Deep learning is a machine learning technique that combines artificial intelligence and image analysis to create highly effective means to detect malicious software. Data scientists from Microsoft and Intel have developed a method called STAMINA. This method combines static analysis and deep learning to collect detailed information about image-converted binaries. The model also uses artificial intelligence to be able to use the data to execute tasks. Let’s dive into the strange world of deep learning and learn how this technique can revolutionize malware detection and analysis.
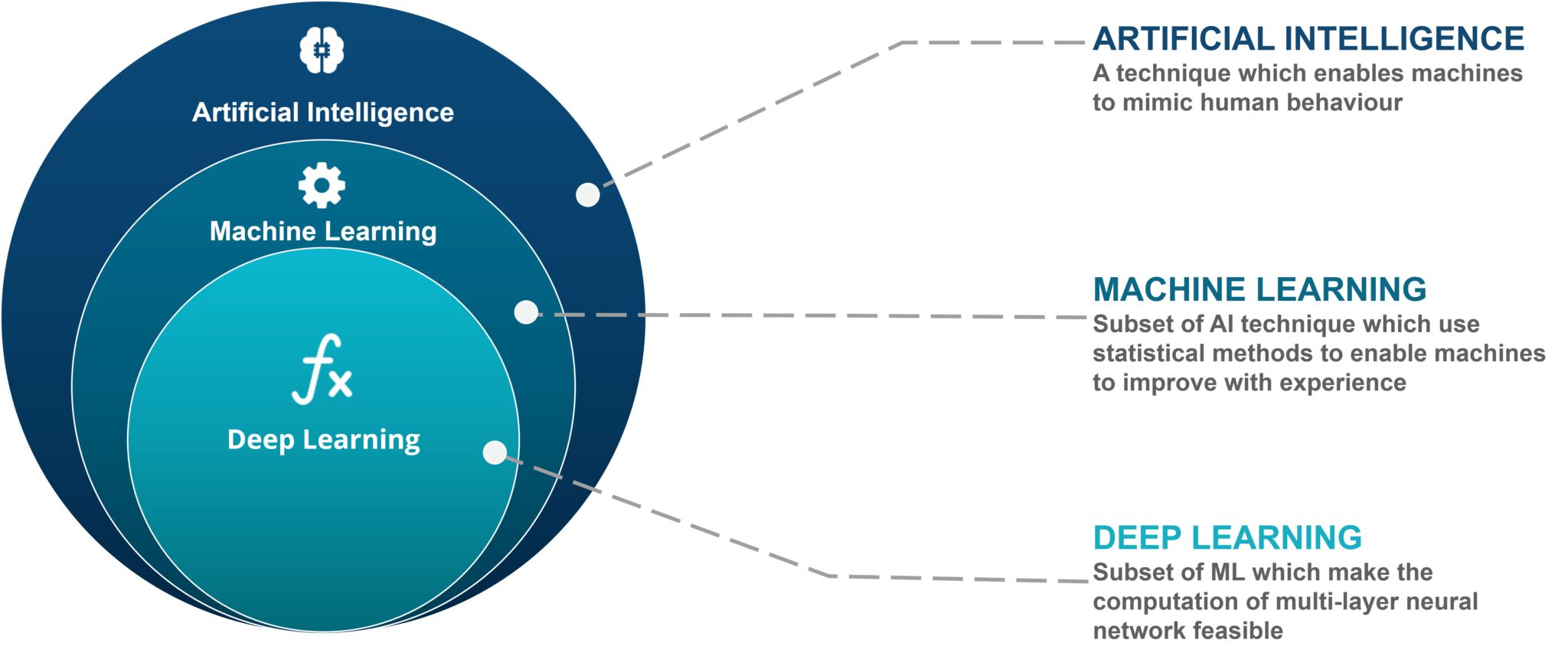
What is Machine Learning?
Machine learning is a type of AI that deals with recognizing patterns and computational learning. This method makes use of computer algorithms to study massive amounts of data. The data will execute tasks based on the data. Machine learning algorithms create their own internal database of information using training data that is inputted into the software to make predictions and decisions. Check out the complete explanation about how machine learning works to get a better understanding of the topic.
Machine learning makes use of neural networks, system software, or hardware to mimic the functions of the human brain to execute tasks. You’ll have quite a selection of applications with machine learning. However, it is most commonly seen in image recognition, speech recognition, traffic predictions, and more. Here are other applications of machine learning that affect our daily lives.
Machine learning is often implemented in two ways, but feature learning is the most common method. Feature learning is a set of techniques that rely on neural networks to identify their features or characteristics. Neural networks detect representations in training data. This, in turn, allows the program to perform specific tasks and learn from the data. Feature learning uses pattern analysis, using algorithms to pick apart the distinct features and details of a particular set of data. The system groups together items with similar traits and classify them into categories. These representations help the system to detect and identify objects in succeeding data. As common scientific sense provides, increasing the volume of reliable input data helps the machine-learning algorithm to perform its tasks better.
What is Deep Learning?


Deep learning is a branch of machine learning involving the creation of intelligent systems capable of learning on their own. Unstructured data are types of data that don’t come in tabular format. These are non-textual data such as digital images, audio, video, MP3 files, and more. Deep learning is the only variant of artificial intelligence that works well with this type of data. Another important factor to understand is that neural networks are at the core of both machine learning and deep learning since the latter is technically a subset of the former.
These detect patterns in data and generate actionable conclusions, but the two have major differences. Check out this article comparing machine learning and deep learning to have a better grasp of their differences. Neural networks are comprised of layers of variables and are very good at learning from raw data. They then use that knowledge they learned to execute tasks.
The system automatically learns what to look for when faced with real data. Scientists often train neural networks using input data consisting of images of different objects. Over time, the system will have the ability to classify similar objects based on the similarities of their features with the features of the input data it has learned. Each of the layers in this network can detect specific features such as edges, corners, faces, and more. Once the neural network has mapped out this information, it can use this knowledge to detect or identity objects in subsequent data. These networks vary in depth which is determined by the number of layers therewith. Traditional neural networks only contained two or three layers. But newer models can have up to 150 layers.
History of Neural Networks
Scientists did not invent the concept of neural networks; in fact, they simply copied it from the biological processes of the brain which also makes use of its own neural networks. Neural networks in artificial intelligence copy the way biological neurons signal to each other within the network. Much like the human brain, each network is made up of input and output layers as well as a hidden layer. This hidden layer allows for the extraction of textural information so that we can capture all features of the malware binaries being examined in detail. The integrated function of neural networks and hidden layers make for an in-depth analysis of training data. These abilities have far-reaching implications in pattern analysis. It also gives the program the ability to solve complex problems.
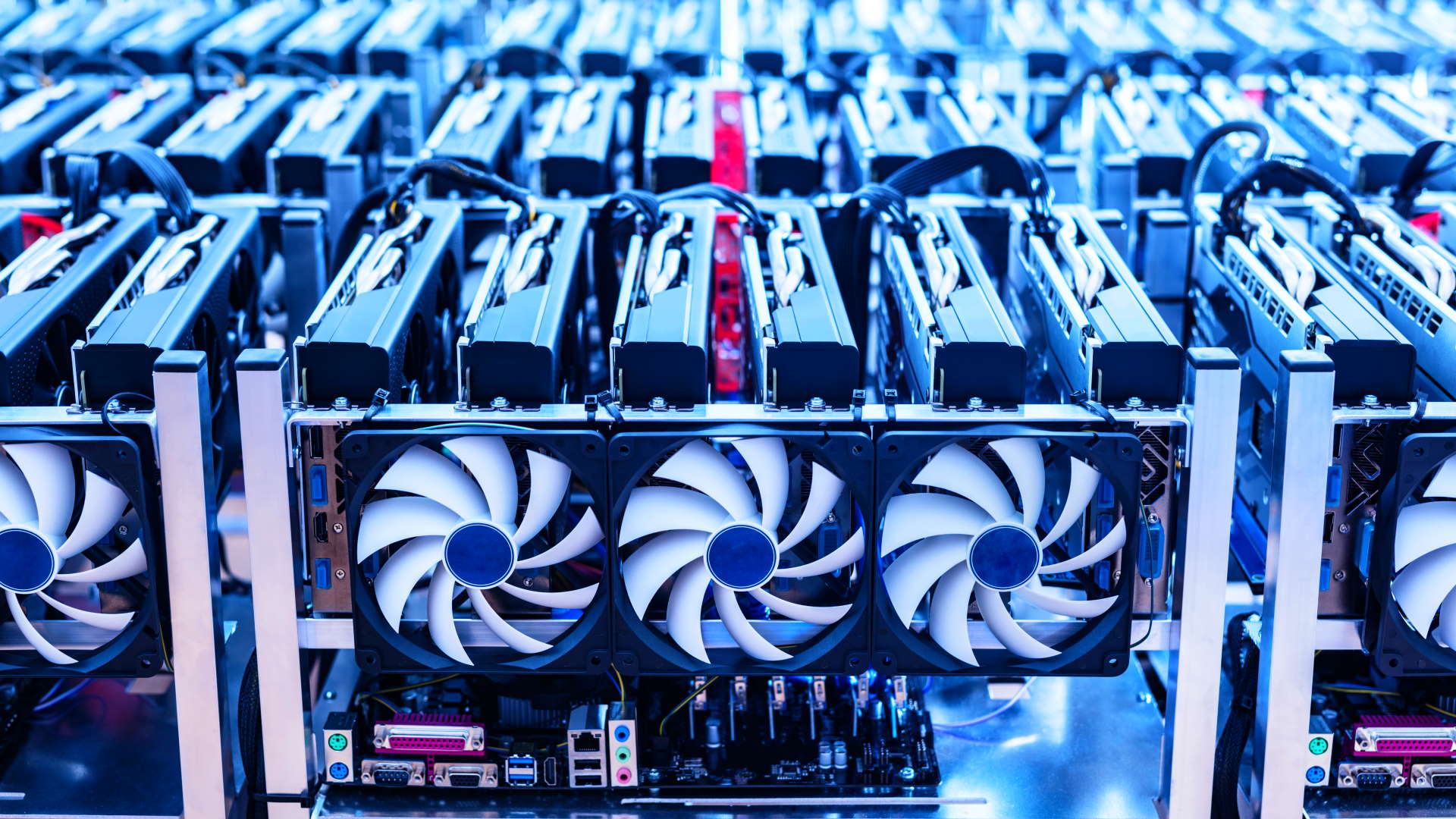
The use of neural networks in artificial intelligence and scientific research isn’t new either. It has been in existence since the 1950s, although the technology conduct real-life experiments did not exist until the early 2000s. However, they were largely ignored during that time due to vast data requirements computing power that was required to execute them. Using neural networks and deep learning suddenly took a turn during the past five years. There are a few fortunate events in the history of scientific advancement that contributed to this change.
The first is due to considerable improvements to the deep learning tools that generate more accurate results. The second is the availability of advanced graphics processing units (GPUs) that can train deep networks at a much faster rate. The third reason is related to the relatively recent popularity and availability of training data. Training data function a lot like research samples and are used to teach the machine learning model what to look out for.
What are the Benefits of Deep Learning?


The unique ability of neural networks to combine complex pattern identification, classification, and application make deep learning uniquely adept at solving complex problems. It’s also the best machine learning technique to deal with unstructured data. It actually manages to outdo machine learning in this area. Neural networks also allow for in-depth analysis and mapping of large amounts of data. Neural networks require less input for analysis, which means faster processing speeds. This is in contrast to deep engineering methods which many scientists consider to be both time-consuming and expensive. The use of automated networks also takes much less time to run.
The research team is keen on benefiting from the program’s neural networks. This type of network requires less input than neural engineering methods. In addition to this, neural networks also promise faster processing speeds and less resource-intensive processing. The researchers are aiming to develop a model that can support large-scale deployment of deep learning for company-based malware protection. This is mainly for the benefit of security firms and industries that might need them.
What are the Most Common Techniques for Malware Detection?


Traditional malware detection approaches usually require a system that can extract binary signatures from data sets. Their purpose is to cross-reference the binary signatures of known malware. The analysis itself can be static, dynamic, or hybrid methods. Antivirus programs that rely on static analysis scans for malware codes in programs without necessarily running the software. This type of analysis usually works well for identifying malicious files in individual and compressed files. Most antivirus programs fall under this category and carry out scans using already-known suspicious codes and pattern-matching analysis. Check out these examples of malware removal tools that you can use on a daily basis. Unfortunately, the analysis does not actually run the code; it can be over-ridden by more advanced malware without being detected.
Dynamic analysis improves on this weakness by running programs to verify the existence of malware. This hands-on approach makes it much harder to conceal runtime applications containing malware. Besides that, it’s also adept at identifying any changes to the system which it immediately flags as malware. Alternatively, data scientists also use hybrid methods for more comprehensive malware scanning. These types of programs can detect malicious codes that are hidden away. Aside from that, hybrid models are also much better at detecting indicators of previously unknown malicious codes.
As mentioned, most antivirus programs rely on signature scanning, which used previously known malicious codes to identity malware. This method works well for most types of known malware. However, signature scanning doesn’t work well for new forms of malware or variations of existing malware. Many new forms of malware have been engineered using machine learning methods. Most new forms of malware can only be distinguished from clean files through behavioral analysis.
What is Deep Learning Used For?


The real-life applications of deep learning range far and wide. At the core of these practical applications and functions, it gives the software the ability to make sense of unstructured data like images, video, and audio. It essentially allows the software to analyze visual and auditory information much as a human does. This is highly characteristic of artificial intelligence.
Deep learning can be found in many applications that we use today, and its potential use ranges across several industries. Its most productive applications include automatic machine translation, speech-to-text transcription, object classification and detection, and many more. Digital assistants rely on these methods to translate voice commands. In the same manner, deep learning models are also responsible for converting your voice to text. A classic example would include the Google Speech To Text app. The Apple Face ID uses the same technology to detect your face as a form of authentication. Aside from this software, Google Photos to classify and detect objects in photos. Facebook tagging uses the same technology to identify and block photos that violate community standards.
Deep learning is also being studied in natural language processing, which has to do with extracting meaning from unstructured text or audio input. It helps speech-to-text software like Google Translate generate more accurate translations of verbal input into different languages. Other industries, such as medicine and car manufacturing, also benefit from deep learning. Doctors and medical professionals rely on deep learning tools to diagnose breast cancer and other diseases. Car manufacturers also make use of deep learning to create visual sensors for self-driving cars. Other practical applications include automatic colorization of black-and-white images, automatic addition of sounds to silent movies and videos, automatic handwriting generation, and more.
How Can Deep Learning Be Used to Track Malware?


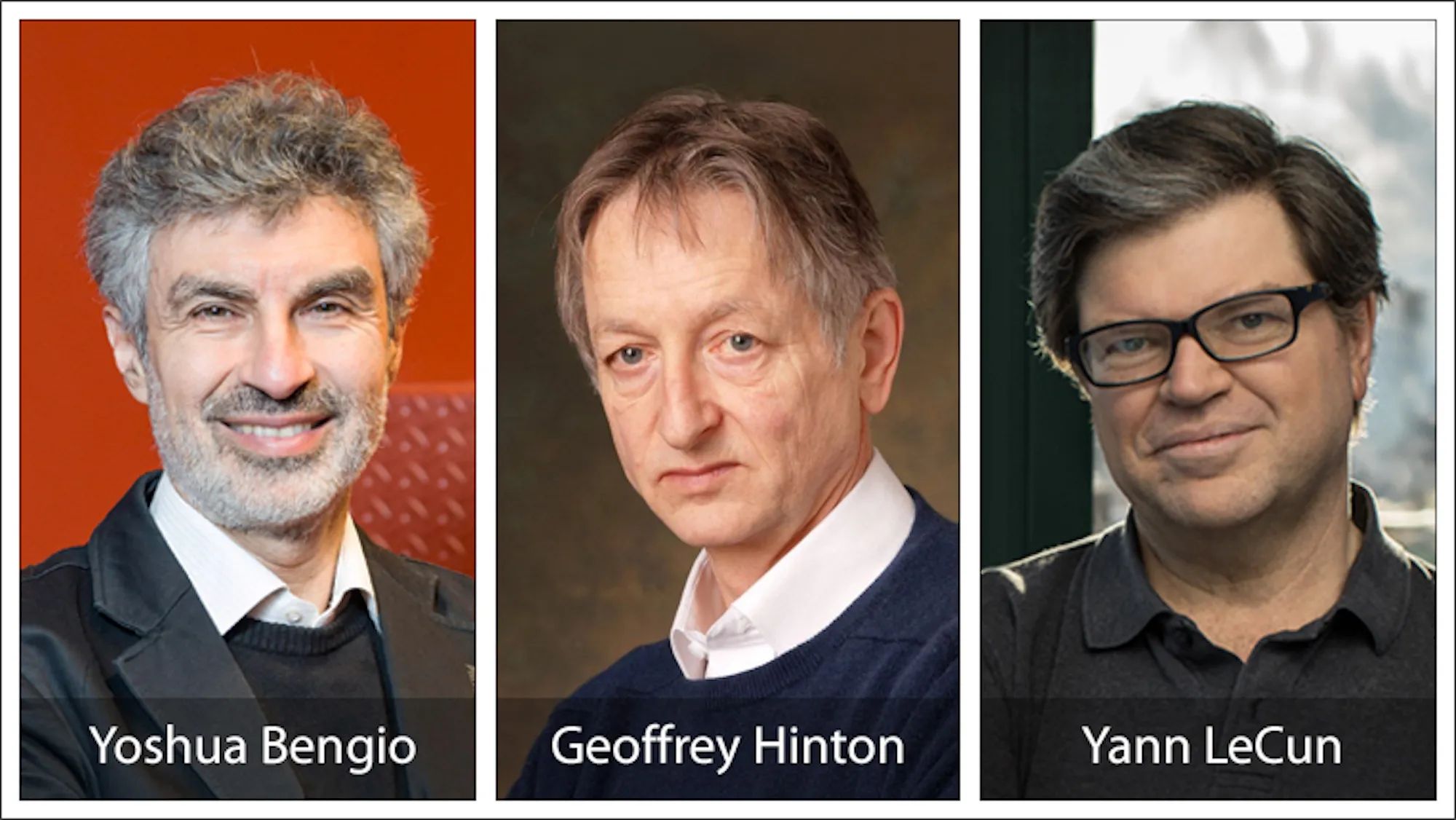
Scientists from Intel Labs and Microsoft Threat Protection Laboratories have collaborated on research to test deep learning application for static malware threat detection. The study looked at applying deep learning techniques to avoid costly feature engineering. It also aims to use machine learning techniques to build a classification system that will identify malware program binaries. They cited the exponential increase in new forms of malware and the concurrent decrease in the efficacy of traditional malware analysis techniques as additional justification.
In order to test their theory regarding the efficacy of deep learning techniques for malware detection, the scientists embarked on a study they called STAMINA. The study name is an acronym for Static Malware-as-Image Network Analysis. The system static malware detection frameworks with deep transfer learning and seeks to train the system using malware samples. For the study, scientists converted two million samples of binary data into two-dimensional grayscale images that can be analyzed using deep learning techniques. Sixty percent of the samples were used to train the deep neural network algorithms. Twenty percent were used to validate the network while the remaining 20 percent were used to test the efficacy of the entire project.
The team achieved a 99.07% percent accuracy rate with a false positive rate of just 2.58%. Accuracy in the context of this study is defined as the proportion of correctly classified samples over the total number of test samples. On the other hand, a false positive refers to the number of benign software wrongly classified as malware divided by the total number of benign software. Undoubtedly, these results match in well with the expectations of the researchers and was a very promising start in proving the potential application of deep learning for malware detection.
The Future of Deep Learning and Malware Detection


Deep learning is a special machine learning approach that can execute tasks based on an in-depth analysis of the features of raw data. Scientific studies have proven the efficacy of deep learning in recognizing and processing language-based information as well as identifying objects using real-time video or screen input. The program works best at detecting the smallest details from unstructured data that are normally difficult to process using traditional machine-learning methods. Besides that, deep learning tools such as ImageNet already possess deep learning capabilities. And these tools surpass human ability when it comes to analyzing unstructured data.
The STAMINA study is only the starting point in the long road to developing a commercially viable option for malware threat detection. Even then, it has managed to provide scientists with the first confirmation of their thesis that deep learning has broader implications and potentially revolutionary functions in malware detection and elimination. It is little surprise then that cybersecurity vendors have been trying to apply deep learning for recognizing malware patterns from large volumes of low-level data.
In a similar fashion, the study also proves with a certain degree of certainty that deep learning models have the ability to learn feature levels of information about a wide variety of malware samples and develop them into one solid model for malware identification. The artificial intelligence component of the model allows the system to train itself from end-to-end. Deep learning learns all components of the data simultaneously and on different levels across the network.
Final Thoughts on Deep Learning and Malware Detection


Machine learning approaches that are designed to help automate data security are gaining traction in both the public and private sectors. Accordingly, the STAMINA study only remains as the starting point in a long series of efforts to provide concrete evidence on the efficacy and timeliness of deep learning and machine learning approaches. It’s also a positive testament to the efficacy of artificial intelligence in combating the increasingly complex nature of malware attacks.
Scientists used to consider deep learning methods as a purely theoretical approach to malware detection. However, the STAMINA study was the first to successfully and completely map out the features of various types of malware. Moreover, it’s also the first artificial intelligence model that could detect modified versions of malware.
Consequently, scientists were also able to demonstrate an understanding of semantic data. This understanding could well evolve into protective measures to protect vulnerable unstructured data in the near future. By continuing their research on this topic, these scientists are hoping to develop a state-of-the-art approach to malware detection. The approach might involve advanced algorithms and neural networks to track never-before-seen malware.
Besides that, researchers are also eyeing deep learning as the most viable solution to plug security gaps in enterprise and individual-based networks. Just as cybersecurity and malware become more diverse over time, so too must security solutions deliver on multiple levels to cover all areas of the widening threat surface. Notwithstanding, this research is only the first step towards developing large-scale models with the capability of matching the speed and scale of advanced malware.