Encryption is not a concern for most people. We commonly associate this level of secrecy with government agencies, big celebrities, and spies. Who would want an Average Joe’s data? However, everyone wants everyone else’s data nowadays. Your information is being used for politics, advertising, and hacking. Encryption is no longer for the rich and the powerful: entities and companies are realizing that your data is the most important thing to have. With this, it is a good idea to practice good cybersecurity like using encrypted messaging apps.
Encrypted messaging apps keep your data private by using end-to-end encryption. Just like disposable emails, this also keeps it safe from hacks and protects your free speech.
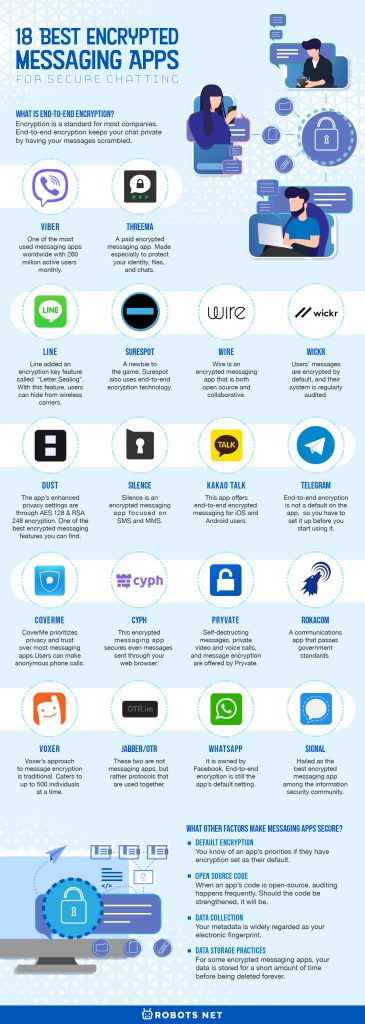
What is end-to-end encryption?


Encryption is a standard for most companies. Whenever you send an email, the content of your messages is protected. Yet, the company facilitating the exchange holds the key to your messages. These are called decryption keys.
End-to-end encryption keeps your chat private by having your messages scrambled. There is no decryption key, and even the app developers don’t have access to your messages. The encryption would be like locking your bedroom door.
If a messaging app has end-to-end encryption, your personal conversations are truly personal. Only you and the person you’re talking to have the “keys” to your messages. No one can track your messages. Every text, photo, video, and file shared is between you and the other person only.
18 Encrypted Messaging Apps for Secure Chatting
Viber


Viber is one of the most used messaging apps worldwide with 260 million active users monthly. This is well deserved since the app is available on Mac, Windows, iOS, and Android.
More importantly, the application is also one of the best encrypted messaging apps you can find. As long as you solely use Viber, that is.
End-to-end encryption has been a reality for Viber users for four years now. If you use Viber, you might realize that your chats are color-coded. These color-coded chats are a result of the encryption feature. As a guide, gray means communication is encrypted; green means you are chatting with a trusted contact; red means you have authentication issues.
Self-destructing messages are also a feature for Viber if you use the secret chats feature. This safety protocol is not just available for chats; it’s effective for calls and file sharing, too.
Unfortunately, this encrypted messaging app can only encrypt personal messages between two people. Group chats are not as protected as their private counterparts.
Threema


Before we get into anything, Threema is a paid encrypted messaging app. This might push some users away, but we are here to tell you that this app is worth its price.
This encrypted messaging app is made especially to protect your identity, files, and chats. It is its selling point and accomplishes it in comprehensive ways.
Threema uses end-to-end encryption for calls and texts. It is open source and is continuously audited for users’ protection. It’s also notable that your Threema account can be set up without an email address or a phone number to aid the anonymity of its users.
Now, you might be wondering how logging in works if you do not give away personal information for a Threema account. Put simply, it generates a unique log-in key for you. This upholds the said anonymity for all transactions (if you want to).
This app also has a “Private Chats” feature to protect your chats from information and identity theft. This feature gives your individual chats a private PIN code.
As for your messages, the Threema developers said that your messages are deleted once they are delivered.
A degree of caution must be had when using Threema, or any messaging app, though. Governments can still collect data from these messaging apps should they ever want to.
LINE


LINE is a famous free messaging app based in Japan. It have over 300 million users and has all the essential messaging features like voice calls and group chats.
While encryption is not the main reason people use LINE, it is proudly one of the app’s uses.
About two years ago, LINE added an encryption key feature called “Letter Sealing”. With this feature, users can hide from wireless carriers. The chat juggernaut strengthened their security system as a result of this update.
LINE users can now chat through the encrypted messaging app safely. Private information can no longer be disclosed to a third party, especially because chats have an encryption key.
Surespot
A newbie to the game, Surespot also uses end-to-end encryption technology. Its instant-messaging practices are open source.
Every message, image, and voice message you send is encrypted. No one can penetrate your conversations, and your data will not be shared with anyone else.
Data storage is not practiced on the platform. However, Surespot can transfer your data to other devices if you have messages you want to keep. This can be done through either PC or Mac.
Wire


Video calls are rarely talked about on encryption, but these calls reveal so much more about your identity than text chats do. If you are worried about this, you should try out Wire.
Wire is an encrypted messaging app that is both open source and collaborative. Its unique features include encrypted video calls, secure file sharing, synced messages on your devices (as long as you’re signed into them), self-destructing messages, session verification, and password locks. In simpler terms, Wire has all the end-to-end encryption you’re looking for.
Don’t worry about syncing your messages, too: Wire does not keep information stored on the infamous cloud.
The best part? It’s free. Well, if you’re going to be using it on your own. Wire is so successful in end-to-end encryption that it offers paid plans for large corporations and organizations.
When using Wire on the web, though, make sure no one else has access to your browser.
Wickr
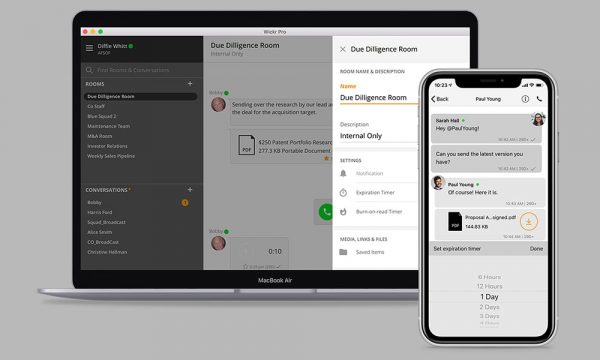
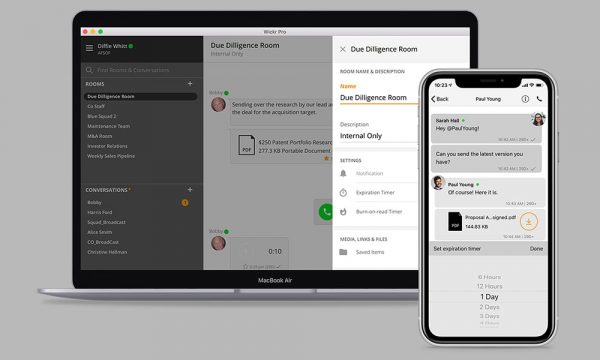
Wickr is one of the first messaging apps founded on the principles of end-to-end encryption. Users’ messages are encrypted by default, and their system is regularly audited.
This encrypted messaging app can be downloaded for free (Wickr Me) or for a price (Wickr Pro). The latter is used by big businesses that need all of their information secure. Wickr Me is fine all on its own for individuals.
Also an open-source platform, Wickr has several security measures. These include screenshot detection, blocking of third-party keyboards (on iOS), and permanent obliteration of your files. All Wickr users can also benefit from self-destructing messages, information deletion, and screenshot banning (on Android).
Not a lot of people use Wickr, which is a shame since it is probably the best encrypted messaging app you can download.
Dust


Dust is also an end-to-end encrypted messaging app. It is founded by Shark Tank billionaire Mark Cuban and is available for both iOS and Android devices. To start, no messages are stored forever on Dust phones and servers. The app’s enhanced privacy settings are through AES 128 and RSA 248 encryption. This is one of the best encrypted messaging features you can find.
Dust is also one of the rare messaging apps that explains their name. Messages on the encrypted messaging app are called “Dusts” because they disappear within 100 seconds of being read. You can fix this feature in the settings if you want messages to stay for 24 hours.
There are also “Blasts”, which you can send to several people privately, and “Groups”, which are your regular group chats. Screenshots are also actively monitored, and Dust has an interesting feature for this. On Android phones, the messenger’s name is removed if someone attempts to screenshot a message. On iOS devices, however, you will only be notified when someone takes a screenshot of your conversation. This isn’t because of Dust playing favorites, but rather because Apple does not block screenshots.
Some users complain about Dust not being open-source. If this is not one of your concerns, then Dust is spotless.
Silence
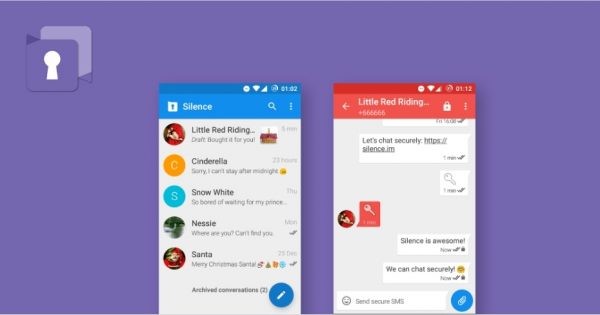
Silence is an encrypted messaging app focused on SMS and MMS. This is a sister app of Signal, another encrypted messaging app. The latter, however, deals especially with web-based instant messaging encryption.
Silence is open source and is regularly audited by professionals. The application makes sure that its systems have not been overridden by government agencies. When opening the app, you have a unique paraphrase to enter. This serves as your password or encryption key.
When messaging someone on Silence, you have access to your contacts. No need to worry: it can tell who you’re talking to but not what you’re talking about. Silence also removes the possibility of screenshotting messages. However, a negative for the app would also be its inability to encrypt video chats. SMS and MMS, after all, do not use video chats.
Kakao TALK


Data privacy and security are concerns for everyone, and this is especially true in South Korea where 90% of smartphone users have Kakao TALK. While the South Korea-based messaging app is not specifically for encryption, it has the option to be.
This app offers end-to-end encrypted messaging for iOS and Android users. This option is not a default setting for the app, so you will have to enable ‘secret chat mode’ through your settings. Setting up encryption in Kakao TALK is easy. You just have to press a button from a dropdown menu, and then you’re ready to launch your secret chat.
Telegram
Like Dust, Telegram is also founded by a billionaire or two. Brothers Nikolai and Pavel Durov, who used to work for Facebook, launched the popular app in 2013. End-to-end encryption is not a default on the app, so you have to set it up before you start using it. Like Kakao TALK, Telegram also has a ‘secret chats’ feature.
When you send messages through this feature, your messages will self-destruct across all your devices at a certain time (which you can set!). The code for the app is also open-source and uses its own protocol, MTProto, in encryption.
These are the only encryption methods Telegram practices, and only time will tell if they add more measures in the future. As of this article’s publication, it’s been found that the encrypted messaging app stores a lot of metadata. You have other choices if you have incredibly sensitive information to share.
CoverMe


CoverMe prioritizes privacy and trust over most messaging apps. A common feature for encrypted messaging apps is end-to-end encryption, but CoverMe offers something new. This app’s users can make anonymous phone calls behind US and Canadian phone numbers, and this will soon expand to Australia, UK, Belgium, and the Netherlands.
Using different phone numbers mask your area codes. People use these for both personal and business reasons as long as they want an extra level of privacy. Other features of CoverMe include encrypted phone calls, self-destructing messages, “hide-and-lock” personal texts, and a private vault for photos, videos, passwords, and other important files.
Last but not the least, third parties cannot access any data on CoverMe.
Cyph
Cyph has its own patented technology for message encryption. Using WebSign, this encrypted messaging app secures even messages sent through your web browser. They call their encryption methods ‘quantum-resistant’ and ‘future-proof’. Basically, their ciphers can automatically adjust to future advancements in quantum computing.
More importantly, auditing is done each time you use Cyph. This makes it especially hard to tamper with its codes and data. This allows you to back up your data without fear.
With Cyph, you can also securely sync across all your devices through encrypted cloud storage.
Another feature for Cyph is its ID verification where you are not required to manually verify your identity. Impersonations of you are weeded out through this feature.
Pryvate


Self-destructing messages, private video and voice calls, and message encryption are offered by Pryvate. This encrypted messaging app specifically caters to large businesses, but you can also get a free version of the app.
Using RSA-4096 encrypted voice, Pryvate can also safely function as an instant messaging platform. It is available for download globally.
RokaCom


iOS and Android users can download RokaCom, a communications app that passes government standards. This is unsurprising because RokaCom originally catered to the needs of large enterprises and government agencies.
What’s so special about RokaCom?
This encrypted messaging app has a lot of features. These features multi-device syncing, secure messaging (for text, voice, and files), and end-to-end encryption. Though pricey, RokaCom gives organizations access to its unique and private cloud server. Its features give their transactions a new level of security.
Voxer
Voxer’s approach to message encryption is traditional. Remember walkie-talkies? Well, Voxer adapted its idea and took voice-orientation to the next level.
Voxer users can listen to voice messages in real-time without painful upload speeds. These can then be played back, whether or not you choose encryption. Users can also send and receive texts, photos, videos, and location details. A big bonus for Voxer users is that it caters to up to 500 individuals at a time.
For its encrypted service, you will have to buy a subscription. For a briefing, Voxer uses the same code from Signal. You can check out that messaging app later in this article.
Jabber/OTR
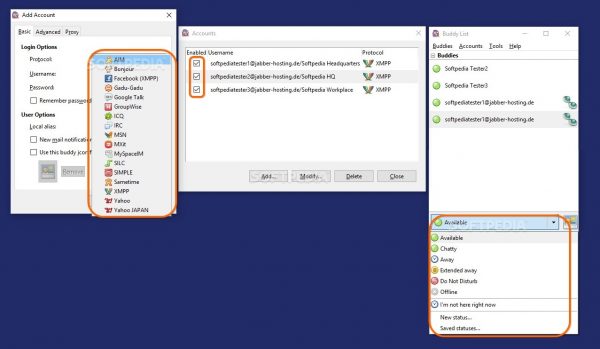
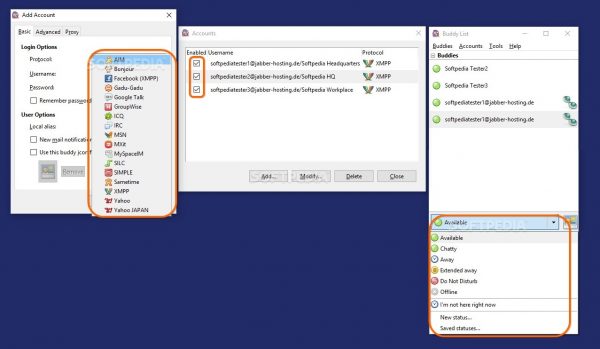
These two are not messaging apps, but rather protocols that are used together. With their tandem, you have a free, open-source, and decentralized communication platform.
Use Jabber and OTR when you’re using other messaging apps such as Pidgin, Adium, Tor Messenger, and Chat Secure. Since these are not technically messaging apps, you can set these up anonymously. Gone are the days of giving away personal information for the sake of security.
We would not suggest you use this on mobile, though, because these have a tendency to lag when running on those devices.


WhatsApp is the most disputed on this list. Why? It is owned by Facebook, and that social network does not have a good track record on information security.
For a brief background, WhatsApp was founded in 2009 as Facebook’s rival. However, its messaging became its most popular feature. As of late, end-to-end encryption is still the app’s default setting. This coexists with features such as video calling, voice messaging, and file sharing.
Facebook bought WhatsApp in 2014. Its encryption services are still ongoing, but no one knows the trajectory the app is heading in the future.
Signal


Signal is hailed as the best encrypted messaging app among the information security community is also currently growing in mass appeal. There are reasons why you should consider getting this for yourself, too.
Signal provides the standard end-to-end encryption for voice calls, video calls, and instant messages. These are done through their own code, called the Signal Protocol.
This special protocol is hailed as the most secure messaging protocol ever developed. As a brief rundown, it uses the X3DH key agreement protocol, the Double Ratchet algorithm, and AES-256 for managing encryption. The Signal Protocol is so popular that a lot of other messaging apps use it, too.
Signal’s servers only keep up with two pieces of information: the day you make an account, and your most recent log-in. It also gives you an extra layer of security by giving you an option to make a password for message protection. Self-destructing messages are a standard for Signal.
As for the future of Signal, its developers are finding a way to eliminate registration by phone number. They are planning to share profile data only through PINS and nothing else.
You cannot go wrong with the most secure messaging app.
What Other Factors Make Messaging Apps Secure?


End-to-end encryption is not the end-all of messaging security. There are other factors in keeping your data safe. Think of encryption as the requirement and these as highly recommended options.
Default Encryption
You know of an app’s priorities if they have encryption set as their default. A lot of instant messaging users do not know about this, but this is important in keeping your data safe and secure. Your texts, files, and other messages might not be protected by default.
So, if you’re using an app that does not have its encryption feature turned on, consider sending your important information elsewhere.
Open Source Code
Sharing your code for everyone else to see sounds counterproductive if you want to keep information secure. For encrypted messaging apps, however, this is always a net positive.
When an app’s code is open-source, auditing happens frequently. Experts and the community can chime in with their opinions. Should the code be strengthened, it will be. More people can safeguard your information, and more people will keep an eye on anything fishy going on.
Data Collection
Your metadata is widely regarded as your electronic fingerprint. It includes information about your device, who you’re talking to, your IP address, and your phone number/s.
Even with encrypted messaging apps, thousands of metadata are stored. So before you choose your encrypted messaging app, check how they handle your metadata. As you saw above, these are collected by apps in varying degrees.
If you want to stick with what you’re currently using, try changing your VPN. This is another way of keeping your information secure. You can download VPN apps on your mobile or laptop today.
Data Storage Practices
For some encrypted messaging apps, your data is stored for a short amount of time before being deleted forever. When you send your messages, they are not permanently saved on the app’s servers.
This should be a consideration of yours in choosing the best encrypted messaging app. Encryption is moot if your messages are still stored on the cloud.
Is an Encrypted Messaging App Enough?


Even the best encrypted messaging app will have its blindsides. When downloading these applications, be prepared for anything. With the internet and technology, people always want to bring others down.
That being said, will encrypted messaging apps be enough? It depends on the information you’re safekeeping and the information you’re willing to gamble every time you send a message through your phone. Regardless, here are other safekeeping measures you can take to beef up your information security.
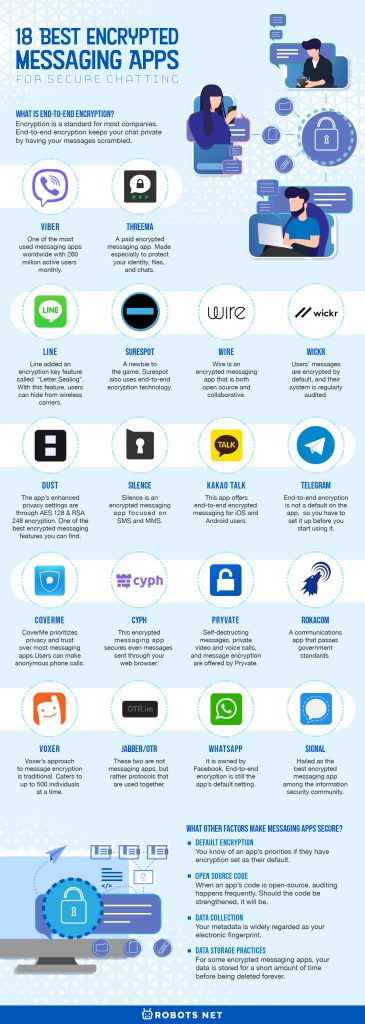
Protect Messaging Apps With a Password
Instead of using biometrics to access your device, nothing beats a strong password. Having your fingerprint scanned feels a lot like a future-fantasy come to life, but it does not increase phone security. It is better to have a password to your device and your special apps.
You can protect your photos, videos, and even sensitive card information with a better peace of mind.
Mobile Wifi Network Connections


If someone truly wanted to impersonate you, they will most likely do it through your mobile network connections. By connecting to the wrong free wifi spots, people can track your every move. They can see what public spaces you go to and how you move in them. This information will be matched to you and how you live your life. They get a very accurate understanding of your behavior.
This can also get worse. By accessing your IP addresses, people can trace it to your credit card number and your face. Be wary with the free hotspots you’re connecting to and try to add something random to your daily routine. Using encrypted messaging apps is one thing, but not having a secure connection can be crucial.
Be Careful in Downloading Apps
Download apps only from official sources. Avoid getting an app through piracy and trust that Google Play and the App Store are there for a reason. Verify your sources before you give an app access to your phone.
Once you do download your apps, be careful with what you give them access to. Luckily, this is not a problem for most if not all Android and iOS users. Android and Apple phones ask you before they give any apps permission. You can choose whether you want to share your camera, microphone, photos, and locations.
A lot of apps are data-hungry, and you have to be skeptical about them. As with encrypted messaging apps, audit your phone as much as you can. If you’re no longer using an app, feel free to delete it! Lessen your virtual thumbmark.
SIM Card Switching


This is the least probable thing you will do, but if you can, you should switch your SIM cards. This does not eliminate your chances of being hacked, but it lessens the threat dramatically. It makes snooping around your information even harder.
Should you buy SIM cards, make sure you buy them from different stores. Also, buy them with cash to make it more difficult for hackers to track your purchasing habits.
Lastly, when using this method of safekeeping, you will need two phones. You can be tracked if your SIM cards do not coexist because your phone has special identifiers of its own.