates are properly installed and configured. Verify that your PHP application is configured to use the encrypted connection by enabling SSL/TLS support in the database connection settings.
Implement proper authentication mechanisms for accessing the database. Avoid using default or weak database credentials, and instead, use strong and unique passwords. Additionally, consider using more advanced authentication methods, such as certificate-based authentication or multifactor authentication (MFA), to add an extra layer of security.
Avoid embedding database credentials directly into your source code. Store them securely in environment variables or configuration files outside of the web root directory. This prevents unauthorized access to the database in case of a code injection or disclosure vulnerability.
Implement the principle of least privilege by ensuring that database users have only the necessary privileges required by your PHP application. Granting excessive database privileges can increase the risk of unauthorized access or data manipulation in case of a successful attack.
Regularly update your database server to ensure that you have the latest security patches and fixes. Stay informed about any known vulnerabilities related to your specific database software and promptly apply any necessary updates.
Use parameterized queries or prepared statements when interacting with the database to prevent SQL injection attacks. These techniques ensure that user-supplied data is treated as data and not executable code, mitigating the risk of unauthorized database access or data manipulation.
Implement proper error handling and logging when dealing with database connections and queries. Avoid displaying detailed database error messages to users, as they can reveal sensitive information and potentially provide attackers with valuable insights into your database structure and configuration.
Regularly monitor and review the database connection settings and access controls to identify any potential vulnerabilities or misconfigurations. Conduct regular security audits and vulnerability assessments to ensure the ongoing security of your database environment.
By following these best practices for securing database connections, you can protect sensitive data stored in your PHP application and reduce the risk of unauthorized access or data breaches. A secure database connection is a critical component of ensuring the overall security and integrity of your PHP application.
Use HTTPS for Secure Communications
Using HTTPS (Hypertext Transfer Protocol Secure) is crucial for ensuring secure communications between a PHP application and its users. It provides encryption and authentication, making it a vital component of overall application security.
HTTPS uses SSL/TLS protocols to encrypt the data transmitted between a webserver and a client’s browser. This encryption prevents unauthorized access, eavesdropping, and tampering with sensitive information exchanged during communication.
Implementing HTTPS requires obtaining an SSL/TLS certificate for your domain. You can obtain a certificate from a trusted Certificate Authority (CA) or use a free certificate from services like Let’s Encrypt. Once you have the certificate, install and configure it on your webserver.
When HTTPS is enabled, all data transmitted between the server and the client, including passwords, credit card information, and other sensitive data, is encrypted. This helps protect user privacy and prevents sensitive information from being intercepted or stolen.
In addition to encryption, HTTPS provides authentication, ensuring that users are communicating with the genuine and legitimate server. This prevents man-in-the-middle attacks where an attacker intercepts and impersonates the server to gain access to sensitive data.
Using HTTPS is particularly important when handling sensitive user data, such as login credentials, personal information, or financial transactions. It not only protects your users but also enhances their trust in your application and brand.
Enabling HTTPS for your PHP application is relatively straightforward. Update your application’s URLs to use the HTTPS protocol (e.g., https://www.example.com) and ensure that all internal links and resources are also served over HTTPS. Consider implementing HTTP to HTTPS redirect rules to automatically redirect users to the secure version of your site.
Regularly verify the SSL/TLS configuration of your webserver using online tools or security scanners to identify any potential security vulnerabilities or configuration issues that could compromise the security of your HTTPS connections.
Lastly, keep in mind that adopting HTTPS is not only a security practice but also an essential ranking signal for search engines. Google, for example, considers HTTPS as a positive ranking factor, rewarding websites that prioritize secure communication with higher visibility in search results.
By using HTTPS for secure communications, you can enhance the overall security and privacy of your PHP application. It ensures the protection of sensitive data, establishes trust with your users, and improves your website’s visibility and reputation.
Protect Against Cross-Site Scripting (XSS) Attacks
Protecting against Cross-Site Scripting (XSS) attacks is crucial for maintaining the security of PHP applications. XSS attacks occur when malicious scripts are injected into web pages and executed in a user’s browser, allowing attackers to steal sensitive information, manipulate user interactions, or carry out other malicious activities.
Implement strict input validation and output encoding measures to prevent XSS attacks. All user-supplied data, including form inputs, query parameters, and data retrieved from the database, must be properly validated and sanitized before being displayed on web pages. Utilize functions like htmlspecialchars() or HTML Purifier to encode user input and prevent the execution of any injected scripts.
Avoid using user-supplied data directly in dynamic HTML or JavaScript code. If you need to incorporate user data, ensure it is properly sanitized and validated before including it. Utilize appropriate HTML entity encoding or JavaScript escaping techniques to prevent script execution.
Implement Content Security Policy (CSP) to mitigate XSS attacks. CSP is a security mechanism that allows you to define and enforce a policy to restrict the types of content that can be loaded by a web page, including inline scripts and external resources. By configuring CSP, you can minimize the risk of XSS vulnerabilities and reduce the impact of successful attacks.
Keep your PHP application and associated libraries up to date to address any known XSS vulnerabilities. Stay informed about security advisories and promptly apply any necessary patches or updates to ensure you are protected against the latest threats.
Regularly perform security testing, including vulnerability scanning and penetration testing, to identify any potential XSS vulnerabilities in your PHP application. Tools like OWASP ZAP or Burp Suite can assist in scanning for common vulnerabilities and provide insights into possible areas of improvement.
Implement secure coding practices, including input validation and output encoding, as part of your development process. Train your development team about secure coding guidelines and encourage the use of secure coding frameworks and libraries that assist in preventing XSS attacks.
Consider utilizing a web application firewall (WAF) to provide an additional layer of protection against XSS attacks. A WAF can help detect and block malicious requests attempting to exploit XSS vulnerabilities, providing an extra line of defense for your PHP application.
Regularly monitor and review your web server logs for any suspicious activities or indicators of potential XSS attacks. Promptly investigate and respond to any identified security incidents to ensure the integrity and security of your application.
By taking these measures to protect against XSS attacks, you can fortify your PHP application and mitigate the risk of unauthorized script execution. Protecting against XSS vulnerabilities is crucial for maintaining the confidentiality, integrity, and availability of your application and safeguarding your users’ sensitive information.
Prevent Cross-Site Request Forgery (CSRF) Attacks
Preventing Cross-Site Request Forgery (CSRF) attacks is essential for maintaining the security and integrity of PHP applications. CSRF attacks occur when a malicious website tricks a user’s browser into making an unintended request to a target application, using the user’s authenticated credentials without their knowledge or consent.
Implementing CSRF protection mechanisms is crucial to prevent such attacks. One common method is to generate and validate anti-CSRF tokens for each user session. An anti-CSRF token is a unique value that is associated with a user’s session and included in each form or request. When a request is made, the server validates the token to ensure that it matches the expected value for the user’s session.
To generate an anti-CSRF token, utilize a strong cryptographic random number generator to generate a random value. Store this token in the user’s session data and also include it as a hidden field in each form or add it to each request as a header. Upon receiving a request, validate the token to ensure it matches the expected value stored in the user’s session.
Ensure that your PHP application enforces the same-origin policy in combination with CSRF protection. The same-origin policy limits interactions between different websites, preventing requests from an unauthorized origin.
Consider implementing the “Referer” header check as an additional layer of CSRF protection. The Referer header includes the URL of the page making the request and can be used to verify that the request originated from an authorized page on your own domain. However, note that the Referer header can be easily manipulated and may not be reliable as a standalone protection mechanism.
Regularly review your application’s codebase, including forms and requests, to ensure that all sensitive actions and operations are appropriately protected against CSRF attacks. Make sure that any action that modifies data or performs critical operations requires proper CSRF protection.
Implement secure coding practices and follow secure session handling techniques to reduce the risk of CSRF attacks. By ensuring that session IDs are securely generated, regenerated after login, and invalidated after logout, you can minimize the potential impact of CSRF attacks.
Educate your users about CSRF attacks and encourage them to be cautious when clicking on unfamiliar links or visiting unknown websites. By raising awareness, users can become an active line of defense against potential CSRF threats.
Perform thorough security testing and vulnerability assessments, including CSRF testing, as part of your regular security assessments. Tools like OWASP ZAP or Burp Suite can help identify potential CSRF vulnerabilities and assist in implementing appropriate countermeasures.
Regularly monitor and review your logs for any suspicious activities or indicators of potential CSRF attacks. Implement monitoring systems that can raise alerts or flag any unusual or unexpected activity.
By implementing proper CSRF protection measures, you can significantly reduce the risk of unauthorized actions and maintain the integrity of your PHP application. Preventing CSRF attacks is an essential aspect of overall application security and should be given utmost attention during development and maintenance.
Use a Content Security Policy (CSP)
Implementing a Content Security Policy (CSP) is a powerful defense against various types of attacks, including Cross-Site Scripting (XSS), data injection, and clickjacking. CSP allows you to define and enforce a policy that specifies the sources from which content can be loaded on your PHP application, thereby reducing the risk of security vulnerabilities.
A Content Security Policy is implemented using an HTTP response header that instructs the browser to only load content from trusted sources. By specifying trusted sources for scripts, stylesheets, images, fonts, and other resources, you can prevent malicious external resources from being loaded and executed on your web pages.
Implementing a strong CSP involves carefully crafting the policy to meet the specific needs of your PHP application. Start by setting a default-src directive that restricts the sources from which all types of content can be loaded. Additional directives, such as script-src, style-src, img-src, and font-src, can be used to further refine the trusted sources for specific types of content.
Avoid using the ‘unsafe-inline’ and ‘unsafe-eval’ keywords in your CSP directives, as they allow the execution of inline scripts and dynamic code evaluation, respectively. Instead, rely on external scripts and properly encoded data to achieve the desired functionality.
Consider implementing the ‘report-uri’ or ‘report-to’ directive to collect reports about policy violations. These reports can provide valuable insights into attempted security breaches and help you identify and address any potential vulnerabilities in your PHP application.
Test and validate your CSP implementation thoroughly across different browsers to ensure compatibility and effectiveness. Consider utilizing the Content-Security-Policy-Report-Only header initially to test the impact of your CSP without blocking any content. This allows you to identify and address any issues without impacting user experience.
Regularly review and adjust your CSP as necessary, especially when making changes or additions to your web application. New features or external dependencies may require updates to the CSP to allow the necessary content to be loaded securely.
Keep in mind that implementing a CSP is not a one-time solution. It should be considered as an integral part of your overall security strategy that requires ongoing monitoring, maintenance, and updates to address evolving security threats.
CSP is a powerful security feature that adds an additional layer of protection to your PHP application. By implementing a restrictive and well-defined Content Security Policy, you can mitigate the risk of various web-based attacks and ensure the integrity and security of your application and its users.
Implement Password Hashing and Salting
Implementing proper password hashing and salting techniques is essential for protecting user credentials and preventing unauthorized access to PHP applications. Password hashing transforms user passwords into irreversible strings of characters, making it extremely difficult for attackers to reverse-engineer the original passwords.
When storing user passwords, avoid using simple or reversible encryption techniques. Instead, utilize strong cryptographic hash functions like bcrypt or Argon2. These algorithms incorporate a built-in salt, which adds an extra layer of security to the hashing process.
A salt is a randomly generated string of characters that is appended to the user’s password before hashing. Each user’s password is hashed with a unique salt value, even if the passwords are the same. The salt value is typically stored alongside the hashed password, allowing the verification process to replicate the same hashing process.
Salting prevents attackers from using precomputed tables, known as rainbow tables, to crack passwords. The unique salt for each user ensures that even if multiple users have the same password, the resulting hashes will be different.
It is crucial to use a secure random number generator to generate the salt. PHP provides the function password_hash() to hash passwords and automatically generate a random salt. Use the PASSWORD_BCRYPT algorithm option for bcrypt hashing or PASSWORD_ARGON2I for Argon2.
To verify passwords during the authentication process, use the password_verify() function. This function compares a user-supplied password with the stored hashed password and validates the authenticity.
Periodically review password security practices and encourage users to follow good password hygiene. Enforce password complexity requirements, such as a minimum length and a mix of uppercase and lowercase letters, numbers, and special characters.
Consider implementing a password reset policy that requires users to change their passwords periodically. This ensures that compromised passwords are not valid indefinitely and adds an extra layer of protection in case of a data breach or unauthorized access.
Protect password-related operations in transit with secure communication protocols like HTTPS. This prevents eavesdropping and ensures that passwords are transmitted securely between the user’s browser and the server.
Regularly educate users on the importance of creating strong and unique passwords. Provide guidance on password best practices and discourage the use of common or easily guessable passwords.
By implementing password hashing and salting techniques, you significantly increase the security of your PHP application. Password hashing with unique salts makes it extremely difficult for attackers to obtain user passwords, protecting both your users and the integrity of your application.
Protect Against SQL Injection Attacks
Protecting against SQL injection attacks is critical for securing PHP applications that interact with databases. SQL injection occurs when malicious SQL code is injected into database queries through user-supplied input. This can lead to unauthorized access, data breaches, data manipulation, or even complete compromise of the database.
Implement prepared statements or parameterized queries to mitigate the risk of SQL injection attacks. Prepared statements separate the SQL code from the user-supplied input, treating the input as data rather than executable code. This ensures that user input is properly sanitized and prevents attackers from injecting malicious SQL code.
Avoid using user input directly in SQL queries. Instead, utilize placeholders and bind the actual values when executing the query. PHP provides prepared statement APIs, such as PDO (PHP Data Objects) and mysqli, which automatically handle parameterized queries.
Sanitize and validate user input to avoid accepting malicious data. Use functions like filter_var() or regular expressions to validate user input and reject any input that does not meet the expected format or pattern.
Strictly limit the privileges of the database user used by your PHP application. Grant the minimum necessary permissions required for the application’s functionality. This reduces the potential impact of SQL injection attacks by restricting the actions an attacker can perform even if successful.
Never trust user input. Implement input validation both in client-side JavaScript and server-side PHP code. Client-side validation improves the user experience by providing immediate feedback, but server-side validation is essential to prevent bypassing of client-side checks.
Regularly update your PHP application and database software to address any known vulnerabilities related to SQL injection attacks. Stay informed about security advisories and promptly apply any necessary patches or updates to ensure you are protected against the latest threats.
Implement proper error handling and logging to detect and respond to SQL injection attacks. Log SQL errors and failures, but avoid divulging any sensitive information in error messages that could be exploited by attackers.
Employ web application firewalls (WAFs) as an additional layer of defense against SQL injection attacks. WAFs can detect and block malicious SQL injection attempts, providing an extra line of protection for your PHP application.
Regularly test your PHP application for SQL injection vulnerabilities using security testing tools or by engaging third-party security professionals. Conduct penetration tests, vulnerability assessments, and code reviews to identify and remediate any potential SQL injection vulnerabilities.
By implementing these measures to protect against SQL injection attacks, you can significantly reduce the risk of unauthorized database access and maintain the integrity and security of your PHP application’s data.
Secure File and Directory Permissions
Securing file and directory permissions is crucial for protecting PHP applications and ensuring the confidentiality and integrity of sensitive data. Properly setting file and directory permissions helps prevent unauthorized access and limits potential damage that could be caused by malicious actors.
Grant the least privileges necessary for files and directories to function correctly. Avoid giving global or excessive permissions that could allow unauthorized users to read, write, or execute files they should not have access to.
Set appropriate permissions for files and directories based on their intended use. Generally, directories should have execute permissions to allow traversal, while files should have read and write permissions limited to authorized users or processes.
Avoid granting write permissions to files or directories that don’t require it. Unnecessary write permissions could potentially lead to unauthorized modifications or tampering of critical files.
Regularly review and audit file and directory permissions to identify any misconfigurations or vulnerabilities. Automated tools like Tripwire or manual inspections can help identify file permission issues and detect unauthorized changes in permissions.
Utilize access control mechanisms, such as access control lists (ACLs), to establish fine-grained permissions for files and directories. ACLs allow you to grant or deny specific permissions to individual users or groups, providing more flexibility and control over access rights.
Separate public and private files into different directories and set appropriate permissions accordingly. Publicly accessible files should have read permissions for all users, while private files should be restricted to authorized users only.
Ensure that files containing sensitive information, such as configuration files or database credentials, are not accessible by unauthorized users. Store these files outside of the web root directory and limit their permissions to prevent direct access.
Regularly monitor and review file and directory permissions for any unauthorized changes or unusual activity. Implement auditing mechanisms or file integrity monitoring systems that can detect and report any unauthorized modifications or changes in permissions.
Consider using file and directory permissions in combination with other security measures, such as authentication and encryption, to provide a layered defense against unauthorized access.
Document and follow best practices for file and directory permissions in your organization. Establish clear guidelines for configuring and managing permissions and regularly train your development and operations teams to ensure they understand the importance of secure file and directory permissions.
By implementing secure file and directory permissions, you can strengthen the security of your PHP application and minimize the risk of unauthorized access or tampering of sensitive data. Properly configured permissions are essential for maintaining the confidentiality and integrity of your application and its associated files.
Conclusion
Securing PHP applications requires a multi-faceted approach that encompasses various aspects of development, configuration, and maintenance. By following the best practices outlined in this article, you can significantly strengthen the security of your PHP applications and protect against common threats and vulnerabilities.
From using the latest version of PHP and keeping the installation up to date to implementing secure coding practices and validating user input, each step plays a vital role in defending against attacks.
Enabling error reporting and logging helps in identifying and addressing issues proactively, while protecting sensitive information through secure session handling and secure database connections ensures the confidentiality and integrity of user data.
It is crucial to use HTTPS for secure communication, protect against Cross-Site Scripting (XSS) and Cross-Site Request Forgery (CSRF) attacks, and use Content Security Policy (CSP) to limit potential security vulnerabilities.
Implementing password hashing and salting techniques, protecting against SQL injection attacks, and securing file and directory permissions are essential measures to safeguard your application’s data and prevent unauthorized access.
Regularly testing and monitoring your PHP applications for vulnerabilities and keeping up with security updates and patches are crucial in maintaining a secure environment.
By consistently implementing these measures, staying informed about evolving threats, and continuously improving your security practices, you can create robust and resilient PHP applications that protect user data and provide a secure experience for your users.
Remember, security is an ongoing effort, and it is vital to stay vigilant, adapt to emerging threats, and continuously assess and enhance your PHP application’s security posture to mitigate the ever-evolving risks present in the digital landscape.