Introduction
Welcome to the mysterious and intriguing world of the Dark Web. Hidden beneath the surface of the internet lies a realm that is vastly different from the websites and platforms we are accustomed to. It is a place shrouded in secrecy, operating outside the boundaries of traditional search engines and accessed only by those in the know.
The allure of the Dark Web is undeniable. For many, it represents a realm of anonymity, where individuals can communicate, transact, and explore without the prying eyes of authorities and corporations. However, it is important to note that the Dark Web is not for the faint of heart, as it comes with its fair share of risks and dangers.
In this article, we will delve into the mysterious realm of the Dark Web, understand its difference from the Deep Web, and explore the precautions and safety measures one must take before venturing into this hidden world. Whether you are simply curious about the Dark Web or considering accessing it for specific purposes, this guide will equip you with essential knowledge and tips to navigate this complex landscape.
What is the Dark Web?
To truly understand the Dark Web, it is important to differentiate it from the Deep Web. The Deep Web refers to any part of the internet that is not indexed by search engines. This includes private databases, password-protected websites, and even your personal email inbox. In contrast, the Dark Web represents a small fraction of the Deep Web that is intentionally hidden and requires specific software or tools to access.
The Dark Web operates on a network called Tor (The Onion Router), which anonymizes users and provides them with a layer of encryption. This network allows individuals to browse websites and communicate with each other anonymously, making it virtually impossible to trace their online activities back to their real-world identities.
Within the Dark Web, you will find a mix of legal and illegal activities. While it is true that the Dark Web has gained notoriety for being a platform for illegal trade, such as drugs, firearms, and stolen data, it is also home to legitimate forums, whistleblower platforms, and communities focused on privacy and cybersecurity. The Dark Web provides a sanctuary for those seeking to exercise their right to free speech or share sensitive information without the fear of censorship or surveillance.
It is crucial to understand that the Dark Web is not accessible through traditional web browsers like Chrome or Firefox. To access it, you need to download and configure special software, such as the Tor Browser. This browser allows you to connect to the Tor network and navigate through the hidden layers of the internet. Once inside, you can access websites with a .onion extension, which are unique to the Dark Web.
It is important to note that while the Dark Web provides anonymity, it does not guarantee absolute security. Law enforcement agencies and cybercriminals alike have found ways to infiltrate this hidden realm, and careless actions can expose users to significant risks. Therefore, before considering a visit to the Dark Web, it is crucial to understand the associated risks and take appropriate precautions to safeguard your online identity and personal information.
Understanding the Deep Web vs. the Dark Web
The terms “Deep Web” and “Dark Web” are often used interchangeably, but they actually refer to different aspects of the hidden internet. While both are obscured from traditional search engines, they serve distinct purposes and hold varying levels of anonymity and accessibility.
The Deep Web encompasses all internet content that is not indexed by search engines. This includes private databases, online banking platforms, password-protected websites, and even subscription-based services like Netflix. These sites require user authentication, making them inaccessible to search engine crawlers.
On the other hand, the Dark Web refers to a small section of the Deep Web that is intentionally hidden and can only be accessed using specific software or tools. It operates on the Tor network, which routes internet traffic through multiple layers of encryption to ensure privacy and anonymity for its users.
While the Deep Web can be likened to a vast ocean, the Dark Web represents the murky depths where individuals can engage in activities away from the prying eyes of authorities and corporations. The Dark Web is home to various illicit marketplaces, where illegal goods and services are bought and sold using cryptocurrencies like Bitcoin. It also hosts websites dedicated to whistleblowing, anonymous forums, and privacy-centric communities.
The key distinction between the Deep Web and the Dark Web lies in their accessibility. While anyone with the appropriate credentials can access the Deep Web, the Dark Web requires users to navigate through the Tor network using the Tor Browser. This added layer of encryption and anonymity ensures that individuals can browse, communicate, and transact under the cloak of secrecy.
It is essential to approach the Deep Web and the Dark Web with caution. While there are legitimate and legal activities happening in both realms, the Dark Web, in particular, has a reputation for facilitating illegal trade and criminal activities. Engaging in such activities can lead to severe legal consequences, as law enforcement agencies actively monitor and target individuals involved in illegal operations.
Understanding the distinctions between the Deep Web and the Dark Web is crucial for anyone venturing into the hidden realms of the internet. It is essential to recognize the risks and dangers associated with these areas and take appropriate precautions to safeguard personal information and maintain a responsible online presence.
The Risks and Dangers of the Dark Web
As alluring as the Dark Web may seem, it is important to understand and acknowledge the inherent risks and dangers associated with venturing into this hidden realm. While anonymity is a key feature of the Dark Web, it also attracts cybercriminals, scammers, and malicious actors who exploit these characteristics for illegal activities. Here are some of the risks and dangers you should be aware of before accessing the Dark Web:
- Illegal Activities: The Dark Web has gained notoriety for being a hub of illicit trade, including drugs, firearms, counterfeit currencies, stolen data, and hacking tools. Engaging in or associating with such activities can have serious legal consequences.
- Identity Theft: While the Dark Web offers anonymity, it also carries the risk of falling victim to identity theft. Cybercriminals may attempt to gather personal information such as usernames, passwords, credit card details, or social security numbers for their malicious purposes.
- Malware and Viruses: The Dark Web is a breeding ground for malicious software and viruses. Downloading files or visiting compromised websites can expose your device to malware that can steal sensitive information or gain control over your system.
- Financial Scams: Dark Web marketplaces can lure unsuspecting users into financial scams, where individuals are tricked into making payments for goods or services that never materialize. Protecting yourself from such scams requires vigilance and skepticism.
- Harmful Content: The Dark Web houses a range of disturbing and illegal content, including child exploitation material, violent imagery, and extremist ideologies. Exposing yourself to such content can have profound psychological and legal consequences.
- Surveillance and Law Enforcement: Despite the anonymity provided by the Dark Web, law enforcement agencies actively monitor and infiltrate illicit activities. Engaging in illegal actions may lead to your identity being compromised and potential legal consequences.
It is crucial to approach the Dark Web with caution and adopt safety measures to mitigate the risks. Prioritize your online security by using strong and unique passwords, regularly updating your software, and utilizing reputable antivirus and security tools. Additionally, staying informed about the latest scams, being skeptical of suspicious offers, and exercising responsible online behavior are essential for protecting yourself against the dangers of the Dark Web.
Should I Access the Dark Web?
The decision to access the Dark Web is a personal one that requires careful considerations. While the allure of anonymity and the freedom to explore a hidden realm may be intriguing, it is important to evaluate whether accessing the Dark Web aligns with your specific needs and priorities. Here are some factors to consider when deciding if you should access the Dark Web:
- Purpose: Determine your motive for accessing the Dark Web. Are you simply curious about its existence or are you seeking specific information or services? Understanding your purpose can help you assess the potential benefits and risks.
- Risk Tolerance: Assess your tolerance for risk. The Dark Web is associated with various illegal activities, scams, and potential legal consequences. If you are risk-averse or have a low tolerance for uncertainty, accessing the Dark Web may not be suitable for you.
- Knowledge and Technical Expertise: Familiarize yourself with the technical aspects of accessing the Dark Web. It requires a certain level of understanding of tools like Tor, VPNs, and encryption. If you lack the necessary knowledge or are uncomfortable with navigating such technologies, the Dark Web may not be for you.
- Ethical Considerations: Reflect on the ethical implications of accessing the Dark Web. While there are legitimate and legal activities that take place, it is important to be aware of the prevalence of illegal trade, exploitation, and harmful content. Ensure that your actions align with your personal values and ethical compass.
- Legal Ramifications: Research and understand the legal implications of accessing the Dark Web in your jurisdiction. Laws regarding the Dark Web vary from country to country, and engaging in illegal activities can lead to severe legal consequences. Make sure to be well-informed and act within the boundaries of the law.
Ultimately, the decision to access the Dark Web rests on your individual circumstances and priorities. It is crucial to consider the potential risks, legal implications, and ethical considerations before venturing into this hidden realm. If you do decide to access the Dark Web, taking appropriate precautions and implementing strict security measures is essential to protect your online identity and personal information.
Precautions and Safety Measures
If you have made the decision to access the Dark Web, it is imperative to prioritize your safety and take necessary precautions to protect yourself from the risks associated with this hidden realm. Here are some essential precautions and safety measures to consider:
- Secure Your Online Identity: Before accessing the Dark Web, ensure that your online identity is well-protected. Use strong and unique passwords for all your accounts, enable two-factor authentication whenever possible, and consider using a password manager to securely store your login credentials.
- Obtain a VPN for Anonymity: Utilize a reputable Virtual Private Network (VPN) to enhance your anonymity and protect your online activities. A VPN encrypts your internet connection and routes it through a server, masking your IP address and making it difficult for others to trace your online activities.
- Download and Configure the Tor Browser: The Tor Browser is the gateway to accessing the Dark Web. Download it from the official Tor Project website and configure it correctly to maximize your privacy and security. Ensure that you keep the browser up to date with the latest patches and security updates.
- Navigating the Dark Web: Exercise caution when exploring the Dark Web. Avoid clicking on unfamiliar links or downloading suspicious files. Stick to reputable and verified websites, and be mindful of phishing attempts and scams.
- Finding Dark Web Markets: If you are specifically interested in Dark Web marketplaces, exercise extreme caution. Research and verify the reputation and legitimacy of these marketplaces before engaging in any transactions. Consider seeking recommendations from trusted sources within the Dark Web community.
- Entering Dark Web Marketplaces: When accessing Dark Web marketplaces, practice good operational security. Maintain a separate identity for your Dark Web activities and avoid using any personal information that can be linked back to your real-world identity. Be cautious of sharing unnecessary personal details or engaging in suspicious communications.
- Purchasing and Transactions: If you decide to make purchases on the Dark Web, exercise utmost caution. Use cryptocurrencies, such as Bitcoin, to ensure a certain level of anonymity. Research the reputation and track record of sellers, read reviews, and use escrow services whenever possible to mitigate the risks of fraudulent transactions.
- How to Stay Safe on the Dark Web: Keep yourself informed and up to date with the latest security practices and trends within the Dark Web community. Regularly educate yourself about new threats, vulnerabilities, and protective measures. Remember that maintaining your safety on the Dark Web is an ongoing process that requires vigilance and constant adaptation.
By implementing these precautions and safety measures, you can minimize the potential risks and protect yourself while accessing the Dark Web. However, it is essential to understand that no security measure is foolproof, and risks still exist. Exercise caution, use your judgment, and prioritize your safety at all times.
Step 1: Secure Your Online Identity
Before venturing into the Dark Web, it is crucial to secure your online identity to protect your personal information and minimize the risks of identity theft. Here are some essential steps to secure your online identity:
- Use Strong and Unique Passwords: Create strong passwords that include a combination of uppercase and lowercase letters, numbers, and special characters. Avoid using easily guessable passwords or reusing the same password across multiple platforms. Consider using a password manager to securely store and generate unique passwords.
- Enable Two-Factor Authentication (2FA): Activate two-factor authentication whenever possible. 2FA adds an extra layer of security by requiring an additional verification step, such as a unique code sent to your mobile device, along with your password. This significantly reduces the risk of unauthorized access to your accounts.
- Regularly Update Software and Applications: Keep your devices, operating systems, and applications up to date with the latest security patches and updates. Software updates often include important fixes for vulnerabilities that hackers could exploit to gain access to your personal information.
- Be Cautious of Phishing Attempts: Be vigilant about phishing attempts, where hackers impersonate trusted entities to trick you into revealing your login credentials or personal information. Be wary of suspicious emails, links, or messages asking for sensitive data. Always verify the authenticity of communication before sharing any personal information.
- Protect Your Social Media Accounts: Review your privacy settings on social media platforms and limit the amount of personal information you share publicly. Avoid accepting friend requests or engaging with suspicious accounts. Be mindful of the information you post, as it can be used to track or impersonate you online.
- Monitor Your Financial Accounts: Regularly monitor your bank accounts, credit cards, and other financial accounts for any unauthorized transactions or suspicious activity. Report any discrepancies immediately to your financial institution.
- Use a Virtual Private Network (VPN): Consider using a reputable VPN service to encrypt your internet connection and mask your IP address. This ensures that your online activities and personal information are protected from prying eyes, enhancing your privacy and security.
- Be Mindful of Personal Information: Avoid sharing unnecessary personal information online, especially on public platforms or websites. Be cautious of providing personal details that can be used to track or identify you. The less information available, the harder it is for malicious actors to target you.
Implementing these steps will significantly reduce the risks associated with your online identity and help protect your personal information. By taking proactive measures to secure your online presence, you are better equipped to navigate the Dark Web with confidence while minimizing the risk of identity theft and other cyber threats. Remember, securing your online identity is an ongoing process, so regularly review and update your security measures to stay protected in the ever-evolving digital landscape.
Step 2: Obtain a VPN for Anonymity
One of the key elements of ensuring your privacy and anonymity while accessing the Dark Web is to use a reputable Virtual Private Network (VPN). A VPN encrypts your internet connection and routes it through a server located in a different geographic location, masking your IP address and making it difficult for others to trace your online activities. Here’s how to obtain a VPN for anonymity:
- Research and Choose a Reputable VPN Provider: Take the time to research and select a reputable VPN provider. Look for providers that have a solid track record, positive reviews, strong encryption protocols, and a no-logs policy. Ensure that the VPN provider you choose does not collect or store your personal information or browsing history.
- Consider Your Needs and Budget: Evaluate your specific needs and budget when choosing a VPN provider. Take into account factors such as the number of devices you need to connect, the level of privacy and encryption offered, the speed and stability of the VPN connection, and the cost of the subscription. Many VPN providers offer different pricing plans to accommodate various budgets.
- Download and Install the VPN Application: Once you have chosen a VPN provider, go to their website and download the VPN application compatible with your operating system. Most reputable VPN providers offer applications for Windows, Mac, iOS, and Android devices. Follow the installation instructions provided by the VPN provider to set up the application on your device.
- Configure the VPN Application: After installation, launch the VPN application and navigate to the settings or preferences section. Here, you can customize the VPN settings to your preferences. Consider enabling features such as a kill switch, which automatically disconnects your internet if the VPN connection drops, ensuring your anonymity is maintained at all times.
- Connect to a VPN Server: Once you have configured the VPN application, select a server location to connect to. VPN servers are available in various countries around the world. Choosing a server in a different country from your own can add an extra layer of anonymity and make it more difficult for others to trace your online activities.
- Test and Verify the VPN Connection: After connecting to a VPN server, test the connection to ensure that your IP address has changed. You can use online tools or websites that display your IP address to verify that the VPN is functioning correctly. If the IP address matches the server location, you can be confident that your anonymity is protected.
- Regularly Update and Use the VPN: Keep the VPN application up to date with the latest software versions and security patches provided by the VPN provider. Whenever you access the Dark Web or engage in any sensitive online activities, ensure that the VPN is active to maintain your anonymity and protect your privacy.
Obtaining a VPN for anonymity is a crucial step in safeguarding your online activities and protecting your identity while accessing the Dark Web. By choosing a reputable VPN provider, configuring the application correctly, and using it consistently, you enhance your privacy and make it significantly more challenging for others to track or monitor your online activities. Remember to stay vigilant and regularly update your VPN application to ensure you are benefiting from the latest security features and protocols.
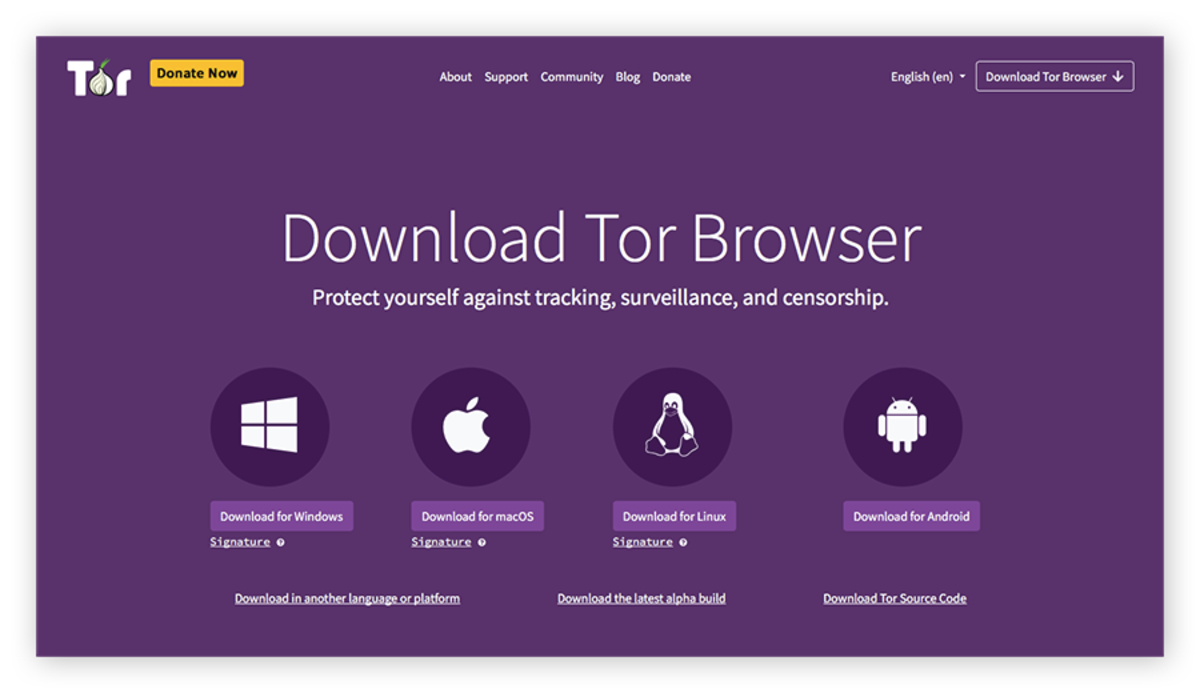
Step 3: Download and Configure the Tor Browser
To access the Dark Web, you will need to download and configure the Tor Browser. The Tor Browser is a specialized web browser that allows you to navigate through the layers of the Tor network, ensuring your anonymity and privacy. Here’s how to download and configure the Tor Browser:
- Visit the Official Tor Project Website: Go to the official Tor Project website (https://www.torproject.org) to ensure you download the legitimate and up-to-date version of the Tor Browser. Avoid downloading the Tor Browser from unauthorized sources to minimize the risk of downloading tainted or modified versions.
- Choose the Appropriate Tor Browser Version: Select the correct version of the Tor Browser for your operating system. The Tor Browser is available for Windows, Mac, Linux, and Android platforms. Make sure to download the version that is compatible with your device.
- Download the Tor Browser: Click on the download link provided on the official Tor Project website to start the download process. The file size is relatively large, so it may take some time depending on your internet speed. Wait for the download to complete before proceeding to the next step.
- Install the Tor Browser: Locate the downloaded file on your device and double-click on it to initiate the installation. Follow the on-screen instructions provided by the installation wizard to install the Tor Browser on your device. After installation, launch the Tor Browser.
- Configure the Tor Browser: When you first launch the Tor Browser, you will be presented with options to configure it for your needs. It is recommended to leave the default settings as they are, as they provide the optimal balance of privacy and security. However, you may choose to adjust the security level based on your comfort level and browsing requirements.
- Connect to the Tor Network: After configuring the Tor Browser, click on the “Connect” or “Start Tor” button to establish a connection to the Tor network. The Tor Browser will connect to a series of relays and encrypt your internet traffic, ensuring your anonymity while browsing the Dark Web.
- Verify your Connection: Once connected to the Tor network, the Tor Browser will display a green onion icon in the top-left corner. This indicates that you are connected and can securely navigate the Dark Web. To verify your connection, you can visit websites like check.torproject.org to ensure that your IP address is masked.
- Securely Browse the Dark Web: Now that your Tor Browser is configured and connected to the Tor network, you can safely browse the Dark Web. Keep in mind the risks and dangers associated with the Dark Web, and exercise caution when exploring and interacting with websites and users.
By following these steps, you can successfully download and configure the Tor Browser to access the Dark Web. It is important to note that the Tor Browser is specifically designed for anonymous browsing and provides a level of privacy and security. However, it is not foolproof, and it is essential to remain vigilant and exercise caution while exploring the Dark Web. Regularly update the Tor Browser to benefit from the latest security patches and enhancements provided by the Tor Project, ensuring your browsing experience remains as safe and secure as possible.
Step 4: Navigating the Dark Web
Once you have successfully configured the Tor Browser and connected to the Tor network, it’s time to navigate the Dark Web. Navigating the Dark Web can be quite different from the regular surface web, as it requires a different approach and understanding of how websites are accessed. Here are some important steps to navigate the Dark Web effectively:
- Use Dark Web Directories and Hidden Wikis: Dark Web directories and hidden wikis are valuable resources that can help you discover and navigate various websites on the Dark Web. These directories list a wide range of websites and provide categories or search functionalities to help you find what you’re looking for.
- Verify Website URLs: Before accessing any website on the Dark Web, ensure that the URL is authentic and trustworthy. Be cautious of clicking on suspicious or unknown links, as they may lead to harmful or malicious websites. Double-check the website URL and verify its legitimacy through trusted sources or communities within the Dark Web.
- Explore Dark Web Forums and Communities: Dark Web forums and communities can provide valuable information and insights into specific topics of interest. Engaging with these communities can help you discover new websites, gain knowledge about current trends, and connect with like-minded individuals. However, exercise caution and avoid sharing personal or sensitive information.
- Be Mindful of Your Digital Footprint: While on the Dark Web, be aware that your actions can leave traces of your digital footprint. Avoid clicking on unnecessary links or engaging in suspicious activities that could compromise your security or anonymity. Limit the amount of personal information you share and perform regular checks to ensure your online activities remain private.
- Exercise Caution with Content: The Dark Web contains a wide array of content, both legal and illegal. It is important to exercise discretion and be mindful of the content you choose to access. Avoid engaging with illegal or harmful material, as it can have serious consequences both legally and morally. Prioritize your safety, well-being, and ethical boundaries.
- Use Search Engines Specifically for the Dark Web: Dark Web search engines, such as Torch and Ahmia, can be useful tools for discovering websites and content. These search engines index specific portions of the Dark Web and provide search functionalities similar to regular search engines. However, keep in mind that not all Dark Web websites are indexed, and searching for specific content may require additional exploration.
- Bookmark Trusted Websites: As you navigate the Dark Web, it is helpful to bookmark trusted websites that you frequently access. This will allow you to revisit them easily in the future without relying solely on directories or search engines. Be cautious of accessing websites from external sources, as they may lead to phishing or scam attempts.
By following these steps, you can navigate the Dark Web with more confidence and effectively explore the hidden corners of this mysterious realm. Always prioritize your safety, exercise caution, and be aware of the potential risks associated with the Dark Web. Remember, the Dark Web can be unpredictable, and practicing responsible online behavior is essential to protect your anonymity and maintain a secure browsing experience.
Step 5: Finding Dark Web Markets
If you are interested in exploring Dark Web markets, where various illicit goods and services are traded, it’s important to understand how to find and identify these marketplaces. Finding Dark Web markets requires some knowledge and research, as they are not openly accessible like regular websites. Here are some steps to help you find Dark Web markets:
- Utilize Dark Web Directories and Hidden Wikis: Dark Web directories and hidden wikis are excellent starting points for discovering Dark Web markets. These platforms often provide comprehensive listings of various marketplaces, along with reviews and ratings from users. Explore these directories and wikis to gather information about different Dark Web markets.
- Join Dark Web Communities and Forums: Engaging with Dark Web communities and forums can provide valuable insights into current Dark Web marketplaces. Users within these communities often share information, discussions, and recommendations related to markets. Joining such communities allows you to connect with experienced individuals who can guide you toward reliable and trusted Dark Web markets.
- Research Reliable Market Reviews: Look for reputable sources that specialize in reviewing Dark Web markets. These reviews evaluate the credibility, security measures, and reliability of various marketplaces. Reading reviews can help you identify trustworthy markets and understand their reputation within the Dark Web community.
- Use Dark Web Search Engines: Dark Web-specific search engines can be useful for finding Dark Web markets. These search engines index the Dark Web to help users find specific websites or content. By utilizing Dark Web search engines, you can search for keywords related to Dark Web markets or specific products you are interested in.
- Consider Recommendations from Trusted Sources: Seek recommendations from trusted individuals within the Dark Web community. These individuals may have firsthand experience with different Dark Web markets and can provide insights into the reliability, quality, and security of these platforms. However, exercise caution and verify the sources before acting on any recommendations.
- Exercise Caution and Research: When exploring Dark Web markets, exercise caution and conduct thorough research. Take the time to verify the legitimacy and reputation of the marketplaces before engaging in any transactions. Read user reviews, check the market’s policies, and look for signs of professionalism and security measures implemented by the market operators.
- Stay Updated on Dark Web Market Trends: Dark Web markets are constantly evolving, with new marketplaces appearing and older ones disappearing or experiencing issues. Stay informed about the latest market trends by following reputable Dark Web news sources, forums, and communities. This awareness will help you make informed decisions about which markets to trust and which to avoid.
Remember that engaging in activities within Dark Web markets carries significant risks, both legal and personal. It is crucial to exercise caution, follow security measures, and make informed decisions while navigating and interacting within these marketplaces. Always prioritize your safety and be aware of the potential consequences of participating in illicit activities within Dark Web markets.
Step 6: Entering Dark Web Marketplaces
Once you have found a Dark Web marketplace that aligns with your interests and needs, it’s time to enter and explore the marketplace. However, entering Dark Web marketplaces requires caution and adherence to security protocols. Here are the essential steps to safely enter Dark Web marketplaces:
- Ensure Your Anonymity: Before accessing any Dark Web marketplace, ensure that you have a secure and anonymous setup. Use a trusted VPN service to encrypt your internet connection and mask your IP address. Make sure to connect to a server located in a different country to further enhance your anonymity.
- Open the Tor Browser: Launch the Tor Browser that you installed and configured previously. Double-check that you are connected to the Tor network by verifying the presence of the green onion icon in the top-left corner of the browser window.
- Obtain the Marketplace URL: Use the information gathered during your research to obtain the URL or onion address of the Dark Web marketplace you wish to enter. Be aware that Dark Web marketplaces may frequently change their URLs for security purposes, so it’s important to rely on up-to-date sources or forums for the most recent URLs.
- Enter the URL in the Tor Browser: In the Tor Browser’s address bar, enter the marketplace URL you obtained and press Enter. Allow the Tor Browser to establish the connection to the marketplace. This may take a moment as the Tor network routes your connection through various relays.
- Follow Marketplace Onboarding Procedures: Each Dark Web marketplace has its own onboarding procedures and registration process. Carefully read and follow the instructions provided on the marketplace’s landing page or homepage. Be aware that some marketplaces may require user registration, while others may permit browsing without an account.
- Exercise Caution and Vigilance: While navigating within Dark Web marketplaces, exercise caution at all times. Be mindful of the products and services being offered, and scrutinize each listing for authenticity and credibility. Read user reviews, compare prices, and consider sellers’ ratings before engaging in any transactions.
- Understand the Marketplace Features: Familiarize yourself with the features and functionalities of the marketplace. Take the time to explore the different sections, such as product categories, search filters, messaging systems, and dispute resolution mechanisms. Understanding how the marketplace operates will help you navigate efficiently and make informed decisions.
- Follow Marketplace Rules and Guidelines: Dark Web marketplaces typically have specific rules and guidelines that users must adhere to. These may include prohibitions on certain types of products, restrictions on communication methods, or guidelines for dispute resolution. Familiarize yourself with these rules and ensure that your actions align with the marketplace’s guidelines.
- Protect Yourself and Maintain Anonymity: As you interact within Dark Web marketplaces, remember to prioritize your safety. Consider using cryptocurrencies for transactions, avoid sharing personally identifiable information, and be cautious when entering into communication with other users. Always prioritize your anonymity and conduct any transactions or communication with discretion.
By following these steps, you can safely enter Dark Web marketplaces and navigate through their offerings. Remember, engaging in any illegal activities within Dark Web marketplaces is strictly prohibited and carries severe consequences. Exercise caution, conduct thorough research, and follow security measures to ensure a safe and responsible experience while exploring Dark Web marketplaces.
Step 7: Purchasing and Transactions
When it comes to making purchases and transactions on Dark Web marketplaces, it is crucial to approach with caution and take several important steps to protect yourself. Here are the key considerations to keep in mind during this step:
- Verify Seller Reputability: Before making a purchase, thoroughly research and verify the reputation of the seller or vendor. Look for user reviews, ratings, and feedback, as this can provide valuable insights into their trustworthiness and the quality of their products or services. Consider purchasing from vendors with a proven track record and positive reviews.
- Ensure Secure Communication: When communicating with a seller, prioritize secure communication methods. Use encrypted messaging platforms, such as the messaging systems provided within the Dark Web marketplace. Avoid sharing personal contact information or communicating outside of the secure platform to maintain your privacy and anonymity.
- Choose Discreet Shipping Options: When selecting shipping options, opt for discreet shipping methods to minimize the risk of attracting unnecessary attention. Vendors often provide different shipping choices, including plain packaging or specialized methods that ensure the confidentiality of the contents. Review the available options and select the one that best aligns with your privacy needs.
- Utilize Cryptocurrencies for Transactions: Cryptocurrencies, such as Bitcoin, are commonly used on Dark Web marketplaces due to their anonymity and ease of use. Prioritize using cryptocurrencies for transactions, as they minimize the risk of exposing your financial information. Familiarize yourself with the process of acquiring and using cryptocurrencies to ensure smooth and secure transactions.
- Verify Product Authenticity: Take the necessary steps to verify the authenticity and quality of the products being offered. Read product descriptions thoroughly, examine product images, and consider reaching out to the seller for additional information. If possible, research the product online to compare prices and gather more details. Exercise caution when purchasing high-risk items, such as drugs or firearms.
- Consider Escrow Services: Many Dark Web marketplaces offer escrow services to facilitate secure and fair transactions. Escrow acts as a middleman between the buyer and seller, holding funds until the transaction is completed satisfactorily. Consider opting for escrow services when available to mitigate the risk of fraud or dispute.
- Read and Understand Vendor Policies: Each Dark Web marketplace has specific policies regarding refunds, disputes, and returns. Familiarize yourself with these policies before making a purchase to understand your rights as a buyer. If any issues arise during the transaction process, refer to the marketplace’s policies for guidance on how to address them.
- Protect Your Identity: Throughout the purchasing process, prioritize safeguarding your identity. Avoid sharing unnecessary personal information or providing details that could compromise your anonymity. Use pseudonyms when interacting with sellers and exercise discretion when discussing sensitive matters. Be cautious of social engineering attempts or scams aimed at obtaining your personal information.
By following these steps, you can navigate the purchasing and transaction process on Dark Web marketplaces more securely. While engaging in transactions within Dark Web marketplaces, always prioritize your safety and be aware of the potential risks. Remember, illegal activities are strictly prohibited, and engaging in such activities can have severe legal consequences. Exercise caution, exercise due diligence, and uphold responsible practices throughout the purchasing process.
Step 8: How to Stay Safe on the Dark Web
Safety should always be a top priority when accessing the Dark Web. As you navigate this hidden realm, it is crucial to take steps to protect yourself and maintain your anonymity. Here are some key measures to ensure your safety on the Dark Web:
- Stay Informed: Keep yourself updated on Dark Web security practices, trends, and emerging threats. Regularly read reputable sources, forums, and communities to stay informed about the latest developments within the Dark Web landscape.
- Use Reliable and Updated Software: Use reliable and up-to-date security software, such as antivirus and firewall programs, to protect your device from malware and other cybersecurity threats. Regularly update your software to benefit from the latest security patches and enhancements.
- Implement Strict Privacy Measures: Prioritize your privacy by using a trusted Virtual Private Network (VPN) to encrypt your internet connection and mask your IP address. Avoid sharing unnecessary personal information and use pseudonyms when interacting with others on the Dark Web.
- Exercise Caution with Links and Downloads: Be cautious when clicking on links or downloading files within the Dark Web. Only access trusted websites and avoid suspicious or unverified links. Download files from reliable sources and scan them with security software before opening or executing them.
- Be Skeptical and Verify: Maintain a healthy dose of skepticism while exploring the Dark Web. Verify information and claims from multiple sources before taking any action. Avoid falling for scams, phishing attempts, or fraudulent schemes by performing thorough research and exercising caution in your interactions.
- Avoid Illegal Activities: Engaging in illegal activities on the Dark Web can have severe legal consequences. Abide by the law and avoid transactions involving illegal items or services. Understand the boundaries and limitations of what is permissible and act responsibly within those confines.
- Regularly Update and Secure Your Online Identity: Regularly update your passwords, enable two-factor authentication, and use unique credentials for each online account. Secure your online identity and minimize the risk of unauthorized access or identity theft.
- Trust Your Instincts: If something seems too good to be true or feels suspicious, trust your instincts. If a deal seems unrealistically lucrative or a transaction seems dubious, it is better to err on the side of caution and avoid it.
- Disconnect When Not in Use: When you’re done browsing the Dark Web, ensure that you disconnect from the Tor network, close the Tor Browser, and turn off the VPN to minimize the risk of unauthorized access or exposure.
- Report Suspicious Activity: If you come across any suspicious or illicit activities on the Dark Web, consider reporting them to the appropriate authorities. Act responsibly and contribute to maintaining a safer online environment.
By following these safety measures, you can navigate the Dark Web with increased security and minimize the potential risks associated with exploring this hidden realm. Always prioritize your safety, privacy, and legal compliance while engaging in activities on the Dark Web. Remember, responsible behavior and caution are key to ensuring a safer experience in this complex and unique online space.
Conclusion
Exploring the Dark Web can be an intriguing endeavor, offering a glimpse into a hidden world with its own set of rules and activities. However, it is crucial to approach the Dark Web with caution and a thorough understanding of the risks involved. By following the steps outlined in this guide, you can navigate the Dark Web more securely and responsibly.
Remember that the Dark Web is a double-edged sword. While it offers anonymity and privacy, it is also associated with illegal activities, scams, and significant risks. Engaging in illicit activities can have severe legal consequences, so it’s vital to uphold ethical boundaries and abide by the law.
Maintaining your safety on the Dark Web requires ongoing diligence. Stay informed about the latest security practices, update your software regularly, and prioritize your privacy through the use of reliable VPNs and secure communication methods.
Additionally, remember that exploring the Dark Web is not suitable for everyone. It requires technical knowledge, risk tolerance, and a discerning mindset. If you are unsure or uncomfortable with the potential risks, it may be best to refrain from accessing the Dark Web altogether.
Ultimately, while the Dark Web may hold intrigue and fascination, it is essential to always prioritize your safety and act responsibly. Stay informed, be cautious, and make informed decisions to ensure a more secure and controlled experience while exploring the hidden corners of the internet.