Introduction
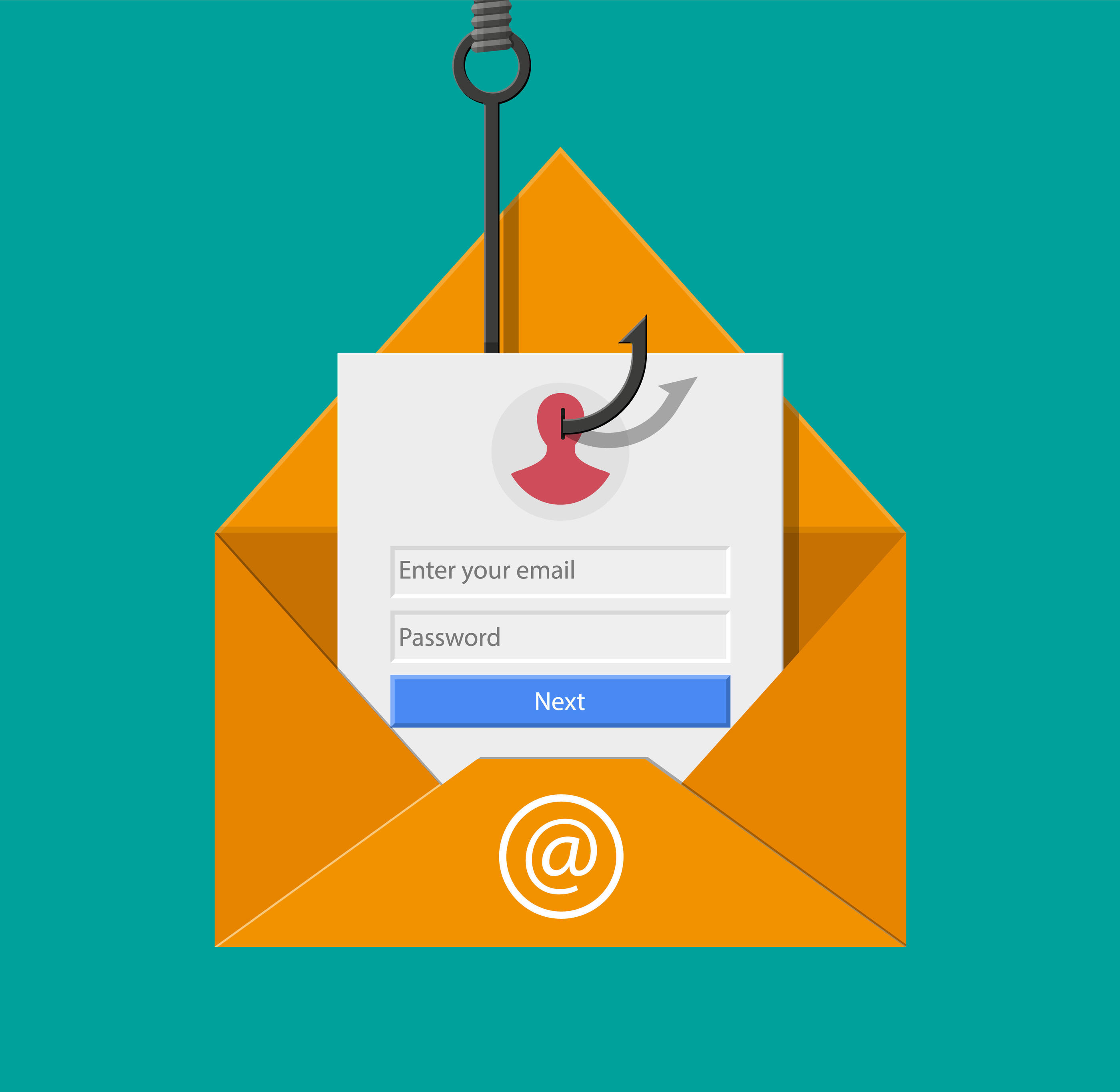
Phishing has become one of the most prevalent and dangerous forms of cyber-attacks in recent years. With the increasing sophistication of technology, cybercriminals are finding new ways to trick individuals into revealing sensitive information or unknowingly installing malware on their devices. Understanding what a phishing email is and how to identify it is essential for protecting yourself and your personal information.
A phishing email is a fraudulent message that is designed to deceive recipients into taking certain actions, such as providing personal information, clicking on malicious links, or downloading malicious attachments. These emails often masquerade as legitimate communication from trustworthy sources, such as banks, social media platforms, or online retailers. The ultimate goal of a phishing email is to manipulate the recipient into divulging sensitive data, which can then be used for identity theft, financial fraud, or unauthorized access to accounts.
It’s important to be aware of the common signs of a phishing email to avoid falling victim to these scams. Phishing emails often contain grammatical errors, spelling mistakes, or poor formatting, which can be indicators of their fraudulent nature. They may also create a sense of urgency or fear, urging recipients to take immediate action without considering the consequences. By familiarizing yourself with these red flags, you can arm yourself against phishing attacks.
In this article, we will explore the different types of scams attempted through phishing emails and the tactics employed by cybercriminals. We will delve into the methods they use to obtain personal information, convince individuals to click on malicious links, install malware on devices, and gain unauthorized access to online accounts. Moreover, we will provide guidelines on how to protect yourself from phishing emails, making it more difficult for cybercriminals to exploit your personal information or compromise your online security.
What is a Phishing Email?
A phishing email is a deceptive message sent by cybercriminals, masquerading as a legitimate source, with the intention of tricking individuals into revealing sensitive information or taking harmful actions. These emails are designed to look authentic, often mimicking the branding and layout of well-known companies, banks, or government agencies in order to gain the recipient’s trust.
Phishing emails typically employ a variety of tactics to deceive their targets. They may use urgent or alarming language to create a sense of panic, making individuals more likely to act without careful consideration. By mimicking official logos, email addresses, and signatures, cybercriminals make it difficult for recipients to distinguish between genuine and fraudulent email communications.
The ultimate goal of a phishing email is to obtain personal information, such as usernames, passwords, credit card details, or social security numbers. This information can be used for various malicious purposes, including identity theft, financial fraud, or unauthorized access to online accounts.
Phishing scams can affect individuals and businesses alike. In targeted attacks, cybercriminals may research their victims to craft highly personalized emails, such as spear-phishing or whaling attacks. These emails often contain specific details or references that make them appear more convincing.
It’s important to note that phishing emails are not limited to traditional email communication. They can also be sent via text messages or social media platforms. Cybercriminals constantly adapt their methods, using any available means to exploit unsuspecting victims.
Phishing emails can be damaging not only to individuals but also to organizations. Falling victim to a phishing attack can result in financial loss, reputational damage, and compromised security. It is crucial to stay vigilant and educated about phishing techniques in order to protect yourself and your sensitive information.
Common Signs of a Phishing Email
Phishing emails can be quite convincing, but there are certain signs you can look out for to help identify whether an email is legitimate or a potential phishing attempt. By being aware of these signs, you can protect yourself from falling victim to these scams.
1. Suspicious email address: Check the sender’s email address carefully. Phishing emails often have email addresses that mimic legitimate sources but contain slight variations or misspellings. Pay attention to domain names, as well.
2. Poor spelling and grammar: Phishing emails frequently contain grammar and spelling mistakes. Legitimate organizations usually have proofreaders and quality control measures in place, so be cautious if you spot multiple errors in an email.
3. Urgent calls to action: Phishing emails often create a sense of urgency, urging you to take immediate action. They may claim that your account will be closed if you don’t provide certain information or make a payment quickly. Be wary of emails that pressure you to act hastily without allowing time for verification.
4. Unexpected attachments or links: Exercise caution when receiving unsolicited attachments or links in an email. Phishing emails may contain malicious attachments that can infect your device with malware or links that take you to fake websites designed to steal your information.
5. Requests for personal information: Legitimate organizations typically don’t ask for personal information via email. Be cautious if an email requests your passwords, Social Security number, bank account details, or other sensitive information. Always verify the request through a different, trusted communication channel.
6. Generic greetings: Phishing emails often use generic greetings like “Dear Customer” instead of addressing you by your name. Legitimate companies usually personalize their communications and address you by your full name.
7. Unusual URLs: Hover over links in the email to see the actual URL. Phishing emails may use misleading hyperlinks that appear legitimate but direct you to fraudulent websites.
Remember, these signs are not foolproof, as cybercriminals continuously refine their tactics. If you have any doubts about the legitimacy of an email, it’s best to directly contact the organization using official channels to verify its authenticity. Your vigilance is key to protecting yourself from phishing attacks.
Types of Scams Attempted through Phishing Emails
Phishing emails come in various forms, each targeting unsuspecting individuals with the goal of obtaining personal information or tricking them into taking harmful actions. It’s essential to familiarize yourself with these types of scams so that you can be alert and protect yourself from falling victim to phishing attacks.
1. Attempts to Obtain Personal Information: One common type of phishing email aims to trick recipients into providing personal information, such as usernames, passwords, credit card numbers, or social security numbers. These emails might pose as an official communication from a bank or online service, requesting immediate action to update or verify account details. Be cautious when providing any personal information and verify the authenticity of such requests through trusted channels.
2. Attempts to Convince you to Click on a Malicious Link: Phishing emails may include convincing-looking links that redirect to malicious websites designed to steal personal information or install malware on your device. These emails might claim that you’ve won a prize, have an important message waiting for you, or need to address an urgent matter. Always hover over links to verify the URL before clicking and avoid clicking on suspicious links and attachments in unsolicited emails.
3. Attempts to Install Malware on your Device: Phishing emails can also contain attachments that, when opened, install malware on your device. These attachments could be disguised as invoices, receipts, or other seemingly innocuous files. Once the malware is installed, cybercriminals can gain unauthorized access to your device, steal sensitive information, or monitor your online activities.
4. Attempts to Gain Access to Your Online Accounts: Some phishing emails aim to trick users into revealing their login credentials for online accounts, such as email, social media, or banking accounts. These emails often impersonate reputable companies and claim that there has been suspicious activity on your account, prompting you to login and verify your credentials. Always access your online accounts directly from trusted websites and never provide your login information through email links.
5. Attempts to Harvest Email Contacts: Another type of phishing scam involves tricking recipients into providing their email login credentials. Once cybercriminals gain access to an email account, they can use it to send phishing emails to the victim’s contacts, spreading the scam further. Avoid providing your login credentials to unknown or untrusted sources.
By staying aware of the various types of scams attempted through phishing emails, you can increase your chances of identifying fraudulent emails and protecting yourself from falling victim to these malicious attacks. It’s important to maintain a healthy level of skepticism and exercise caution when interacting with emails that ask for personal information or prompt you to take immediate action.
Attempts to Obtain Personal Information
One of the primary objectives of phishing emails is to trick recipients into revealing personal information. Cybercriminals use various tactics to obtain this sensitive data, which can then be used for identity theft, financial fraud, or unauthorized access to accounts. Understanding how these attempts are made can help you recognize and avoid falling victim to such phishing scams.
1. Account Verification: Phishing emails often pretend to be from reputable organizations, such as banks or online service providers, requesting immediate action to verify or update account information. They may claim that there has been unusual activity on your account or that your account will be locked unless you provide the requested information. Remember, legitimate organizations typically do not request sensitive information via email. Instead of clicking on any links provided in the email, always access your accounts directly from trusted sources to verify any such requests.
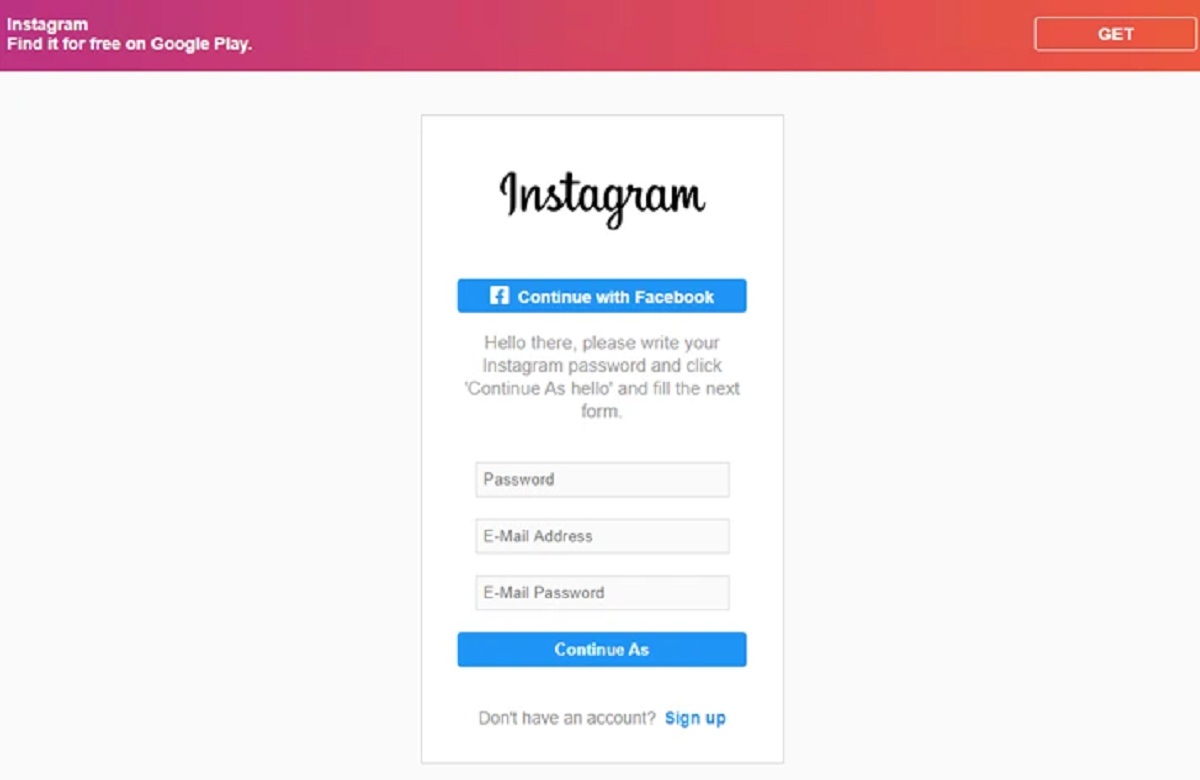
2. Usernames and Passwords: Phishing emails may try to trick you into revealing your login credentials by directing you to fake login pages. These pages look identical to the legitimate ones and are designed to capture your username and password. Be cautious when prompted to log in through an email link and ensure the website’s URL is secure and matches the legitimate organization’s domain before entering any login details.
3. Financial Information: Phishing emails may request financial information, such as credit card numbers, bank account details, or social security numbers. They might claim it’s necessary for a refund, prize claim, or account update. Legitimate organizations never ask for such sensitive information via email. Avoid providing any financial details unless you have verified the authenticity of the request through official channels.
4. Personal Identifiable Information (PII): Phishing emails may also attempt to collect personal identifiable information (PII), such as your full name, address, phone number, or date of birth. Cybercriminals can use this information for identity theft or to perpetrate other fraudulent activities. Be cautious of any email that asks for personal information and ensure you are interacting with a trusted source before sharing any PII.
5. Social Engineering Tactics: Phishing emails often employ social engineering tactics to manipulate recipients into revealing personal information. They may create a sense of urgency, fear, or excitement to prompt immediate action without thinking twice. If an email seems suspicious, take a step back, and carefully evaluate its authenticity before providing any personal information.
Remember, protecting your personal information should be a top priority. Be skeptical of any email that requests sensitive data and never provide personal or financial details unless you are certain of the email’s legitimacy. When in doubt, contact the organization directly through official channels to verify the request and ensure your information remains secure.
Attempts to Convince You to Click on a Malicious Link
Phishing emails often employ sophisticated techniques to convince recipients to click on malicious links. These links may appear harmless but can lead to websites that are designed to steal personal information, infect devices with malware, or initiate other malicious activities. Understanding how cybercriminals manipulate individuals into clicking on these links is essential for protecting yourself from phishing scams.
1. Urgent Calls to Action: Phishing emails typically create a sense of urgency, urging you to take immediate action by clicking on a link. They may claim that your account has been compromised, a payment is overdue, or you have won a prize. By leveraging urgency, cybercriminals aim to bypass your critical thinking and prompt you to click without considering the consequences. Be cautious when faced with such urgency and double-check the legitimacy of the request before taking any action.
2. Spoofed Websites: Phishing emails often direct you to spoofed websites that look nearly identical to legitimate sites. To entice you to click on the link, they may use well-known branding, logos, and familiar website layouts. However, these websites are designed to trick you into entering your personal information, such as login credentials or financial details. Always scrutinize the URL before clicking on any link and verify that the website is secure and genuine.
3. False Security Warnings: Phishing emails can also employ false security warnings to make you believe that your device or online account is at risk. These warnings may state that your device is infected with a virus, your account has been compromised, or your data is at risk of being lost. To resolve the issue, you are prompted to click on a link that leads to a malicious website. Be cautious of unsolicited security warnings and verify the authenticity of such claims through trusted sources before taking any action.
4. Phishing through Social Media: Phishing attacks are not limited to email but can also occur through social media platforms. Cybercriminals may send phishing messages through private messages or impersonate trusted contacts to persuade you to click on a link. Be wary of unsolicited messages, especially those containing suspicious links, and avoid clicking on them without verifying their legitimacy.
5. Email Attachments: Phishing emails may contain attachments that appear harmless but actually contain malware. These attachments could be disguised as invoices, receipts, or important documents. When opened, they can infect your device with malware, allowing cybercriminals to gain unauthorized access, steal personal information, or monitor your online activities. Exercise caution when opening attachments from unknown sources or unexpected emails.
To protect yourself from the tactics employed to convince you to click on a malicious link, exercise caution when interacting with unknown or suspicious emails. Be skeptical of urgency, verify the authenticity of security warnings, and always hover over links to verify their destination before clicking. Maintaining cybersecurity awareness and staying vigilant are key to avoiding the potential risks associated with phishing emails.
Attempts to Install Malware on Your Device
One of the primary objectives of phishing emails is to trick recipients into downloading and installing malware on their devices. Cybercriminals utilize various tactics to convince individuals to open malicious attachments or visit infected websites, allowing them to gain unauthorized access, steal sensitive information, or monitor online activities. Understanding how these attempts to install malware are made can help you safeguard your device and personal information from phishing scams.
1. Malicious Attachments: Phishing emails often contain attachments that are disguised as harmless files, such as invoices, resumes, or official documents. These attachments, once opened, can unleash malware onto your device. It is crucial to exercise caution and refrain from opening attachments from untrusted or unfamiliar sources, especially if you were not expecting them.
2. Infected Links: Phishing emails may include links that direct you to infected websites. Once you click on these links, malware can be automatically downloaded and installed on your device without your knowledge. Always hover your mouse over links to inspect the URL before clicking on them. If the link appears suspicious or unrelated to the email’s content, avoid clicking on it.
3. Drive-By Downloads: Some sophisticated phishing attacks can initiate drive-by downloads. This method involves redirecting you to compromised websites that automatically download malware onto your device without any interaction or consent. Keeping your web browser and security software up to date can provide an additional layer of protection against such attacks.
4. Exploiting Software Vulnerabilities: Phishing emails may attempt to exploit vulnerabilities in the software installed on your device. This can include outdated operating systems, web browsers, or plugins. Cybercriminals can craft emails that prompt you to click on a link or open an attachment, which then exploits these vulnerabilities to install malware. Regularly updating your software with the latest security patches helps patch these vulnerabilities and reduce the risk of malware installation.
5. Fake Software Updates: Phishing emails may also mimic software update notifications to deceive users into downloading and installing malware disguised as legitimate updates. Always download updates directly from the official software provider’s website or use the built-in update mechanism of the software itself to ensure their authenticity.
To protect your device from malware installation attempts through phishing emails, exercise caution when interacting with attachments, links, or software updates from untrusted or suspicious sources. Avoid opening attachments or clicking on links if you are unsure of their origin or legitimacy. Regularly update your software and maintain up-to-date security software to protect against known vulnerabilities and potential malware threats.
Attempts to Gain Access to Your Online Accounts
One of the main goals of phishing emails is to trick individuals into revealing their login credentials for online accounts. Cybercriminals employ various tactics to gain unauthorized access to your accounts, which can lead to identity theft, financial loss, or compromised personal information. Understanding these attempts to breach your online accounts is crucial for protecting your digital identity from phishing scams.
1. Impersonation of Legitimate Companies: Phishing emails often impersonate well-known companies or online service providers. They create convincing emails that appear to come from reputable sources, using logos, branding, and email templates similar to the legitimate organization. These emails may inform you of suspicious activities or require you to confirm your account details, leading you to a fake login page where your credentials are obtained. Always double-check the URL before entering your login credentials and navigate to the official website independently to ensure you are accessing the genuine login page.
2. Redirecting to Fake Login Pages: Phishing emails may contain links that appear legitimate but direct you to fake login pages. These pages are designed to capture your login credentials, allowing cybercriminals to gain unauthorized access to your online accounts. Be cautious of any email that requests you to log in or verify your account information. Instead of clicking on the provided link, manually type the website address into your browser or use a trusted bookmark to access your accounts.
3. Password Reset Scams: Phishing emails may claim that there is an issue with your account and prompt you to reset your password. When you click on the link provided, you are directed to a fake website where your new password is captured by cybercriminals. They can then use this information to gain complete control over your account. To ensure the legitimacy of any password reset request, always initiate the reset process directly through the official website or contact the company’s support team through trusted channels.
4. Account Upgrade or Verification Requests: Phishing emails may also pose as account upgrade or verification requests, asking you to provide personal information or login credentials. They may claim that failure to comply will result in account closure or limited access. Avoid providing any information or credentials through email. Instead, reach out to the organization directly through official contact details to verify the request’s authenticity.
5. Social Engineering Techniques: Phishing emails often employ social engineering techniques to manipulate individuals into revealing their account credentials. They may prey on emotions, such as fear, urgency, curiosity, or excitement, to prompt you to act without fully considering the implications. Be cautious and think critically when encountering such emotional triggers in email communications.
To protect your online accounts from phishing attempts, never provide your login credentials or personal information through email or suspicious links. Be vigilant in verifying the legitimacy of any requests before taking any action. Enable multi-factor authentication (MFA) whenever possible and regularly monitor your accounts for any unusual activities. By staying aware and practicing good cybersecurity habits, you can significantly reduce the risk of your online accounts being compromised by phishing attacks.
How to Protect Yourself from Phishing Emails
Protecting yourself from phishing emails is essential to safeguard your personal information, online accounts, and financial security. By following these best practices, you can significantly reduce the risk of falling victim to phishing scams.
1. Be Vigilant and Skeptical: Develop a habit of skepticism when it comes to email communications. Be cautious of unsolicited emails, especially those requesting personal information or urging immediate action. If something seems suspicious, take the time to investigate further before responding or clicking on any links.
2. Verify Email Senders: Double-check the email address and sender’s name to verify their authenticity. Phishing emails often use a similar display name but have a different email address. Hover over the sender’s name to see the actual email address, and compare it to the official contact information from the organization in question.
3. Don’t Click on Suspicious Links: Avoid clicking on links in emails that seem suspicious or come from unknown sources. Hover over links to see the actual URL before clicking, and ensure it matches the legitimate website’s address. If in doubt, manually type the website address into your browser or use a trusted bookmark to access the website.
4. Think Before Acting: Phishing emails often create a sense of urgency or fear, hoping to bypass your rational thinking. Take a step back and analyze the situation. Be cautious of emails that demand immediate action or contain threats. Confirm any claims or requests by reaching out to the organization using official contact information.
5. Keep Software Updated: Regularly update your operating system, web browser, and security software. Software updates often include security patches that address known vulnerabilities, making it harder for cybercriminals to exploit them.
6. Use Antivirus and Anti-Malware Software: Install reputable antivirus and anti-malware software on your devices. These programs help detect and block malicious files, emails, and websites, providing an additional layer of protection against phishing attempts.
7. Enable Multi-Factor Authentication (MFA): Whenever available, enable multi-factor authentication for your online accounts. MFA adds an extra layer of security by requiring additional verification, such as a unique code sent to your mobile device, in addition to your password.
8. Educate Yourself: Stay informed about the latest phishing techniques and scams. Educate yourself and your colleagues/family members about the common signs and best practices for identifying and avoiding phishing emails. Regularly share information and resources to ensure everyone is aware of the risks and how to protect themselves.
9. Report Phishing Attempts: If you receive a phishing email, report it to the appropriate authorities. This can include forwarding the email to the Anti-Phishing Working Group (reportphishing@apwg.org) or reporting it to your email service provider. By reporting phishing attempts, you help authorities in their efforts to combat cybercrime.
By implementing these precautions and practices, you can significantly reduce the risk of falling victim to phishing emails. Remember, staying vigilant, thinking critically, and verifying the legitimacy of requests are crucial steps in protecting yourself and your sensitive information from phishing scams.
Conclusion
Phishing emails continue to be a significant threat in the digital landscape, targeting individuals and organizations alike. It’s crucial to stay informed and vigilant to protect yourself and your personal information from falling into the hands of cybercriminals.
Throughout this article, we’ve explored what phishing emails are, common signs to look out for, and the various tactics employed by cybercriminals. We discussed attempts to obtain personal information, convince you to click on malicious links, install malware on your device, and gain unauthorized access to your online accounts.
To protect yourself from phishing emails, it’s important to be skeptical and cautious when receiving unsolicited emails or requests for personal information. Verify the authenticity of senders and email addresses, evaluate the legitimacy of security warnings or urgent calls to action, and avoid clicking on suspicious links or opening attachments from unknown sources.
Regularly update your software and security tools, enable multi-factor authentication whenever possible, and stay educated about emerging phishing techniques. By implementing these best practices, you can significantly reduce the risk of falling victim to phishing scams.
Remember, your digital safety is in your hands. By staying vigilant, thinking critically, and maintaining a healthy skepticism, you can protect yourself and your sensitive information from phishing emails and ensure a safer online experience.