Twenty years ago, the internet was a bare skeleton. However, in the last two decades, the industry has experienced exponential growth. Moreover, there is an unimaginable amount of data stored everywhere. There was little need for database security best practices.
Since our databases are data mines for the hackers, they are always eager to devise newer ways of attacking and stealing the information.
As the name suggests, database security refers to a set of practices or protocols that must be in place to thwart or at least diminish the probability of a cybersecurity event.
In this article, we will explore a variety of database security practices. Please note the list does not depict any order or preference, whatsoever.
Best Practices For Database Security
Before we start discussing the list, it is important to understand that the foremost measure requires you to ensure the physical security of your database. It is as simple as it sounds. It implies that you should place the server containing your DB in a secure location with only privileged access. In ideal cases, it is advisable not to rest your database on a public server.
1. Firewalling
Now that we have discussed the physical aspect, let’s talk about how firewalling could enhance database security. Its purpose is to allow only “permitted” traffic to pass through the barrier before accessing the server.
Depending upon the scenario, you might want to consider using a web application firewall to prevent an attack through SQL injection. This directs at your database and tries to make modifications in the stored data.
In plenty of cases, a firewall is also useful in ensuring that there is no unnecessary outbound connection unless required by the application utilizing the database.


2. Hardening
This is a generic term covering an array of practices that must be performed if you want to keep your database “absolutely secure.”
To start with, you must know the vendor or open source project who made the database you are using. Also, make sure that you are always using one of the recent versions. Sometimes, people do not bother to look up the internet and continue using the DBs for several years even after the vendor’s official discontinuation of the product.
Moreover, it is also important to keep tabs on what’s unnecessary on your server. Since there are many Content Management Systems these days, people simply “disable” the 3rd party apps. If that app turns out to be malicious, then you might bring down wrath on your server and ultimately, the database. Therefore, when you do not need something, get rid of it from your server before it is too late.
There are plenty of tools in the market that you could use to notify you when an unexplainable change happened to your hardened settings.


3. Encrypting
Well, the name says it all!
Encryption of stored data is a regular procedure in most of the organizations. However, they often forget about encrypting the backups. That’s how the hackers hunt for information. Another important aspect is to segregate the stored data and decryption keys. If they are in the same location, you are offering butter and bread to the hacker!
After securing the stored data, it is also crucial to take necessary measures and ensure that when data moves from location A to location B, it always travels through an encrypted channel to avoid external breaches.


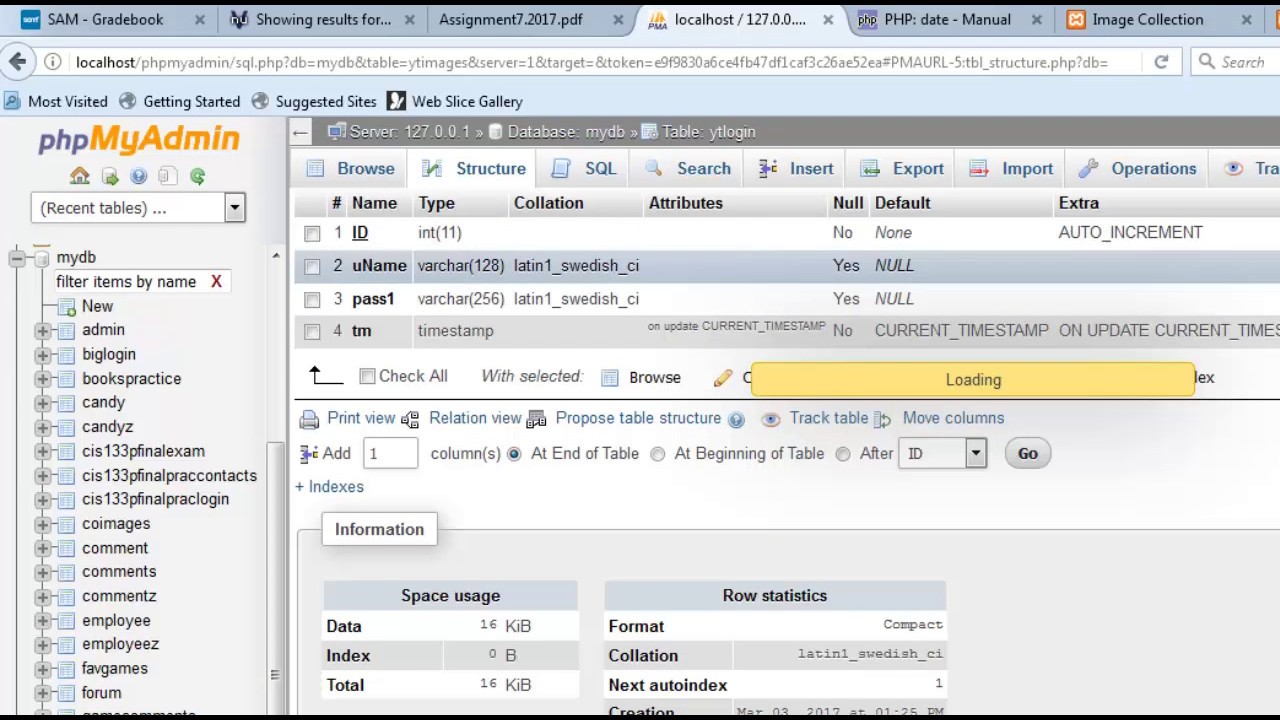
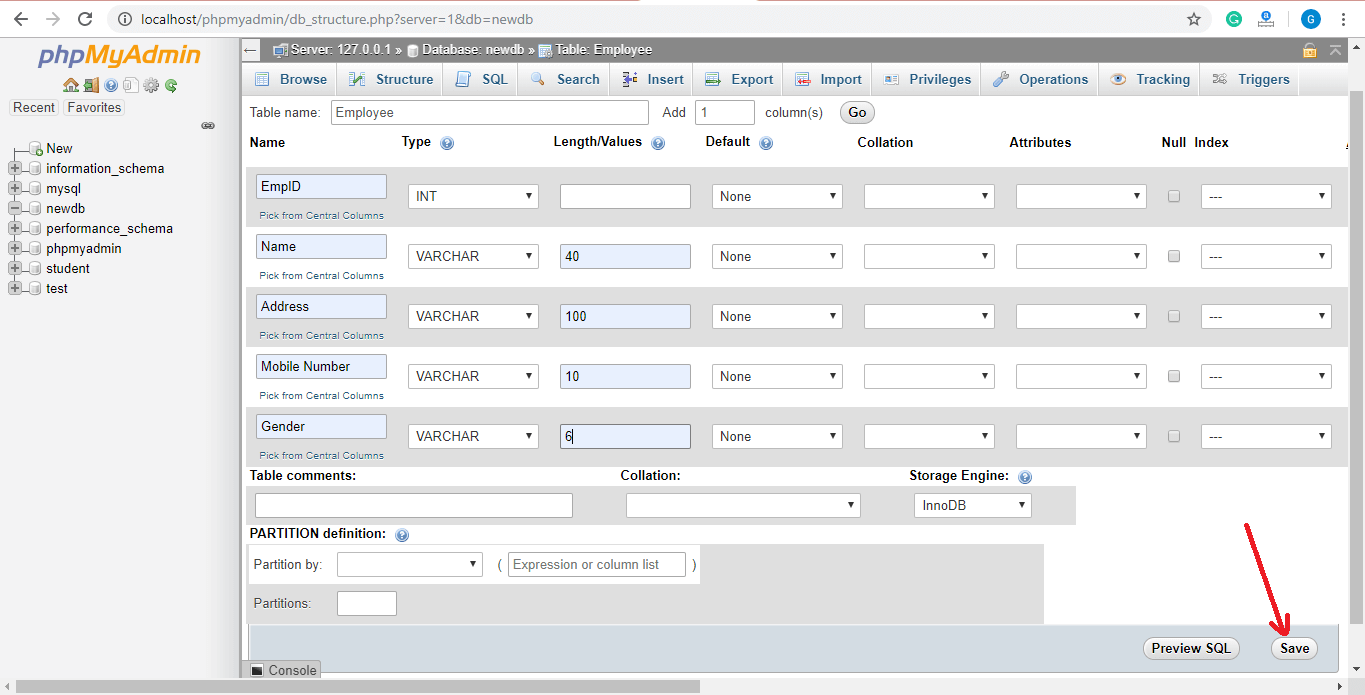
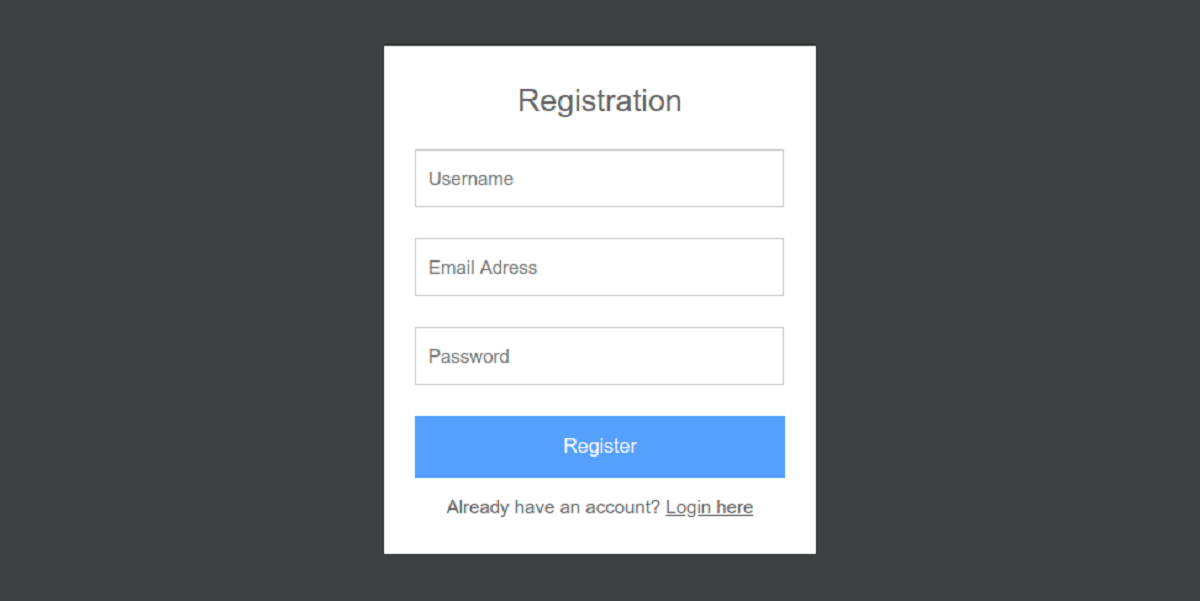
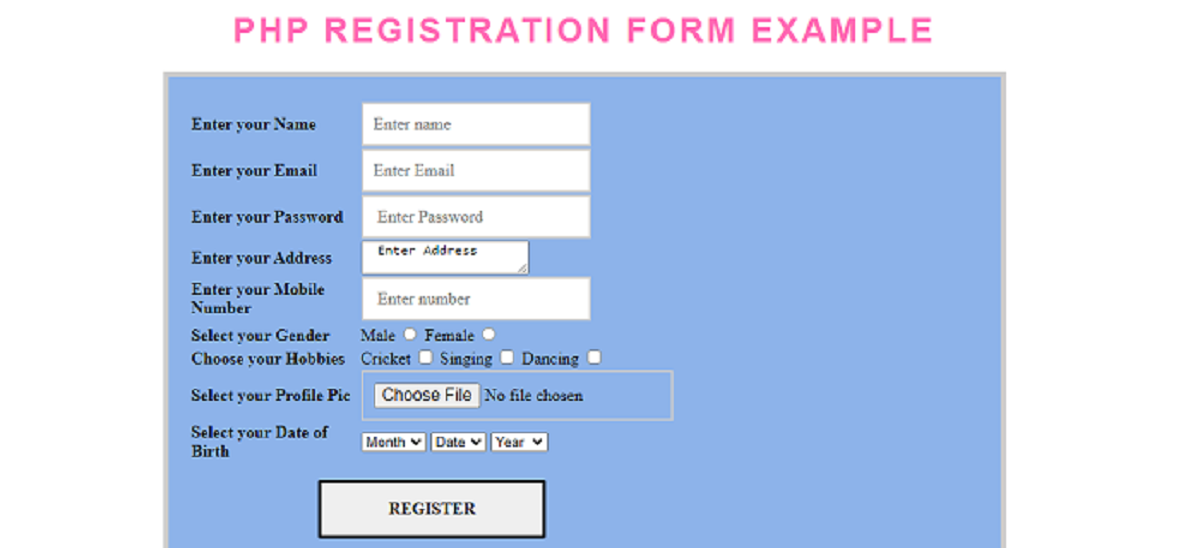
4. Authenticating
This is another basic requirement. It comes in handy when you want to optimize database security. Authentication requires you to identify the people who might need access to the database, for any reasons. Once you do that, it is ideal to give them a username and password. This way, they can verify their credentials every time before gaining access.
There are multiple types of authentications. For the external one, you could simply define the users. Moreover, the network service or OS can authenticate them before granting access. In some cases, SSL might also be used for the same purpose.
Furthermore, if your organization is pretty big, it is ideal to opt for an enterprise directory and define the roles of different users to ensure they are only given access to particular sections of the database.
All of these database security measures depend upon the nature of your organization and the related approach you can afford (in terms of resources and efficiency) for daily operations.
5. Patching
All vendors release regular patches to ensure that their products are up-to-date and there is no technical glitch. Therefore, as an end-user, it is your prime responsibility to look for the released patches regularly to keep your database secure.
It is worth noticing that since older versions are in the market for long, the possibility of any hacking attempt is also higher. This is because hackers know about their loopholes. However, if you install the latest service packs by the vendors, there is no such reason to worry.
It must be noted that some network administrators install the service packs straight in the production phase. This is not a good practice even if you are an expert. The best approach is to test each aspect in a local environment or sandbox, in segregation from the production model.


6. Disabling JS Execution
This is a very crucial data security practice, particularly if you are using MongoDB. As an expert DB administrator or programmer, the words “execution” and “arbitrary” should ring bells to you if used in the same sentence.
By disabling JS execution, you can ensure that no one can retrieve the details of the users or other entries. Just to clue you in, operators including “where” and “group” can expose your entire database with a single query.
The thing is, most of these functions always return a true value which a hacker can exploit. Therefore, DB administrators need to lock down JS execution access.
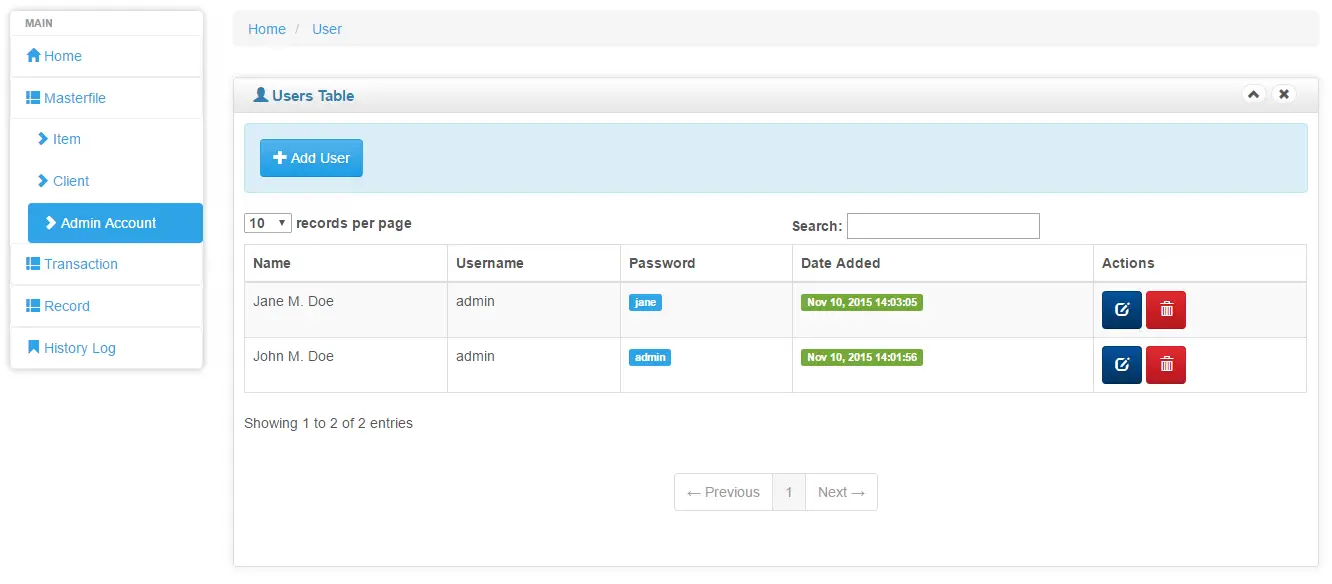
7. Managing Access
Some vendors do not offer access control by default. This is yet another loophole exploited by hackers to gain unauthorized access. To enhance database security, it is a good idea to implement access controls and restrict the people who can run commands and operations on your DB.
However, before you can implement access control, you must create an admin account first, so that the admin can manage the controls.
As a result of this, every user who requests access to the database would have to provide his credentials, provided by the administrator. If they don’t match, there is no easy way of seeing what is in the database.
Every time you change the access control, it is advisable that you restart the respective database service to ensure that the changes are applied.
8. Auditing / Monitoring
It is important to keep tabs on database changes and ensure that no suspicious activities are going on for the organization. Fortunately, there are several system auditing tools in the market, and you could use any of them (if applicable), depending on your requirements.
Moreover, some organizations also go for custom configurations to address the core concern of system auditing. They do this by writing the events to a file or a Syslog connection, whatever they find convenient and most usable. Once the collection of data, it is sent to a Security Information and Event Management Tool to perform a comprehensive analysis and determine whether any changes in the settings pose a threat to the database.
9. Testing And Addressing The Irregularities
If your database or its related settings show some irregularities, it is in your best interest to fix them before a hacker exploits these vulnerabilities. Apart from appointing a diligent DB administrator, you should also define guidelines for your programmer to ensure that their work is always as less prone to exploitation as possible.
Of course, it happens to be a tiring process. However, it is achievable if there’s a division of roles within the organization and all the workers follow a database security guideline while doing their work.
Hint: Pay attention to the development and integration phases to avoid irregularities.
10. Minimizing The Value
This is the last thing in our list, and it is pretty self-explanatory. By nature, hackers want to bring down a system with maximum value. As an organization, you are also forced to keep all of your details somewhere where digital access is handy. However, we strongly suggest you diminish the value of your database by not storing “important but unnecessary” information. For instance, if your website accepts credit cards, there is no need to store your customers’ credit card numbers and security codes together.
In some cases, you might want to take sensitive information from the users and then store in your database. That’s fine because your business depends upon it. However, as soon as it becomes outdated for your organization, delete it permanently from your server.