Introduction
In the vast digital landscape, web browsers serve as our gateway to the online world, allowing us to explore, connect, and access a myriad of information with just a few clicks. However, this convenience comes with its own set of risks, one of which is the presence of browser hijackers. These intrusive pieces of software can disrupt our browsing experience, compromise our privacy, and even expose our devices to security threats.
Understanding the nature of browser hijackers is crucial for safeguarding our online activities and protecting our digital assets. By delving into the workings of these insidious entities, we can equip ourselves with the knowledge needed to identify, prevent, and eradicate their presence from our systems.
In this article, we will embark on a comprehensive exploration of browser hijackers, shedding light on their definition, operational mechanisms, common symptoms, preventive measures, and effective removal strategies. By unraveling the complexities of this digital menace, we aim to empower users with the insights necessary to fortify their online defenses and preserve the integrity of their browsing experiences.
Definition of Browser Hijacker
A browser hijacker is a type of malicious software designed to alter the behavior of a web browser without the user's consent. This unauthorized modification can manifest in various forms, such as changing the default homepage, search engine, or new tab page, as well as injecting unwanted toolbars, extensions, or advertisements. The primary objective of a browser hijacker is to redirect web traffic to specific sites or to generate revenue through deceptive advertising practices.
Unlike traditional malware that directly damages or steals data from a system, browser hijackers operate under the guise of seemingly legitimate browser enhancements or search engine tools. Once installed, they stealthily manipulate the browser settings, often making it challenging for users to revert to their preferred configurations. This surreptitious behavior allows browser hijackers to persist undetected, exerting control over the user's browsing activities while potentially exposing them to security vulnerabilities and privacy breaches.
Furthermore, browser hijackers can infiltrate a user's system through various channels, including software bundling, deceptive download links, or misleading advertisements. They often masquerade as free utilities, browser add-ons, or multimedia players, enticing unsuspecting users to install them under the guise of offering enhanced browsing features or improved search capabilities. Once embedded within the browser, these hijackers can initiate a cascade of undesirable effects, disrupting the user's online experience and undermining the integrity of their browsing environment.
In essence, a browser hijacker represents a covert intrusion into the user's digital domain, subverting the autonomy of their browsing preferences and subjecting them to a barrage of unwanted redirects, pop-ups, and altered search results. By understanding the defining characteristics of browser hijackers, users can discern their presence, thwart their incursion, and safeguard their browsers from unauthorized manipulation.
How Browser Hijacker Works
Browser hijackers employ a multifaceted approach to infiltrate and exert control over a user's web browser, leveraging deceptive tactics and stealthy maneuvers to subvert the user's browsing experience. These insidious entities often gain access to a system through deceptive software installations, misleading advertisements, or compromised websites. Once embedded within the browser, they initiate a series of disruptive actions aimed at redirecting web traffic, altering search results, and inundating the user with intrusive advertisements.
One of the primary mechanisms through which browser hijackers operate is by modifying the browser's settings without the user's explicit consent. This can involve altering the default homepage, search engine, or new tab page to redirect the user to predetermined websites or to display sponsored content. By usurping these critical browser configurations, the hijacker effectively steers the user's online activities towards specific destinations, often with the intent of generating revenue through deceptive advertising practices.
Furthermore, browser hijackers may clandestinely install unwanted toolbars, extensions, or plugins within the browser, thereby augmenting their control over the user's browsing environment. These additions can introduce additional layers of obtrusive advertising, track the user's online behavior, or collect sensitive information, further compromising the user's privacy and security.
In some instances, browser hijackers may also manipulate search results, injecting sponsored links or advertisements into the user's query outcomes. This surreptitious alteration of search results can lead to the dissemination of misleading or potentially harmful content, potentially exposing the user to fraudulent schemes or malicious websites.
Moreover, browser hijackers often employ persistence mechanisms to evade detection and removal, ensuring their continued influence over the user's browsing activities. By integrating themselves deeply within the browser's architecture and leveraging stealthy techniques, such as rootkit installations or registry modifications, these hijackers can elude traditional security measures and persist within the user's system.
In essence, the operation of a browser hijacker hinges on its ability to surreptitiously manipulate the user's browser settings, redirect web traffic, and inundate the user with unwanted advertisements. By understanding the intricate workings of these digital intruders, users can fortify their defenses, remain vigilant against deceptive tactics, and safeguard their browsing experiences from the pernicious influence of browser hijackers.
Common Symptoms of Browser Hijacker
Identifying the presence of a browser hijacker is pivotal in mitigating its disruptive impact on one's browsing experience. By recognizing the telltale signs of a hijacked browser, users can promptly take remedial action to restore the integrity of their online activities. Here are the common symptoms that may indicate the presence of a browser hijacker:
-
Altered Browser Settings: One of the most conspicuous indicators of a browser hijacker is the unauthorized modification of browser settings. This can manifest as a sudden change in the default homepage, search engine, or new tab page, redirecting users to unfamiliar or suspicious websites upon launching the browser.
-
Unwanted Toolbars or Extensions: The presence of unfamiliar toolbars, extensions, or plugins within the browser, especially those that were not intentionally installed by the user, can signify the intrusion of a browser hijacker. These additions may clutter the browser interface and introduce unwanted functionalities.
-
Frequent Redirects: Users may experience frequent and unexplained redirects to unfamiliar websites, often unrelated to their intended browsing activities. These redirects may lead to dubious or potentially malicious sites, disrupting the user's online experience and raising concerns about the security of their browsing environment.
-
Incessant Pop-up Advertisements: The sudden proliferation of intrusive pop-up advertisements, especially those promoting questionable products or services, can indicate the presence of ad-injecting browser hijackers. These ads may appear irrespective of the user's browsing context, impeding their ability to navigate the web seamlessly.
-
Sluggish Browser Performance: A browser hijacker's presence can lead to diminished browser performance, causing sluggishness, unresponsiveness, or frequent crashes. These performance issues may arise due to the hijacker's resource-intensive activities or its interference with the browser's normal functioning.
-
Unexplained Changes in Search Results: Users may notice that their search results are being manipulated, with an influx of sponsored links, advertisements, or irrelevant content interspersed among the genuine search outcomes. This alteration of search results can undermine the user's ability to access accurate and reliable information.
-
Privacy Concerns: Browser hijackers may compromise the user's privacy by tracking their online activities, collecting sensitive information, or transmitting data to third-party servers without consent. Users may observe unauthorized data collection practices or notice a breach of their privacy due to the hijacker's presence.
By remaining vigilant for these symptoms, users can promptly identify and address the presence of a browser hijacker, thereby safeguarding their browsing experience and preserving the security of their digital environment.
How to Prevent Browser Hijacker
Preventing the infiltration of browser hijackers necessitates a proactive approach to fortifying one's digital defenses and cultivating safe browsing habits. By implementing a combination of security measures and prudent online behavior, users can significantly reduce the risk of falling victim to these insidious entities. Here are several effective strategies to prevent browser hijackers:
-
Exercise Caution When Installing Software: Be discerning when downloading and installing software, especially from unverified sources or unfamiliar websites. Opt for reputable download platforms and scrutinize the installation process to avoid inadvertently bundling browser hijackers with legitimate software.
-
Keep Software Updated: Regularly update your operating system, web browser, and security software to patch vulnerabilities and mitigate the risk of exploitation by browser hijackers. Timely updates ensure that known security flaws are addressed, bolstering the resilience of your digital ecosystem.
-
Utilize Security Software: Deploy reputable antivirus and antimalware solutions to proactively detect and neutralize potential threats, including browser hijackers. These security tools can provide real-time protection, conduct system scans, and offer additional layers of defense against malicious software.
-
Exercise Vigilance Online: Remain cautious when interacting with online content, especially advertisements, pop-ups, and download links. Exercise restraint when clicking on unfamiliar or suspicious elements, as these can serve as entry points for browser hijackers and other forms of malware.
-
Verify Browser Extensions and Add-ons: Prior to installing browser extensions or add-ons, verify their legitimacy and scrutinize user reviews and ratings. Opt for extensions from reputable sources and exercise discretion when granting permissions to these additions.
-
Customize Browser Security Settings: Leverage the security features offered by your web browser, such as pop-up blockers, phishing protection, and safe browsing settings. These built-in safeguards can fortify your browser against potential hijacking attempts and malicious content.
-
Educate Yourself and Others: Stay informed about the latest cybersecurity threats and educate yourself on best practices for safe browsing. Share this knowledge with friends, family, and colleagues to collectively bolster the resilience of the digital community.
By integrating these preventive measures into your digital routine, you can fortify your defenses against browser hijackers and cultivate a secure and resilient browsing environment. Vigilance, informed decision-making, and proactive security measures are pivotal in mitigating the risk of browser hijacker infiltration, empowering users to navigate the online landscape with confidence and peace of mind.
How to Remove Browser Hijacker
Removing a browser hijacker from your system requires a systematic approach to identify and eliminate the intrusive software while restoring the integrity of your web browser. Here are the steps to effectively remove a browser hijacker:
-
Identify Suspicious Programs: Begin by scrutinizing your installed programs and browser extensions for any unfamiliar or suspicious entries. Access the list of installed programs on your system and review the installed browser extensions or add-ons to pinpoint any potentially unwanted software associated with the browser hijacker.
-
Uninstall Suspicious Software: Once identified, proceed to uninstall the suspicious programs from your system. Navigate to the Control Panel on Windows or the Applications folder on macOS to initiate the uninstallation process. Follow the on-screen prompts to remove the unwanted software, ensuring that all associated components are thoroughly eliminated.
-
Reset Browser Settings: To purge the lingering effects of the browser hijacker, reset your web browser to its default settings. This can typically be accomplished through the browser's settings or preferences menu. Resetting the browser will eradicate any unauthorized modifications imposed by the hijacker, restoring the browser to its original state.
-
Scan for Malware: Conduct a comprehensive malware scan using reputable antivirus or antimalware software. Initiate a full system scan to detect and eliminate any residual traces of the browser hijacker or other potential threats. Follow the recommended actions provided by the security software to quarantine or remove the identified malware.
-
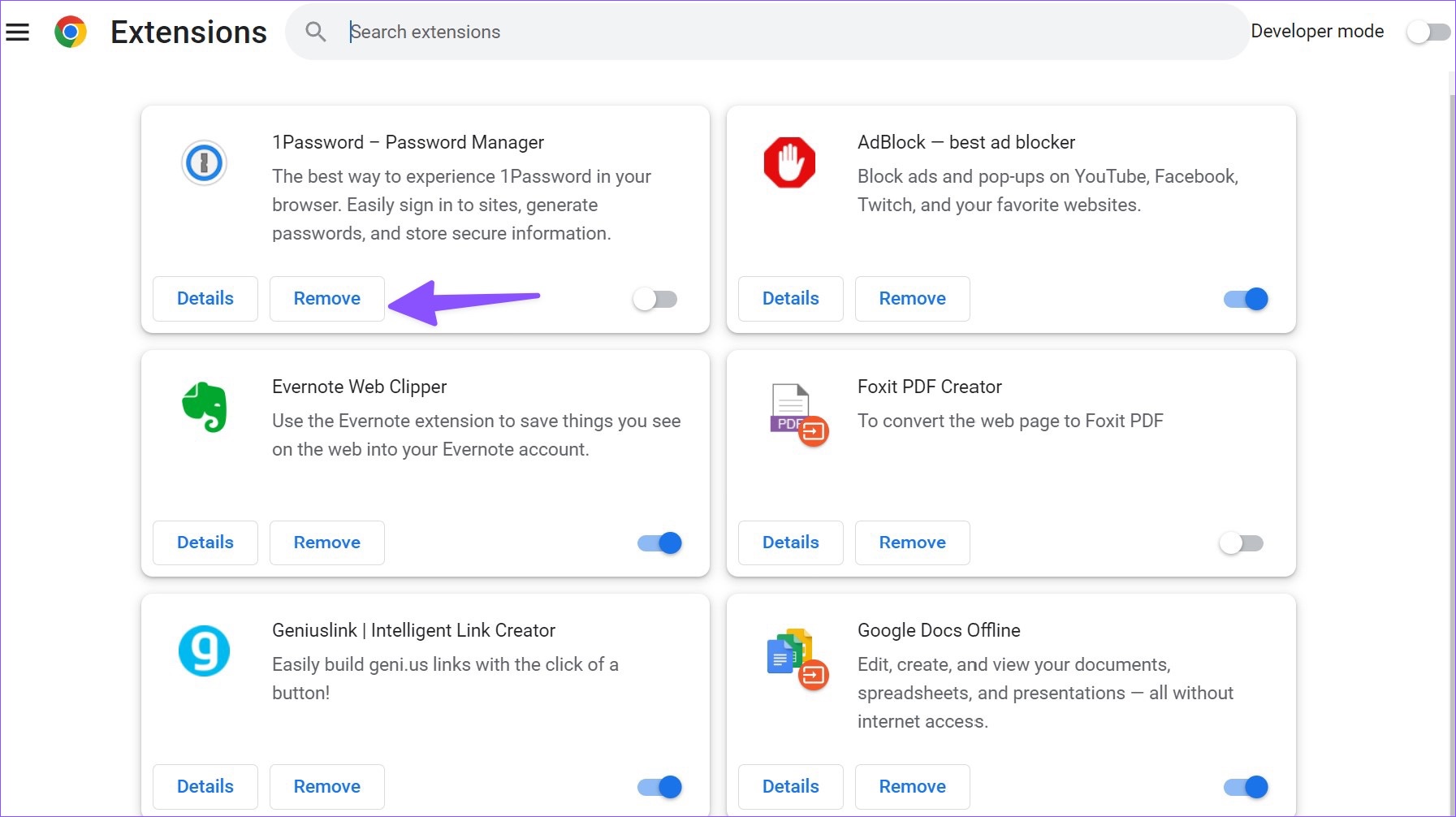
Review Browser Extensions: After removing the suspicious software and resetting the browser, review the installed browser extensions or add-ons. Ensure that only legitimate and trusted extensions remain active. Remove any remaining extensions that exhibit suspicious behavior or are linked to the browser hijacker.
-
Clear Browser Data: Purge your browser's cache, cookies, and browsing history to expunge any remnants of the hijacker's activity. This can be accomplished through the browser's settings or privacy controls. Clearing this data helps eliminate any persistent tracking or re-infection vectors associated with the browser hijacker.
-
Monitor for Anomalies: After completing the removal process, monitor your browser for any lingering anomalies or signs of unauthorized activity. Remain vigilant for unexpected redirects, intrusive advertisements, or other irregularities that may indicate the persistence of the browser hijacker.
By diligently following these steps, you can effectively remove a browser hijacker from your system and restore the integrity of your web browser. It is essential to remain proactive in maintaining a secure digital environment, staying informed about potential threats, and implementing robust security measures to safeguard against future intrusions.