Introduction
As technology advances, so do the risks associated with our online presence. One such risk is the presence of our email addresses on the Dark Web. The Dark Web, a hidden network within the deep recesses of the internet, is a haven for illegal activities, including the sale of personal information, such as email addresses. If your email address falls into the wrong hands on the Dark Web, you could become a target for cybercriminals.
Having your email address on the Dark Web can lead to a multitude of risks, including identity theft, phishing attempts, spam emails, and even financial loss. It is crucial to take proactive measures to protect your online identity and remove your email address from the Dark Web.
In this article, we will discuss the various risks associated with having your email address on the Dark Web and provide you with step-by-step guidance on how to identify if your email address is compromised. We will also outline effective strategies to remove your email address from the Dark Web and minimize the chances of falling victim to cyber threats.
What is the Dark Web?
The Dark Web refers to a part of the internet that cannot be accessed through traditional search engines like Google, Bing, or Yahoo. It is a network that operates on overlay networks, such as Tor (The Onion Router), which allows users to browse the internet anonymously.
Unlike the surface web, which is easily accessible and indexed by search engines, the Dark Web operates within encrypted networks, making it harder to trace and monitor. It is often associated with illegal activities, such as drug trafficking, weapons trading, and hacking services.
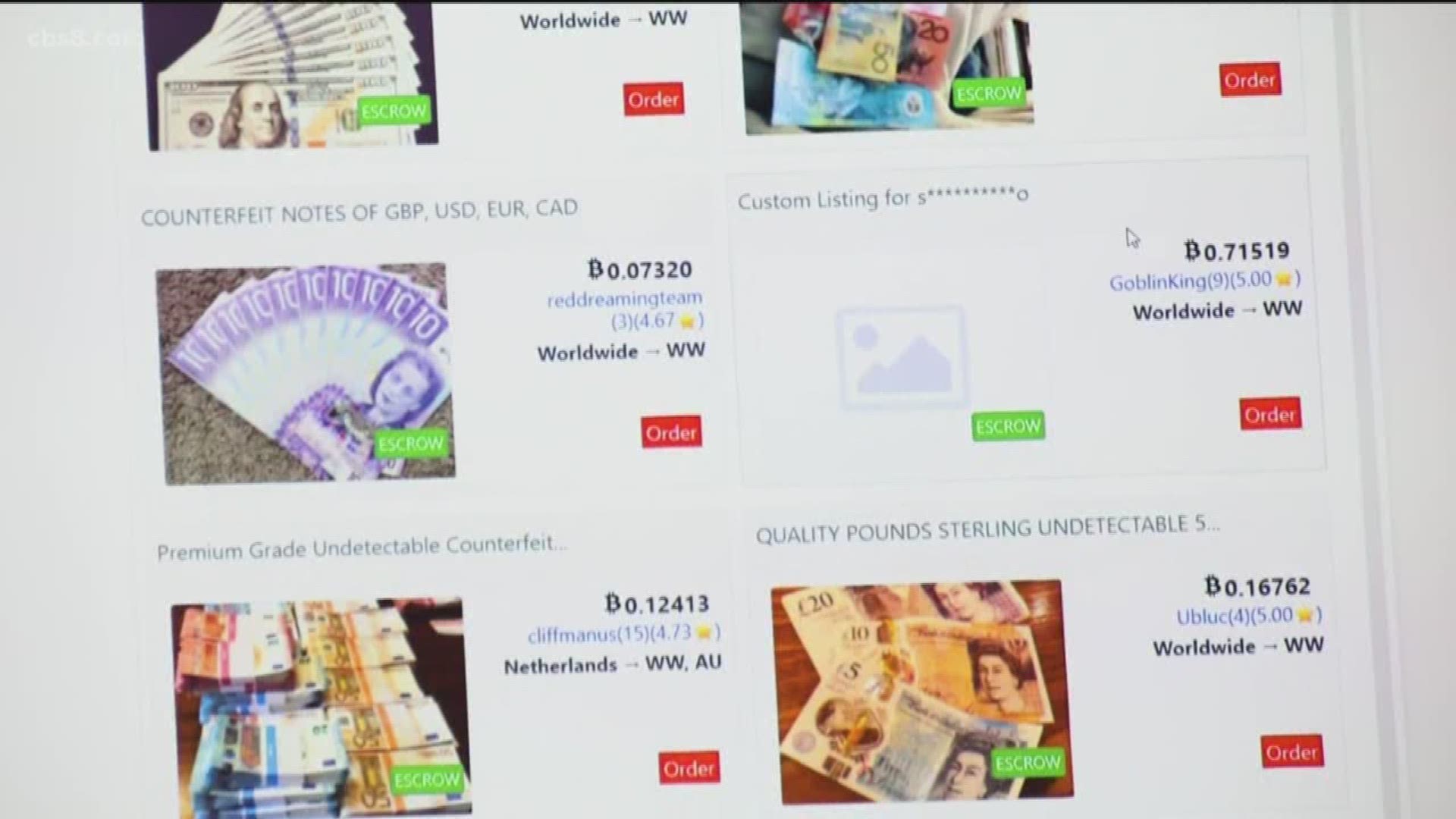
Within the Dark Web, there are hidden websites, also known as Darknet markets, where users can buy or sell various illegal goods and services. These marketplaces operate using cryptocurrencies like Bitcoin, providing an extra level of anonymity to those involved.
While not all activities on the Dark Web are illegal, its anonymity and lack of regulation make it an attractive place for cybercriminals to engage in illicit activities. One such activity is the sale of personal information, including email addresses.
It’s important to note that the Dark Web is just one part of the broader internet and should not be confused with the deep web. The deep web refers to all web pages that are not indexed by search engines, including private databases, academic resources, and password-protected sites.
Why would your email address be on the Dark Web?
There are several reasons why your email address might end up on the Dark Web. One common way is through data breaches. When a company or organization experiences a data breach, hackers can gain access to their databases and steal sensitive information, including email addresses.
These stolen email addresses are then sold or traded on the Dark Web, where cybercriminals can purchase them for various nefarious purposes. For example, they may use these email addresses to send phishing emails, spam, or even perform targeted attacks to obtain additional personal information.
Another way your email address may end up on the Dark Web is through phishing attacks. Phishing is a technique where cybercriminals impersonate legitimate entities, such as banks or popular websites, to deceive users into revealing their personal information, including email addresses and passwords.
If you fall victim to a phishing attack and unknowingly provide your email address to the attackers, they may sell or use it on the Dark Web, exposing you to potential risks.
Moreover, if you tend to reuse the same email address and password combination across multiple platforms or websites, your email address could be vulnerable to compromise. If one of those platforms suffers a data breach, your email address could be exposed and end up on the Dark Web.
It’s crucial to understand that no one is completely immune to having their email address on the Dark Web. Even if you follow best security practices, there’s still a chance that your email address could be involved in a data breach or fall into the hands of cybercriminals.
The risks of having your email address on the Dark Web
Having your email address on the Dark Web can expose you to a range of risks and potential consequences. Here are some of the most significant risks associated with having your email address on the Dark Web:
- Identity theft: Cybercriminals who obtain your email address from the Dark Web can use it as a stepping stone to commit identity theft. They might use your email address to gain access to your accounts, reset passwords, and potentially access sensitive information.
- Phishing attempts: With your email address, cybercriminals can launch phishing attacks, sending emails that appear to be from legitimate sources in order to trick you into revealing personal information, such as passwords or financial details. Falling victim to a phishing attack can lead to significant financial loss or compromise of your online accounts.
- Spam emails: Your email address may end up on mailing lists used by spammers. This can result in an influx of unsolicited emails, advertisements, and potential scams landing in your inbox.
- Targeted attacks: Cybercriminals can use your email address to conduct targeted attacks against you. They may send malicious links or attachments that, when clicked or opened, could compromise your device, steal personal data, or install malware.
- Compromised online accounts: If you use the same email address and password combination across multiple platforms, a data breach involving one of those platforms could have cascading effects. Cybercriminals who obtain your email address can attempt to access your other accounts using known password combinations.
- Loss of privacy: Having your email address on the Dark Web means that your personal information is accessible to cybercriminals. This compromises your privacy and can lead to targeted attacks or attempts to exploit your personal information.
Given these risks, it is essential to take proactive steps to minimize the chances of your email address ending up on the Dark Web and to protect your personal information from falling into the wrong hands.
How to check if your email address is on the Dark Web
Checking if your email address is on the Dark Web can help you identify potential security risks and take appropriate measures to protect your online identity. Here are several steps you can take to determine if your email address is compromised:
- Use reputable Dark Web monitoring services: There are various online platforms and services that can scan the Dark Web for mentions of your email address. These services utilize advanced algorithms to search through the hidden corners of the internet and notify you if they find any matches.
- Check breached data repositories: Several websites aggregate and store data from known data breaches. You can visit these websites and enter your email address to see if it has been included in any past breaches.
- Monitor your email for suspicious activity: Keep an eye on your email account for any unusual or suspicious activity, such as unrecognized login attempts or emails indicating password resets that you did not initiate.
- Check with your email provider: Some email providers have built-in security features that can help check if your email address is compromised. Explore the security settings or contact customer support to learn about the available options.
- Stay informed about recent data breaches: Stay updated on news related to data breaches and check if any of the breached organizations were holding your email address. You can subscribe to services or newsletters that provide timely information on such incidents.
Remember, the Dark Web is constantly evolving, and new breaches occur regularly. It is essential to periodically check if your email address is compromised and take necessary action if any potential risks are identified.
If you find that your email address is on the Dark Web or has been compromised in a data breach, it’s crucial to take immediate steps to secure your accounts and protect your personal information.
Steps to remove your email address from the Dark Web
Discovering that your email address is on the Dark Web can be a cause for concern, but there are steps you can take to minimize the risks associated with having your information exposed. Here are some effective strategies to remove your email address from the Dark Web:
- Change your email password: Start by changing the password for your email account. Ensure that the new password is strong, unique, and not used for any other accounts. This will help prevent unauthorized access to your account.
- Enable two-factor authentication: Activate two-factor authentication (2FA) for your email account. This adds an extra layer of security by requiring a second form of verification, such as a code sent to your phone, to log in.
- Update security settings for other accounts: Review and update the security settings for your other online accounts. Change passwords, enable 2FA where available, and use unique, strong passwords for each account.
- Use a unique email address for different platforms: Avoid using the same email address across multiple platforms or websites. By using unique email addresses, you can minimize the potential impact of a data breach on multiple accounts.
- Be cautious when sharing your email address online: Be mindful of where and how you provide your email address online. Avoid sharing it on untrusted websites or platforms that may compromise your privacy.
- Report phishing attempts and spam emails: If you receive suspicious emails or phishing attempts, report them to your email provider or the appropriate authorities. This helps in combating cybercrime and protecting others from falling victim to similar attacks.
- Regularly monitor your online presence: Monitor your online presence by conducting periodic searches of your email address and personal information. Set up Google Alerts or use specialized monitoring services to stay informed if your information appears on the Dark Web.
While these steps can help mitigate the risks associated with having your email address on the Dark Web, it’s important to note that prevention is key. Maintain good security practices, such as using unique passwords, regularly updating security settings, and being cautious online.
Remember that removing your email address from the Dark Web is an ongoing process. Stay vigilant, stay informed about security best practices, and take appropriate action promptly to protect your online identity and personal information.
Change your email password
One of the first steps in removing your email address from the Dark Web is to change your email password. By doing so, you can prevent unauthorized individuals from accessing your account and compromising your personal information. Here’s how you can change your email password:
- Login to your email account: Visit the website or open the application associated with your email provider and enter your login credentials.
- Navigate to account settings: Look for the account settings or preferences section within your email account. This may vary depending on the email provider.
- Find the password change option: Look for an option to change your password. It may be labeled as “Password,” “Security,” or similar.
- Enter your current password: Provide your current password as a security measure to confirm your identity.
- Create a strong, unique password: Generate a new password that is secure and hard to guess. Make sure to use a combination of uppercase and lowercase letters, numbers, and special characters.
- Update your password: Enter your new password in the designated field and confirm the change.
- Remember your new password: It’s crucial to remember the new password or securely store it using a reputable password manager.
Changing your email password regularly and using a unique, strong password can significantly enhance the security of your email account and reduce the risk of unauthorized access.
Remember, it is essential to avoid using the same password for multiple accounts. This helps to prevent the potential domino effect of a single data breach compromising multiple accounts.
Additionally, consider enabling password recovery options, such as security questions or alternate email addresses, to further secure your email account.
By taking the necessary steps to change your email password, you are proactively safeguarding your email account and minimizing the chances of your email address being misused on the Dark Web.
Enable two-factor authentication
Enabling two-factor authentication (2FA) adds an extra layer of security to your email account, making it more difficult for unauthorized individuals to access your account. By requiring an additional form of verification, such as a code sent to your phone, 2FA helps protect your email account even if your password is compromised. Here’s how you can enable 2FA:
- Login to your email account: Visit the website or open the application associated with your email provider and enter your login credentials.
- Access your account settings: Look for the account settings or preferences section within your email account.
- Find the security or privacy settings: Look for an option related to security or privacy settings. It may be labeled as “Security,” “Two-Factor Authentication,” or something similar.
- Enable two-factor authentication: Follow the prompts and instructions provided to enable two-factor authentication for your email account.
- Choose a verification method: Select the preferred method for receiving the verification code, such as SMS, email, or authentication app.
- Verify and confirm: Complete the verification process by entering the code sent to your selected method to confirm your identity.
- Save your settings: Ensure that you save your settings and make any necessary changes to complete the two-factor authentication setup.
With two-factor authentication enabled, each time you log in to your email account, you will need to provide both your password and the additional verification code. This adds an extra layer of security and significantly reduces the risk of unauthorized access.
Remember to keep your contact information updated, especially if you choose to receive the verification codes via SMS or email. Regularly review your two-factor authentication settings to ensure seamless access to your email account while maintaining maximum security.
Enabling two-factor authentication is a highly recommended security measure that can greatly enhance the protection of your email account from cyber threats, including unauthorized access and potential misuse on the Dark Web.
Update security settings for other accounts
It’s essential to review and update the security settings for your other online accounts to minimize the risk of unauthorized access and protect your personal information. By taking these steps, you can ensure that your accounts are more secure and less vulnerable to compromise. Here’s how you can update security settings for your other accounts:
- Identify your online accounts: Make a comprehensive list of all the online accounts you have, including social media, banking, shopping, and other platforms.
- Review the security settings: Visit the website or application for each account and locate the security or privacy settings. Look for options related to password strength, two-factor authentication, and account recovery.
- Change your passwords: Ensure that you are using unique, strong passwords for each account. Update any passwords that are weak, easily guessable, or similar to your previous passwords.
- Enable two-factor authentication: Wherever possible, enable two-factor authentication for your accounts. This adds an extra layer of security by requiring a verification code in addition to your password.
- Verify recovery options: Check and update the recovery options for each account. Ensure that the associated email addresses and phone numbers are accurate so that you can regain access to your accounts if needed.
- Monitor account activity: Regularly review the activity logs or notifications from your accounts. Report any suspicious or unauthorized activity immediately to the respective service provider.
- Stay up to date with security features: Keep yourself informed about the latest security features offered by the platforms you use. Take advantage of features such as biometric authentication, device authorization, and security alerts.
By updating the security settings for your accounts and implementing strong security measures, you decrease the likelihood of unauthorized access and minimize the risk of your email address being compromised on the Dark Web. Regularly reviewing and strengthening your security settings is an important aspect of maintaining a secure online presence.
Remember, securing your accounts is an ongoing process. Stay vigilant, stay informed about security best practices, and adapt your security settings as needed to protect your personal information from falling into the wrong hands.
Use a unique email address for different platforms
Using a unique email address for different platforms is an effective strategy to protect your online identity and minimize the impact of a potential data breach. By maintaining separate email addresses for various accounts, you reduce the risk of your email address being compromised on the Dark Web. Here’s why and how you can use unique email addresses:
Why use unique email addresses:
Using a unique email address for each platform offers several benefits:
- Increased security: If a data breach occurs on one platform and your email address is compromised, using a unique email address ensures that your other accounts remain secure.
- Better organization: Having separate email addresses for different platforms allows for easier management and organization of emails, notifications, and account-related communications.
- Improved privacy: Using unique email addresses helps protect your privacy by limiting the number of platforms and websites associated with each address.
How to use unique email addresses:
- Create new email addresses: Consider creating separate email addresses for different purposes, such as one for personal use, one for work-related accounts, and another for online shopping or social media.
- Choose a reliable email provider: Use reputable email service providers that offer reliable security features and customizable email options.
- Keep track of your email addresses: Maintain a record or use a password manager to keep track of the unique email addresses you create for different platforms.
- Update your accounts: Update the email addresses associated with your existing accounts to the unique addresses you’ve created.
- Use forwarders or email aliases: Some email providers offer features like email forwarding or aliases, which allow you to receive emails from different addresses in a single inbox.
By using unique email addresses, you add an extra layer of protection to your online accounts and reduce the risk of your email address being exposed on the Dark Web. Remember to periodically review and update your email addresses as needed.
Take charge of your online security by implementing this practice to safeguard your personal information and maintain control over your digital identity.
Be cautious when sharing your email address online
Being cautious when sharing your email address online is crucial in protecting your privacy and reducing the chances of it ending up on the Dark Web. By following some simple guidelines, you can minimize the risk of your email address being compromised. Here are some tips to help you be cautious when sharing your email address online:
- Think before you share: Consider the necessity of providing your email address before sharing it online. Only share it when absolutely necessary and with trusted sources.
- Use contact forms: Whenever possible, use contact forms instead of directly displaying your email address on websites or forums. This makes it harder for email scraping bots to collect your address.
- Avoid public forums: Be cautious when sharing your email address in public forums or comment sections. Scrappers or spammers may gather email addresses from these platforms.
- Check privacy policies: Before signing up for online services or platforms, review their privacy policies. Ensure that they have a strict policy in place regarding the protection of your personal information, including your email address.
- Opt out of sharing: Look for options to opt out of sharing your email address with third parties when creating accounts or making online purchases.
- Use disposable email services: Consider using disposable email services when signing up for questionable or one-time services. These services provide temporary email addresses that forward emails to your primary inbox.
- Be cautious with public Wi-Fi: When using public Wi-Fi networks, avoid accessing or sending sensitive information via email. Public Wi-Fi connections can be compromised, putting your email address and data at risk.
- Protect your email address on social media: Be mindful of how you share your email address on social media platforms. Avoid publicizing it in your bio or publicly accessible posts.
- Consider using aliases: Some email providers offer email alias features. This allows you to create unique, separate email addresses that deliver emails to your primary account without revealing your actual email address.
By being cautious and selective when sharing your email address online, you reduce the chances of it falling into the wrong hands and being exposed on the Dark Web. Remember to prioritize your privacy and take necessary precautions to protect your personal information.
Always trust your instincts and err on the side of caution when it comes to sharing sensitive information, including your email address, online.
Report phishing attempts and spam emails
Reporting phishing attempts and spam emails not only helps protect yourself but also contributes to combating cybercrime and preventing others from falling victim to these malicious activities. When you encounter suspicious emails or phishing attempts, taking immediate action to report them is crucial. Here’s how you can effectively report phishing attempts and spam emails:
- Do not click on suspicious links or download attachments: If you receive an email that you suspect to be a phishing attempt or spam, refrain from clicking on any links or downloading any attachments within the email. Engaging with these elements can expose you to potential risks.
- Use the reporting feature provided by your email provider: Most email providers have built-in reporting features that allow you to flag and report suspicious emails. Look for options like “Report as phishing” or “Mark as spam” within your email interface.
- Forward the email to your email provider: If there is no reporting feature available, forward the suspicious email to your email provider’s support or abuse department.
- Report to anti-phishing organizations: In addition to reporting to your email provider, you can also report phishing attempts to trusted anti-phishing organizations, such as the Anti-Phishing Working Group (APWG) or the Internet Crime Complaint Center (IC3).
- Notify the potential target of impersonation: If the phishing attempt is impersonating a known organization or individual, consider contacting the impersonated entity directly to alert them of the situation.
- Do not provide personal information: Never provide your personal information, such as passwords, account numbers, or social security numbers, in response to suspicious emails or requests.
- Educate yourself about phishing and spam: Stay informed about common tactics used in phishing attempts and spam emails. This knowledge will help you recognize and report them more effectively.
Reporting phishing attempts and spam emails is vital as it helps email providers identify and block sources of fraudulent activities. It also enables them to enhance their security measures to prevent similar attacks in the future.
By taking the time to report phishing attempts and spam emails, you contribute to the collective effort in creating a safer online environment for everyone.
Regularly monitor your online presence
Regularly monitoring your online presence is an essential practice to identify any potential security threats and take prompt action to protect your personal information. By staying vigilant and proactive, you can minimize the risk of your email address being compromised and appearing on the Dark Web. Here are some key steps to effectively monitor your online presence:
- Perform regular searches: Conduct periodic searches of your email address and other personal information using search engines. This can help you identify any mentions or appearances of your information on public websites or forums.
- Set up Google Alerts: Utilize Google Alerts to monitor specific keywords associated with your email address or personal information. You will receive notifications whenever new information related to those keywords appears online.
- Use online monitoring services: Consider utilizing online services that specialize in monitoring your personal information on the internet, including the Dark Web. These services can provide you with timely alerts if your email address or other sensitive information is found.
- Monitor login activity: Regularly review the login activity and access logs for your online accounts. Watch for any suspicious or unrecognized login attempts, as they may indicate unauthorized access to your accounts.
- Review account statements: Check your financial and billing statements regularly for any unauthorized transactions or suspicious activities. Report any discrepancies or fraudulent charges immediately to the respective financial institution or service provider.
- Stay informed about data breaches: Stay updated on news and announcements regarding data breaches. If a company or organization you are associated with experiences a breach, take immediate action to secure your accounts and change your passwords.
- Protect your devices: Ensure that you have up-to-date antivirus software and firewalls installed on your devices. Keep your operating system and applications updated with the latest security patches to minimize vulnerabilities.
Regularly monitoring your online presence allows you to stay proactive in detecting any potential compromises and taking necessary precautions to protect your personal information. By being aware of how your information is being used and taking swift action, you can significantly reduce the risk of your email address appearing on the Dark Web.
Remember, online monitoring should be an ongoing practice. With the evolving nature of cyber threats, it’s important to remain vigilant and adapt your monitoring strategies accordingly to safeguard your online identity.
Conclusion
Having your email address on the Dark Web can expose you to a variety of risks, including identity theft, phishing attempts, spam emails, and compromised online accounts. However, by taking proactive steps, you can minimize these risks and protect your online identity.
In this article, we discussed the significance of understanding the Dark Web and the reasons your email address may end up on it. We explored the risks associated with having your email address on the Dark Web, such as identity theft and targeted attacks.
We also provided a comprehensive guide on how to check if your email address is on the Dark Web. By utilizing reputable monitoring services, checking breached data repositories, and being vigilant about suspicious activity, you can identify potential compromises.
Furthermore, we outlined important steps to remove your email address from the Dark Web. By changing your email password, enabling two-factor authentication, updating security settings for other accounts, using unique email addresses, being cautious when sharing your email address online, reporting phishing attempts and spam emails, and regularly monitoring your online presence, you can significantly enhance your online security.
Remember, protecting your email address and online identity requires ongoing effort and vigilance. Stay informed about the latest security practices, keep your software up to date, and be cautious when interacting online. By taking these steps, you can reduce the risk of your email address being compromised on the Dark Web and protect your personal information from falling into the wrong hands.
Proactively safeguarding your email address and online presence will provide you with peace of mind and ensure that you can enjoy the benefits of the digital world securely.