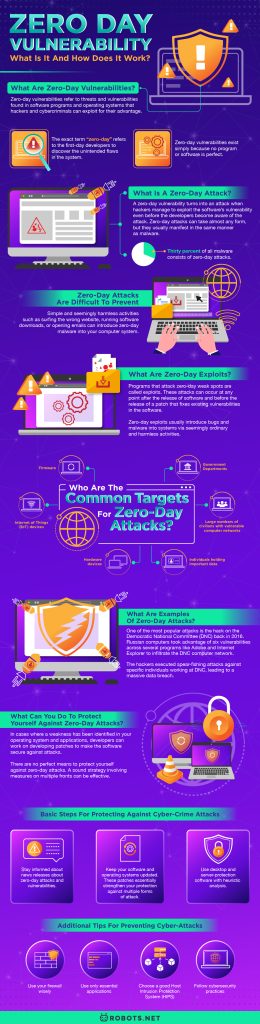
Many might be familiar with zero-day attacks. However, not a lot know what it means or how we can protect ourselves against this form of attack. Most firewalls and antivirus programs cannot protect against zero-day attacks, and the looming threat only increases over time. Let’s find out what these vulnerabilities and attacks are, how they happen, and how they affect data security.


What are Zero-Day Vulnerabilities?
Zero-day vulnerabilities refer to threats and vulnerabilities found in software programs and operating systems that hackers and cybercriminals can exploit for their advantage. The exact term “zero-day” refers to the first-day developers to discover the unintended flaws in the system. it also refers to the first day that developers work on a code to patch up the vulnerability. Hackers that use Zero-day can manipulate code to achieve anything from surveillance to theft. Suppose we can use an analogy to clarify the concept. In that case, zero-day vulnerabilities are much like open windows in a house where criminals can enter and wreak havoc.
Vulnerabilities are open doors for attackers to introduce malicious codes and allow the attackers to take control of the software that runs the system. This is why zero-day attacks are often coupled with bugs designed to take control of systems. The most popular of these bugs are called remote code execution. This lets hackers break into devices without being dependent on any action from their targets. It can happen regardless of where you are.
Zero-day vulnerabilities exist simply because no program or software is perfect. There are many vulnerabilities with any given software or program at any given time. Zero-day vulnerabilities also sell on the black market for thousands, even millions, of dollars. The selling price would depend on the software the vulnerabilities are in and how useful these can be to achieve a particular purpose. Just a few months ago, internet sleuths confirmed the existence of two zero-day exploits on the video conferencing software Zoom. The information was being sold on the dark web and potential buyers included anyone with nefarious intentions and even government spy agencies.
What is a Zero-Day Attack?


A zero-day vulnerability turns into an attack when hackers manage to exploit the software’s vulnerability even before the developers become aware of the attack. In most cases, the developers will know that there is a vulnerability in the code. However, it is possible that they have no publicly available fixes for the attack. Zero-day attacks can take almost any form, but they usually manifest in the same manner as malware.
In fact, thirty percent of all malware consists of zero-day attacks. Symptoms of a malware attack often include very slow internet, missing data encryption, computer crashes, hard drive malfunctioning, disabled security solutions, unusual network activities, and more. Check out this article about why your internet could be working too slowly.
Most zero-day attacks comprise of fresh malware, which is very difficult to detect and diagnose. That’s because zero-day attacks usually aren’t detected by antivirus programs and firewalls because these tools rely on the signatures of known malware and can only flag signatures of known malware.
Most zero-day attacks comprise a new malware re-engineered from older forms of malware or created from new malware binaries. Zero-day attacks can come from any place at any time, and this high level of unpredictability makes them very difficult to detect and diagnose. Check out this list of the best free malware removal tools you can use as a first recourse.
Zero-Day Attacks Are Difficult to Prevent


This unpredictable nature also makes it very easy to contract on any platform. Simple and seemingly harmless activities such as surfing the wrong website, running software downloads, opening emails, or clicking on pop-up notifications can introduce zero-day malware into your computer system. Hackers love to exploit zero-day vulnerabilities to penetrate business networks and even individual networks. Hackers sometimes love to play cat-and-mouse games with software companies to show their dominance.
And sadly, for the rest of us, the only real way to prevent attacks is to wait for the software manufacturer to develop patches for the zero-day vulnerabilities. Sometimes software manufacturers don’t even discover zero-day vulnerabilities until after a major incident. Sometimes they don’t even discover it until a third-party security firm informs them of a vulnerability that has been exploited. Developing a patch can also take anywhere from weeks to months, or even years to complete.
What are Zero-Day Exploits?


Programs that attack zero-day weak spots are called exploits. In their developed form, they can infiltrate any software with the same code. These attacks can occur at any point after the release of software and before the release of a patch that fixes existing vulnerabilities in the software. This can be a race between the good guys and the bad buys. Will the software manufacturer develop a fix for the bug, or will hackers learn to use these vulnerabilities before they can release a patch?
Zero-day attacks are particularly dangerous because no one has seen them before. It’s also for this same reason that they are difficult to defend against. Any form of attack can occur anytime between the program’s release and the release of a security update that can patch up the problem. Zero-day exploits usually introduce bugs and malware into systems via seemingly ordinary and harmless activities. Anything from accidentally visiting a fake website or opening a malware-infested link can lead to a system infection. In most cases, the victims remain helpless and unaware until the next software update comes along. Some hackers even time their zero-day attacks after the company releases patches or security updates for unrelated vulnerabilities.
Microsoft experienced this last year when cybercriminals took advantage of their monthly security updates to execute zero-day attacks targeting remaining vulnerabilities. Cybercriminals timed their attacks just after Patch Tuesday – the second Tuesday of each month when Microsoft releases patches for vulnerabilities it has found. Microsoft avoids releasing information about vulnerabilities it has discovered. But hackers are able to look for ways to detect and exploit them even before the company can get the chance to respond. Security experts have coined the term “zero-day Wednesday” to describe this strategy.
Who Are the Common Targets for Zero-Day Attacks?


Hackers would have different targets for their exploits. Anyone can be a target — including government departments, individuals holding important data, and large numbers of civilians with vulnerable computer networks. Cybercriminals can also get through to hardware devices, firmware, and the internet of things (IoT) devices. If you want to know which of your properties could be at risk, check out this piece on the best IoT platforms to keep an eye on in 2020. In some cases, government spy agencies like the FBI and CIA harvest information on zero-day vulnerabilities. They use vulnerabilities as a point of entry on organizations and individual networks that threaten national security.
What are Examples of Zero-Day Attacks?
Traditional zero-day attacks have been known for a while now. As such, it is relatively easier to understand what exactly takes place. There have been numerous attacks across the history of software companies, and these have blended in well with the vast repository of cybercriminal activities. One of the most popular attacks is the hack on the Democratic National Committee (DNC) back in 2016. Russian computers took advantage of six vulnerabilities across several programs like Adobe and Internet Explorer to infiltrate the DNC computer network. The hackers executed spear-fishing attacks against specific individuals working at DNC, leading to a massive data breach.
The attacks that we hear about usually have to do with business networks. For example, Google Chrome experienced an attack that exploited zero-day vulnerabilities to deliver malware in a campaign called Operation WizardOpium. The series of attacks had plenty of similarities with previous attacks that were carried out in Korea over the past few years. Hackers created a fake Korean-language news portal and inserted malicious JavaScript code that would load malware once opened. Another attack against Google took advantage of a vulnerability in the software to gain additional privileges in controlling the software. Hackers sent out phishing emails requesting users to download a malware-infected app that would conduct surveillance on the users.
International Cases
In rare cases, hackers execute large-scale attacks against multiple organizations at once. Operation Aurora was one of the more sophisticated attacks against dozens of organizations at one time. The hackers exploited zero-day weaknesses in Internet Explorer to gain access to and modify source code repositories at high-end security companies.
Their targets included Adobe, Symantec, Google, and more. The hackers made off with Google’s intellectual property assets and copied the contents of select Chinese dissidents’ emails. Even worse, the exploit code used in the attack was uploaded online, which may be used by other cybercriminals to craft new attacks.
The Stuxnet attack is another example of a large-scale zero-day attack. Hackers took advantage of vulnerabilities in software running on industrial computers used for manufacturing purposes. These computers are known as programmable logic controllers (PLCs), and the software running them was of the Siemens software brand.
Hackers created a worm that could infect the PLCs through the software. The worm drove the software to carry out pirated commands on the assembly line machinery. The worm reportedly infected over 200,000 computers and destroyed almost one-fifth of Iran’s widely expensive nuclear centrifuges designed for combining uranium compounds.
What Can You Do to Protect Yourself Against Zero-Day Attacks?


In cases where a weakness has been identified in your operating system and applications, developers can work on developing patches to make the software secure against attacks. Unfortunately, writing patches takes time, so you are at risk of a compromise before the problem is even fixed. Unpatched programs on your network increase the risk of successful attacks by zero-day threats.
And the situation is even worse when the hackers have found these unpatched areas. This brings us to the importance of being on guard against threats. There are no perfect means to protect yourself against zero-day attacks. A sound strategy involving measures on multiple fronts can be effective.
Basic Steps for Protecting Against Cyber-Crime Attacks
- Stay informed about news releases about zero-day attacks and vulnerabilities. The internet is the first resource to turn to when it comes to internet security, and there are plenty of resources out there that issue warnings about zero-day attacks and vulnerabilities that have to do with major programs that you use on a daily basis.
- Keep your software and operating systems updated. Software engineers work hard to keep their software updated and patched. Many people don’t understand the importance of software updates, and little do they know that software updates often contain critical patches to security holes. These patches essentially strengthen your protection against multiple forms of attack. In addition to security fixes, a software update typically includes certain new features. Software updates usually arrive at regular intervals. The best way to make sure that you get them all is to schedule software updates automatically.
- Use desktop and server-protection software with heuristic analysis. To detect malware traditionally, you can compare codes with existing codes of virus types. By use of Heuristic analysis, you can spot any new or old viruses.
Additional Tips for Preventing Cyber-Attacks
- Use your firewall wisely: Having a good firewall is important when protecting your system against zero-day threats. Configure your firewall to only allow necessary transactions while blocking out potentially harmful applications.
- Use only essential applications: With millions of software applications available, you’ll likely have one installed that you don’t really need. This inevitably leaves your system open to attacks, and the more software you have, the higher the risks involved. Reduce your risk for attacks by making sure only to keep the software and programs that you really need.
- Choose a good Host Intrusion Protection System (HIPS): Your antivirus protection will contain some form of HIPS but this will only be at a limited capacity.
- Follow cybersecurity practices. Cybercriminals will always be on the prowl for new victims. But that doesn’t mean that you have to be a sitting duck waiting to be the next victim. There are plenty of ways to protect yourself and your precious data. Although there’s no such thing as complete protection, the combination of techniques might make it harder for hackers and cybercriminals to get to your data. Check out this compilation of the best cybersecurity practices that you must follow.
Final Thoughts on Zero-Day Attacks


Data scientists don’t know much duration and prevalence of zero-day attacks. But if cybercrime history has anything to prove, it is that these vulnerabilities act as free passes allowing cybercriminals to attack almost anyone without fear of detection. Unfortunately for us, these kinds of malware are difficult to evaluate.
For most cases, data is unavailable until after an attack has taken place. Some form of data loss or destruction has already taken place before the patch can be produced in many cases. And since there are no perfect programs, so vulnerabilities will always exist in each of the programs we use.
Zero-day vulnerabilities are always a race against time and a race between the software manufacturers and the cybercriminals. And while we currently don’t have any advanced technologies capable of spotting zero-day exploits, data scientists researching machine learning and deep learning techniques with the potential to detect emerging malware. Current research is being used to develop advanced algorithms and machine learning tools for large-scale detection of zero-day exploits and mutated malware.
This process can take a few months to a few years to perfect. And while this technology is under development, consumers still need to be aware of how dangerous zero-day attacks can be and take the appropriate measures for self-protection.