Benefits of Using a VPN Concentrator
A VPN Concentrator is a powerful tool that offers numerous advantages for businesses and individuals looking to secure their network connections and protect their online activities. Here are some key benefits of using a VPN Concentrator:
- Enhanced Security: One of the primary benefits of using a VPN Concentrator is the enhanced security it provides. By encrypting data packets and establishing secure connections, a VPN Concentrator helps protect sensitive information from unauthorized access or interception. This is especially crucial when accessing sensitive data over public Wi-Fi networks or when connecting to remote servers.
- Increased Privacy: With a VPN Concentrator, users can enjoy increased privacy by masking their IP addresses and keeping their online activities anonymous. By routing internet traffic through the VPN concentrator, all data transmissions are encrypted, making it difficult for third parties to track or monitor online activities.
- Remote Access: A VPN Concentrator allows remote users to securely access corporate resources or connect to private networks from any location. This enables employees to work remotely while maintaining a secure connection to their company’s resources, increasing productivity and flexibility.
- Scalability: VPN Concentrators are highly scalable and can handle multiple concurrent connections. This makes them suitable for organizations of all sizes, from small businesses to large enterprises. As the number of users or network traffic increases, the VPN Concentrator can easily handle the additional load without compromising performance.
- Ease of Use: VPN Concentrators are designed to be user-friendly, making it easy for both IT administrators and end-users to set up and manage secure connections. With intuitive interfaces and streamlined configuration options, deploying and maintaining a VPN Concentrator is straightforward, even for non-technical users.
- Cost Savings: By using a VPN Concentrator, organizations can save money on expensive dedicated lines or leased circuits while still maintaining secure connections. VPNs can utilize existing internet connections, eliminating the need for additional infrastructure investments.
In summary, a VPN Concentrator provides enhanced security, increased privacy, remote access capabilities, scalability, ease of use, and cost savings. It is an essential tool for businesses and individuals looking to protect their network connections and maintain online privacy. If you value security and privacy, consider implementing a VPN Concentrator to achieve peace of mind and safeguard your digital activities.
How Does a VPN Concentrator Work?
A VPN Concentrator is a specialized networking device that enables secure communication between multiple remote clients and a centralized network. It plays a crucial role in establishing and managing VPN connections. Here’s a breakdown of how a VPN Concentrator works:
- Authentication and Encryption: When a client initiates a connection to the VPN Concentrator, the first step is authentication. The client provides credentials to verify its identity, ensuring only authorized users can access the network. Once authenticated, encryption techniques are applied to secure data transmission.
- Tunneling Protocol: The VPN Concentrator uses a tunneling protocol to encapsulate and encrypt data packets before sending them across the public internet. Common tunneling protocols used by VPN Concentrators include IPsec (Internet Protocol Security) and SSL/TLS (Secure Sockets Layer/Transport Layer Security).
- Data Encryption: Encryption is a vital component of VPN Concentrator functionality. It ensures that data is protected during transit by converting it into an unreadable format. Strong encryption algorithms, such as AES (Advanced Encryption Standard), are typically used to safeguard information.
- Routing and Decryption: Once the encrypted data packets reach the VPN Concentrator on the corporate network, they are decrypted and routed to their intended destination. The VPN Concentrator acts as a gateway, facilitating secure communication between remote clients and network resources.
- Network Address Translation (NAT): A VPN Concentrator uses Network Address Translation to translate private IP addresses used by the remote clients into public IP addresses for communication with external networks. This ensures that multiple clients can share a single public IP address without conflicts.
- Load Balancing: In scenarios where multiple VPN Concentrators are deployed, load balancing distributes the incoming VPN connections across these devices to optimize performance and prevent a single device from becoming overwhelmed. This ensures efficient resource utilization and high availability.
Overall, a VPN Concentrator provides a secure and efficient method for establishing VPN connections. By employing authentication, encryption, tunneling protocols, and network address translation, it ensures the confidentiality, integrity, and availability of data transmitted between remote clients and the centralized network. With its robust capabilities, a VPN Concentrator is indispensable for organizations seeking a reliable and secure means of remote access.
VPN Concentrator vs. VPN Server: What’s the Difference?
When it comes to setting up a virtual private network (VPN), you may come across the terms VPN Concentrator and VPN Server. While these terms are often used interchangeably, there are some key differences between them. Here’s a breakdown of the differences between a VPN Concentrator and a VPN Server:
- Role: A VPN Concentrator acts as a central point for managing and terminating VPN connections. Its primary function is to handle incoming VPN connections from multiple clients and facilitate secure communication between the clients and the centralized network. On the other hand, a VPN Server primarily provides the VPN services, such as authentication, encryption, and routing. It serves as a gateway for establishing VPN connections and may also handle other network functions.
- Scalability: VPN Concentrators are designed to handle a large number of concurrent VPN connections. They are capable of supporting multiple VPN tunnels simultaneously, making them suitable for organizations with high-volume VPN traffic. In contrast, a VPN Server may have limitations in terms of the number of concurrent connections it can handle, especially in scenarios with significant traffic.
- Network Integration: VPN Concentrators are typically deployed at the edge of a network, acting as a gateway between the remote clients and the centralized network. They are designed to integrate seamlessly into existing network infrastructure and provide secure remote access. In contrast, a VPN Server can be deployed on a standalone server or integrated into a network device, such as a firewall or router.
- Functionality: VPN Concentrators offer advanced features specifically designed for managing and optimizing VPN connections. These features may include load balancing, high availability, VPN tunnel redundancy, and network address translation (NAT). VPN Servers, on the other hand, focus on providing VPN services such as encryption, authentication, and routing. They may not offer the same level of advanced features found in VPN Concentrators.
- Scalability: VPN Concentrators are often used in larger enterprise environments with a significant number of remote clients and VPN traffic. They can handle high volumes of concurrent connections and offer robust performance. VPN Servers are more suitable for smaller environments or scenarios with lower VPN traffic, where scalability is not a primary concern.
While both VPN Concentrators and VPN Servers play essential roles in establishing and managing VPN connections, they differ in terms of their primary functions, scalability, network integration, functionality, and usability. Choosing between a VPN Concentrator and a VPN Server depends on your specific requirements, the size of your network, and the expected VPN traffic. By understanding these differences, you can make an informed decision about which solution is best suited for your needs.
Types of VPN Concentrators
VPN Concentrators come in various types, each offering unique features and capabilities to accommodate different networking requirements and environments. Here are some common types of VPN Concentrators:
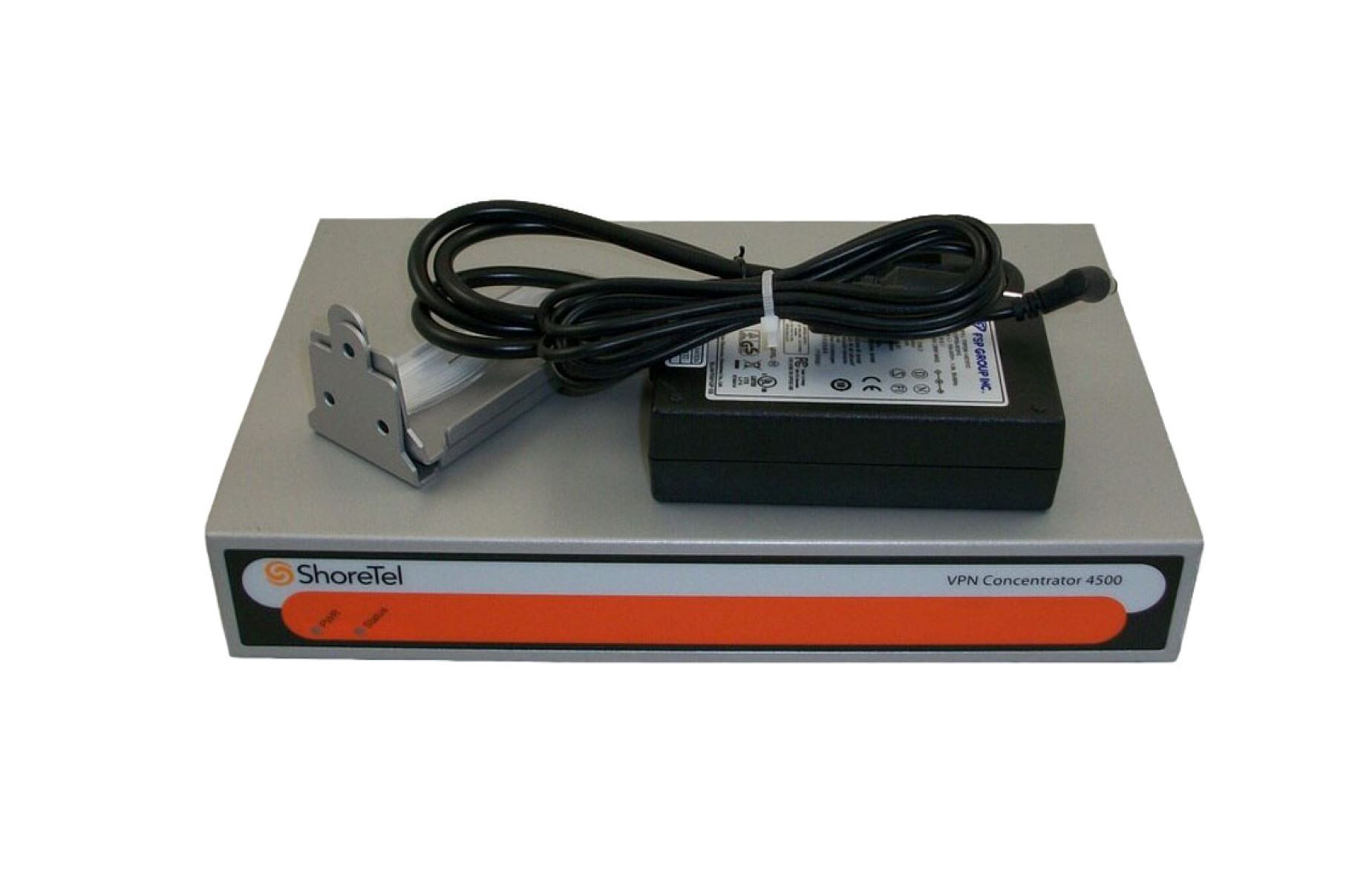
- Hardware VPN Concentrator: This type of VPN Concentrator is a physical device that is dedicated to handling VPN connections. It is purpose-built for secure communication and can handle a large number of concurrent connections. Hardware VPN Concentrators offer robust performance, scalability, and advanced features such as load balancing and high availability. They are often preferred for enterprise-level environments with high VPN traffic.
- Software VPN Concentrator: A Software VPN Concentrator is a virtual appliance or software application that runs on a server or cloud-based infrastructure. It offers similar functionality to hardware VPN Concentrators but is implemented in a software-based format. Software VPN Concentrators provide flexibility, scalability, and cost-effectiveness as they can be deployed on existing hardware or in the cloud. They are ideal for smaller organizations or those with limited resources or budgets.
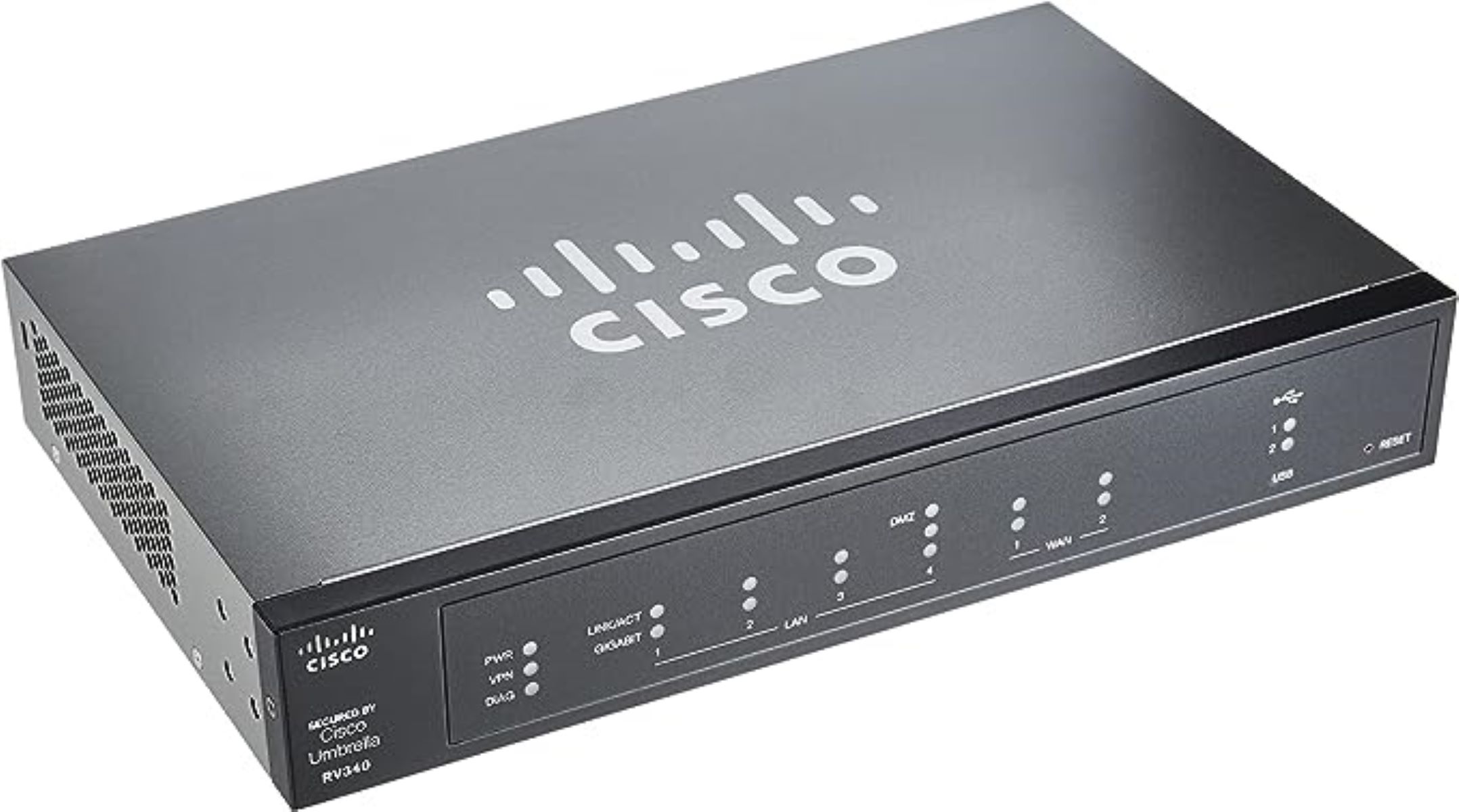
- Integrated VPN Concentrator: Some network devices, such as firewalls or routers, offer built-in VPN Concentrator functionality. These integrated VPN Concentrators are designed to provide secure remote access along with other networking capabilities. They are suitable for smaller networks or environments where there is a need for a compact and integrated solution. Integrated VPN Concentrators may have limitations in terms of scalability and advanced features compared to dedicated hardware or software-based VPN Concentrators.
- Mobile VPN Concentrator: For mobile or remote users, mobile VPN Concentrators are specifically designed to provide secure access to corporate resources while on the go. These devices are often compact and portable, allowing users to establish secure connections over cellular networks or public Wi-Fi. Mobile VPN Concentrators offer features such as strong encryption, authentication, and secure tunneling for mobile devices, making them essential for professionals who frequently work outside a traditional office environment.
Choosing the right type of VPN Concentrator depends on your specific needs, such as the size of your network, the expected number of VPN connections, available resources, and budget. Hardware VPN Concentrators offer robust performance and scalability, whereas software-based solutions provide flexibility and cost-effectiveness. Integrated VPN Concentrators are suitable for smaller networks, and mobile VPN Concentrators cater to the needs of remote or mobile users. By understanding the types of VPN Concentrators available, you can select the one that best suits your requirements and enhances your network security and remote access capabilities.
Features to Consider When Choosing a VPN Concentrator
When selecting a VPN Concentrator for your network, it is important to consider various features to ensure it meets your specific requirements. Here are some key features to consider when choosing a VPN Concentrator:
- Scalability: Determine the maximum number of concurrent VPN connections the VPN Concentrator can handle. It should be able to accommodate your current needs and have room for future growth.
- Security: Look for strong encryption protocols such as AES and secure tunneling protocols like IPsec or SSL/TLS. The VPN Concentrator should also support features like firewall integration, intrusion detection, and prevention systems to enhance network security.
- Connection Speed and Performance: Consider the throughput and processing power of the VPN Concentrator to ensure it can handle the expected VPN traffic without compromising connection speed and performance.
- Reliability: Look for features such as high availability, failover capabilities, and load balancing to ensure uninterrupted VPN connectivity even in the event of device failures or network disruptions.
- Management and Administration: Evaluate the ease of configuration, monitoring, and administration of the VPN Concentrator. An intuitive user interface and centralized management capabilities can save time and effort in managing the VPN infrastructure.
- Protocol Support: Ensure that the VPN Concentrator supports the VPN protocols that are compatible with your network environment. Commonly used protocols include IPsec, SSL/TLS, and PPTP (Point-to-Point Tunneling Protocol).
- Compatibility: Consider the compatibility of the VPN Concentrator with your existing network infrastructure. It should integrate seamlessly with your routers, firewalls, and other network devices to ensure smooth operation.
- Client Support: Check if the VPN Concentrator supports a wide range of client platforms, including Windows, macOS, Linux, and mobile operating systems such as iOS and Android. This will provide flexibility for users accessing the VPN from different devices.
- Cost: Evaluate the upfront cost, maintenance costs, and licensing fees associated with the VPN Concentrator. Consider your budget and choose a solution that provides the best value for your organization.
By considering these features, you can choose a VPN Concentrator that aligns with your network requirements and provides the necessary security, performance, scalability, and management capabilities. Investing time and effort in selecting the right VPN Concentrator will ensure a robust and secure VPN infrastructure for your organization.
Best Practices for Setting Up and Using a VPN Concentrator
A VPN Concentrator is a powerful tool that requires careful setup and management to ensure optimal performance and security. Here are some best practices for setting up and using a VPN Concentrator:
- Plan your network architecture: Before deploying a VPN Concentrator, thoroughly plan your network architecture to determine the placement of the device and consider factors such as network segmentation, firewall rules, and routing.
- Choose strong authentication methods: Implement strong user authentication methods such as multi-factor authentication (MFA) or certificate-based authentication to add an extra layer of security and prevent unauthorized access.
- Implement strong encryption: Configure the VPN Concentrator to use strong encryption algorithms such as AES-256 to ensure the confidentiality of data transmitted over the VPN.
- Regularly update firmware and security patches: Keep the VPN Concentrator up to date with the latest firmware and security patches to mitigate any known vulnerabilities and ensure optimal performance and security.
- Monitor VPN traffic and security logs: Regularly review and monitor VPN traffic and security logs to detect any abnormal or suspicious activities. This helps identify potential security threats or unauthorized access attempts.
- Enforce strong password policies: Implement strong password policies for VPN user accounts to prevent easy brute-force attacks. Encourage users to choose complex passwords and enforce password change policies.
- Regularly review and update access controls: Periodically review and update the VPN Concentrator’s access control policies to ensure that only authorized users have access to the VPN resources. Remove any unnecessary or obsolete user accounts or access permissions.
- Encrypt all sensitive data: Ensure that all sensitive data transmitted over the VPN is encrypted. This includes file transfers, email communication, and other sensitive information exchanged between users and the network.
- Implement logging and auditing: Enable logging and auditing features on the VPN Concentrator to track and monitor user activity. This can be helpful in detecting any unauthorized access attempts or policy violations.
- Regularly test disaster recovery and backup procedures: Perform regular testing of disaster recovery and backup procedures to ensure that backups are working correctly and can be restored in the event of a failure or data loss.
Following these best practices will help to ensure the secure and efficient operation of your VPN Concentrator. Regular monitoring, updates, and adherence to security protocols will contribute to a robust VPN infrastructure that protects your network and sensitive data from unauthorized access.
Common FAQ About VPN Concentrators
When it comes to VPN Concentrators, there are often questions and concerns that arise. Here are answers to some common FAQs about VPN Concentrators:
- What is a VPN Concentrator? A VPN Concentrator is a specialized networking device or software application that handles and manages multiple VPN connections. It acts as a gateway, facilitating secure communication between remote clients and a centralized network.
- Why do I need a VPN Concentrator? A VPN Concentrator is essential for organizations that require secure remote access and want to protect their network connections. It provides enhanced security, privacy, and scalability for VPN connections, allowing secured communication between remote users and the corporate network.
- What is the difference between a VPN Concentrator and a VPN Gateway? The terms “VPN Concentrator” and “VPN Gateway” are often used interchangeably. Both devices serve a similar purpose, acting as a central point for managing VPN connections. However, the term “VPN Concentrator” is usually associated with high-performance devices used in large-scale deployments, while “VPN Gateway” can refer to a broader range of devices or software solutions.
- Can I use a VPN Concentrator for personal use? Yes, a VPN Concentrator can be used for personal use, particularly if you require secure remote access to your home network or want to protect your online activities. There are VPN Concentrators available for personal use that offer user-friendly interfaces and advanced security features.
- Is a VPN Concentrator difficult to set up? The complexity of setting up a VPN Concentrator can vary depending on the device and your network configuration. However, most VPN Concentrators come with intuitive interfaces and straightforward configuration options, making the setup process relatively straightforward. It can be helpful to refer to the documentation or seek assistance from IT professionals if needed.
- Can a VPN Concentrator improve network performance? Yes, a VPN Concentrator can improve network performance by efficiently handling and managing VPN connections. It can optimize bandwidth utilization, provide load balancing capabilities, and prioritize traffic to ensure smooth and efficient communication between remote clients and the network.
- Can a VPN Concentrator be used with any type of VPN protocol? Most VPN Concentrators support commonly used VPN protocols such as IPsec, SSL/TLS, and PPTP. However, it is important to verify the supported protocols of the specific VPN Concentrator you are considering to ensure compatibility with your network environment.
- Are VPN Concentrators expensive? The cost of a VPN Concentrator can vary depending on factors such as the brand, features, performance, and scalability. While some high-end VPN Concentrators can be costly, there are also more affordable options available, including software-based VPN Concentrators or virtual appliances.
- Can a VPN Concentrator be used with mobile devices? Yes, VPN Concentrators can be used with mobile devices such as smartphones or tablets. There are VPN Concentrators specifically designed for mobile use to provide secure remote access while on the go. They often support popular mobile platforms like iOS and Android.
These FAQs should provide a better understanding of VPN Concentrators and their functionality. If you have further questions or require specific information about a particular VPN Concentrator, it is advisable to consult the manufacturer’s documentation or seek assistance from IT professionals.
Conclusion
A VPN Concentrator is a powerful networking tool that offers numerous benefits for businesses and individuals. Its ability to secure network connections, enhance privacy, and provide remote access capabilities makes it an essential component of a modern network infrastructure.
By using a VPN Concentrator, organizations can ensure the confidentiality and integrity of data transmitted over the network. It encrypts data packets, making it difficult for unauthorized individuals to intercept or access sensitive information. This is particularly crucial when connecting to public Wi-Fi networks or accessing resources remotely.
In addition to security, a VPN Concentrator also offers increased privacy. By masking IP addresses and encrypting network traffic, it prevents third parties, including internet service providers and governments, from tracking or monitoring online activities. This is especially important for individuals who value their online privacy.
Remote access is another key advantage of a VPN Concentrator. It allows employees to securely connect to their company’s resources from any location, enabling flexible work arrangements and increasing productivity. With a VPN Concentrator, businesses can facilitate secure communication and collaboration, even when employees are outside of the office.
When selecting a VPN Concentrator, it is important to consider important features such as scalability, security, performance, and compatibility. By evaluating these factors, organizations can choose a VPN Concentrator that aligns with their specific needs and enhances network security and remote access capabilities.
In conclusion, a VPN Concentrator is a powerful tool that offers enhanced security, increased privacy, and remote access capabilities. It should be considered an essential component for businesses and individuals looking to protect their network connections, maintain online privacy, and facilitate secure remote access. With careful planning, configuration, and management, a VPN Concentrator can provide a robust and secure solution for connecting users to a centralized network.